Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Understanding Bluetooth Technology: Basics and Connection Establishment
Bluetooth is a wireless technology used for short-range communication between devices without the need for a direct line of sight. It operates in piconets, with a master coordinating communication with up to seven active slaves. The process of establishing a connection involves procedures like inqui
1 views • 39 slides
IEEE 802.11 and Bluetooth Coexistence Simulations: Assumptions and Models
This document presents simulations on the coexistence of IEEE 802.11 (Wi-Fi) and Bluetooth technologies in the 5.945GHz to 6.425GHz spectrum. It explores various assumptions and models, including spectrum usage, channelization, scenario setups for Bluetooth and Wi-Fi links, and the capabilities of b
6 views • 54 slides
Bluetooth SIG September 2023 Update on Spectrum Sharing Plans
Bluetooth SIG provided an update on their actions and plans for sharing the 5 and 6 GHz bands with incumbents and unlicensed devices. They aim to collaborate with the Wi-Fi industry to enable equitable sharing for Bluetooth, particularly focusing on the 6 GHz band. The overall plan includes forming
4 views • 8 slides
Improving performance of LBT-enabled NB devices
This submission delves into optimizing the performance of narrowband signals like Bluetooth by utilizing Listen-Before-Talk (LBT) for channel access in the 5 and 6 GHz frequency bands. The study explores the potential advantages for Bluetooth devices in improving efficiency and reliability through L
0 views • 15 slides
Update on Bluetooth SIG's Spectrum Sharing Plans
This update discusses Bluetooth SIG's actions and plans for sharing the 5 and 6 GHz bands with incumbents and unlicensed devices. It highlights the goals, the overall plan, recent actions, and collaboration with the Wi-Fi industry to enable equitable sharing of these bands. The detailed plan involve
0 views • 9 slides
Update on Bluetooth SIG's Plans for Spectrum Sharing in January 2024
Bluetooth SIG presents an update on their actions and plans for sharing the 5 and 6 GHz bands with incumbents and unlicensed devices. Recognizing the need for future growth, they aim to collaborate with the Wi-Fi industry to develop optimal sharing mechanisms in the 6 GHz band. Their plan includes c
0 views • 11 slides
Understanding Bluetooth Low Energy Addresses in IEEE 802.11-21/1535r0
The document explores the features of resolvable addresses in Bluetooth Low Energy (BLE) within the IEEE 802.11-21/1535r0 standard. It discusses the two types of addresses in BLE, Public and Random, and their usage. The emphasis is on Random addresses due to their popularity and privacy features. Th
2 views • 11 slides
Explore the World of Bluetooth Technology
Discover the fascinating world of Bluetooth technology which enables wireless connections between various electronic devices without the need for cables. Learn about its development by a group of renowned electronics manufacturers, its association with King Harald Bluetooth of Denmark, and how it ov
1 views • 30 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
IEEE 802.11-23/1999r0: Beacon Reception Impact of Narrow-Band Frequency Hopping Interference
Explore the impact of Narrow-Band Frequency Hopping (NBFH) interference on Wi-Fi beacon reception in IEEE 802.11-23/1999r0. The study delves into beacon traffic characteristics, spectrum usage assumptions, scenario analysis with Bluetooth links, and channelization details for Bluetooth ACL versus is
0 views • 15 slides
TT Lock - Smart Lock Management Software Overview
TT Lock is a comprehensive management software designed for smart locks, offering functionalities such as key and card management, Bluetooth unlocking, attendance monitoring, system settings, and more. The software supports various types of smart locks and facilitates easy installation via the iOS a
2 views • 55 slides
Understanding BLE Security in EECS 582 - Spring 2015
Delve into the realm of Bluetooth Low Energy (BLE) security as covered in EECS 582 during the Spring of 2015. Explore topics including BLE refresher, attacks, improvements, authentication, and privacy. Gain insights into the BLE layers, connection establishment, encryption methods, and more to enhan
0 views • 16 slides
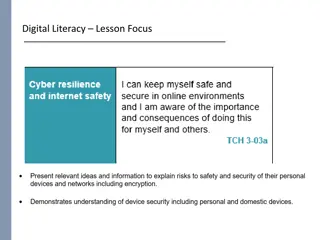
Enhancing Digital Literacy and Security Practices
Explore key topics such as securing USB sticks, setting up VPNs, and addressing Bluetooth security issues to enhance your digital literacy and protect your devices from potential threats. Learn essential strategies and preventive measures to safeguard your information and maintain a secure online pr
0 views • 11 slides
Exploring Bluetooth Technology and IoT Initiative at University of Notre Dame
Dive into the world of Bluetooth technology and the Internet of Things (IoT) through the 2018 Summer Engineering Program at the University of Notre Dame. Learn about the innovative Bluetooth's history, key characteristics, topology including piconet and scatternet, and more. Get insights into Blueto
0 views • 28 slides
Understanding Wireless Network Threats and Vulnerabilities
Explore the various threats and vulnerabilities present in wireless networks, including different types of attackers, weaknesses in WLAN security standards, such as WEP, and the risks associated with Bluetooth and Ad Hoc networks. Learn about the profiles of cyber attackers and the importance of imp
2 views • 20 slides
Update on Bluetooth SIG Actions for Spectrum Sharing
This update focuses on Bluetooth SIG's plans to share the 5 and 6 GHz bands with incumbents and unlicensed devices. It discusses the goals, overall plan, recent actions, and collaboration with the Wi-Fi industry to secure the future growth of Bluetooth technology in these bands.
0 views • 9 slides
Introduction to NXT-G Binary Bluetooth Functions for Brick-to-Brick Communication
Explore the history of Bluetooth and learn how it works, from activating Bluetooth on the NXT Brick to disconnecting it. Understand programming binary Bluetooth commands for brick-to-brick communication, connecting multiple devices in a master-slave piconet architecture. See images illustrating the
0 views • 12 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Channel Access Simulation Study for Bluetooth-Wi-Fi Coexistence in IEEE 802.11-23
A detailed simulation study was conducted to analyze the coexistence of Bluetooth and Wi-Fi in the IEEE 802.11-23 standard. The study covered aspects such as channel access, transmission setup, Bluetooth-Wi-Fi interactions, impact on latency, throughput, and observations on performance under various
0 views • 14 slides
Smart IoT Lock for Convenient Home Access
A detailed exploration of an Internet of Things (IoT) solution that revolutionizes home security by introducing a smart lock system. By implementing an IoT lock on your front door, you can effortlessly unlock the door as your phone comes in proximity and it locks automatically when you move out of r
0 views • 8 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Robotics Training Essentials
Explore the fundamental components of robotics training including sensors, switches, loops, example codes, ports, Bluetooth connectivity, and more. Learn about various sensors like light, gyro, and ultrasonic, and how they evaluate the robot's surroundings. Understand the importance of switches and
0 views • 15 slides
Holistic Approach to IoT Communication: Connecting to BLE Devices
Explore a comprehensive approach to problem-based education in ICT through international collaboration under pandemic conditions. Discover the process of connecting to Bluetooth Low Energy (BLE) devices using devices like FiPy with ESP32 Pycom, and iNode Care Sensor PHT. Learn about Bluetooth method
0 views • 17 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Advanced Wireless Networks: Bluetooth Technology Overview
Bluetooth technology, adopted as IEEE 802.15.1 standards, is designed as a short-range, low-power, and inexpensive wireless cable alternative. This technology enables communication between a master device and up to 7 slave devices in a piconet structure. Scatternets allow overlapping piconets, enabl
0 views • 27 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
A Comprehensive Guide to Binary Bluetooth Functions for Brick-to-Brick Communication
Explore the fascinating world of binary Bluetooth functions for seamless brick-to-brick communication. Learn about the history of Bluetooth, how it works, activating and disconnecting Bluetooth on the EV3 brick, programming binary Bluetooth commands, and more.
0 views • 12 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Introduction to Bluetooth Low Energy (BLE) Technology
Bluetooth Low Energy (BLE) is a wireless protocol that enables direct connections between devices such as phones and health trackers. It is a lightweight subset of classic Bluetooth, offering advantages like low power consumption and faster throughput. BLE devices typically have two roles: periphera
0 views • 19 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
Update on Bluetooth SIG's Plans for Spectrum Sharing
Bluetooth SIG provides an update on their actions and plans for sharing the 5 and 6 GHz bands with incumbents and unlicensed/license-exempt devices. The document outlines Bluetooth SIG's goals, overall plan, recent actions, and next steps in collaborating with the Wi-Fi industry to secure the future
0 views • 9 slides