Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
How to Fix Quickbooks Error 80070057?
How to Fix Quickbooks Error 80070057?\nQuickBooks Error 80070057 can disrupt financial management. It occurs due to file extension issues or data damage. Symptoms include inability to open files and error code display. Causes involve incorrect file extensions or firewall settings. Diagnostic tools l
1 views • 5 slides
How to Fix “The File Exists QuickBooks Error” Warning Message
How to Fix the \"The File Exists QuickBooks Error\" warning message requires a systematic approach to troubleshoot and resolve the underlying issues that cause this problem. QuickBooks, being a complex accounting software, may encounter various errors related to file management and system compatibil
0 views • 5 slides
Understanding Filesystems: A Comprehensive Overview
File systems provide a structured approach to storing and organizing data on secondary storage devices. They involve logical organization of files, directories for grouping related files, sharing data between users, and managing permissions. Files contain data with attributes like size, ownership, a
3 views • 29 slides
Implementation of File System in Operating Systems
Various structures, such as boot control blocks and directory implementations, play a crucial role in implementing a file system in operating systems. These structures help in managing disk and in-memory data efficiently, ensuring effective file storage and retrieval. Linear lists and hash tables ar
1 views • 22 slides
DataSecurity Plus - Unified Data Visibility and Security Platform
DataSecurity Plus by ManageEngine offers a unified data visibility and security platform with capabilities such as file server auditing, ransomware detection, data leak prevention, cloud protection, and more. It provides solutions for file audit, file analysis, data risk assessment, data leak preven
0 views • 24 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Understanding Distributed File Systems
A distributed file system manages files across multiple machines on a network, providing users with a seamless experience as if they were using a local file system. This system abstracts details such as file locations, replicas, and system failures from the user, ensuring efficient and reliable file
0 views • 35 slides
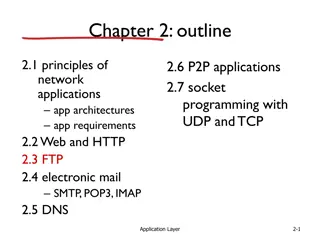
Understanding File Transfer Protocols in Networking
Explore the fundamental concepts of File Transfer Protocol (FTP) in networking, covering its architecture, operation, commands, security considerations, and a comparison with Secure File Transfer Protocol (SFTP). Gain insights into how FTP enables the transfer of files between client and server, inc
0 views • 33 slides
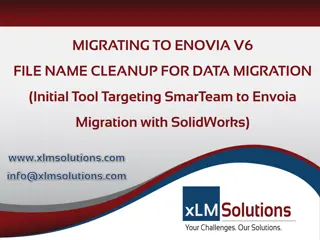
ENOVIA V6 File Name Cleanup for Data Migration
Problematic file names with unsupported characters can hinder data migration into ENOVIA V6, impacting object busname, titles, and filenames. This article proposes a solution involving filename changes, database updates, and file vault maintenance. The methodology includes SQL queries for analysis,
0 views • 5 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
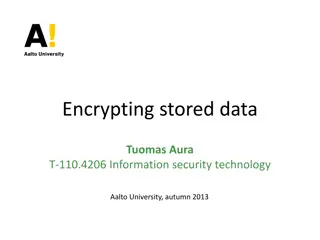
Understanding Data Encryption and File Security
Exploring data encryption and file security, covering topics such as scenarios for encryption, file encryption methods, limitations, and secure file deletion techniques. Highlighting the challenges of balancing security, usability, and reliability in computer systems.
0 views • 29 slides
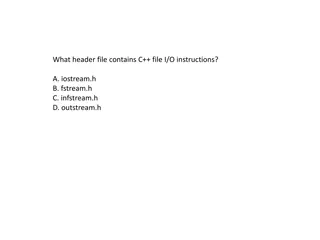
Understanding C++ File I/O Operations
Learn about C++ file I/O operations, including input/output instructions, file handling with ifstream and ofstream, opening multiple files, checking end of file, and a review of the file I/O process. Discover how to write to an ASCII file and read data from it in C++ programming. Practice with examp
0 views • 47 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
Understanding File Input/Output in Java
Learn about file input/output operations in Java. Explore how to read and write data to files, handle exceptions using try/catch, work with streams, understand the process of file handling, and examine file structure examples like storing airline data. Enhance your Java programming skills by masteri
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Understanding DFS in Dyalog File Server
DFS (Dyalog File Server) is a client/server system that replaces direct access to component files. It offers features like monitoring, backup, and user authentication. DFS enhances security and performance compared to traditional file access methods like DCF. Learn about its architecture, features,
0 views • 35 slides
Data Encryption and File Security Overview
Explore the complexities and challenges of encrypting stored data, file encryption, and ensuring secure systems. Learn about the scenarios where data encryption is crucial, the limitations of file encryption, and the importance of secure data wiping practices for maintaining confidentiality. Delve i
0 views • 30 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Efficient Ways to Store and Share Large Files
Explore the world of file hosting services for storing and sharing large files, focusing on Google Drive, Dropbox, and SkyDrive. Discover their similarities, security features, and sharing capabilities. Learn about SSL support, file encryption, and the ability to share files with ease. Dive into the
0 views • 19 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Fast File Clone in ZFS Design Proposal Overview
This document details a proposal for implementing fast file clone functionality in ZFS, allowing for nearly instant file copying through referencing. The motivation behind this proposal includes support for VMware VAAI, NAS Full File Clone, and Fast File Clone to save memory and disk space. The prop
0 views • 29 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding File Input/Output in Python Programming
Exploring the basics of File I/O (Input/Output) in Python, including reading from and writing to text files. Learn how to read all content from a file as a string or a list, and how to write data to a file using Python's file handling capabilities.
0 views • 12 slides
Evolution of Networked File Systems in Computer Science
The evolution of networked file systems in the computer science field has been pivotal in enabling remote file storage, distributed coordination, and improved system stability. Starting from Bill Joy's innovations in the BSD version of Unix to the introduction of NFS by Sun Microsystems, the concept
0 views • 55 slides
Understanding File Processing and Input/Output Operations in Java
Gain insights into file processing and I/O operations in Java programming, covering topics such as file handling, reading files, file paths, compiler errors, exceptions, and the 'throws' clause. Learn how to work with files, handle errors effectively, and optimize your code for efficient file manage
0 views • 41 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
Understanding File System Calls and Operations in Operating Systems
Explore the concepts of file system calls, opening files, reading from files, setting file offsets, closing files, and maintaining file states in an operating system. Learn how to interact with files efficiently while understanding the underlying mechanisms and necessary actions for file handling.
0 views • 21 slides
Understanding File Input/Output (I/O) in C++
File Input/Output (I/O) is an essential concept in C++ programming, allowing for interaction with files stored on secondary storage devices. This involves steps like including the fstream header file, declaring file stream variables, associating them with input/output sources, opening the file, perf
0 views • 19 slides
Understanding File Systems in Operating Systems
File systems are essential components of operating systems that manage the organization, storage, and retrieval of files. This content explores the function of file systems, their interfaces, design tradeoffs, file concepts, attributes, and structures. It covers topics such as access methods, direct
0 views • 49 slides
Understanding File Systems: File Naming, Extensions, and Structure
File systems and commands play a crucial role in managing information on disks while shielding users from the complexities of storage mechanisms. This article delves into the rules of file naming, distinctions between upper and lower case letters, file extensions indicating file types, and the under
0 views • 85 slides
Understanding File System Design Challenges and Options
Exploring the complexities of file system design, this content delves into various aspects such as file layout, design constraints, data structures, design challenges, options like FAT, FFS, NTFS, and more. It discusses the challenges of locating file blocks, index granularity, free space management
0 views • 33 slides
Sequential File Maintenance and Organisation Process
In sequential file maintenance, the master records are updated and written to a new file in sequence after processing transaction records. This process continues until all relevant master records are updated, resulting in a new file with unchanged and updated records. Additional steps involve file s
0 views • 7 slides