BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Enhancing Security Definitions for Functional Encryption
This study delves into the realm of functional encryption (FE) against probabilistic queries, highlighting the necessity for improved security definitions to address existing limitations such as counter-intuitive examples and impossibility results. The exploration leads to proposing a new security n
4 views • 20 slides
Shielding Your Organization: Chief Security Officer Recruitment Insights
\"Shielding Your Organization: Chief Security Officer Recruitment Insights\" offers invaluable guidance for businesses seeking to fortify their security posture by recruiting the right Chief Security Officer (CSO). This comprehensive resource delves into the intricacies of chief security officer rec
0 views • 7 slides
security service solutions
With skilled workers and cutting-edge technology, Ingenuity Security Solutions offers full tower security services in Maryland to keep your property safe. Our personalized security options for businesses include video, limiting who can enter, and assessing the risk. Keeping the highest standards of
0 views • 1 slides
security service solutions
With skilled workers and cutting-edge technology, Ingenuity Security Solutions offers full tower security services in Maryland to keep your property safe. Our personalized security options for businesses include video, limiting who can enter, and assessing the risk. Keeping the highest standards of
1 views • 1 slides
The Importance of Cultural Fit in Chief Security Officer Recruitment
Ensuring cultural fit in Chief Security Officer recruitment is crucial for aligning security leadership with company values, enhancing collaboration, and improving retention. A CSO who meshes well with the organizational culture can effectively drive strategic security initiatives and foster a cohes
0 views • 8 slides
International Approaches to Enhance Nuclear Safety and Security
Understanding the concepts of nuclear safety and security, their differences, and the importance of establishing a robust nuclear security culture are essential for safeguarding nuclear facilities. The International Atomic Energy Agency (IAEA) plays a significant role in promoting nuclear safety and
1 views • 10 slides
TSA Updates on Security Training Rule for OTRB Companies
In the recent updates by TSA, the Security Training Rule for over-the-road bus (OTRB) companies has been highlighted. The rule mandates TSA-approved security training for employees in security-sensitive roles, emphasizing key requirements and elements of security training. Urban areas covered by the
1 views • 18 slides
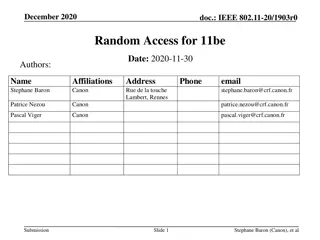
Proposal for Random Access Efficiency Enhancement in IEEE 802.11be Networks
This document presents a proposal for enhancing random access efficiency in IEEE 802.11be networks through a Random-Access NFRP (RA-NFRP) principle. The proposal addresses the challenges of low efficiency in the current UORA procedure and introduces modifications based on the 802.11ax standard to im
5 views • 16 slides
AEP Enterprise Security Program Overview - June 2021 Update
In the June 2021 update for the Kentucky Interim Committee on Natural Resources and Energy, American Electric Power (AEP) addresses recent ransomware events, their security program updates, and details about their enterprise security measures. AEP, one of the largest electric utilities in the U.S.,
0 views • 12 slides
Efficient Pink Team Review for Proposal Success
The Pink Team plays a crucial role in validating proposal strategies, win themes, and providing direction to the proposal team. This brief covers the purpose, process, and guidelines for conducting an efficient Pink Team review that ensures the proposal aligns with the customer's needs and achieves
0 views • 9 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Subscription Transfer via Old Primary Device Proposal for TS.43
This proposal discusses the inclusion of Subscription Transfer methods starting from the old Primary Device in TS.43 standards. It highlights the benefits of initiating transfers from the old device, such as enhanced security with EAP-AKA authentication and improved user experience. The proposal sug
1 views • 4 slides
DRD3 Community Workshop at CERN: Proposal Formation and Collaboration Building
DRD3 Community Workshop at CERN on 22-23 March 2023 focuses on forming the DRD3 proposal team, outlining the mandate, and organizing activities for solid-state detector research. The team's role is to guide a bottom-up process for proposal development, conduct a community survey, and facilitate coll
0 views • 16 slides
Red Team Debriefing: Evaluating Proposal Effectiveness
In this presentation, the Red Team led by [Red Team Leader's Name] reviews the proposal to provide valuable feedback from an outsider's perspective. The Red Team aims to predict scoring, ensure compliance, assess quality, and recommend improvements for the proposal's success. Operational approaches,
0 views • 18 slides
5G Use Case Proposal for Dublin Ericsson
This proposal outlines the use of NETCONF for configuration management in 5G networks, focusing on Dublin. It covers topics like Configuration with NETCONF, NETCONF Overview, NETCONF Security, YANG Overview, and Proposed Use Cases and Requirements for Dublin. The proposal emphasizes the importance o
7 views • 20 slides
Effective Proposal Management Strategies for Success
Proposal managers play a crucial role in the success of bids and proposals. They must navigate different scenarios, engage early in the capture/strategy phase, transition to proposal development, and collaborate with core teams effectively. Strategic proposal managers help identify gaps, establish r
0 views • 22 slides
Rural Access Compliance Rules Proposal by Glenn Disher - PBM Investigator
Proposal by Glenn Disher, a PBM Compliance Investigator, outlines rules for rural access compliance. The proposal focuses on considering local conditions and enforcing rules for maximum impact. It includes recommendations for zip code rules, compliance mileage rules, and examples of non-compliant ru
0 views • 7 slides
Comprehensive Hotel Proposal Template and Guide
Explore a comprehensive hotel proposal template and guide, including sections on event details, proposal validity, contact information, event overview, accommodation, meeting space, and food and beverage. Find tips on writing each section effectively to create a professional proposal for your event.
0 views • 8 slides
Proposal for IEEE 802.11-23/1984r1 TGbi Coordinated MAC Rotation
The document discusses a proposal for IEEE 802.11-23/1984r1 TGbi focusing on coordinated MAC rotation, EDP epochs, anonymity sets, and group epochs. It introduces concepts like individual and mass rotations, anonymity set size, and hiding in the crowd examples. The coordination for group epochs and
1 views • 10 slides
Grant Proposal Requirements and Checklist for SCDD Cycle 45 RFP
This comprehensive grant proposal guide outlines the requirements and checklist for submitting a proposal for the California State Council on Developmental Disabilities (SCDD) Cycle 45 Request for Proposal (RFP). Developed by a collaboration of prestigious institutions, this resource covers essentia
0 views • 25 slides
GMAS Proposal Entry and Homepage Enhancements Overview
GMAS Proposal Entry and Proposal Homepage are undergoing enhancements, consolidating multiple screens into one for Initial Proposal and Competing Renewal entries. Changes include smarter organization look-up, streamlined principal investigator search, new sponsor look-up, and automatic period genera
0 views • 17 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
Guide for Women in Business: Proposal Development & Bid Preparation
In the world of business, proposals and bids go hand in hand. This comprehensive guide is tailored for women in business, covering topics such as the steps to writing a proposal and bid, best practices, and the importance of understanding client needs. It explains the intricacies of proposal develop
0 views • 26 slides
Enhancing Eco-Innovation in Waste Water Treatment - LIFE+ Proposal Budapest
Life+ Proposal Budapest, November 6th, 2012, focuses on improving framework conditions for fast-track eco-innovation in waste water treatment along the Blue Danube. The proposal outlines objectives such as promoting technological innovation in waste water treatment plants, enhancing policy and gover
0 views • 11 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Effective Proposal Submission Process for Sponsored Research Administration
Streamlined proposal submission process involves finding relevant funding, reviewing agency guidelines, preparing and obtaining approvals, utilizing proposal tools, and establishing a working relationship with the Sponsored Research Administration (SRA). Adhering to the three-working-day policy ensu
0 views • 41 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides