Civil War Causes and Key Figures: Divines of the North and South
Explore the relationships and events leading up to the Civil War, including the disparity between North and South, the Kansas-Nebraska Act, popular sovereignty, the Dred Scott Case, John Brown's Raid, and President Lincoln's efforts to preserve the Union. Dive into economic, political, and social di
0 views • 23 slides
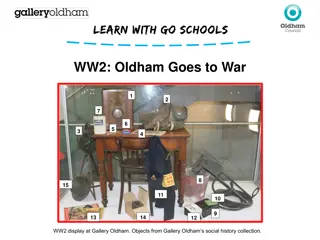
WW2: Oldham Goes to War Display at Gallery Oldham
Explore the WW2 display at Gallery Oldham showcasing objects from the social history collection, including a radio set, air raid siren, infant respirator, ration books, powdered milk tin, ARP insignia badges, and more. Discover how these artifacts played a crucial role during wartime, from maintaini
2 views • 7 slides
Resolving QuickBooks Event ID Log Error 4
Learn how to resolve QuickBooks Event ID Log Error 4 with our comprehensive guide. This detailed resource provides step-by-step solutions to address this common issue, ensuring your QuickBooks functions smoothly. Discover how to identify the root causes of Event ID Log Error 4, from file corruption
1 views • 4 slides
How to Restore deleted Invoice in Quickbooks Online?
How to Restore deleted Invoices in Quickbooks Online?\nRestoring a deleted invoice in QuickBooks Online involves using the Audit Log to track and recreate it. First, access the Audit Log via the Gear icon under \"Tools\" and identify the deleted invoice details. Then, manually recreate the invoice b
1 views • 7 slides
Efficient Log Analysis and Data Reduction Using AWK
Learn how AWK and regex can streamline log analysis and data reduction tasks, saving you time and effort compared to manual methods like Excel. Discover how these tools excel at parsing columns of data, enabling advanced lexical analysis and efficient comparison of log files.
0 views • 15 slides
Workforce Ready (New Kronos) Log-in Instructions & Resources for Assistance
Comprehensive log-in instructions for Workforce Ready (New Kronos), including steps for web and mobile access, as well as resources for further assistance and training materials. Users can log in using their regular Doane credentials and follow the provided guidance. For additional help, resources,
0 views • 5 slides
Comprehensive RAID Log Presentation and Management Overview
This comprehensive presentation template provides a detailed overview of a RAID log, including risks, issues, threats, assumptions, dependencies, and reliance factors. It offers insights on tracking and managing different aspects of project planning and execution, categorized by risk levels. The bre
0 views • 6 slides
Understanding RAID Technology in DBMS: Redundancy and Performance
This content provides insights into RAID technology, discussing the combination of reliability and performance in managing multiple disks through various RAID levels like RAID 0, RAID 1, RAID 2, RAID 3, RAID 4, and RAID 5. It explores the advantages of RAID, such as data striping, mirroring, bit int
0 views • 61 slides
The Impact of John Brown's Raid on Harper's Ferry in 1859
John Brown's raid on Harper's Ferry in 1859 was an attempt to incite a slave rebellion and abolish slavery. Brown believed in the righteousness of his cause, but his actions sparked national debate and differing reactions. While some saw him as a martyr for freedom, others viewed him as a radical ex
2 views • 9 slides
Understanding Erasure Coding in Storage Systems
Erasure Coding is a data storage technique that enhances fault tolerance by breaking files into chunks and generating additional pieces for reconstruction. This technology, exemplified by systems like Ceph, offers more robust data protection than traditional methods like RAID or replication. Erasure
0 views • 10 slides
Overview of Mass Storage Systems in Computer Engineering
Mass storage in computer engineering involves secondary and tertiary storage devices like magnetic disks and tapes, providing permanent storage for large volumes of data. The structure, performance characteristics, and operating system services for mass storage are discussed, including RAID and HSM.
9 views • 77 slides
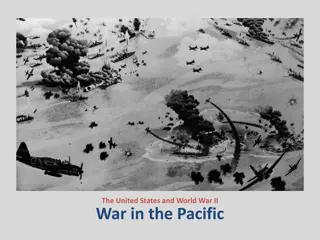
World War II in the Pacific: Unfolding of Events Post Pearl Harbor Attack
The war in the Pacific escalated post the Pearl Harbor attack with Japan's domination over various territories, including the Philippines leading to significant battles like the Japanese Invasion of the Philippines and Doolittle's Raid. American strategy, led by figures like Gen. MacArthur, played a
0 views • 12 slides
Understanding Storage Systems Dependability
This content discusses storage systems dependability, covering topics such as data reliability, fault-tolerant techniques, error detection and correction, component levels, disk protection techniques, types of disk faults, and protection mechanisms like RAID and ECC. It provides insights into ensuri
1 views • 25 slides
The Impact of John Brown's Raid on Harper's Ferry
John Brown's raid on Harper's Ferry in 1859 was a pivotal event that escalated tensions between the North and South in the lead-up to the Civil War. Brown's failed attempt to arm enslaved individuals and spark a revolt had far-reaching consequences, leading to heightened sectional tensions and a gre
0 views • 7 slides
Advanced Techniques for Heavy Hitters Detection in Insertion Streams
Beating CountSketch algorithms, like those presented by David P. Woodruff and team, offer innovative solutions for identifying heavy hitters in insertion streams with minimal space complexity. Guarantees such as L1 and L2 outputs and the CountSketch approach are explored to achieve efficient heavy h
0 views • 18 slides
John Brown's Role in Escalating Tensions Towards the Civil War
Explore John Brown's pivotal role in the lead-up to the Civil War through his radical abolitionist actions, including the violent events in Bleeding Kansas and his infamous raid on Harper's Ferry. Brown's staunch anti-slavery stance and militant tactics further polarized the nation on the issue of s
0 views • 9 slides
Practical Strategies for Digital Preservation at IWU
Explore digital preservation strategies in practice at Illinois Wesleyan University. Learn from Meg Miner, the University Archivist, about preservation philosophy, local-centric decisions, and the importance of prioritizing digital collections inventory. Gain insights into updates on processing acti
0 views • 33 slides
Comprehensive RAID Log Presentation Template
This comprehensive presentation template includes a RAID log with risks, assumptions, issues, and dependencies structured in a professional layout. Utilize this template to effectively manage project risks and dependencies. The template also features a simple RAID log slide template for a clear over
0 views • 7 slides
Understanding Redundant Arrays of Inexpensive Disks (RAID)
This informative material discusses the concept of RAID, its various levels such as RAID 0, 1, and 2, their advantages and disadvantages, and the motivation behind implementing RAID systems. It highlights the need for data redundancy, disk throughput optimization, and reliable storage solutions usin
0 views • 30 slides
Elastic Parity Logging for SSD RAID Arrays
SSDs are widely used for their performance and efficiency, but face challenges like flash errors and poor random write performance. The paper introduces EPLog, a new RAID design for SSD arrays, enhancing reliability, endurance, and performance through elastic parity logging. The solution redirects w
0 views • 23 slides
Evolution of Indian-White Relations: Raid or Trade?
The article discusses how Indian-White relations transitioned from cooperation to conflict over time, exploring the factors influencing negotiation outcomes versus violent confrontations. The model presented highlights the role of property rights, informational asymmetry, military technology, and th
0 views • 4 slides
Overview of Distributed Systems, RAID, Lustre, MogileFS, and HDFS
Distributed systems encompass a range of technologies aimed at improving storage efficiency and reliability. This includes RAID (Redundant Array of Inexpensive Disks) strategies such as RAID levels, Lustre Linux Cluster for high-performance clusters, MogileFS for fast content delivery, and HDFS (Had
0 views • 23 slides
Enhancing Data Storage Reliability with High-Parity GPU-Based RAID
The research discusses the challenges faced by traditional RAID systems in maintaining data reliability and proposes a solution using High-Parity GPU-Based RAID. It highlights the limitations of current technologies in fault tolerance, the inaccuracies in disk failure statistics, and the significanc
1 views • 13 slides
Understanding RAID: A Case for Redundant Arrays of Inexpensive Disks
Delve into the world of Redundant Arrays of Inexpensive Disks (RAID) exploring its evolution, motivation, and various RAID levels like RAID 1, RAID 2, RAID 3, and RAID 4. Discover the importance of data redundancy and fault tolerance in storage systems.
0 views • 17 slides
Ecuadorian Diplomatic Crisis: The Raid on Mexico's Embassy and Its Global Impact
Ecuadorian police raid Mexico's embassy in Quito, arresting former Vice-President Jorge Glas. Mexico grants him asylum, leading to a diplomatic standoff. The incident reflects political tensions between the countries and raises concerns about adherence to diplomatic norms. Regional powers condemn Ec
0 views • 5 slides
Understanding RAID 5 Technology: Fault Tolerance and Degraded Mode
RAID 5 is a popular technology for managing multiple storage devices within a single array, providing fault tolerance through data striping and parity blocks. This article discusses the principles of fault tolerance in RAID 5, the calculation of parity blocks, handling degraded mode in case of disk
0 views • 12 slides
Understanding Storage Devices in Computer Systems
This content provides an in-depth look at storage devices used in computer systems, covering topics such as hard drives, RAID, SSDs, addressing and geometry of hard drives, disk interfaces, types of delays with disks, and how to calculate transfer time. It explores the components, functionalities, a
0 views • 62 slides
NVDIMM High-Level Use Cases Overview
Explore various high-level use cases for NVDIMM technology, including local NVDIMM kernel access, SW RAID configurations, and NVDIMM utilization in both public and private cloud environments. These scenarios involve accessing, caching, and replicating data using NVDIMMs to enhance memory performance
0 views • 10 slides
Central Log Service & IT Policies Overview
Central Log Service (CLS) is a university service for storing and analyzing log information, operated by the Division of IT Network Infrastructure and Services Monitoring team. The service provides a centralized location for log storage, analysis tools, and real-time indexing capabilities. IT Loggin
1 views • 7 slides
Evacuation and Adventure: Journey through the Wardrobe
Amid the backdrop of air raid sirens, evacuation, and a mysterious wardrobe, follow Lucy's journey as she delves into unexpected discoveries waiting on the other side. What secrets lie within the old professor's house, and what will Lucy find as she ventures deeper into the unknown?
1 views • 50 slides
Satchel.One Pupil Guide: Log in via the App at Knightswood Secondary School
A step-by-step guide for pupils to log in to Satchel.One (formerly Show My Homework) app at Knightswood Secondary School. Learn how to download the app, search for the school, log in via RM Unify, and enter your Glow username and password with helpful images.
0 views • 6 slides
I/O-Efficient Protection Against Silent Data Corruptions in RAID Arrays
This paper discusses the risks of silent data corruptions in RAID arrays, which are challenging to detect and can lead to serious consequences. It presents the concept of integrity protection to enhance RAID systems' ability to detect and recover from such corruptions efficiently. The paper investig
0 views • 26 slides
Versatile Tests for Comparing Survival Curves Based on Weighted Log-Rank Statistics
Overview of various statistical tests for comparing survival curves beyond the traditional log-rank test. The focus is on weighted log-rank statistics sensitive to non-proportional hazards scenarios, with examples and methodologies discussed. These tests aim to provide more nuanced insights into dif
0 views • 31 slides
How to Synchronize EPPO Data with Log Shipping
EPPO provides multiple files in XML format, and it is challenging to update data in a SQLite database. Log shipping is a technique for replicating a database to another instance by copying transaction log files. Follow steps to set up log shipping on the EPPO Data services portal for efficient data
0 views • 8 slides
Understanding 4-Log Virus Treatment and Groundwater Rule Compliance
This collection of images and information delves into the importance of 4-log virus treatment under the Groundwater Rule, regulatory requirements for groundwater systems, the basics of Ct calculations for disinfection, types of disinfectants used, and understanding log inactivation of viruses. The c
0 views • 24 slides
Development of Log Data Management System for Monitoring Fusion Research Operations
This project focuses on creating a Log Data Management System for monitoring operations related to MDSplus database in fusion research. The system architecture is built on Big Data Technology, incorporating components such as Flume, HDFS, Mapreduce, Kafka, and Spark Streaming. Real-time and offline
0 views • 6 slides
Utilizing Topic Modeling for Identifying Critical Log Lines in Research
By employing Topic Modeling, Vithor Bertalan, Robin Moine, and Prof. Daniel Aloise from Polytechnique Montréal's DORSAL Laboratory aim to extract essential log lines from a log parsing research. The process involves building a log parser, identifying important log lines and symptoms, and establishi
0 views • 18 slides
Importance of Logging and Auditing in Cybersecurity
Discussing the significance of logging and auditing in cybersecurity, emphasizing the need for both a priori and a posteriori techniques to prevent security violations. Logging helps record events for system analysis, while auditing involves analyzing log records to provide understandable system inf
0 views • 32 slides
Quantum Space-Bounded Complexity in Logarithmic Space: A Comprehensive Overview
Quantum space-bounded complexity explores the memory requirements for solving problems in log space. Examples include matrix multiplication, undirected graph connectivity, and problems like inverting matrices and determining connectivity. The significance of deterministic log space (NL) and nondeter
0 views • 49 slides
Raft: A Consensus Algorithm for Replicated Logs Overview
Raft is a consensus algorithm developed by Diego Ongaro and John Ousterhout at Stanford University. It aims to ensure replicated log clients and consensus modules maintain proper log replication and state machine execution across servers. Raft utilizes leader election, normal operation for log repli
0 views • 31 slides