Cyber Crime Police Station Hyderabad City
Learn about various types of cyber crimes including online debit/credit card and bank frauds, UPI money scams, social media offenses, hacking incidents, job/visa frauds, and loan/insurance/lottery scams. Stay informed and protect yourself online.
1 views • 12 slides
How to Protect Your On-Demand App from Cyberattacks and Data Breaches
On-demand app development solutions provide convenient services but also carry cybersecurity risks like hacking, malware, and data breaches. This comprehensive guide explores best practices to secure on-demand apps and protect sensitive user data. Learn how encryption, multifactor authentication, ac
0 views • 4 slides
Dismissive Reviews, Citation Cartels, and the Replication Crisis
The study delves into the replication crisis in research, citing factors influencing research credibility such as sample size, effect size, and financial interests. It highlights issues like gaming the system, P-hacking, and data sharing reluctance. The growth of Metascience as a response to these c
0 views • 45 slides
Practice Areas - Aegle Marmelos Law Firm in Chennai & Madurai
Practice Areas - Aegle Marmelos Law Firm in Chennai & Madurai\n\n\u2022\tCriminal:\nViolent crimes (murder, assault)\n\u2022\tSexual offenses (rape, harassment)\n\u2022\tProperty crimes (theft, burglary)\n\u2022\tFinancial crimes (fraud, embezzlement)\n\u2022\tCybercrimes (hacking, online fraud)\n\u
0 views • 4 slides
Penetration Testing and Incident Response Technologies Overview
Explore the world of penetration testing, incident response technologies, and ethical hacking in the context of CIS 6395 course at UCF. Learn about tools like Metasploitable 2 VM for vulnerability testing and techniques such as Ping Sweep and Ping. Discover essential concepts for testing and securin
0 views • 32 slides
Understanding Man-in-the-Middle Attacks and Network Security Threats
Explore the risks associated with Man-in-the-Middle attacks including password sniffing and cracking. Learn about ethical hacking, ARP poisoning techniques, encryption methods, and the importance of information security. Discover the legality of hacking under certain conditions and gain insights int
0 views • 13 slides
Understanding the Essence of Data Science
Data science is a dynamic field blending hacking and statistics to derive insights from vast amounts of data. It involves converting various aspects of life into data, creating new forms of value. The demand for data scientists is surging due to the data explosion and technological advancements. A d
0 views • 11 slides
Understanding Cyber Crimes: History, Categories, and Types
Delve into the world of cyber crimes through an exploration of its history, categories, and types. Discover the evolution of cyber crimes from the first recorded incident in 1820 to modern-day threats like hacking, child pornography, denial of service attacks, and more. Uncover the motives behind th
3 views • 15 slides
Understanding Cyber Crime: Risks and Prevention Measures
Cyber crime, including hacking, phishing, and pharming, poses a significant threat in today's digital world. Learn about the types of hackers and how to tackle phishing and pharming attacks effectively. By following security measures such as avoiding sharing sensitive information and updating anti-p
4 views • 18 slides
Understanding Non-Standard Errors in Research Methods
Research teams conducting experiments using the same data show large variations in results, termed as non-standard errors (NSE). Peer feedback helps reduce NSE, but factors like vague hypotheses and test statistic definitions can lead to result discrepancies. Addressing issues like multiple hypothes
0 views • 12 slides
Comprehensive Guide to Hacking Techniques & Intrusion Detection
This guide by Ali Al-Shemery provides insights into reconnaissance, intelligence gathering, target selection, and open-source intelligence for successful attacks. It covers the importance of OSINT, rules of engagement, and different forms of information gathering in the realm of cybersecurity.
2 views • 46 slides
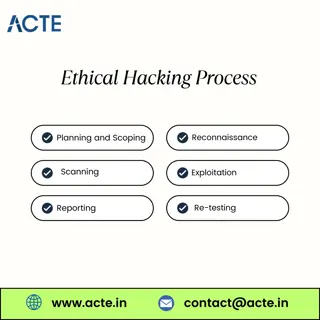
Fundamentals of Ethical Hacking
Ethical hackers are often called \u201cwhite hats\u201d in contrast to \u201cblack hats,\u201d who are the malicious hackers. White hats use their skills to improve security and protect information, while black hats exploit vulnerabilities for illega
0 views • 1 slides
Ethical Hacking Essential Knowledge
Ethical hackers use the same tools and techniques as cybercriminals but with permission and for good reasons.\n\nThink of it as a friendly security check-up. Just like you might get a health check-up to catch any issues early, ethical hacking helps o
0 views • 2 slides
Understanding Chronic Cough: Case Study and Assessment
30-year-old L.B., a secretary, presents with a dry, hacking cough and shortness of breath post-bronchitis recovery. History of asthma in family raises concerns. Intake nurse must acquire vital signs, medical history, symptoms, and potential triggers to determine the underlying cause of the chronic c
0 views • 13 slides
Quality Blended Learning: Google Searching and Security Risks
Google searching has become a standard method for accessing information online, but it can also pose security risks if webpages are left vulnerable to hacking. This article explores how the Google search engine can be used to find valuable resources for designing, developing, and evaluating quality
0 views • 27 slides
Protecting Your Computer and Laptop: Tips for Maintenance and Security
In this presentation, learn how to safeguard your computer and laptop with simple precautions to prevent physical damage, viruses, hacking, and more. Discover dos and don'ts for handling serious computer issues and ensuring your devices stay in optimal condition. Remember these key steps for maintai
0 views • 5 slides
Understanding Network Security Threats and Goals in Computer Systems
Explore the concept of threats in communication networks, including examples of attacks such as hacking and data disclosure. Learn about key security goals like confidentiality, data integrity, accountability, availability, and controlled access. Discover technically defined threats like masquerade,
0 views • 32 slides
Protecting Your Work Environment from Hacking Threats
Safeguarding your work environment from hacking is crucial to prevent potential losses. Addressing human errors, hacker infiltration, targeted phishing, and extortion are key steps to enhance security. Implementing measures like device security, two-factor authentication, firewall protection, and em
0 views • 8 slides
Unveiling Google Hacking Techniques
Explore the art of Google hacking, a method of utilizing advanced search operators and logic operators to uncover sensitive information online. From understanding Google hacking to diving into advanced search strategies and leveraging the Google Hacking Database (GHDB), discover how to enhance your
0 views • 14 slides
Understanding Security Threats and Countermeasures
Explore the diverse threats posed by attackers in the information security landscape, ranging from employee sabotage to hacking incidents. Learn about fundamental security terminology, types of security compromises, and countermeasure strategies to prevent, detect, and correct security breaches. Gai
0 views • 32 slides
Unpacking Ethical Issues in Academic Research
Exploring the broader landscape of ethics and plagiarism in academic research beyond Turnitin, diving into questionable research practices, like p-hacking and HARKing. Understanding the significance of recognizing unethical behavior and promoting integrity in scholarly pursuits, emphasizing the impo
0 views • 19 slides
Strategies for Growth Hacking in Child Welfare Tech Entrepreneurship
Implementing growth hacking tactics, such as social media engagement, webinars, and event participation, to elevate the visibility of a women-led tech company improving child welfare through software solutions. Focus on leveraging female tech entrepreneurship, engaging social worker communities, and
0 views • 6 slides
Linux Administration Essentials: A Comprehensive Training Program
Join the Cooper Union Retraining Program at CAMBA for an intensive course on Linux (Unix) Administration instructed by Dr. Tavaris J. Thomas. Learn core objectives spanning from file system management to network configuration without diving into hacking or programming. Explore the history of Linux,
0 views • 35 slides
Ethical Hacking_ Principles, Practices, and Significance
Ethical hacking involves authorized attempts to gain unauthorized access to a system, application, or data. Also known as penetration testing or white-hat hacking, ethical hacking uses the same methods as malicious hackers to find security weaknesses
0 views • 8 slides
Cybersecurity News and Insights
Explore the latest cybersecurity news and insights on hacking incidents, data breaches, vulnerabilities, and attacker strategies discussed in the context of MIS. Stay informed about ongoing cyber threats and how attackers operate once inside a system.
0 views • 31 slides
Understanding Unix/Linux Hacking Techniques
Explore Unix/Linux hacking techniques including footprinting, scanning, enumeration, vulnerability mapping, remote access, data-driven attacks, buffer overflow, input validation, and countermeasures. Discover methods to gain root access, exploit vulnerabilities, perform brute force attacks, and secu
0 views • 6 slides
Securing Our Elections: Challenges and Solutions
The article delves into the critical issue of election security, highlighting vulnerabilities such as hacking, tampering, and outdated voting machines. It discusses potential threats like information leaks and voter suppression, emphasizing the importance of safeguarding the electoral process. With
0 views • 20 slides
Understanding Cyber Crimes and Their Impact in India
Cyber crimes have become a growing concern in India, with Bengaluru being labeled as the cybercrime capital. Statistics reveal a high number of reported cases, with various types of cybercrimes such as hacking, email bombing, and cyberstalking posing significant threats. It is crucial to address the
0 views • 18 slides
Community-Led Qualitative Research on LDSS/N Distribution Preferences
Dr. Annie Madden leads a community-led research project focused on the values and preferences of people who inject drugs regarding LDSS/N distribution. The study aims to generate evidence on the feasibility and impact of implementing LDSS/N distribution programs, involving phases from pre-implementa
0 views • 8 slides
Exploring Ethical Hacking: Understanding the Different Types of Hackers
Ethical hacking, presented by Mr. Bhushan S. Kulkarni, involves identifying and exploiting vulnerabilities in computer systems for security improvement. This article delves into the definition of hacking, the roles of hackers (Black Hat, White Hat, Grey Hat), and their distinct characteristics and m
0 views • 7 slides
Comprehensive Guide to Hacking Techniques & Intrusion Detection
Dive into the world of hacking techniques, intrusion detection, and network protocols with expert Ali Al-Shemery. Learn about host discovery, port scanning, packet crafting, and more using tools like Nmap. Explore the importance of network protocols like TCP, UDP, ICMP, and ARP. Discover the art of
0 views • 50 slides
Community Land Trusts: Empowering Communities through Collective Ownership
Community Land Trusts (CLTs) are legal entities run by local volunteers to collectively own and manage property/land, undertake development projects, and secure assets for the community. With priorities set by communities to address local issues like affordable housing and recreation, CLTs provide a
0 views • 13 slides
Inside the Mind of Hackers: Behavior, Motivation, and Notable Cases
Explore the intriguing world of hackers, delving into their behavior, motivations, and infamous cases such as Kevin Mitnick's social engineering hacks and Adrian Lamo's unique approach to vulnerability disclosures. Discover how figures like Stephen Wozniak and Loyd Blankenship transitioned from hack
0 views • 59 slides
Understanding Hacking: Types, Hackers, and Ethics
Hacking is a complex area covering various topics and activities, originating from MIT in 1960. It involves finding vulnerabilities in computer systems and networks for unauthorized access, potentially harming systems or stealing information. Ethical hacking serves the purpose of identifying and fix
0 views • 11 slides
Comprehensive Guide to Hacking Techniques and Intrusion Detection
This guide by Ali Al-Shemery provides insights into hacking techniques, intrusion detection, fingerprinting, external and internal footprinting, passive reconnaissance, WHOIS lookups, and various online tools for intelligence gathering during penetration tests. It covers identifying customer externa
0 views • 29 slides
Bishop's Castle Community Partnership (BCCP) - Advancing Citizenship and Community Development
The Bishop's Castle Community Partnership (BCCP), an independent charity, works towards advancing citizenship and community development in Bishop's Castle. Through a Community-Led Town Plan and various sustainability projects, the BCCP collaborates with the local community, Town Council, and other o
0 views • 6 slides
Community-Centered Strategic Direction for Building a Better Community
Discovering, learning, and growing together to formulate a community-centered strategic direction in 2016. Leaders focus on what they believe in - connecting, learning, innovating, and collaborating. Their purpose is to inspire the community through enrichment and engagement. Their vision is a vibra
0 views • 6 slides
Innovative Security Solutions: Gaetano Perrone Tutor Simon Pietro Romano
Gaetano Perrone, a PhD holder in Information Technology, is the co-founder of SecSI and has a background in Computer Science Engineering. He has worked on projects like AI platforms for ethical hacking and security automation. His contributions include software development of a collaborative ethical
0 views • 10 slides
Understanding Cross-Site Scripting (XSS) Attacks and Prevention Measures
Cross-Site Scripting (XSS) is a prevalent security vulnerability in web applications that allows attackers to inject malicious scripts, potentially leading to unauthorized data access or manipulation. The content covers types of XSS attacks, finding vulnerable websites, testing exploits, and legal i
0 views • 10 slides