Costing Out Approaches
Costing out approaches and studies have been developed to ensure schools and districts have adequate resources to meet state education standards. Implementing these approaches involves professional judgment, evidence-based benchmarks, and data requirements. Using multiple approaches allows for trian
0 views • 12 slides
Apache MINA: High-performance Network Applications Framework
Apache MINA is a robust framework for building high-performance network applications. With features like non-blocking I/O, event-driven architecture, and enhanced scalability, MINA provides a reliable platform for developing multipurpose infrastructure and networked applications. Its strengths lie i
3 views • 13 slides
Modeling and Generation of Realistic Network Activity Using Non-Negative Matrix Factorization
The GHOST project focuses on the challenges of modeling, analyzing, and generating patterns of network activity. By utilizing Non-Negative Matrix Factorization (NMF), realistic network activity patterns can be created and injected into live wireless networks. Understanding and predicting user behavi
4 views • 28 slides
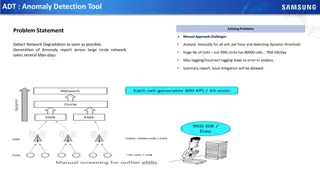
Automated Anomaly Detection Tool for Network Performance Optimization
Anomaly Detection Tool (ADT) aims to automate the detection of network degradation in a mobile communications network, reducing the time and effort required significantly. By utilizing statistical and machine learning models, ADT can generate anomaly reports efficiently across a large circle network
8 views • 7 slides
Revolutionizing Network Management with Intent-Based Networking
Explore the concept and benefits of Intent-Based Networking (IBN) in simplifying network configuration and enhancing efficiency. Learn how IBN automates network operations, aligns with business objectives, improves security, and ensures scalability and reliability. Discover the potential of IBN tool
0 views • 14 slides
Modern Approaches in Political Science: Overview and Characteristics
Explore modern approaches in political science pioneered by intellectuals to address the limitations of traditional methods. These approaches emphasize empirical data, interdisciplinary study, and scientific methods to draw conclusions beyond political structures and historical analysis. Key modern
1 views • 13 slides
Network Compression Techniques: Overview and Practical Issues
Various network compression techniques such as network pruning, knowledge distillation, and parameter quantization are discussed in this content. The importance of pruning redundant weights and neurons in over-parameterized networks is highlighted. Practical issues like weight pruning and neuron pru
0 views • 37 slides
Modernizing Network Security with nQUIC Noise-Based Packet Protection
Explore the evolution of network security mechanisms through nQUIC Noise protocol, comparing it against traditional HTTPS stack. Delve into the secure transmission aspects of TCP/IP, TLS, and the innovative approaches of QUIC protocol, emphasizing the significance of securing protocols with TLS in m
2 views • 119 slides
Network Slicing with OAI 5G CN Workshop Overview
Overview of Network Slicing with OAI 5G CN workshop focusing on the crucial role of network slicing in realizing the service-oriented 5G vision. This workshop covers topics like multiple logical networks creation on shared infrastructure, different types of network slices, preparation and instantiat
1 views • 6 slides
Understanding Models of Postgraduate Supervision and Different Supervisory Approaches
Explore the various roles, styles, and models of postgraduate supervision, delving into the distinctions between supervisor tasks, interaction approaches, and supervision structures. Learn how different supervision models like one-on-one, panel, project, and doctoral programme supervision impact res
1 views • 13 slides
Network Design Challenges and Solutions in Business Data Communications
Issues in designing a Local Area Network (LAN) include needs analysis, technological design, and cost assessment. The traditional approach involves structured systems analysis, but faces challenges due to rapidly changing technology and increasing network traffic. The Building Blocks Approach recomm
1 views • 20 slides
Approaches to Study Comparative Politics: Traditional vs. Modern Perspectives
This chapter discusses the importance of approaches in the study of comparative politics, categorizing them into traditional and modern perspectives. Traditional approaches include philosophical, historical, and traditional institutional approaches, highlighting their strengths and limitations. Mode
0 views • 7 slides
Understanding 5G RAN Network Slicing and Architecture
Explore the intricate world of 5G Radio Access Network (RAN) and Network Slicing, delving into concepts such as SO Service Orchestrator, SDN-C Service Design, and Core Network Elements. Discover the significance of managing and designing mobile slice services, including eMBB, Massive IoT, and Missio
0 views • 26 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
Understanding Word Sense Disambiguation: Challenges and Approaches
Word Sense Disambiguation (WSD) is a complex task in artificial intelligence that aims to determine the correct sense of a word in context. It involves classifying a word into predefined classes based on its meaning in a specific context. WSD requires not only linguistic knowledge but also knowledge
2 views • 12 slides
Data Flows and Network Challenges in Particle Physics Infrastructure
This overview delves into the data flows and network challenges faced in particle physics infrastructure, focusing on the JUNO project. It discusses the process of data reception, storage, and replication across various data centers, highlighting the bidirectional nature of data flows. Additionally,
0 views • 24 slides
Understanding Devices and Network Security Implementation
This content discusses the installation and configuration of network components to enhance organizational security. It covers topics such as intrusion detection systems (IDS), different types of IDS approaches, passive and active responses to intrusions, and using hubs to attach network-based IDS. T
0 views • 13 slides
Emerging Trends in Network Design and Verification
Explore the evolution of network design from manual configurations to custom networks and software-defined solutions. Discover the challenges facing current networks and the potential for optimizing network performance through innovative approaches like P4 and SDNs. Delve into the intersection of di
0 views • 45 slides
Progress of Network Architecture Work in FG IMT-2020
In the Network Architecture Group led by Namseok Ko, significant progress has been made in defining the IMT-2020 architecture. The work has involved gap analysis, draft recommendations, and setting framework and requirements. Phase 1 focused on identifying 19 architectural gaps, such as demands for
1 views • 11 slides
Understanding Interconnection Networks Topology
Exploring the topology of interconnection networks helps determine the arrangement of channels and nodes, impacting network cost, performance, latency, energy consumption, and complexity of implementation. Abstract metrics such as degree, hop count, and network diameter play crucial roles in evaluat
1 views • 56 slides
Transportation Network Modeling and Analysis with C.Coupled SE Platform
This content outlines the features and functionalities of the C.Coupled SE Platform (CSET Platform) developed by the Connetics Transportation Group. It covers aspects such as interface design, inputs merging, purposes, platform development using Cube, TAZs merging, and network attributes. The platfo
0 views • 11 slides
Human Disease Symptom Network: Understanding Disease Relationships Through Symptoms and Genes
The Human Disease Symptom Network (HSDN) is constructed using a large-scale medical bibliographic records database to form a network of human diseases based on symptom similarities. By integrating disease-gene associations and protein-protein interaction data, correlations between symptom similarity
0 views • 37 slides
Introduction to Network Analysis Using .NET
This presentation introduces the concept of network analysis using .NET in the humanities classroom. It provides a template for teaching and adapting network analysis tools for educational purposes. The guide explains the relevance of networks in processing and visualizing data, emphasizing the coll
0 views • 20 slides
Meridian: An SDN Platform for Cloud Network Services
Meridian is an SDN platform developed by Mohammad Banikazemi, David Olshefski, Anees Shaikh, John Tracey, and GuohuiWang at IBM T. J. Watson Research Center. The platform focuses on providing cloud network services efficiently. It encompasses an architecture that enables faster and more convenient n
0 views • 21 slides
Network Coordinate-based Web Service Positioning Framework for Response Time Prediction
This paper presents the WSP framework, a network coordinate-based approach for predicting response times in web services. It explores the motivation behind web service composition, quality-of-service evaluation, and the challenges of QoS prediction. The WSP framework enables the selection of web ser
0 views • 30 slides
Enhancing Network Security with Software-Defined Snort and OpenFlow
Explore the implementation of Snort, Barnyard, and PulledPork within a Software-Defined Network framework using OpenFlow technology. Learn how these tools enhance network security through intrusion detection engines, rule management, and network traffic control mechanisms. Dive into the architecture
0 views • 15 slides
Workshop Evaluation - Project READ Literacy Network
Workshop evaluation presented by Jane Tuer and Lisa McArthur from Project READ Literacy Network in June 2014. The workshop focused on introducing the LMA project to develop a screening tool, different approaches to discussing literacy with clients, how LBS programs can meet client needs, and practic
0 views • 77 slides
Understanding Network Metrics Through Centrality Analysis
This presentation introduces network metrics as tools to describe network characteristics and answer important questions. Using centrality metrics as an example, participants learn how to identify the most important nodes in a network based on different criteria such as degree centrality and closene
0 views • 15 slides
Understanding Project Network and Plan Development
The process of developing a project plan involves creating a project network that outlines the sequence, interdependencies, and timings of activities. This network acts as a guide for scheduling, estimating duration, budgeting, and highlighting critical tasks. The construction of a project network i
0 views • 38 slides
Understanding Cellular Network Performance in User Context
Explore the importance of capturing in-context measurements of cellular network performance, including factors to consider, existing approaches, use cases, and empirical studies. Learn how network data, controlled experiments, and active measurements contribute to enhancing user experience.
0 views • 27 slides
PhD in Telematics Engineering: Traffic Prediction with Big Data Technologies
This PhD study focuses on traffic prediction using Big Data technologies within Software-Defined Networking (SDN). It explores the separation of data and control planes in SDN architectures, emphasizing the benefits of centralized control for network operations. Additionally, the study delves into t
0 views • 33 slides
Understanding Mobility in Wireless and Mobile Networks
Explore the vocabulary and approaches related to mobility in wireless and mobile networks. Understand concepts such as home network, home agent, permanent address, visited network, care-of-address, and more. Learn about different mobility approaches and the registration process in these networks.
0 views • 17 slides
Understanding Network Analysis: Whole Networks vs. Ego Networks
Explore the differences between Whole Networks and Ego Networks in social network analysis. Whole Networks provide comprehensive information about all nodes and links, enabling the computation of network-level statistics. On the other hand, Ego Networks focus on a sample of nodes, limiting the abili
0 views • 31 slides
Understanding Network Interference in CS590B/690B Lecture
Delve into the realm of network interference through the CS590B/690B lecture with Phillipa Gill at UMass Amherst. Explore topics such as Internet routing, timing attacks, BGP hijacks, Tor network functionality, relay selection, collusion scenarios, use of guards, web site fingerprinting attacks, tra
0 views • 11 slides
Approaches to Variance Estimation in Social Policy Research
This lecture discusses approaches to estimating sampling variance and confidence intervals in social policy research, covering topics such as total survey error, determinants of sampling variance, analytical approaches, replication-based approaches, and the ultimate cluster method. Various methods a
0 views • 34 slides
Contribution of HALA Network to ATM Community and SESAR 2020: Achievements and Future Directions
HALA network has been instrumental in fostering research and innovation in the field of automation for ATM systems, providing a platform for knowledge dissemination, collaboration, and advancement. The network has facilitated exploratory research, encouraged young scientists' participation, and crea
0 views • 12 slides
Exploring Network Slicing in Future 5G Networks
The research delves into the design of a 5G-ready architecture known as NFV-based Network Store, aiming to serve as a digital distribution platform for 5G applications. By focusing on network slicing and programmability, the architecture enhances resource efficiency and agility in deploying software
0 views • 17 slides
Network Function Virtualization (NFV) Overview
Network Function Virtualization (NFV) focuses on virtualizing network functions to improve efficiency and reduce costs in network infrastructure. The lecture discusses key readings, devices that compose a network, specialization of devices, benefits of one-device-does-anything approach, and the goal
0 views • 21 slides
Enhancing Network Stability with Network Monitoring Systems
Network monitoring is crucial for efficient management and proactive issue detection in a network environment. Factors influencing an effective network system include choosing the best OEM, SLA agreements, and selecting a reliable System Integrator. Reactive monitoring can lead to financial losses a
0 views • 12 slides
Dell Network Consulting Services Overview
Dell Network Consulting provides expert insights and workshops to enhance your network infrastructure's efficiency. Services include network assessments, topology discovery, traffic analysis, and wireless site assessments. Deliverables include detailed reports, remediation plans, and infrastructure
1 views • 5 slides