Addressing 5G Signaling Protocol Vulnerabilities
The 8th meeting of the Communications Security, Reliability, and Interoperability Council to discuss and address security vulnerabilities in the newly adopted 5G signaling protocol, HTTP/2. Learn about potential risks, recommended safeguards, and the prevention of these vulnerabilities in the upcomi
3 views • 85 slides
Understanding Malicious Attacks, Threats, and Vulnerabilities in IT Security
Malicious attacks, threats, and vulnerabilities in IT systems pose significant risks and damages. This chapter explores the types of attacks, tools used, security breaches, and measures to protect against cyber threats. Learn how security professionals safeguard organizations from malicious attacks
0 views • 24 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Understanding Vulnerabilities of Individuals with Autism in Disciplinary Hearings and Employment Tribunals
People with autism may face vulnerabilities in disciplinary proceedings and employment tribunals due to impaired theory of mind, communication difficulties, insistence on sameness, stereotyped behaviors, and sensory sensitivities. These challenges can lead to misunderstandings, difficulties in copin
0 views • 10 slides
Understanding Security Management in an ICT Environment
Security management in an ICT environment involves organizing and controlling resources in a business enterprise to mitigate network threats and vulnerabilities. This comprehensive overview covers the foundations of security, information security policies, enforcing security, and ensuring business c
0 views • 75 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Understanding Cyber Security and Risks
Cyber security, also known as IT security or computer security, is crucial for safeguarding information systems from theft, damage, and disruption. With the increasing connectivity of devices through the internet, the importance of cyber security cannot be overstated. Cyber risks encompass cyber cri
2 views • 24 slides
Understanding Buffer Overflow Vulnerabilities in Programming
Buffer overflow vulnerabilities pose serious security threats by allowing attackers to execute arbitrary code on victim machines. This issue arises from overwriting memory in a way that manipulates the program's behavior. Learn about the dangers of buffer overflow bugs, how they can be exploited, an
2 views • 33 slides
Software Security Principles and Practices: Enhancing Program Code Security
Understanding and addressing critical web application security flaws like unvalidated input, cross-site scripting, buffer overflow, injection flaws, and improper error handling is crucial in enhancing the security of program code. The NIST report NISTIR 8151 provides valuable recommendations to redu
2 views • 44 slides
Understanding Computer Security and Software Vulnerabilities
Computer security, also known as cybersecurity or IT security, encompasses the protection of information systems from theft and damage. This overview delves into software security, control-flow attacks, memory vulnerabilities, and the historical impact of events like the Morris Worm. Various aspects
0 views • 53 slides
Overview of Global Farmed Salmon and Organic Production
The data showcases the production figures for global farmed salmon across various countries, with Norway leading the production, followed by Chile, Scotland, and others. Additionally, insights into the growing organic salmon production, vulnerabilities in the sector, and details on organic mussels p
0 views • 9 slides
Analysis of file:// Vulnerabilities in Android Browser Apps
The study delves into file:// vulnerabilities in Android browser apps, uncovering risks posed by the file:// URI scheme. It highlights how file:// requests can breach app data isolation, potentially compromising sensitive files. The research presents a unified attack model, FileCross automated testi
0 views • 22 slides
Emerging Threats in Banking: Mobile Banking Vulnerabilities
Mobile banking apps face emerging threats such as mobile malware, third-party apps with poor security practices, unsecured Wi-Fi networks, and risky user behaviors. Security experts have uncovered vulnerabilities like lack of Certificate Pinning, enabling man-in-the-middle attacks. These issues pose
0 views • 20 slides
Mobile App Security: Vulnerabilities in User and Session Authentication
Mobile apps face widespread vulnerabilities in user and session authentication, posing threats like eavesdropping and man-in-the-middle attacks. End-to-end security is crucial to protect apps from untrusted networks. App developers must prioritize security measures to prevent unauthorized access to
0 views • 30 slides
Automated Detection of SSL Vulnerabilities in Applications
This research introduces SSLint, a systematic approach and automated tool for detecting incorrect SSL API usage vulnerabilities in applications. By analyzing millions of lines of code, the tool discovered previously unknown SSL/TLS vulnerable apps. The study addresses the motivation, problem stateme
0 views • 29 slides
Server-Side Technologies and Security Vulnerabilities in Mobile Services
This content delves into server-side technologies such as SQL, SOAP, JSON, and ReST used in mobile services, highlighting vulnerabilities that expose sensitive data. It emphasizes the importance of general web service security guidelines and discusses attacks against XML-based web services, outlinin
0 views • 52 slides
Understanding Blockchain Vulnerabilities to Quantum Attacks
Explore the vulnerabilities of blockchains to quantum attacks and the potential impact of quantum devices on blockchain technologies. Learn about key concepts such as blockchain basics, proof-of-work, quantum computing, quantum computing algorithms, and vulnerabilities like ECDSA and peer-to-peer ne
0 views • 23 slides
Understanding Security Threats and Vulnerabilities in Computer Systems
In computer security, threats exploit vulnerabilities to breach security and cause harm. Vulnerabilities arise from system weaknesses, attacker access, and capability. Threats include spoofing, data tampering, repudiation, information disclosure, denial of service, and elevation of privilege. Catego
0 views • 13 slides
Addressing Software Security, Economic, and Liability Issues
In the realm of software security, economic considerations often lead to negligence in addressing vulnerabilities, resulting in billions of dollars wasted annually due to exploits by hackers. The focus is on the prevalence of vulnerabilities, limited sources of security issues, and the need for a sh
0 views • 37 slides
Practical Computer Security Course Overview
Explore the crucial aspects of practical computer security in this comprehensive course led by Dr. Mark Ciampa from Western Kentucky University. From analyzing security vulnerabilities to understanding cyber threats and safeguarding your digital assets, this course equips you with essential knowledg
0 views • 114 slides
IPv6 Security and Threats Workshop Summary
David Kelsey from STFC-RAL presented on IPv6 security and threats at the IPv6 workshop pre-GDB at CERN in June 2016. The workshop covered topics such as IPv6 protocol attacks, issues for site network security teams and sys admins, new features of IPv6, security pros and cons, immediate IPv6 concerns
0 views • 29 slides
Understanding the Importance of OWASP Dependency-Check Project
Explore the significance of OWASP Dependency-Check in managing software dependencies and mitigating known vulnerabilities in applications. Learn about the risks associated with using components with vulnerabilities and the challenges of patching programs. Discover how OWASP Dependency-Check provides
1 views • 26 slides
Data Disaggregation Taskforce: Assessment and Recommendations on Vulnerabilities
The Data Disaggregation Taskforce is conducting an assessment of current practices across sectors, assessing 10 sectors/clusters, 15 categories of affected populations, and identifying vulnerabilities in 17 categories. The Taskforce is working on harmonizing categories and finalizing recommendations
0 views • 6 slides
Understanding Spectre and Meltdown Security Vulnerabilities
Spectre and Meltdown are two critical security vulnerabilities that exploit microarchitectural features to gain unauthorized access to memory. These vulnerabilities enable attackers to read memory that should be inaccessible, targeting branch prediction and exception handling mechanisms. Side channe
0 views • 19 slides
Web Security Threats and Vulnerabilities: An Overview
Understanding the risks associated with web security, including issues like IP hijacking, cache poisoning, and transparent proxies. Explore how existing approaches fall short in protecting against malicious attacks and potential exploits, with observed vulnerabilities highlighting the importance of
0 views • 17 slides
Web Security Essentials
Discover the importance of web security, reported vulnerabilities, web versus system vulnerabilities, browser security model, HTTPS protocol, familiar web technologies, goals of web security, HTTP basics, and more to safeguard your online activities and applications effectively.
0 views • 60 slides
Understanding Cloud Security Threats and Vulnerabilities
Explore the world of cloud security through the eyes of Dr. Liang Zhao, focusing on mobile security, WLAN security, and cloud threats. Learn about threat modeling, mitigating cloud vulnerabilities, and common threats such as data leakage, insecure interfaces, and more. Discover practical threat anal
0 views • 18 slides
Gamifying Vulnerability Reporting for Coordinated Disclosure at Microsoft Security Response Center
Christa Anderson, a Senior Security Program Manager at Microsoft's Security Response Center, discusses the importance of gamifying vulnerability report data to encourage coordinated disclosure. The MSRC Top 100, announced at Black Hat USA, plays a crucial role in the public credit strategy by recogn
0 views • 13 slides
Importance of Security in Web Development
Our perception of security has evolved to acknowledge the presence of malicious actors and potential vulnerabilities in web applications. To write secure code, developers must assume the worst-case scenario and adopt a security mindset that trusts no one. Attackers have various goals, such as steali
0 views • 18 slides
Understanding Network Security Vulnerabilities and Attacks
Explore the world of network security vulnerabilities and attacks, including Denial-of-Service (DoS) and Distributed-Denial-of-Service (D-DoS), security flaws in the TCP/IP protocol suite, ICMP attacks, routing attacks, and TCP attacks. Learn about common security vulnerabilities such as address spo
0 views • 36 slides
Understanding Web Application Vulnerabilities in Information Warfare
Web application vulnerabilities such as Cross-Site Scripting, SQL Injection, and Broken Authentication pose significant risks in information warfare. Current solutions include Black-Box Security Testing and XSS Analyzers, but they have limitations like static verification and dependence on security
0 views • 21 slides
Understanding Programming Language Vulnerabilities and ISO/IEC/SC22/WG23
Explore the history and evolution of ISO/IEC/SC22/WG23 focusing on programming language vulnerabilities, led by Stephen Michell. Learn about the formation in 2006, publications, identified vulnerabilities, and the upcoming Edition 3 outlook with language-specific annexes. Discover comparisons with A
0 views • 15 slides
Basic Web Security Model for Secure Electronic Commerce
This presentation covers the basic web security model for secure electronic commerce, focusing on vulnerabilities such as XSS and SQL injection. It discusses the decline in web vulnerabilities since 2009 and explores reported web vulnerabilities. The course theme includes topics like web application
0 views • 38 slides
Understanding Web Security: Threats and Protections
Exploring the landscape of web security through discussions on historical vulnerabilities, top web threats, browser security models, and the goals of web security. Delve into the world of web programming, security threat models, and learn about the goals and importance of maintaining a secure web br
0 views • 74 slides
Understanding Computer Security Threats and Vulnerabilities
Explore the prevalent computer security issues such as buggy software and gullible users that can be exploited for financial gain. Learn about the marketplace for vulnerabilities, owned machines, and methods attackers use to profit from compromised systems. Discover the motivations behind owning mac
0 views • 23 slides
Understanding Spectre and Meltdown Security Flaws
Recent security vulnerabilities named Spectre and Meltdown have surfaced in the realm of computer architecture and hardware implementation. These flaws allow attackers to access sensitive data through covert channels utilizing speculative execution mechanisms. The vulnerabilities exploit the perform
0 views • 12 slides
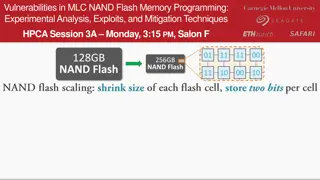
Experimental Analysis of Vulnerabilities in MLC NAND Flash Memory Programming
This session at HPCA explores the experimental analysis, exploits, and mitigation techniques related to vulnerabilities in MLC NAND flash memory programming. The presentation delves into the risks associated with NAND flash memory, such as data corruption and errors during read operations. It discus
0 views • 10 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Best Practices for Password Security and User Authentication
Password security is crucial for protecting sensitive information. Passwords should not be shared and should be changed regularly to prevent unauthorized access. Implementing strong passwords, two-factor authentication, and biometric security measures can greatly enhance security. Additionally, main
0 views • 16 slides
Formal Security Evaluation for Microarchitectural Modeling
This content discusses the challenges and defenses in evaluating formal security for microarchitectural modeling. It covers topics such as constant-time programs, speculative machines, post-quantum cryptography, side-channel attacks, and defense proposals against vulnerabilities like Spectre and Gho
0 views • 20 slides