Efficient Key Recovery Attack on SIDH
Efficient key recovery attack on Supersingular Isogeny Diffie-Hellman (SIDH) protocol. It explores the vulnerability of the protocol and proposes a concrete solution. The attack leverages auxiliary points to solve the isogeny problem and reveals instances of the common secret key.
5 views • 22 slides
Myocardial infarction
Myocardial infarction (heart attack), including its types, causes, symptoms, and first aid techniques. Discover how to recognize the signs of a heart attack and provide immediate care at home or in a hospital setting.
2 views • 14 slides
Fernandes Thriving in United's Resurgent Attack^J Euro 2024 Success
Fernandes Thriving in United's Resurgent Attack, Euro 2024 Success\n\nhttps:\/\/blog.worldwideticketsandhospitality.com\/2024\/02\/15\/fernandes-thriving-in-uniteds-resurgent-attack-euro-2024-success\/\n\nUEFA Euro 2024 fans from all over the world can book European Championship 2024 Tickets on our
2 views • 5 slides
Information Security – Theory vs. Reality
Exploring the concept of fault attacks in hardware security, this lecture delves into the various techniques used to compromise systems through non-nominal and nominal channels, as well as the potential risks introduced by trojan horses in the IT supply chain. The discussion includes differential fa
1 views • 37 slides
Understanding Modern Phishing Techniques and Evilginx Framework
Explore the evolution of phishing from its inception to modern-day strategies like Evilginx, a man-in-the-middle attack framework. Learn about the effectiveness of phishing, its impact on financial losses, and how Evilginx bypasses multi-factor authentication to capture sensitive information. Dive i
7 views • 30 slides
Effective Workflow for Vulnerability Research in Production Environments
Professional vulnerability research involves finding bugs efficiently through fuzzing techniques. The main goal is to develop a comprehensive workflow and toolset for effective bug discovery and triaging. Ancillary goals focus on determining exploitability, optimizing human and CPU efficiency, and e
0 views • 69 slides
National Wildfire Coordinating Group (NWCG) - S-200 Initial Attack Incident Commander Course Overview
NWCG aims to enhance coordination among wildfire management agencies to improve fire management program effectiveness. The S-200 course focuses on transitioning from Operations to Command roles, developing leadership skills, incident management, and evaluation techniques. Student evaluation includes
0 views • 12 slides
Insights into Application Security Testing and Best Practices
Dive into the world of application security testing with a seasoned practitioner's advice and musings. Explore the basics, types of testing, initial steps like reconnaissance, user inputs, test cases, attack strategies, and useful tools. Learn about code reading techniques and key hints for securing
0 views • 27 slides
Understanding Fingerprint Development Techniques
Exploring the development of latent fingerprints through physical and chemical methods, conditions affecting latent prints, and various fingerprint development techniques like visual examination, powder techniques, and chemical techniques. Techniques such as alternate light sources and powder method
2 views • 22 slides
First Nations Attack on Fort Michilimackinac 1763: Causes, Tribes, and Aftermath
The First Nations' attack on Fort Michilimackinac in 1763 was triggered by British actions that disrupted their way of life. The Ojibwe, Odawa, Potawatomi, Ottawas, and Hurons were involved in the attack, led by Chief Pontiac. Following the attack, the British did not rebuild the fort but establishe
1 views • 7 slides
Information Security Tabletop Exercise: Malware & DDOS Attack
Conduct a tabletop exercise focused on a malware and DDOS attack scenario at your company. Explore incident response, decision-making, communication, and coordination among your crisis team. Enhance preparedness and identify gaps in your cybersecurity strategy to effectively mitigate threats. The ex
0 views • 21 slides
Enhancing Cybersecurity for Windows Infrastructure: A Practical Guide
In this informative session, Vladimir Stefanovi, a seasoned System Engineer and Technical Trainer, sheds light on the vulnerabilities of Windows servers and provides valuable insights on how to protect and fortify your infrastructure against cyber threats. From traditional to modern attack vectors,
0 views • 21 slides
Exploring Cinematography and Lighting in "Attack the Block
Discover how cinematography and lighting play a crucial role in shaping the visual aesthetics of the film "Attack the Block." Dive into key sequences and technical terminology to understand how these elements contribute to the overall look and feel of the movie. Explore the use of various camera sho
1 views • 10 slides
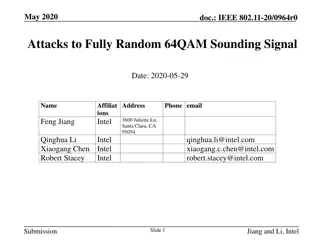
Attacks on Fully Random 64QAM Sounding Signal in IEEE 802.11-20/0964r0
Presentation by Intel demonstrates vulnerabilities in fully random QPSK and 64QAM sounding signals in IEEE 802.11-20/0964r0. Proposed attack methods, including Viterbi equalizer attacks, and solutions such as Secure LTF mechanism and windowed FFT are discussed to enhance security in ranging. The pre
0 views • 31 slides
Understanding Network Denial of Service (DoS) Attacks
Network Denial of Service (DoS) attacks aim to disrupt services by overwhelming them with traffic. These attacks can occur at various layers of the network stack and exploit weaknesses to achieve their goal. Amplification attacks, such as the Smurf attack and DNS Amplification attack, can significan
2 views • 52 slides
Duane Wolf Attack Simulation Study: Insights for Law Enforcement Officers
Duane Wolf conducted an attack simulation study to test the speed at which an un-handcuffed suspect sitting on a curb can launch an attack on officers. The study involved volunteers in different leg positions to mimic real-life scenarios. Findings emphasized the importance of officers staying alert
0 views • 9 slides
World War II in the Pacific: Unfolding of Events Post Pearl Harbor Attack
The war in the Pacific escalated post the Pearl Harbor attack with Japan's domination over various territories, including the Philippines leading to significant battles like the Japanese Invasion of the Philippines and Doolittle's Raid. American strategy, led by figures like Gen. MacArthur, played a
0 views • 12 slides
Adversarial Risk Analysis for Urban Security
Adversarial Risk Analysis for Urban Security is a framework aimed at managing risks from the actions of intelligent adversaries in urban security scenarios. The framework employs a Defend-Attack-Defend model where two intelligent players, a Defender and an Attacker, engage in sequential moves, with
1 views • 26 slides
Understanding Blending Attacks on Mixes by Meng Tang
Explore the effectiveness of blending attacks on mixes, including steps of a blending attack, attack models, factors affecting the attack, defense strategies, and insights from the attacker's viewpoint.
0 views • 25 slides
Multi-phase System Call Filtering for Container Security Enhancement
This tutorial discusses the importance of multi-phase system call filtering for reducing the attack surface of containers. It covers the benefits of containerization, OS virtualization, and the differences between OS and hardware virtualization. The tutorial emphasizes the need to reduce the kernel
0 views • 32 slides
Understanding Vulnerabilities and Attack Surfaces in Cybersecurity
Exploring the complexities of system security metrics, this study delves into the challenges of measuring and improving security techniques. It highlights the limitations of current metrics, emphasizing the importance of evaluating the impact in deployment environments. By examining various vulnerab
0 views • 32 slides
Signature-Based IDS Schemes for Heavy Vehicles
This research focuses on developing signature-based Intrusion Detection System (IDS) schemes for heavy vehicles, particularly targeting the Controller Area Network (CAN) bus. The study delves into various attack vectors and payloads that have targeted commercial vehicles over the years, proposing th
0 views • 18 slides
Volleyball Referee Hand Signals for Common Violations
Learn the essential hand signals used by volleyball referees to indicate common violations during a game. Signals include illegal alignment, line violation, illegal hit, delay of service, over the net, net foul, legal back row attack, illegal attack of serve back row attack, and illegal block/screen
0 views • 26 slides
Understanding Key Events in "Of Mice and Men": Curley's Attack on Lennie
In Chapter Three of "Of Mice and Men," Curley's attack on Lennie is a key incident that reveals the brutal nature of Curley and the immense strength and vulnerability of Lennie. The event not only showcases effective characterisation but also evokes sympathy for Lennie while foreshadowing the conseq
0 views • 24 slides
Defending Against Cache-Based Side-Channel Attacks
The content discusses strategies to mitigate cache-based side-channel attacks, focusing on the importance of constant-time programming to avoid timing vulnerabilities. It covers topics such as microarchitectural attacks, cache structure, Prime+Probe attack, and the Bernstein attack on AES. Through d
0 views • 25 slides
Automated Signature Extraction for High Volume Attacks in Cybersecurity
This research delves into automated signature extraction for high-volume attacks in cybersecurity, specifically focusing on defending against Distributed Denial of Service (DDoS) attacks. The study discusses the challenges posed by sophisticated attackers using botnets and zero-day attacks, emphasiz
0 views • 37 slides
Understanding the Sniper Attack on Tor Network
Explore the implications of the Sniper attack, which aims to anonymously deanonymize and disable the Tor network. Learn about defense strategies against this threat and delve into the background of large-scale internet censorship that drives the development of privacy-enhancing tools like Tor.
0 views • 54 slides
Antidotes and Screening Capacities for Dirty Bomb Attack Preparedness
Explore the preparedness strategies for dealing with the aftermath of a dirty bomb attack, focusing on antidotes, screening capacities, and medical countermeasures. Learn about the types of injuries, national stockpiles for radiological and nuclear emergencies, and different approaches to decorporat
0 views • 14 slides
Mechanism of Br2 Attack on Trans-Cinnamic Acid
The detailed anti-attack and syn-attack mechanisms of Br2 on trans-cinnamic acid are presented, illustrating the intricate steps involved in preventing or facilitating the attack of bromine on the compound. The process involves initial attack, bridgehead formation, bond rupture, bond stabilization,
0 views • 11 slides
Case Study on Acid Attack and Violence in Nigeria
This case study highlights a horrific acid attack on a young woman, B.U., and her siblings in Nigeria. The incident stemmed from a confrontation over stolen money and a rejected romantic advance, leading to severe physical and psychological consequences for the victims. The story underscores issues
0 views • 7 slides
Journey into the World of Security with Hamid Nosrati
Explore the fascinating realm of security with Hamid Nosrati, covering topics such as attack types, security standards, CIA triad, common attacks, malware, viruses, social engineering, and more. Learn about the methods, tools, and personnel used to safeguard digital assets, and delve into various cy
0 views • 30 slides
Exclusive Coverage of Eyewitness Account in Benghazi Attack
Tonight's news features exclusive interviews with a security officer who witnessed the attack on the U.S. Diplomatic Mission in Benghazi. The events of that night have been clouded by misinformation, confusion, and intense partisanship, which have overshadowed the truth. From security footage to fir
0 views • 5 slides
Understanding Fingerprint Development Techniques
Latent fingerprints are hidden impressions left by the friction ridges of the skin which require physical or chemical techniques for visualization. Factors affecting latent prints include surface type, touch manner, weather, humidity, perspiration, and suspect care. Techniques such as visual examina
0 views • 22 slides
Terrorist Attack on Indian Parliament: Trial and Convictions
An incident on 13th December 2001 where the Indian Parliament was attacked resulted in casualties. Five terrorists were killed, and four accused persons were linked to the conspiracy. Mohd. Afzal Guru and Shaukat Hussain Guru were involved in supplying materials and funds for the attack. Accused Nav
0 views • 11 slides
Collective Security in International Relations: A Comprehensive Overview
Collective security is a crucial concept in international politics, aimed at maintaining peace and preventing aggression among nations. This system calls for joint action to counter threats to global peace, originating post-World War I with the League of Nations. Based on four key principles, nation
0 views • 8 slides
Analyzing Improved Cryptanalysis of UOV and Rainbow Signature Algorithms
In this detailed study, the cryptanalysis of UOV and Rainbow signature algorithms by Ward Beullens is explored, focusing on key recovery attacks and the trapdoor structures of Oil & Vinegar and Rainbow schemes. The research highlights the complexities involved in deciphering these multivariate quadr
0 views • 11 slides
MTD-Based Self-Adaptive Resilience in Cloud Systems
Cloud systems face increasing attack surfaces, requiring resilient and self-healing mechanisms. This study explores a Moving Target Defense (MTD) approach for cloud systems, aiming to construct an attack-resilient framework through dynamic network configuration and continuous replacement of virtual
0 views • 36 slides
Analytical Techniques in Pharmaceutical Analysis
Analytical techniques play a crucial role in determining the identification and concentration of chemical substances in pharmaceutical analysis. Techniques range from simple gravimetric analysis to sophisticated methods using specialized instrumentation. Various techniques like gravimetric, titrimet
0 views • 17 slides
Social Engineering Attack Framework (SEAF) - Understanding the Process
Social Engineering Attack Framework (SEAF) provides a structured approach to executing social engineering attacks. It defines the attack framework, assists in planning and execution, and helps in verifying the success of the attack. The process involves identifying the attack goal, assessing potenti
0 views • 16 slides
Big Data-Based Security Analytics for Protecting Virtualized Infrastructures in Cloud
This paper proposes a novel big data-based security analytics approach to detect advanced attacks in virtualized infrastructures in cloud computing. By utilizing network logs and user application logs collected from virtual machines, attack features are extracted through graph-based event correlatio
0 views • 54 slides