Parsimoni – the European IoT/Edge OS. Secure, efficient, flexible.
Revolutionizing IoT/Edge computing with secure, efficient, and flexible technology, Parsimoni aims to set new standards in the industry. Led by CEO Miklos Tomka, the company leverages European open-source technology to create a secure-by-design OS for IoT/Edge applications. Seeking partners for cons
1 views • 5 slides
Understanding Secure Act 2.0 Key Provisions
In a detailed report by Dee Spivey and Angie Zouhar, key provisions of SECURE Act 2.0 are outlined, including changes in retirement plans like RMD age increase, employee certification of hardship withdrawals, and more. Secure 1.0 and Secure 2.0 differences, effective dates, and necessary actions for
5 views • 12 slides
Effective Cash Collection Procedures and Controls
Adhering to the University Cash Collection Policy is crucial to minimize risks and ensure consistency in cash handling procedures. Cash includes various forms like currency, checks, and electronic funds. Maintaining PCI DSS compliance for credit card payments is essential. Implementing segregation o
0 views • 20 slides
Introduction to SFTP & PGP Encryption for Secure Data Transfer
Discover how to ensure reliable data transfer, make informed decisions, and gain a strategic advantage through the use of Secure File Transfer Protocol (SFTP) and Pretty Good Privacy (PGP) encryption. The session includes demonstrations on PGP encryption and SFTP access, along with insights on setti
1 views • 22 slides
Secure Cash Handling Procedures for Office of the Bursar
Guidance and procedures are provided for secure revenue handling by employees in the Office of the Bursar to prevent fraud, mishandling of funds, and ensure compliance with regulations. This includes details on revenue deposits, employee responsibilities, types of revenue accepted, registration prot
0 views • 26 slides
Ensuring Secure Testing Environments in Oregon Education System
Oregon's Statewide Assessment System (OSAS) emphasizes the critical need for secure testing environments to maintain the validity and accuracy of assessment data. This includes handling secure printed test materials, identifying and preventing improprieties, and reporting any irregularities. From ma
2 views • 20 slides
Safe & Secure Gaming Platform Is Online Cricket ID In India
The most secure and safe gaming platform in India is Online Cricket ID. Faster withdrawals within 5 minutes with your online cricket ID. Secure and trusted online cricket and casino ID provider with 24x7 customer support.\nVisit for more information:
1 views • 3 slides
Enhancing Privacy in Crowdsourced Spectrum Allocation
This research focuses on protecting privacy in crowdsourced spectrum allocation, addressing the security challenges faced due to the presence of multiple entities and the sensitive information collected. By proposing potential ideas like Fully Homomorphic Encryption (FHE) and Secure Multi-Party Comp
0 views • 26 slides
Secure Computation Techniques in RAM Models with Efficient Automation
Explore the automation of efficient RAM-model secure computation techniques, including examples such as secure binary search. Discover how traditional solutions using circuit abstractions can be improved for sub-linear time computation through methods like Oblivious RAM. Learn about techniques such
0 views • 37 slides
Advancements in Active Secure Multiparty Computation (MPC)
Delve into the realm of secure multiparty computation under 1-bit leakage, exploring the intersection of DP algorithms, MPC, and the utilization of leakage for enhanced performance. Discover the overhead implications of achieving active security, as well as the evolution of secure computation protoc
0 views • 43 slides
Secure Access to OAuth-Based Services in HTCondor Jobs
Enhance the security of HTCondor job submissions by leveraging OAuth tokens for secure access to file storage services. Learn how the Credd and Credmon architecture facilitates the management and secure transfer of credentials, ensuring sensitive data remains protected during job execution.
0 views • 23 slides
Enhancing Cybersecurity in University Research: Insights from SouthEast SECURE Program
The SouthEast SECURE program at universities like Clemson and University of Alabama focuses on improving cybersecurity for NSF-funded research projects. It provides metrics, communication facilitation, and practical assistance to enhance data security. The program aims to support researchers in util
0 views • 22 slides
Tamper-Evident Pairing (TEP) Protocol for Secure Wireless Pairing Without Passwords
This article discusses the challenges of traditional secure wireless pairing methods that rely on password validation and proposes the Tamper-Evident Pairing (TEP) protocol as a secure in-band solution to protect against Man-in-the-Middle (MITM) attacks. TEP eliminates the need for out-of-band chann
1 views • 40 slides
Evolution of Proofs in Cryptography
Cryptography has evolved from classical proofs to interactive and probabilistically checkable proofs, enabling the development of applications like Non-Malleable and Chosen-Ciphertext Secure Encryption Schemes. Non-Malleability protects against active attacks like malleability and chosen-ciphertext
0 views • 29 slides
Secure Multiparty Computation: Enhancing Privacy in Data Sharing
Secure multiparty computation (SMC) enables parties with private inputs to compute joint functions without revealing individual data, ensuring privacy and correctness. This involves computations on encrypted data using techniques like homomorphic encryption for scenarios like e-voting. SMC serves as
2 views • 27 slides
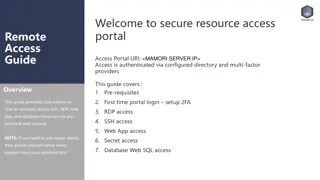
Comprehensive Remote Access Guide for Secure Resource Access Portal
This detailed guide provides step-by-step instructions for setting up remote access to SSH, RDP, web applications, and databases via secure authentication processes. It covers prerequisites, initial login setup with 2FA, and connecting to various resources securely. Follow the guide to ensure a smoo
0 views • 12 slides
Actively Secure Arithmetic Computation and VOLE Study
Exploring actively secure arithmetic computation and VOLE with constant computational overhead at Tel Aviv University. Understanding how functions are represented in secure computation using arithmetic circuits over boolean circuits. Efficiently evaluating arithmetic circuits over large finite field
0 views • 36 slides
Accessing and Utilizing CPCSSN Secure Research Environment (SRE)
Learn how to access the CPCSSN Secure Research Environment (SRE) for secure data analysis. Follow steps such as setting up VPN, accessing SQL databases, and establishing ODBC connections for statistical analysis using tools like SAS, R, SPSS, or Stata. Enhance your research capabilities within a sec
0 views • 12 slides
Advancements in Multi-Key Homomorphic Encryption Using TFHE
Revolutionary research has led to the development of Multi-Key Homomorphic Encryption (MKHE) from TFHE, enabling secure and efficient computations on encrypted data. This technology offers advantages such as dynamic operability, stronger security, and minimized interaction, making it an ideal soluti
0 views • 20 slides
Enhancing Animal Telemetry Data Systems for Secure Collaboration
Wide spectrum of animal telemetry data collection protocols and platforms require enhanced data stewardship options for secure sharing before public release. The need for a more granular understanding of available data and structured systems integration is crucial. Initial workflow involves providin
0 views • 4 slides
Test Requirements and Procedures Overview for TCB Council Meeting
This document outlines the test requirements and procedures prepared by Mark Briggs and Mark Maynard for the TCB Council meeting scheduled for September 16, 2024. It covers EMC test procedures, FCC regulations, Industry Canada standards, RF exposure procedures, and equipment certification guidelines
0 views • 25 slides
Understanding Secure Information Transmission in Cryptography
Explore the concepts of secure information confidentiality, integrity, and authenticity in the realm of cryptography, including digital signatures, signcryption, and the challenges faced in ensuring secure communication. Delve into the attempts to encrypt, authenticate, and solve issues like non-rep
0 views • 23 slides
NSCAS Test Administration Orientation 2022-2023 Overview
The Nebraska Student-Centered Assessment System (NSCAS) Test Administration Orientation for 2022-2023 provides information on the assessments, security procedures, training goals, and administration guidelines for ensuring fairness and equity in testing. It outlines the security measures, contact in
0 views • 28 slides
Exploring Secure Computation in the Age of Information
Welcome to Secure Computation Lecture 1 by Arpita Patra. The course covers evaluation policies, projects, and references in the realm of secure computation. The content delves into the significance of information security across various sectors, emphasizing the importance of safeguarding sensitive d
0 views • 36 slides
Secure Method of Information Exchange: Overview of Hub Concept & Prototype
This document presents an overview of the Hub Concept & Prototype for Secure Method of Information Exchange (SMIE) developed in April 2013 by New Zealand and the USA. It discusses drivers, ePhyto transmission options, Direct NPPO to NPPO ePhyto exchange, Hub/Cloud communication, security mechanisms,
0 views • 20 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
0 views • 12 slides
Secure Software Development Best Practices
Embrace secure software development practices by considering security throughout the software development lifecycle. Identify sensitive data, define security requirements, apply secure design principles, implement coding rules, conduct thorough testing including penetration testing, and explore diff
1 views • 17 slides
Understanding Secure Electronic Transactions (SET)
Secure Electronic Transactions (SET) is an encryption and security specification designed to protect credit card transactions on the Internet. SET provides a secure way to utilize existing credit card payment infrastructure on open networks, such as the Internet, involving participants like clients,
1 views • 6 slides
Secure Two-Party Computation and Basic Secret-Sharing Concepts
In today's lecture of "Foundations of Cryptography," the focus is on secure two-party and multi-party computation, emphasizing semi-honest security where Alice and Bob must compute without revealing more than necessary. Concepts such as real-world vs. ideal-world scenarios, the existence of PPT simu
0 views • 27 slides
Healthcare Challenges in Secure Environments
The secure environments of prisons, secure mental health hospitals, young offenders institutions, and immigration centers face various healthcare challenges. The aim is to provide healthcare equivalent to that in the wider community. Background information highlights the evolution of healthcare in p
0 views • 26 slides
Research Data Classification and Secure Storage Options
Explore the classification of research data into public, private, secure DoD, and VA data categories, with examples and guidelines for secure storage options. Understand the risks associated with unauthorized disclosure of private/confidential data and learn how to protect sensitive information to p
0 views • 16 slides
Linear Communication in Secure Multiparty Computation for Efficient and Fast Processing
The research focuses on achieving perfectly secure multiparty computation (MPC) with linear communication and constant expected time. It explores efficient approaches using a broadcast-hybrid model and P2P communication, aiming to balance speed and efficiency in MPC. The study highlights the importa
0 views • 23 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Exploring Secure Care Services in Scotland
Delve into the world of secure care services in Scotland, focusing on achievements, challenges, and opportunities in providing youth justice. Learn about trends in secure care, reduction in costs, reasons for referrals, and evidence-based programs like DBT in Glasgow. Gain insights from industry lea
0 views • 77 slides
Step-by-Step Guide to Using secure.colostate.edu NetConnect
Accessing secure.colostate.edu NetConnect is crucial for connecting securely to Colostate's network. Follow these steps: Use your web browser to login, allow Juniper Network installation, access Secure.Colostate.edu, connect behind the firewall, and utilize Pangea for file access. Obtain the Pangea
0 views • 8 slides
Understanding Secure PRFs and PRPs in Cryptography
Dive into the world of secure Pseudo-Random Functions (PRFs) and Pseudo-Random Permutations (PRPs) in cryptography. Learn about the definitions, security criteria, and examples of secure PRFs and PRPs such as 3DES and AES. Explore the concepts of secure block ciphers and key principles behind these
0 views • 54 slides
Fire and Emergency Procedures at Edinburgh Napier University
The Health & Safety Team at Edinburgh Napier University has provided detailed fire and emergency procedures for the safety of individuals on campus. In case of a fire, immediate action such as raising the alarm and evacuating the building using designated exit points is crucial. Additionally, guidel
0 views • 21 slides
Foundations of Cryptography: Secure Multiparty Computation
Explore the foundations of cryptography with insights into secure multiparty computation, including the Secure 2PC from OT Theorem and the Two-Party Impossibility Theorem. Delve into the impossibility of 2-Party Secure MPC, claims, and exercises on extending to statistical security. Learn about redu
0 views • 39 slides
Understanding Secure Messaging and Encryption Techniques
Explore the possibilities of sending secure messages through encryption without the need for advanced degrees in Computer Science or Math. Learn about symmetric and asymmetric key encryption methods, the use of PGP for secure messaging, and the concept of shared-key encryption. Discover the intricac
0 views • 16 slides
Tritium Safety Protocols and Containment Procedures for Hall A Target Facility
This document outlines the safety protocols and containment procedures related to tritium handling at the Hall A Target Facility. It covers various aspects such as tritium containment, procedures development, access control, truck ramp protocols, and controlled access procedures. Detailed instructio
1 views • 45 slides