Protection Analysis using the PAF
In this session, participants will learn how to utilize the Protection Analysis Framework (PAF) and its tools to conduct effective protection analysis. The session covers an overview of PAF, understanding its pillars, and analyzing data to comprehend essential protection concepts. Key points include
5 views • 48 slides
The Digital Personal Data Protection Act 2023
The Digital Personal Data Protection Act of 2023 aims to regulate the processing of digital personal data while balancing individuals' right to data protection and lawful data processing. It covers various aspects such as obligations of data fiduciaries, rights of data principals, and the establishm
3 views • 28 slides
Proposed Approach for MAC Address Assignment in IEEE 802.11
IEEE 802.1CQ is working on a mechanism to assign local MAC address blocks to end nodes specifically related to IEEE 802.11 standards. The current draft lacks a pre-association mechanism for IEEE 802.11 stations to obtain a local MAC address before association. The proposed remedy suggests specifying
6 views • 7 slides
Enhanced Security Considerations in IEEE 802.11-23 for UHR
The document discusses enhanced security considerations for control frames and MAC headers in IEEE 802.11-23 addressing vulnerabilities and proposing encryption/decryption methods. It highlights the need for support for security protocols in control frames and the importance of protecting MAC header
0 views • 13 slides
IEEE 802.11-20/0054r1 MLD MAC Address and WM Address
In the document IEEE 802.11-20/0054r1, the focus is on Multi-Link Framework for MLD address identification and differentiation. It explains the usage of MLD MAC address and STA WM medium address in wireless setups. The document also addresses the need for identifying different MLDs using MAC address
0 views • 16 slides
Understanding the General Data Protection Regulation (GDPR) and Data Protection Bill
The General Data Protection Regulation (GDPR) is a set of rules aimed at safeguarding individuals' personal data and privacy rights, with key changes from the previous Data Protection Act 1998. The GDPR introduces transparency, consent requirements, enhanced individual rights, breach notifications,
3 views • 40 slides
Groundskeeping Safety and Personal Protective Equipment Training
This presentation covers essential information on groundskeeping safety and the proper use of personal protective equipment (PPE). Topics include head protection, eye/face protection, hearing protection, respiratory protection, hand protection, body protection, foot protection, as well as guidance o
0 views • 35 slides
Enhancing Privacy with Randomized MAC Addresses in 802.11 Networks
This presentation discusses the use of randomized MAC addresses as a privacy-enhancing measure in 802.11 networks. Passive observation of MAC addresses poses privacy risks, and the proposal suggests assigning random MAC addresses to portable devices to mitigate tracking risks. By periodically changi
0 views • 10 slides
Programmable Parser and Header Definitions at University of South Carolina
Programmable parsers and custom header definitions play a crucial role in network packet processing. This presentation by Jorge Crichigno at the University of South Carolina covers topics such as parser operation, predefined states, and header formats. The content delves into the capabilities of pro
1 views • 22 slides
Enhanced Replay Detection for Header Protection in IEEE 802.11-23/1960r1
Enhancing security in IEEE 802.11 is a key goal of UHR. This document discusses the need for improved replay detection mechanisms for header protection in the MAC layer. The proposal suggests incorporating a time component in the Packet Number (PN) to mitigate jam, record, and replay attacks. By uti
0 views • 11 slides
Privacy Issues in IEEE 802.11 Networks: Tracking and MAC Randomization
This presentation delves into the privacy concerns surrounding 802.11 networks, focusing on tracking vulnerabilities and the limitations of MAC randomization in preventing tracking. It discusses the ease of tracking devices, the risk of passive tracking due to MAC addresses being visible in frames,
0 views • 27 slides
IEEE802.15-14-0110-01-0mag MAC Timing Discussion Points for IEEE 802.15.4 Revision
Initial discussion document submitted by Benjamin A. Rolfe from Blind Creek Associates addressing MAC timing issues in the IEEE 802.15.4 standard revision. The document identifies potential problems, provides a list of questions for consideration, and outlines areas for improvement. It includes stat
0 views • 8 slides
Summary of MAC Address Policy Contribution to IEEE 802.11
This document outlines the contribution of MAC address policy to IEEE 802.11, focusing on defining ANQP and Beacon elements to convey information about addressing types supported by the network. It details how specific bits in the ANQP element represent support for various MAC address types includin
0 views • 5 slides
Implications of IEEE 802.11 State Machine and MAC Randomization
The document discusses the state machine transitions in IEEE 802.11, focusing on MAC address handling and implications for STA connectivity within an ESS. It explains the scenarios where a STA can use different MAC addresses, emphasizing the binding of state to specific address configurations and th
0 views • 11 slides
IEEE 802.11-21/1585r10: Identifiable Random MAC Address Presentation Summary
This presentation discusses the concept of Identifiable Random MAC (IRM) addresses in the IEEE 802.11-21/1585r10 standard. It covers the purpose of IRM addresses in preventing third-party tracking while allowing trusted parties to identify specific devices. The presentation outlines the use of Ident
0 views • 24 slides
Vulnerabilities in Unprotected MAC Header Fields in IEEE 802.11 Standard
The document discusses the risks associated with unprotected fields in the MAC header of MPDUs in IEEE 802.11 standards, highlighting how these fields can be vulnerable to attacks leading to adverse effects on receivers. Fields like Frame Control, Sequence Control, and QoS Control are identified as
0 views • 10 slides
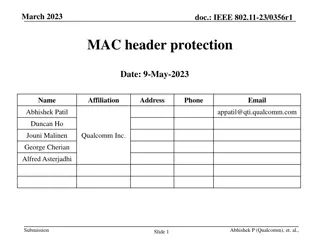
Enhancing MAC Header Protection in IEEE 802.11 for Improved Security
Numerous critical fields in the MAC header of IEEE 802.11 frames lack protection during encryption, making them vulnerable to attacks that can have adverse effects on receivers. By safeguarding these fields, performance goals can be met, power efficiency enhanced, and reliability improved. The docum
0 views • 9 slides
How to Record Your Voice: A Comprehensive Guide for Windows, Mac, and Smartphones
Learn how to record your voice for ePoster, MP3, or podcasts using Windows 10, Mac, Android, or iPhone/iPad devices. Find step-by-step instructions for recording on different platforms, including using Windows Voice Recorder on a Windows 10 computer and QuickTime Player on a Mac. Discover tips for a
1 views • 10 slides
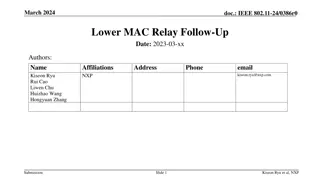
IEEE 802.11-24/0386r0 Lower MAC Relay Protocol Details
Detailed discussion on supporting the relay protocol in IEEE 802.11bn, covering relay addressing, end-to-end BA, relay TXOP protection, beacon forwarding, security processing, non-UHR STA support, sounding procedure, A-MPDU aggregation, de-aggregation, and more. The relay operation involves relay de
0 views • 16 slides
Exploring Mac OS & VoiceOver: A Comprehensive Guide with Belinda Rudinger
Dive into the world of Mac OS and VoiceOver with expert Belinda Rudinger in this detailed tutorial. Learn about screen readers, VoiceOver commands, built-in features, interaction tools, customization options, and useful utilities. Discover how to navigate the Mac ecosystem seamlessly using VoiceOver
0 views • 20 slides
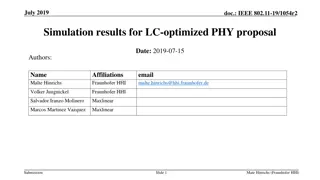
Simulation Results for LC-Optimized PHY Proposal in July 2019
The document presents simulation results for an LC-optimized PHY proposal for TGbb based on G.9991 PHY. It includes details on the simulation setup, frame detection results, header modulation, coding simulation results, payload modulation, and coding simulation results. The setup involved various re
0 views • 18 slides
Lightweight Cryptography: Key-Reduced Variants and Beyond-Birthday-Bound Security
Lightweight cryptography has emerged as a hot research topic in the past two decades, with over 60 ciphers proposed. This includes examples like PRESENT, GIFT, SIMON/SPECK, and more. Authenticated encryption through CAESAR and NIST LWC plays a vital role, with ASCON and ACORN leading the lightweight
0 views • 25 slides
Understanding C Programming: Arrays, Coding Practices, and File Organization
In this educational content, we delve into the concept of arrays in C programming and discuss a practical coding exercise involving finding the maximum, minimum, mean, variance, median, and mode of a list of values. We also cover important coding practices such as organizing C files, using header fi
0 views • 25 slides
The Migration Advisory Committee Review and Findings
The Migration Advisory Committee (MAC) is an independent advisory body formed in 2007 to provide recommendations to the government on migration issues. The MAC does not create or implement policy but advises through research and analysis in various areas like economics, education, and stakeholder en
0 views • 13 slides
Local MAC Address Assignment Protocol (LAAP) and 802.1CQ
The Local MAC Address Assignment Protocol (LAAP) in conjunction with 802.1CQ specifies protocols and procedures for locally unique assignment of MAC addresses in IEEE 802 networks. LAAP operates in two modes - Server Mode and Peer-to-Peer Mode, ensuring efficient allocation of MAC addresses while av
0 views • 15 slides
Improving Consumer Protection in Ghana: Insights from the Sixth Annual African Dialogue Consumer Protection Conference
The Sixth Annual African Dialogue Consumer Protection Conference held in Lilongwe, Malawi in September 2014 shed light on the challenges faced by Ghana's consumer protection policies. Irene Aborchie-Nyahe, a legal consultant, highlighted the gaps in Ghana's legislative framework, lack of effective i
0 views • 14 slides
Understanding Carnegie Mellon's Protection and Security Concepts
Carnegie Mellon University emphasizes the importance of protection and security in operating systems. Protection involves preventing unauthorized access by users, while security focuses on external threats and authenticating system users. The goals of protection include preventing access violations
0 views • 37 slides
Introduction to IEEE 802c SLAP
IEEE 802c defines Local Medium Access Control (MAC) Address Usage, providing structured approaches through the Structured Local Address Plan (SLAP) in different regions of the local MAC address space. Local MAC addresses are not globally unique, and the assignment is within local administration's sc
0 views • 9 slides
Caseous Mitral Valve Calcification (C-MAC) and Stroke: Overview and Management
Caseous Mitral Valve Calcification (C-MAC) is a rare condition characterized by spectrum liquefaction necrosis of the mitral annular calcification (MAC), potentially leading to cardiovascular complications like strokes and emboli. This article discusses the features, diagnostic aspects, and treatmen
0 views • 7 slides
Examples of Header Images for Anna Andersson in November
Collection of header images featuring Anna Andersson from November 2015 to 2018, including varied designs and layouts. Contact details provided for further inquiries. Visit www.bioinnovation.se for more information.
0 views • 11 slides
Enhancing MAC Header Protection in IEEE 802.11 Networks
This document discusses the need for improved protection of MAC headers in IEEE 802.11 networks to address security concerns related to certain fields that are currently not adequately protected. It emphasizes the importance of safeguarding vital information in MAC headers to prevent potential attac
0 views • 12 slides
IEEE 802.11-22/0424r1 - MAAD MAC Protocol Overview
The document discusses the MAAD MAC protocol, where the AP assigns a MAAD MAC address to the STA during association. Key differences from other schemes are highlighted, emphasizing the use of MAAD MAC addresses as identification. Details on support indication, address allocation, and recognition mec
0 views • 7 slides
IEEE 802.11-22/0955r0 TGbh Pre-association Schemes Exploration
The document explores the pre-association schemes NGID, MAAD, and IRM within the IEEE 802.11-22 standard. It discusses how the schemes operate, comparing RRCM to MAAD and IRM, and addresses the use of Probes and MAC addresses in pre-association scenarios. The presentation clarifies the allocation of
0 views • 15 slides
Discussion on Secure Control Frame and MAC Header Protection in IEEE 802.11-24/0490r0
This document discusses the importance of addressing secure control frame and MAC header protection in IEEE 802.11-24/0490r0. It examines potential issues such as data disruption, denial of service, power drainage, and resource wastage. The author questions the necessity of solving these issues and
0 views • 9 slides
RCM Procedure for Secure Parameter Obfuscation in IEEE 802.11 Networks
The document discusses the RCM procedure within IEEE 802.11 networks, focusing on obfuscating parameters like MAC addresses for enhanced security during CPE Client and CPE AP association. It outlines mechanisms for changing MAC addresses, SN, PN, AID, and TID without connection loss. The proposal su
0 views • 12 slides
Understanding IP Datagrams and Header Fields in Computer Networks
This detailed content covers the essentials of IP datagrams and header fields in computer networks. It explains the structure of IP datagrams, key fields in the IP header, and the concept of fragmentation to handle varying Maximum Transmission Units (MTUs) in networks. The illustrations and explanat
0 views • 62 slides
IEEE 802.11-23/0421r1: Understanding the IRM Scheme for MAC Address Privacy
The document discusses the use of the Same MAC Address (SMA) scheme in IEEE 802.11-23/0421r1 and introduces the Improved Randomized MAC (IRM) scheme as a privacy-enhancing solution. It explores the implementation and benefits of IRM over SMA, addressing issues like privacy requirements, device ident
0 views • 7 slides
Workshop on Data Protection: Mauritius Police Force Presentation
The workshop on data protection by Mrs. D. Madhub, Data Protection Commissioner, held on May 15, 2019, focused on the Data Protection Act, the Data Protection Office, definitions, functions, powers, and obligations related to data protection, covering areas such as processing of personal data and ri
0 views • 46 slides
Enhancement of Rule-based Random and Changing MAC Proposal in IEEE 802.11-22/1802r0
This document details the enhancements proposed for the Rule-based Random and Changing MAC (RRCM) in IEEE 802.11-22/1802r0. The RRCM concept involves generating Random MAC (RMA) addresses locally to increase security and prevent trackability in wireless networks. Key aspects include RMA generation,
0 views • 12 slides
MAC Address Randomization in IEEE 802.11: Privacy Concerns and Solutions
The document discusses the rise of MAC randomization in IEEE 802.11 networks, addressing motivations, benefits, concerns over privacy implications, and real-life scenarios highlighting the risks associated with passive observation of MAC addresses. It emphasizes the importance of safeguarding privac
0 views • 14 slides