Satellite Communications Support for Enhanced Emergency Communications
Providing support for enhanced emergency communications through mobile and fly-away satellite systems. These systems offer cellular-based WiFi, satellite-based WiFi, and voice over IP phone numbers for use during communication disruptions. Satellite airtime is provided at no cost to TxDOT through th
2 views • 4 slides
Texas FFA Agricultural Communications Career Development Event 2023
The 2023 Texas FFA Agricultural Communications Career Development Event offers a comprehensive schedule including team orientation, press conference, quizzes, practicums, and more. Contestants will engage in activities such as a communications quiz, editing exercise, practicum work, and web design.
1 views • 20 slides
CEPT Workshop on 6G Mobile Communications: Numbering & Network Issues
CEPT Workshop on 6G Mobile Communications, led by Elizabeth Greenberg of Ofcom UK, addresses the role of numbering and networks in the ECC, numbering considerations for 6G, and how WG NaN contributes to the development of numbering for 6G technologies. Key topics include ensuring non-discriminatory
1 views • 8 slides
Expert Group on Communications Technology for Automated Driving
The Expert Group on Communications Technology for Automated Driving, established by ITU, focuses on key topics such as V2V communications capabilities, protecting vulnerable road users, and matching service life of communications equipment with automobiles. The group recently had its first meeting t
0 views • 7 slides
Understanding Secure Act 2.0 Key Provisions
In a detailed report by Dee Spivey and Angie Zouhar, key provisions of SECURE Act 2.0 are outlined, including changes in retirement plans like RMD age increase, employee certification of hardship withdrawals, and more. Secure 1.0 and Secure 2.0 differences, effective dates, and necessary actions for
5 views • 12 slides
Introduction to SFTP & PGP Encryption for Secure Data Transfer
Discover how to ensure reliable data transfer, make informed decisions, and gain a strategic advantage through the use of Secure File Transfer Protocol (SFTP) and Pretty Good Privacy (PGP) encryption. The session includes demonstrations on PGP encryption and SFTP access, along with insights on setti
1 views • 22 slides
Ensuring Secure Testing Environments in Oregon Education System
Oregon's Statewide Assessment System (OSAS) emphasizes the critical need for secure testing environments to maintain the validity and accuracy of assessment data. This includes handling secure printed test materials, identifying and preventing improprieties, and reporting any irregularities. From ma
2 views • 20 slides
Fundamentals of Data Communications: Characteristics and Components
Data communications involve the exchange of data between devices through transmission mediums. The effectiveness of a data communications system relies on key characteristics like delivery, accuracy, timeliness, and jitter. The system components include the message, sender, receiver, transmission me
2 views • 63 slides
Secure Computation Techniques in RAM Models with Efficient Automation
Explore the automation of efficient RAM-model secure computation techniques, including examples such as secure binary search. Discover how traditional solutions using circuit abstractions can be improved for sub-linear time computation through methods like Oblivious RAM. Learn about techniques such
0 views • 37 slides
Tamper-Evident Pairing (TEP) Protocol for Secure Wireless Pairing Without Passwords
This article discusses the challenges of traditional secure wireless pairing methods that rely on password validation and proposes the Tamper-Evident Pairing (TEP) protocol as a secure in-band solution to protect against Man-in-the-Middle (MITM) attacks. TEP eliminates the need for out-of-band chann
1 views • 40 slides
Enhancing Privacy and Anonymous Communications with Technology
Explore the world of Privacy Enhancing Technologies (PETs) and Anonymous Communications through the work of George Danezis and his team at UCL. Dive into the challenges of network identity, lack of privacy, and weak identifiers in today's digital landscape. Learn about Ethernet and IP packet formats
0 views • 49 slides
Fundamentals of Data and Computer Communications Explained
In this tutorial, we delve into Chapter 6 of data and computer communications, focusing on transmission overhead calculations, asynchronous and synchronous communication comparisons, CRC computation, and character transmission requirements. Learn about start bits, stop bits, control bits, parity bit
1 views • 12 slides
Actively Secure Arithmetic Computation and VOLE Study
Exploring actively secure arithmetic computation and VOLE with constant computational overhead at Tel Aviv University. Understanding how functions are represented in secure computation using arithmetic circuits over boolean circuits. Efficiently evaluating arithmetic circuits over large finite field
0 views • 36 slides
DirectLOGIC Communications Training Overview
Explore the technical training communications for Do-more DirectLOGIC systems, focusing on setting up communication between DL Servers and Clients using built-in Ethernet ports and ECOM100 modules. Learn about communication configurations, memory allocation, and parameter settings to establish effec
0 views • 28 slides
Accessing and Utilizing CPCSSN Secure Research Environment (SRE)
Learn how to access the CPCSSN Secure Research Environment (SRE) for secure data analysis. Follow steps such as setting up VPN, accessing SQL databases, and establishing ODBC connections for statistical analysis using tools like SAS, R, SPSS, or Stata. Enhance your research capabilities within a sec
0 views • 12 slides
COVID-19 Outbreak Communications Toolkit for Congregate Living Environments
This communications toolkit, developed in collaboration with multiple health organizations, provides guidance and resources for managing communication during a COVID-19 outbreak in congregate living environments. It includes information on processes, notifications, web updates, media relations, key
0 views • 34 slides
Future-Proofing EVSE for Secure Communications in VGI Working Group Proposal
This proposal discusses enabling secure communications between the grid and electric vehicles (EVs) through Evaluation, Additional Option consideration, and concerns over VGI communication protocols. The focus is on developing EVSE capabilities allowing for flexible VGI applications to evolve seamle
0 views • 14 slides
Enhancing Animal Telemetry Data Systems for Secure Collaboration
Wide spectrum of animal telemetry data collection protocols and platforms require enhanced data stewardship options for secure sharing before public release. The need for a more granular understanding of available data and structured systems integration is crucial. Initial workflow involves providin
0 views • 4 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
0 views • 12 slides
Understanding Secure Electronic Transactions (SET)
Secure Electronic Transactions (SET) is an encryption and security specification designed to protect credit card transactions on the Internet. SET provides a secure way to utilize existing credit card payment infrastructure on open networks, such as the Internet, involving participants like clients,
1 views • 6 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Exploring Secure Care Services in Scotland
Delve into the world of secure care services in Scotland, focusing on achievements, challenges, and opportunities in providing youth justice. Learn about trends in secure care, reduction in costs, reasons for referrals, and evidence-based programs like DBT in Glasgow. Gain insights from industry lea
0 views • 77 slides
Understanding Secure PRFs and PRPs in Cryptography
Dive into the world of secure Pseudo-Random Functions (PRFs) and Pseudo-Random Permutations (PRPs) in cryptography. Learn about the definitions, security criteria, and examples of secure PRFs and PRPs such as 3DES and AES. Explore the concepts of secure block ciphers and key principles behind these
0 views • 54 slides
Unlocking Total Value with Hosted Communications for Your Business
Business communications are evolving, with hosted solutions offering more than just cost savings. They provide flexibility, productivity enhancements, and future-proofing benefits for businesses of all sizes. Switching to a hosted communications solution like [Product Name] can lead to immediate cos
0 views • 4 slides
Understanding the Fiduciary Duty Exception to Attorney-Client Privilege
Several courts have deliberated on extending attorney-client privilege to protect communications between law firms' in-house counsel seeking advice on handling potential malpractice claims. This exception, known as the fiduciary duty exception, has faced scrutiny and rejection in recent cases, safeg
0 views • 36 slides
Enhancing Alliance Strategy Implementation through Effective Communications
This internal communications session aims to establish a framework for Secretariat communications to assist Members in strengthening the Alliance. Key focuses include aligning with the 2016-2021 Alliance strategy, identifying potential gaps, and devising strategies to address them for improved colla
0 views • 6 slides
Communicate! Marketing and Communications Committee Amsterdam Meeting Summary September 2015
The meeting of the Communicate! Marketing and Communications Committee in Amsterdam focused on various themes such as clean air, public communications, public acceptance, gas innovation, and marketing campaigns. Members discussed cooperation with the IGU Presidency to support clean air campaigns, ra
0 views • 12 slides
Understanding Sexual Assault Communications Privilege and Balancing Public Interests
Exploring the complexities and practical challenges surrounding Sexual Assault Communications Privilege (SACP), this content delves into the reasons for its establishment, the services it provides, and the implications for both defence lawyers and complainants in sexual assault trials. It sheds ligh
0 views • 19 slides
Partnership Internal Communications Plan & Stakeholder Analysis
Developing an effective internal communications plan for a partnership involves drawing insights from stakeholder analysis, drafting, validating, and implementing the plan. Engaging with internal stakeholders, understanding their awareness, engagement levels, and expectations, and prioritizing commu
1 views • 6 slides
Understanding Satellite Communications and Orbits in Engineering
Exploring the intricacies of satellite communications and orbits in engineering, focusing on special types of inclined orbits, circular orbits, elliptic orbits, and the calculation of eccentricity. Examples such as the International Space Station's orbit are used to illustrate concepts. The content
0 views • 17 slides
Understanding Strategic Communications Planning
This content delves into the intricacies of strategic communications planning, covering topics such as defining communication goals, elements of a communications plan, and the importance of strategy in various arenas. The importance of strategy in connecting purpose, audience, and outcomes is emphas
0 views • 22 slides
Quarterly Overview Report: Feb-April 2016 for NTB Communications
Highlights include successful workshops on communication strategy, website revamp, and monthly communications activities. NTB also provided regular updates through newsletters and board meeting summaries. Various other panui were shared via mail, website, and social media. Barry Caldwell is the main
0 views • 4 slides
Foundations of Cryptography: Secure Multiparty Computation
Explore the foundations of cryptography with insights into secure multiparty computation, including the Secure 2PC from OT Theorem and the Two-Party Impossibility Theorem. Delve into the impossibility of 2-Party Secure MPC, claims, and exercises on extending to statistical security. Learn about redu
0 views • 39 slides
Implementing VPN for Secure Corporate Communication
A Virtual Private Network (VPN) offers a secure method for corporations with multiple sites to transfer data over the Internet while maintaining confidentiality. By encrypting data and using tunneling techniques, VPN software ensures that communications remain private, making it a cost-effective and
0 views • 10 slides
Understanding ICASA Control and Ownership Requirements
In South Africa, the Independent Communications Authority of South Africa (ICASA) regulates the licensing framework for electronic communications services. ICASA's mandate involves establishing licensing frameworks, promoting ownership by historically disadvantaged groups, and supporting black econo
0 views • 14 slides
MOIMS Protocol Viewpoint for SEA Reference Architecture Updates
This content describes the MOIMS Protocol Viewpoint inputs to the SEA Reference Architecture updates by Roger Thompson from ESA SAWG. It includes details about the graphical conventions, data store elements, organizational domains, network layers, communications protocols, and space communications c
0 views • 21 slides
Underwater Light Communications in November 2017
Discusses the advantages of light communications (LC) for underwater use, such as high data rate, low latency, and cost-effectiveness. Contrasts LC with acoustic and RF methods, highlighting benefits and limitations. Explores use cases including communication between submarines, divers, oil platform
0 views • 5 slides
Understanding Secure Messaging and Encryption Techniques
Explore the possibilities of sending secure messages through encryption without the need for advanced degrees in Computer Science or Math. Learn about symmetric and asymmetric key encryption methods, the use of PGP for secure messaging, and the concept of shared-key encryption. Discover the intricac
0 views • 16 slides
Understanding Digital Communications in CTE Department: Concepts and Applications
In the realm of Digital Communications at the CTE Department, delve into a thorough exploration of fundamental principles and practical applications. Concepts such as television signal transmission, binary PCM, quantization levels, code word lengths, transmission bandwidth, signaling rates, and nois
0 views • 8 slides
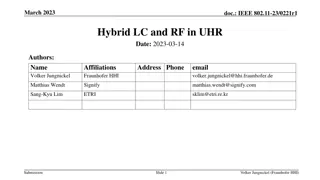
Integration of Light Communications for Enhanced Reliability in Multilink Operations
The presentation discusses the integration of Light Communications (LC) into the Multilink Operation (MLO) framework to enhance reliability and reduce latency in wireless communications. By proposing the incorporation of LC as a new offloading opportunity within the MLO framework, the potential for
0 views • 15 slides