Understanding Floods: Major Hazards and Disasters in Environmental Geography and Disaster Management
Floods, a common natural disaster, are often caused by factors like intense rainfall, river overflow, and human activities. Regions in India, such as Assam and Bihar, face significant loss due to recurrent floods. Factors like skewed rainfall patterns and transnational rivers contribute to the flood
0 views • 15 slides
Understanding Primary Clarifiers in Wastewater Treatment
Primary clarifiers are crucial components designed to remove particles with specific settling rates from wastewater. They come in rectangular and circular designs, each with typical dimensions and performance data for BOD and TSS removal. Understanding the design parameters like detention time, over
0 views • 15 slides
IEEE 802.11-20/1238r5 August 2020 Preamble Design Open Issues
In these slides, designs for U-SIG content & overflow and EHT-SIG design are proposed. The focus is on punctured channel indication design with the aim of conveying puncturing patterns efficiently while keeping signaling overhead low. The proposal includes a 6-bit field for puncturing information, a
1 views • 41 slides
Understanding the FLAGS Register in Assembly Language
An exploration of the FLAGS register in assembly language, highlighting the key status flags such as Carry Flag (CF), Parity Flag (PF), Auxiliary Carry Flag (AF), Zero Flag (ZF), Sign Flag (SF), and Overflow Flag (OF). These flags play a crucial role in reflecting the outcome of operations within th
1 views • 24 slides
Understanding Flag Registers in Microprocessor 8086
This content discusses the flag registers in the Microprocessor 8086, covering conditional flags such as Carry Flag (CF), Auxiliary Flag (AF), Parity Flag (PF), Zero Flag (ZF), Sign Flag (SF), and Overflow Flag (OF), as well as control flags including Trap Flag (TP), Interrupt Flag (IF), and Directi
1 views • 23 slides
IEEE 802.11-20/0029r3 Preamble Structure and SIG Contents Overview
The document dated January 2020 discusses the preamble structure and SIG contents, focusing on EHT-SIG in IEEE 802.11-20/0029r3 amendment. It covers the introduction of U-SIG, EHT-SIG format, EHT.PPDU types, and EHT-SIG design for MU PPDU. The discussion includes the necessity of accommodating overf
3 views • 22 slides
Understanding Buffer Overflow Attacks at Carnegie Mellon
Learn about the Carnegie Mellon 15-213 Recitation Attack Lab, where you can hijack programs using buffer overflow attacks. Gain insights into stack discipline, stack frames, and defeating secure programs through return-oriented programming. Dive into topics like stack smashing attacks, buffer overfl
8 views • 24 slides
IEEE 802.11-20/1238r1 Preamble Design Open Issues
Proposed designs addressing preamble design issues in IEEE 802.11-20/1238r1 include U-SIG content and overflow for Unified SU/MU PPDU, EHT-SIG design, and punctured channel indication. The focus is on conveying puncturing patterns efficiently while minimizing signaling overhead. The design features
5 views • 32 slides
Overview of 8086 Assembly Language Arithmetic Operations
The 8086 assembly language provides instructions for arithmetic operations such as addition, subtraction, and comparison. These operations are essential for manipulating data in memory and registers. The instructions support various operand types, including registers, memory locations, and immediate
0 views • 24 slides
Understanding Floods: Types, Causes, and Impacts
Floods are a natural hazard resulting from various factors like heavy rainfall, river bank overflow, or dam failure. They lead to land submergence and occur worldwide, causing significant economic losses. This article explores different types of floods, including precipitation and non-precipitation
1 views • 14 slides
Understanding Arithmetic Operations for Computers
The chapter delves into the fundamentals of arithmetic for computers, covering operations on integers, dealing with overflow, handling floating-point real numbers, and more. It explores addition, subtraction, multiplication, and division in detail, showcasing examples and techniques for efficient co
4 views • 18 slides
Understanding Buffer Overflow Vulnerabilities in Programming
Buffer overflow vulnerabilities pose serious security threats by allowing attackers to execute arbitrary code on victim machines. This issue arises from overwriting memory in a way that manipulates the program's behavior. Learn about the dangers of buffer overflow bugs, how they can be exploited, an
2 views • 33 slides
Software Security Principles and Practices: Enhancing Program Code Security
Understanding and addressing critical web application security flaws like unvalidated input, cross-site scripting, buffer overflow, injection flaws, and improper error handling is crucial in enhancing the security of program code. The NIST report NISTIR 8151 provides valuable recommendations to redu
2 views • 44 slides
Understanding Computer Security and Software Vulnerabilities
Computer security, also known as cybersecurity or IT security, encompasses the protection of information systems from theft and damage. This overview delves into software security, control-flow attacks, memory vulnerabilities, and the historical impact of events like the Morris Worm. Various aspects
0 views • 53 slides
Buffer Overflow: Understanding, Defenses, and Detection
Dive into the world of buffer overflow attacks with insights on understanding the concept, implementing defenses, and detecting stack smashing using techniques like canary values. Discover how to protect against vulnerabilities and grasp the significance of elements such as EIP, ASLR, DEP, and NX bi
0 views • 10 slides
Understanding Memory Layout in Computer Systems at Carnegie Mellon
Explore the memory layout in computer systems through the lens of Carnegie Mellon University's advanced topics in machine-level programming. Learn about buffer overflow vulnerability protection, memory allocation examples, x86-64 Linux memory layout, and addressing schemes. Dive into practical examp
2 views • 47 slides
The Magic Porridge Pot - A Magical Tale of Good Intentions
Once upon a time, a kind girl named Poppy received a magic porridge pot from an old lady. Excitedly, she brought it home and shared its wonders with her mother. However, a mishap occurred when she forgot the pot's stopping words, causing porridge to overflow everywhere. This delightful story teaches
0 views • 11 slides
Prepare and Stay Safe: A Comprehensive Guide for Earthquake Preparedness
This comprehensive guide covers various aspects of earthquake preparedness, including potential risks, necessary precautions, and steps to take during and after an earthquake. It emphasizes the importance of personal, family, and community preparedness, along with valuable insights on how to reduce
0 views • 102 slides
Understanding Heap Overflow Attacks
A heap is a collection of variable-size memory chunks managed by the program. Heap overflow attacks occur when malicious actors corrupt heap memory, potentially allowing them to overwrite data and execute arbitrary code. This poses a significant security risk. The process involves manipulating heap
2 views • 19 slides
Insights on Overflow through the Western Valley of the Iceland-Faroe Ridge
Research by Bogi Hansen, Karin M. H. Larsen, Steffen Olsen, Detlef Quadfasel, Kerstin Jochumsen, and Svein Østerhus delves into the negligible overflow through the Western Valley of the Iceland-Faroe Ridge. Various field experiments and data analyses demonstrate minimal flow through the Western Val
0 views • 12 slides
Role of Sugar Industry in Circular Economy - Case Study on Spray Pond Overflow Treatment
The two-day summit organized by Mahatma Phule Krushi Vidhyapeet Krushi Mahavidhyalaya, Pune, in collaboration with various organizations, focused on the significant role of sugar and allied industries in promoting circular economy and sustainability. The event highlighted the necessity of treating s
0 views • 15 slides
Understanding Interrupts in Computer Systems
Interrupts in computer systems play a crucial role in handling various events and managing the flow of instructions. This content discusses the types of interrupts, causes, handling procedures, and the role of supervisory modes in modern computers. It covers topics such as internal and external inte
0 views • 29 slides
Reliable Liquid Filling Machine Manufacturers in India for Optimized Production
Explore advanced liquid filling machine manufacturers in India, such as Authentic Designers, offering top-quality solutions for industries. With machines like overflow, piston, and liquid filling machine manufacturer in India, these manufacturers ens
0 views • 10 slides
Introduction to Poetry Analysis: Techniques and Approaches" (66 characters)
Delve into the world of poetry analysis with key insights on understanding the poet's craft, approaching unseen poems confidently, and identifying literary devices to unravel thematic content. Explore how to analyze poems effectively using the ART WARS framework and break free from common misconcept
0 views • 12 slides
Apple iOS 4 Security Evaluation - Insights on Code Signing and Exploitation Prevention
Dino A. Dai Zovi's paper on Apple iOS 4 Security Evaluation reveals insights into vulnerabilities like buffer overflow attacks and the effectiveness of security measures such as Address Space Layout Randomization and Code Signing Enforcement. Learn about the importance of Trust Certificates and how
1 views • 12 slides
Overcoming Writer's Block: Strategies and Techniques for Creative Inspiration
Explore diverse methods to combat writer's block including diagnosing the type of block, generating ideas, dealing with an overflow of ideas, initiating writing, outlining effectively, dealing with being stuck, and managing boredom or stress. Discover helpful tips from understanding assignments to o
0 views • 12 slides
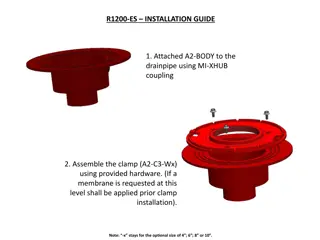
R1200-ES Installation Guide
The R1200-ES Installation Guide provides detailed instructions for attaching A2-BODY to the drainpipe, assembling clamps, installing ABS nipples, adjusting height, applying insulation membrane, securing clamps, attaching the dome, and setting up overflow. The guide includes images for reference at e
0 views • 4 slides
Understanding Buffer Overflow in Computer Programming
This content delves into the intricacies of buffer overflow vulnerabilities in computer programming, showcasing real-world examples such as the Internet Worm and IM War incidents. It covers topics like stack buffer overflow exploits, Unix function implementations prone to buffer overflow, and the re
1 views • 35 slides
Understanding Memory Layout and Allocation in Computer Systems at Carnegie Mellon University
Exploring the memory layout and allocation in computer systems through lectures at Carnegie Mellon University, focusing on topics such as buffer overflow vulnerability protection, unions, shared libraries, stack, heap, data locations, addresses, and practical memory allocation examples. The content
1 views • 55 slides
Overflowing Blessings in 2017: A Message of Abundance and Joy
Prepare to receive an abundant overflow of blessings, joy, and favor as you trust in the promises of God from Psalm 23:5 and Malachi 3:10. Through prayer and seeking the Lord's strength, move towards a life of abundance and fulfillment, leaving behind scarcity and embracing a season of more than eno
0 views • 27 slides
Analysis of Wordsworth's Preface to Lyrical Ballads
William Wordsworth's Preface to Lyrical Ballads serves as a manifesto for the Romantic movement, emphasizing the use of common language and the expression of emotion in poetry. Wordsworth defines poetry as the spontaneous overflow of powerful feelings, rooted in contemplation rather than mere sponta
0 views • 10 slides
Practical Approach to Year 2038 Problem for 32-bit Embedded Systems
A research study conducted at Osaka University addresses the Year 2038 problem in 32-bit embedded systems, discussing the potential time value issues and digit overflow that may occur. The study presents methods and outcomes to tackle this problem, highlighting the significance of handling time_t va
0 views • 39 slides
Understanding Unix/Linux Hacking Techniques
Explore Unix/Linux hacking techniques including footprinting, scanning, enumeration, vulnerability mapping, remote access, data-driven attacks, buffer overflow, input validation, and countermeasures. Discover methods to gain root access, exploit vulnerabilities, perform brute force attacks, and secu
0 views • 6 slides
Smart Bathtub Vulnerabilities and Remote Control Risks
Explore the risks associated with a remote-controlled bathtub controlled via a smartphone app, including vulnerabilities in controlling water flow, water level sensing, and potential overflow scenarios. Learn how attackers could manipulate signals wirelessly and the likelihood of causing the bathtub
0 views • 38 slides
Understanding Buffer Overflow in C and C++ Programs
Buffer overflow is a common vulnerability in C and C++ programs where the allocated memory buffer is overwritten, causing unpredictable behavior. This vulnerability allows attackers to exploit the program by injecting malicious code. The lack of automatic bounds checking in these languages makes it
0 views • 6 slides
Understanding Stack Buffer Overflow Vulnerabilities
Stack buffer overflow is a critical security issue caused by writing more data to a buffer than allocated, leading to bugs, crashes, and potential attacks. This vulnerability, exemplified by the Twilight Hack, allows executing arbitrary code. Learn about its causes, implications, and mitigation stra
0 views • 7 slides
Buffer Overflow Attack and Vulnerable Programs
Understanding buffer overflow attacks and vulnerable programs, the consequences of such attacks, how to run malicious code, and the setup required for exploiting vulnerabilities in program memory stack layouts. Learn about creating malicious inputs (bad files), finding offsets, and addressing shellc
0 views • 36 slides
Understanding Buffer Overflow in Stack: SEED Workshop Lab
This content provides a comprehensive overview of buffer overflow in stack focusing on SEED Workshop Lab scenarios. It covers principles, practice, high-level pictures, program memory layout, function stack layout, function call chains, vulnerable program examples, and more. Through detailed images
0 views • 34 slides
Understanding Stack Overflow Vulnerabilities and Exploitation Techniques
Explore the history of stack overflow vulnerabilities, learn how to control a PC using stack overflow, place shellcode in memory, calculate shellcode addresses, and execute shellcode. Understand different types of overflows including stack overflow, heap overflow, and integer overflow. Delve into th
0 views • 33 slides
Understanding CSS Float, Positioning, and Clear Properties
CSS Float property allows elements to float to the left, right, or none (default), affecting the flow of text around them. Positioning elements using float can be tricky, especially when setting widths. The clear property prevents overlapping floated elements. Addressing common errors like container
0 views • 15 slides