Autonomous Conjunction Assessment Methodology Among Satellites
Methodology for Collision Avoidance (CA) among constellations of autonomously-controlled satellites is crucial for protecting assets in space. From straightforward protection against dead satellites to active coordination for maneuverable payloads, the range of primary-secondary CA possibilities is
1 views • 12 slides
Understanding 2D Collision Detection in Game Development
Explore the intricacies of 2D collision detection in game development through methods like distance checks, bounding shapes, and optimizing collision tests. Dive into concepts like sprite speed assumptions, square-square collisions, and rectangle testing complexities. Learn about useful Rectangle me
5 views • 29 slides
Understanding Emotionally Based School Avoidance in Children and Young People
Emotionally Based School Avoidance (ESBA) is a common issue among children and young people, leading to school attendance concerns. This article sheds light on the diverse presentation of school avoidant behaviors, effective strategies for addressing them, and the prevalence of anxiety and stress as
1 views • 42 slides
Spectrum Sensing for Enhanced Channel Access in Wireless Networks
This document presents a proposal for Spectrum Sensing Based Deferral (SSBD) to improve channel access in wireless networks. SSBD incorporates spectrum sensing with transmission deferral in a time-bound manner to enhance performance, reliability, and latency control. The proposed solution safeguards
1 views • 11 slides
Considerations on Inter-PPDU Based Preemption Scheme in IEEE 802.11-23
In this document, considerations are presented for a preemption scheme in IEEE 802.11-23, focusing on issues such as coordination, ACK transmission timing, and channel access fairness. The proposed inter-PPDU based preemption scheme aims to improve the transmission of low latency traffics within the
1 views • 12 slides
Understanding Different Types and Classifications of Heliports
Heliports, helidecks, helistops, and helipads serve as key landing areas for helicopters. They come in various classifications including military, federal, private use, public use, commercial service, and personal use. Factors influencing site selection include traffic considerations, obstruction av
0 views • 21 slides
Autonomous Obstacle Avoidance Robot Using ROS, Lidar, and Raspberry Pi with Matlab Path Planning
Obstacle avoidance in robotics has evolved from basic collision avoidance to autonomous path planning with the use of Lidar and ROS. This project involves mapping the environment using Lidar scans and implementing a path planning algorithm in Matlab to navigate around obstacles. By utilizing a Raspb
0 views • 15 slides
Advanced Emergency Braking System (AEBS) Definition and Activation Guidelines
The provided content outlines the definition and activation requirements of the Advanced Emergency Braking System (AEBS). It covers the phases involved, including Collision Warning and Emergency Braking, as well as the speed limitations for activation. The system aims to automatically detect potenti
0 views • 12 slides
Preventing Artificial Avoidance of PE Status in International Business: Case Studies & Exemptions
Explore case studies on Agency PE and Preparatory/Auxiliary Services, along with PE exemptions for specific activities to prevent the artificial avoidance of Permanent Establishment status in the global tax landscape.
2 views • 14 slides
Understanding Deadlock: Conditions, Detection, and Avoidance
Explore strategies for dealing with deadlocks, from detection and recovery to dynamic avoidance. Learn about deadlock avoidance methods like being conservative in resource granting and dive into safe and unsafe states, the Banker's algorithm, and the four conditions for deadlock. Discover how to pre
0 views • 15 slides
Michigan OIG: Cost Avoidance and Investigation Types Overview
Michigan's Office of Inspector General (OIG) within the Department of Health & Human Services conducts investigations to ensure data integrity, targeting areas like cost avoidance, fraud, and program violations in public assistance programs. The OIG's efforts have resulted in significant savings and
0 views • 12 slides
Understanding Deadlock Avoidance in Operating System Concepts
Deadlock Avoidance is a critical concept in operating system design to prevent system resources from entering a deadlock state. By requiring additional information about resource requests and utilizing algorithms like the banker's algorithm, systems can dynamically allocate resources to avoid circul
1 views • 29 slides
Robust Space-Time Footsteps for Agent-Based Steering by Glen Berseth, Mubbasir Kapadia, Petros Faloutsos
This research focuses on enhancing the interface between steering and motion synthesis for agent-based systems. It introduces geometric pruning of search space, randomized step directions and times, and new types of footsteps, leading to significant performance improvements, stability enhancement, a
0 views • 17 slides
Exploring DRONET: Learning to Fly by Driving
DRONET presents a novel approach to safe and reliable outdoor navigation for Autonomous Underwater Vehicles (AUVs), addressing challenges such as obstacle avoidance and adherence to traffic laws. By utilizing a Residual Convolutional Neural Network (CNN) and a custom outdoor dataset, DRONET achieves
0 views • 20 slides
Innovative DIY Quadcopter Project with Autonomous Features
Explore the Drone Project by Krish Kabra & Stefan Orosco, detailing the creation of a DIY Quadcopter Drone with Arduino-based control, radio-frequency, PID stabilization, collision avoidance, and voice control. Discover its applications in search and rescue, agriculture, entertainment, and defense,
0 views • 27 slides
ACAS Improvements for Enhanced Airborne Safety
Module N.B0-101 focuses on improving existing Airborne Collision Avoidance Systems (ACAS) to reduce nuisance alerts without compromising safety levels. It introduces several optional enhancements to minimize unnecessary alerts and improve overall safety during airborne operations. The module aims to
0 views • 12 slides
Physics Collision Problems Explained
Explore various collision scenarios involving bullets, blocks, cars, and people in this physics problem set. Calculate velocities, masses, and recoils to understand the dynamics of collisions and their effects on different objects involved.
0 views • 15 slides
Understanding Convex Hulls in Computational Geometry
Convex hulls play a vital role in computational geometry, enabling shape approximation, collision avoidance in robotics, and finding smallest enclosing boxes for point sets. The convex hull problem involves computing the smallest convex polygon containing a set of points, with extreme points determi
0 views • 119 slides
Understanding the Dynamics of Collision: Bug vs. Windshield
Explore the intriguing physics behind a bug hitting a windshield, delving into concepts like Newton's third law, momentum conservation, and the differences in force, time of impact, and change in velocity. Discover why a bug goes splat while a windshield remains intact in a collision scenario, with
0 views • 19 slides
Understanding Avoidance Behavior and Its Theories
Avoidance behavior involves negative reinforcement to increase the frequency of operant responses, not punishment. Different types of avoidance tests, such as discriminated avoidance and shuttle avoidance, are used to study negative reinforcement. The Two-Factor Theory of avoidance conditioning expl
0 views • 61 slides
Drone Collision Avoidance Simulator for Autonomous Maneuvering
Our project focuses on developing a drone collision avoidance simulator using NEAT and Deep Reinforcement Learning techniques. We aim to create a model that can maneuver obstacles in a 2D environment, enhancing performance and survivability. Previous attempts utilizing non-machine learning solutions
0 views • 28 slides
Overview of Canadian and South African General Anti-Avoidance Rules (GAARs)
This review discusses the General Anti-Avoidance Rules (GAARs) in Canada and South Africa, focusing on the criteria for identifying avoidance transactions and impermissible avoidance arrangements. The Canadian GAAR targets transactions seeking tax benefits, while the South African GAAR focuses on bu
0 views • 15 slides
Analysis of Tax Avoidance Transactions in Case Study on GAAR Application
The case study explores the incorporation of a business into a corporation to realize tax benefits, including tax deferral and lower rates. It raises questions on whether the transactions were primarily for tax avoidance purposes, highlighting the complexities of tax planning and the application of
0 views • 47 slides
Radar Familiarization Guide for Surface Operations: Understanding How Radar Works
This radar familiarization guide by the National Response Directorate provides important information on the proper use of radar equipment, including its basic principles, functions, and practical applications for surface operations. It emphasizes the significance of radar in ensuring safe navigation
0 views • 47 slides
Advanced Techniques in Collider Physics for Enhanced Luminosity
Explore cutting-edge research on beam-beam effects, crab waist colliders, and luminosity optimization in collider physics. Discover how innovative strategies like crab waist technology and bunch crabbing mitigation are revolutionizing particle collision studies. Dive into the complexities of achievi
0 views • 10 slides
Understanding GST Fraud and Avoidance Schemes
Exploring the nuances between tax fraud and tax avoidance in the context of GST, this content delves into types of GST abuse, Division 165 anti-avoidance rule, scheme structures, and consequences of GST fraud. Learn about the implications of dishonest tax practices and lawful tax conduct in the real
0 views • 10 slides
Understanding BEPS Action Plan 7: Preventing Artificial Avoidance of Permanent Establishment Status
The Action 7 Report aims to prevent artificial avoidance of Permanent Establishment (PE) status by making changes to the PE definition in the OECD Model Tax Convention. BEPS refers to tax planning strategies exploiting tax rule gaps to shift profits to low-tax locations. The OECD issued 15 action pl
0 views • 10 slides
Effective Coping Strategies for Stress Management
Avoidance coping is described as a maladaptive way of dealing with stress by avoiding the source of discomfort. In contrast, active coping involves addressing stressors directly through cognitive or behavioral strategies. Avoidance coping can lead to increased stress and conflict in relationships, w
0 views • 11 slides
Understanding the Relationship between Decisional Second-Preimage Resistance and Preimage Resistance in Cryptographic Hash Functions
This work delves into the subtle question of when Decisional Second-Preimage Resistance (SPR) implies Preimage Resistance (PRE) in hash functions. It presents a tool for enabling tight security proofs for hash-based signatures by exploring the success probability of adversaries against collision res
0 views • 25 slides
Foundations of Cryptography: Digital Signatures and Collision-Resistant Hash Functions
Foundations of Cryptography explores the construction of digital signature schemes and collision-resistant hash function families using one-way functions and safe primes. The content delves into the concept of collision-resistant hash functions and their construction from the discrete logarithm prob
0 views • 31 slides
Foundations of Cryptography: Lecture 12 - Digital Signatures and Collision-Resistant Hash Functions
The lecture covers the construction of collision-resistant hash functions from discrete log, the security behind it, and the implications for digital signature schemes. It delves into the theoretical foundations of cryptography, showcasing the interplay between one-way functions, hash functions, and
0 views • 25 slides
Comprehensive Overview of CSE 373 Data Structures and Algorithms Course - Autumn 2018
This document provides detailed information about the CSE 373 Data Structures and Algorithms course in Autumn 2018, presented by Shrirang (Shri) Mare. It covers topics such as hashing, collision strategies, hash tables, design decisions, testing, and more. The content includes announcements, midterm
0 views • 25 slides
Privacy Address Requirements for Wireless Personal Area Networks
This document discusses the privacy address requirements for IEEE P802.15 Working Group's TG4ab standard for Wireless Personal Area Networks (WPANs). It covers the need for 48-bit addresses with collision resistance, the use of different privacy addresses for each frame, and the adequacy of 12-bit c
0 views • 8 slides
Understanding TCAS - Traffic Collision Avoidance System
A Traffic Collision Avoidance System (TCAS) is a vital aircraft collision avoidance technology that helps reduce mid-air collisions by monitoring the airspace around an aircraft. TCAS operates independently of ground-based equipment and advises pilots on potential conflicting aircraft. Mandated by t
0 views • 13 slides
Vehicle Safety Protocols: Handling Tire Blows, Brake Failure, and More
Learn essential actions for handling emergencies like tire blowouts, brake failure, stuck accelerator, and steering failure. Additionally, understand off-road recovery, minimizing damage due to potholes, and escaping from a sinking vehicle. Discover collision avoidance techniques and steps to take i
0 views • 9 slides
Leveraging Vehicle-Based Safety Technology for Curtailing Distracted Driving
Perdue's private fleet employs various vehicle-based safety technologies to combat distracted driving, including video technology and mobile device interventions. The hierarchy of controls is discussed, covering strategies like substitution, engineering controls, and collision avoidance systems. By
0 views • 26 slides
Micro:bit Robot Ultrasonic Obstacle Avoidance Tutorial
Learn how to set up and program a micro:bit robot for ultrasonic obstacle avoidance. Follow the step-by-step guide to prepare hardware, connect the micro:bit to the computer, search for programming blocks, and test the ultrasonic sensor. Children can understand the concepts and experiment with obsta
0 views • 10 slides
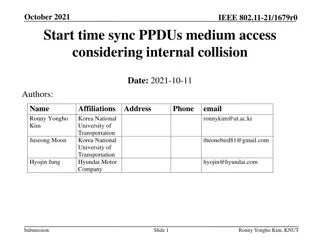
Understanding Start Time Sync Procedures in IEEE 802.11-21/1679r0
In the document authored by Ronny Yongho Kim et al., the focus is on start time sync PPDU medium access considering internal collision in IEEE 802.11-21/1679r0. It discusses the importance of defining a clear rule to resolve internal collision cases during medium access procedures. Specific attentio
0 views • 9 slides
Understanding Hash Tables and Hashing Concepts in Computer Algorithms
This content delves into the concept of Hash Tables, covering topics such as the support for dictionary operations, achieving constant time through direct address tables, case studies in web server maintenance, and an exploration of hashing functions and collision avoidance. It also touches upon key
0 views • 40 slides
MitM Attack by Name Collision: Implications and Vulnerability Assessment
In this research study, the authors delve into the risks and vulnerabilities associated with Man-in-the-Middle (MitM) attacks exploiting name collision in the era of new generic Top-Level Domains (gTLDs). The study highlights how attackers can intercept web traffic by manipulating vulnerable domains
0 views • 25 slides