Understanding Critical and Non-Critical Incidents in Incident Reporting
Critical incidents, as defined by regulations, are serious events that pose immediate risk to health, safety, or welfare. Non-critical incidents, on the other hand, are minor in nature and do not have serious consequences. Incident reports play a crucial role in documenting occurrences, identifying
0 views • 29 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Comprehensive Guide to Initial Operational Response (IOR) in Hazardous Substance Incidents
This guide outlines the objectives, principles, and key elements of Initial Operational Response (IOR) to incidents involving hazardous substances or CBRN materials. It covers the stages of response, transition to Specialist Operational Response (SOR), primary objectives of IOR, JESIP principles, an
4 views • 25 slides
Reporting Incidents on Sphera
The Council utilizes Sphera to manage health and safety risks, requiring employees to report accidents, near misses, violence incidents, and more promptly. This guide explains how to report incidents on Sphera, including accessing the reporting portal, completing mandatory fields, and obtaining pape
9 views • 26 slides
Understanding Critical Incidents for Personal Growth
Critical incidents are integral learning opportunities that can lead to significant personal development. They do not necessarily involve danger but are situations that prompt deeper reflections. The BCU Assessment tracker is used to track progression towards key themes. The associated teacher's pro
1 views • 4 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Evolving Security Practices in DevOps: A Holistic Approach
Explore the evolution of security practices within the DevOps landscape, from debunking the myth of DevSecOps non-existence to embracing a shift-left mentality. Discover the challenges of traditional security views, the importance of continuous security integration, and the impact of delivery exposu
1 views • 25 slides
Process Safety Incidents and Prevention Best Practices
Process safety incidents involving hazardous materials like caustic solutions, ammonia leaks, and TFE have caused injuries and fatalities. Key incidents include burns from caustic exposure, fatalities due to ammonia leaks, and an explosion from improper TFE handling. Learning from these incidents hi
7 views • 21 slides
Understanding Security Onion: Network Security Monitoring Tools
Security Onion is a Linux distribution designed for network security monitoring using various tools like Full Packet Capture, Network IDS, Host IDS, and Analysis Tools. It offers capabilities for detecting and responding to security incidents effectively, making it a valuable asset for defensive net
1 views • 17 slides
Clinical Incidents and Complaints: Understanding, Management, and Prevention
Explore the definition of clinical incidents, learn how to recognize and react to them, understand patient complaints, and discover ways to prevent incidents and complaints in healthcare settings. Discover who to report incidents to and how healthcare organizations handle complaints. Gain insights i
0 views • 12 slides
Understanding Level I Serious Incidents Reporting
Defining and discussing Level I Serious Incidents in the context of DBHDS regulations, including the criteria, reporting requirements, and examples. Learn how to identify, document, and analyze incidents that occur during service provision or on provider premises, ensuring the safety and well-being
0 views • 41 slides
Analyzing Key Incidents in Literature: A Comprehensive Guide
Explore the significance of key incidents in literary works through a detailed examination of pivotal moments that shape characters, themes, and plots. Learn how to analyze and interpret key incidents using appropriate techniques to enhance your understanding of the text as a whole.
0 views • 18 slides
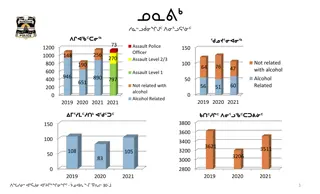
Analysis of Assault Incidents in Relation to Police Officers
This data presents a detailed analysis of assault incidents involving police officers, categorized by assault level, alcohol-related factors, and year. The data covers non-criminal and criminal incidents, as well as the combined total incidents over the years 2019, 2020, and 2021.
0 views • 36 slides
Understanding Standoff Incidents in Law Enforcement
Standoff incidents present unique challenges for law enforcement, with suspects often better armed than initial responders and potentially suicidal. The incidents may involve planned attacks, barricaded suspects, hostage situations, or active shooters, requiring specific response protocols such as c
0 views • 22 slides
Major Information Security Challenges Faced by Financial Services Firms
In today's digital age, large financial services firms encounter significant information security challenges such as exponential growth in malware threats, sophisticated cyber attacks, and frequent penetrations of information systems. The perfect storm of technological advancements and connectivity
0 views • 29 slides
Camp and Club Incidents at 4-H Programs
Various incidents occurred at 4-H programs involving negligence, resulting in injuries to participants. From a camper injured by a protruding nail, to an accident caused by a faulty van, and accidents during horse riding and archery activities, these incidents highlight the importance of ensuring sa
0 views • 11 slides
Update on Hazing Incidents in Schools: Consequences and Lessons
Recent hazing incidents in schools have raised concerns, with various cases involving freshmen being subjected to harmful practices by senior students. These incidents have led to legal repercussions, jail time, probation, and community backlash. The stories highlight the importance of vigilance by
0 views • 39 slides
Regulatory Changes and Quality Improvement in October 2018
The content discusses regulatory changes related to risk and quality improvement in October 2018, focusing on serious incidents, reporting requirements, risk management, and monitoring service quality. Providers are mandated to review, analyze trends, identify systemic issues, recommend remediation,
0 views • 31 slides
Understanding Security Threats and Countermeasures
Explore the diverse threats posed by attackers in the information security landscape, ranging from employee sabotage to hacking incidents. Learn about fundamental security terminology, types of security compromises, and countermeasure strategies to prevent, detect, and correct security breaches. Gai
0 views • 32 slides
Recent High-Potential Incidents and Recommendations in Queensland Coal Mines
The Queensland Coal Mines Inspectorate has reported several serious accidents and high-potential incidents, including injuries, equipment failures, and near-miss collisions. Recommendations include auditing safety controls, enhancing training for mobile plant operators, and ensuring compliance with
0 views • 15 slides
Recent High Potential Incidents and Recommendations - Queensland Coal Mines Inspectorate
The July 2022 incident periodical by the Queensland Coal Mines Inspectorate highlights two significant incidents involving a tyre fire and a CMW crush injury. Recommendations include improving road conditions, enhancing emergency response procedures, and ensuring proper task planning and risk assess
0 views • 14 slides
Responding to Incidents Related to Culture and Identity in Issaquah School District: Parent Workshop Summary
In this session by the Equity and Family Partnership Department along with school counselors in Issaquah School District, parents were guided on how to support their children in reporting and responding to incidents related to culture and identity at middle and high school levels. The importance of
0 views • 26 slides
Reporting Accidents and Incidents at Work: Understanding RIDDOR Regulations 2013
The Reporting of Injuries, Diseases, and Dangerous Occurrences Regulations 2013 (RIDDOR) outlines the legal requirements for reporting work-related accidents and incidents. It specifies what must be reported, who to report to, types of reportable accidents, recording requirements, and how to report
0 views • 9 slides
Understanding Disability Hate Crime and Hate Incidents
Disability hate crime and incidents involve criminal offenses or non-crime incidents perceived as motivated by hostility or prejudice towards a person's disability. Key elements include hostility, prejudice, perception, and may involve racial, religious, or sexual orientation hate. Perceptions are c
0 views • 16 slides
Addressing Bias-Related Incidents at Concordia University
The report discusses bias reporting at Concordia University, highlighting the importance of understanding and addressing bias-related incidents. It covers examples of bias, distinction between bias incidents and hate crimes, and strategies for response. Presenters from the Office of Multicultural En
0 views • 11 slides
Understanding the Hazards of Arc Flash Incidents by Littelfuse Startco
Littelfuse Startco highlights the dangers of arc flash incidents, emphasizing the costly and dangerous consequences such as fires, burns, injuries, and even fatalities. The case study of an electrician's severe burns serves as a stark reminder of the potential risks associated with electrical hazard
0 views • 24 slides
Understanding Reportable Incidents in Developmental Disability Care
The report outlines the criteria for incidents to be classified as reportable in the context of intellectual and developmental disabilities care. It covers various types of incidents, including abuse, neglect, serious injuries, and behavioral or medical incidents requiring specific interventions. Th
0 views • 28 slides
Offshore Health and Safety Executive Report on Dropped Objects Incidents in 2015
The Health and Safety Executive report provides a detailed overview of dropped objects incidents in the offshore industry during 2015. The report includes data on quarterly totals, types of incidents, and specific cases of objects being dislodged and falling. Various scenarios involving derricks, cr
0 views • 13 slides
Clinical Incidents, Complaints, and Learning Objectives in Healthcare
Understand the importance of recognizing and reacting to clinical incidents, handling patient complaints, and learning from adverse events. Learn about the definition of clinical incidents, who to inform, and the process of reporting incidents in healthcare settings. Discover reasons behind patient
0 views • 12 slides
Food Defense Training and Rapid Response Team Meeting Overview
Food Defense Training and Rapid Response Team Meeting provides insights into food security, food defense, and food safety to protect against intentional and unintentional contamination incidents. The presentation delves into incidents, policies, responses, and preparedness, emphasizing the importanc
0 views • 24 slides
Workplace Incident Investigation and Root Cause Analysis
Workplace incident investigations are crucial for preventing future incidents. They help determine what happened, identify causes, and uncover unsafe conditions or procedures. By conducting thorough investigations, management can take corrective actions and demonstrate commitment to safety. Understa
0 views • 17 slides
ConnectWise Incident Response Service: Expert Help for Security Incidents
ConnectWise Incident Response Service offers expert assistance 24/7 for handling worst-case security incidents. Gain direct access to incident response analysts, real-time management, recovery procedures, insights on attacker tactics, and post-incident monitoring. Choose from flexible service option
0 views • 13 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Serious Incidents Reporting and Investigations in Bikeability Program
The Serious Incidents Reporting and Investigations guide provides crucial information on responsibilities, reporting procedures, and types of incidents such as safeguarding, health and safety, data breaches, and risks to reputation. It emphasizes timely reporting, record-keeping, and continuous lear
0 views • 20 slides
Xoserve Incident Summary - July 2020
This presentation provides an overview of P1/2 incidents experienced by Xoserve in July 2020. It describes high-level impacts, causes, and resolutions undertaken by Xoserve to address the incidents. The information is shared to give customers insight into Xoserve's platforms supporting critical busi
0 views • 7 slides
School Safety Report for 2022-2023 Academic Year
The school safety report for the 2022-2023 academic year highlights key data on incidents reported through the Student Safety Data System (SSDS) and the Electronic Violence & Vandalism Reporting System (EVVRS). The report covers various aspects such as incidents of harassment, violence, vandalism, a
0 views • 9 slides
Airline Passenger Incidents: A Disturbing Trend Unfolds
Incidents of unruly behavior on airplanes have been on the rise, prompting concerns for passenger safety. From fights over reclining seats to disturbing acts like groping and urinating, the incidents showcase a range of troubling behaviors. Factors like intoxication, frustration, and mental health i
0 views • 27 slides
Oregon Department of Education Discipline Data Collection 2023-2024
Oregon Department of Education presents information on discipline incidents, restraint, seclusion incidents, seclusion rooms, data collection training materials, information security, and what's new for 2023-2024. They emphasize the purpose of collecting student-level records about discipline incide
0 views • 52 slides