County Election Board 101
Basic duties and responsibilities of the County Election Board, including voter registration and administration of public elections. It covers the composition of the board, qualifications of its members, officer roles, board minutes, budget estimates, and proxy usage.
142 views • 26 slides
Candidates and agents briefing
Briefing updated to cover changes under the Elections Act, including key election dates, qualifications, nominations, voter ID, polling procedures, candidate spending, integrity issues, and contacts. Details on roles such as Returning Officer and Electoral Registration Officer, election timetables,
0 views • 46 slides
APPENDIX: EVALUATION OF FIRM FUEL REQUIREMENTS AND RAA-RELATED RESULTS
This discussion focuses on the evaluation of firm fuel requirements and their relation to RAA results as well as the comparison of storage MRI and FDOR in ISO-NE. Analysis uncovers factors driving storage rMRI, impact on resource capacity during winter, and similarities between FDOR and Proxy Storag
4 views • 10 slides
What Is Proxy Card Access?
Explore the world of contactless access control. Learn how proxy cards work, their benefits, and common uses. Upgrade your security today!
1 views • 4 slides
What is the Purpose of a Proxy?
Confused about proxies? Wondering what they do and why they matter? This post wyja\u015bnia (wyja\u015bnia - Polish for \"explains\") the purpose of proxies, their benefits, and how they can impact your online experience
0 views • 6 slides
Understanding the Cold War: Phases and Perspectives in B.A. IV Semester
Cold War, characterized by economic, political, and military competition between the US and Soviet Union, stemmed from ideological differences leading to global conflicts and proxy wars in the Global South, ultimately fueling neo-colonialism and neo-imperialism.
1 views • 15 slides
Important Updates: IT Directors Meeting July 2022 & Technology Migration
In the IT Directors Meeting July 2022, key updates were shared, including the migration of Cambium Assessment to Amazon Web Services (AWS) and changes in platform support for ChromeOS, Windows, and macOS. The meeting emphasized the need for updating firewall allowlists and proxy settings. Additional
0 views • 12 slides
Overview of Mormon Beliefs and Practices
The Mormon religion, officially known as The Church of Jesus Christ of Latter-Day Saints, was founded by Joseph Smith in the 1830s in the U.S. Mormons believe in the atonement of Jesus Christ, ongoing revelations from God, and unique practices such as proxy baptism for the deceased. They emphasize m
0 views • 8 slides
CAISO PDR-LSR: Comprehensive Overview and Implementation Guidelines
Explore the concept of Enhanced Proxy Demand Resource (PDR) - Load Shift Resource (LSR) within the CAISO framework. Learn about the design, key features, bidding options, energy services, performance evaluation methodology, and typical use calculations. Discover how the PDR-LSR aims to efficiently a
1 views • 8 slides
Employee Timesheet Approval Procedures and Self-Service Challenges
The policy outlines the importance of accurately completing timesheets and timely approvals by supervisors. It also covers proxy designations for approving timesheets in case of unavailability, along with self-service challenges employees may face. The procedure for timesheet submissions, approval d
0 views • 19 slides
Understanding Redis Cluster Distribution Approach
Redis Cluster offers a pragmatic approach to distribution, connecting all nodes directly with a service channel. Each node communicates using a binary protocol, optimized for bandwidth and speed. Nodes do not proxy queries, and communication involves messages like PING, PONG, and Gossip. Hash slot k
0 views • 17 slides
Improving Access to Healthcare for Care Homes in East of England
The healthcare improvement plan developed by the Mid and South Essex Sustainability and Transformation Partnership aims to enhance healthcare services for care home residents in the region. By leveraging innovation and technology, the initiative includes a successful proxy ordering program in partne
0 views • 29 slides
Dynamic Oracle Training in Constituency Parsing
Policy gradient serves as a proxy for dynamic oracles in constituency parsing, helping to improve parsing accuracy by supervising each state with an expert policy. When dynamic oracles are not available, reinforcement learning can be used as an alternative to achieve better results in various natura
0 views • 20 slides
Optimum Solar Proxy for Long-Term Ionospheric Studies
The search for the best solar proxy for long-term ionospheric studies is ongoing due to the lack of consistent solar radiation data. Various solar proxies have been analyzed, and the use of Mg II for foF2 and F10.7 for foE has shown promising results, describing a high percentage of variance in the
1 views • 10 slides
Insights from CO2 Measurement in Classroom Ventilation
Understand the significance of CO2 measurements in classroom ventilation for better indoor air quality and reduced infection risks. Explore the use of CO2 sensors, data analysis, and proxy models to improve ventilation systems in schools. Discover findings on airborne infection risk and variations w
2 views • 9 slides
Developing Proxy Indicators for Farm Profitability in Irish Agriculture
This study by Ciara O'Donovan focuses on developing and testing proxy indicators of farm profitability and efficiency measurements for knowledge transfer use on Irish farms. The research aims to identify indicators of farm performance, tailor them based on enterprise, scale, and seasonality, and tes
0 views • 20 slides
GOES-R ABI Aerosol Detection Product Validation Summary
The GOES-R ABI Aerosol Detection Product (ADP) Validation was conducted by Shobha Kondragunta and Pubu Ciren at the NOAA/NESDIS/STAR workshop in January 2014. The validation process involved testing and validating the ADP product using proxy data at various resolutions for detecting smoke, dust, and
1 views • 21 slides
Understanding Proposals, Offers, and Acceptance in Contracts
In Chapter 2, we delve into the essence of proposals and acceptance in legal agreements. A proposal signifies one's willingness to act or refrain from acting to secure another's agreement. Legal rules surrounding offers are discussed, along with various kinds of offers like general offers, specific
0 views • 10 slides
Proposal for AS Proxy Offer Optimization
This proposal aims to optimize AS proxy offers for TCPA and LCRA to ensure fair market prices without distorting market competition. It includes strategies like Proxy AS Price Floor Proposals and the use of L Factor to determine proxy AS offer prices. The goal is to make AS capacity available to ERC
0 views • 10 slides
Understanding Offers and Acceptance in Contract Law
Exploring the fundamental concepts of offers and acceptance in contract law, this content dives into various types of offers, legal rules surrounding offers, and the significance of acceptance in forming a binding agreement. From express and implied offers to specific and standing offers, learn abou
0 views • 14 slides
Understanding Unidirectional Updatable Encryption and Proxy Re-Encryption
Unidirectional updatable encryption and proxy re-encryption are key concepts in secure cryptography deployments. Key management and rotation are essential for secure encryption schemes such as Proxy Re-Encryption (PRE) and Updatable Encryption (UE). PRE allows delegation of decryption abilities, whi
0 views • 16 slides
Importance of Internet Security and Setting Up an Office Proxy Server
Learn how to enhance internet security by setting up an office proxy server to limit staff web surfing. Understand the risks associated with system flaws in Windows, Mac, browsers like Internet Explorer, Firefox, Chrome, and the immediate threat of Zero-Hour Attacks by hackers.
0 views • 28 slides
Stepping Stone Detection at the Server Side: Real-Time Algorithm
An innovative real-time algorithm is introduced to detect the use of a proxy as a stepping stone from the server's perspective. The solution addresses the limitations of existing methods by focusing on TCP connection initiation. Previous research and vulnerabilities related to proxy servers and step
0 views • 37 slides
German eID and eIDAS: Secure Digital Identification Overview
The German eID system, including eIDAS integration, offers secure digital identification services through government-issued ID cards with embedded chips. It allows citizens and service providers to authenticate each other securely online. The system emphasizes interoperability and privacy protection
0 views • 16 slides
Proxy Access to Medications Implementation Stages
This document outlines the implementation stages for proxy access to medications. It covers agreements with healthcare providers, prerequisites including compliance and data sharing agreements, and systems configuration for access to medical records. The stages include setting up access for care pro
0 views • 7 slides
Proxy Voting in Indian Elections: Developments and Perspectives
India has seen progress in allowing proxy voting for Non-Resident Indians, with recent proposals to extend this privilege to overseas Indians. The initiative aims to enhance voter participation, especially for those residing abroad. While some political parties support proxy voting, concerns exist r
0 views • 35 slides
Defensive Tactics Against Hostile Takeovers in Mergers and Acquisitions
Hostile takeovers in mergers and acquisitions involve one company acquiring another directly from shareholders without board approval. Tactics include tender offers, proxy fights, poison pills, crown jewels defense, golden parachutes, and Pac-Man defense to deter or resist takeovers.
0 views • 15 slides
Enhancing Air Quality Forecasting with TEMPO Retrievals in Proxy Observing System
Improvements in Air Quality Forecast Skill (AQFS) are explored by assimilating TEMPO retrievals in a Proxy Air Quality Observing System (AQOS) using WRF-Chem/DART. The study focuses on benefits identified through a designed OSSE scenario, including application to the Front Range Air Pollution and Ph
0 views • 8 slides
Trust as a Proxy for Certainty in Social Cohesion
Exploring the intricate relationship between trust, security, and social cohesion, this study delves into how trust serves as a proxy for certainty in uncertain environments. By analyzing societal properties and the role of trust in managing risks and insecurities, the Peace Research Institute Oslo
0 views • 16 slides
Updates on GOES-R Aerosol Optical Depth Validation Activities
Generated proxy data algorithm enhancements for post-launch validation activities were discussed at the GOES-R AWG 2nd Validation Workshop in January 2014. The use of MODIS reflectances as a proxy for ABI to retrieve Aerosol Optical Depth (AOD) was emphasized, along with the importance of AERONET gr
0 views • 25 slides
Proxy QoS Management for XR Devices in IEEE 802.11-23/1958r0 - November 2023
This document discusses the challenges faced by XR devices in terms of size, thermal constraints, cost, and power limitations leading to the proposal of Proxy QoS Management to enhance Wi-Fi performance. The aim is to leverage TGbn devices for improving legacy devices' connectivity within a Wi-Fi ne
0 views • 6 slides
Privacy Preservation in Machine Learning Systems via Proxy Use
Proxy use in machine learning systems is crucial for preserving privacy, especially in scenarios where fairness and privacy are at risk. This involves defining influential sub-programs, both qualitatively and quantitatively, to protect sensitive attributes. By utilizing proxies effectively, it enabl
0 views • 15 slides
Achieving Pay Equity Using Proxy Comparison Method in Ontario
Presentation by Doreen Lurie on achieving and maintaining pay equity in Ontario through the proxy method of comparison. Covers an overview of the Pay Equity Act, differences from Employment Standards, purpose of the act, and basic pay equity terms.
0 views • 5 slides
Setting Up a Proxy for Web Time Entry Approvers
Setting up a proxy is essential for Web Time Entry Approvers to ensure seamless approval processes when out of the office. Follow the outlined steps to grant proxy access and maintain security protocols. Remember to remove proxies when necessary and contact Payroll for any assistance.
0 views • 5 slides
Understanding Dynamic Proxy in Java for Type-Safe Proxy Objects
Learn about creating dynamic proxy classes in Java to implement interfaces at runtime without pre-compilation, enabling type-safe proxy object creation for method invocations. This allows for flexible and efficient handling of method calls through uniform interfaces.
0 views • 16 slides
Understanding Web Proxies and Proxy Architectures
Web proxies play a crucial role in networking by facilitating web requests between clients and servers. They come in various types such as forward proxies, reverse proxies, and open forward proxies, each with unique functionalities like content filtering, translation, and load balancing. This articl
0 views • 15 slides
Understanding the Impact of Proxy on Disability and Health Determinants Association
National surveys are evaluating standardized disability identifiers. The Washington Group Short Set and American Community Survey are being compared in the National Health Interview Survey. Limited research exists on these questions in disability research, providing an opportunity for analysis. The
0 views • 15 slides
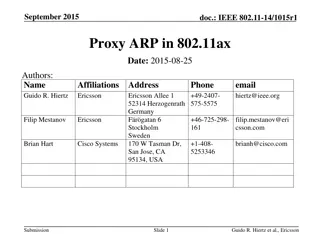
Understanding Proxy ARP Implementation in IEEE 802.11ax
Proposed in September 2015, the document discusses the implementation of Proxy ARP with 802.11ax Access Points. It explains the Address Resolution Protocol (ARP), detailing how devices in a LAN communicate using MAC and IP addresses. The submission aims to provide comprehensive explanations on Proxy
0 views • 18 slides
Understanding Mobile Proxy Ecosystem: Privacy and Security Implications
The paper delves into the emerging trend of mobile proxy services, specifically focusing on the use of mobile devices as proxy peers. It addresses the security and privacy concerns associated with this practice, highlighting the potential risks posed to end-users. The study offers novel insights int
0 views • 21 slides
Proxy Effects and Fair Adaptation for Dynamic Adaptive Streaming
This study focuses on the implementation of a proxy effect analysis and fair adaptation algorithm for managing multiple competing dynamic adaptive streaming over HTTP clients. By considering factors like client awareness, network structure, and adaptation decisions, the algorithm aims to mitigate ne
0 views • 16 slides