Social Balance Theory and Network Interactions
Explore social balance theory and its application in network interactions, based on chapters 10 and 11 of "Networks, Crowds, and Markets" by D. Easley and J. Kleinberg. Learn about global balance index, exchange cost, social power, network building algorithm, random and scale-free networks, matching
3 views • 27 slides
Apache MINA: High-performance Network Applications Framework
Apache MINA is a robust framework for building high-performance network applications. With features like non-blocking I/O, event-driven architecture, and enhanced scalability, MINA provides a reliable platform for developing multipurpose infrastructure and networked applications. Its strengths lie i
3 views • 13 slides
Modeling and Generation of Realistic Network Activity Using Non-Negative Matrix Factorization
The GHOST project focuses on the challenges of modeling, analyzing, and generating patterns of network activity. By utilizing Non-Negative Matrix Factorization (NMF), realistic network activity patterns can be created and injected into live wireless networks. Understanding and predicting user behavi
4 views • 28 slides
Evolution of Mathematical Theories and Proof Systems
Development of mathematical theories such as model theory, proof theory, set theory, recursion theory, and computational complexity is discussed, starting from historical perspectives with Dedekind and Peano to Godel's theorems, recursion theory's golden age in the 1930s, and advancements in proof t
1 views • 29 slides
Psychological Theories of Criminality: Understanding the Roots
Psychological theories of criminality delve into the association between intelligence, personality, learning, and criminal behavior. Major theories include Psychodynamic Theory by Freud, Behavioral Theory by Bandura, and Cognitive Theory by Kohlberg. These theories explore how unconscious mental pro
1 views • 20 slides
Understanding Max Flow in Network Theory
In network theory, understanding the concept of maximum flow is crucial. From finding paths to pushing flow along edges, every step contributes to maximizing the flow from a source to a target in the graph. The process involves determining capacities, creating flows, and calculating the net flow ent
2 views • 41 slides
Network Compression Techniques: Overview and Practical Issues
Various network compression techniques such as network pruning, knowledge distillation, and parameter quantization are discussed in this content. The importance of pruning redundant weights and neurons in over-parameterized networks is highlighted. Practical issues like weight pruning and neuron pru
0 views • 37 slides
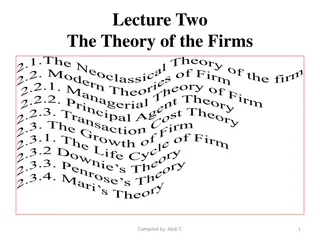
Understanding the Theory of Firms: Neoclassical vs. Modern Approaches
The theory of firms is explored through the Neoclassical and Modern perspectives. Neoclassical theory focuses on profit maximization, while Modern theory delves into managerial, principal-agent, and transaction cost theories. The discussion covers criticisms of Neoclassical theory and the essential
1 views • 79 slides
Network Slicing with OAI 5G CN Workshop Overview
Overview of Network Slicing with OAI 5G CN workshop focusing on the crucial role of network slicing in realizing the service-oriented 5G vision. This workshop covers topics like multiple logical networks creation on shared infrastructure, different types of network slices, preparation and instantiat
1 views • 6 slides
Elements of Social Action: Understanding Human Behavior in Society
Social action plays a vital role in analyzing human behavior within a society. Max Weber's concept emphasizes how actions influence and are influenced by others, holding subjective meanings. Talcott Parsons outlined five components: actor, objective, social situation, normative orientation, and ener
1 views • 9 slides
Theories of Causation in Psychological and Social Sciences
Overview of theories of causation categorized into psychological, social psychological, and sociological perspectives. Psychological theories focus on instinctive, biological, and psychological qualities of abusers, including Attachment Theory, Psychodynamic Theory, Social Learning Theory, and Situa
0 views • 15 slides
Understanding Political Theory through a Contextual Approach
Exploring G.H. Sabine's perspective on political theory through a contextual approach, emphasizing the importance of historical context and societal influences. Sabine argues that while political theory evolves with its contemporary politics, it should be analyzed within its specific time and social
0 views • 9 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
Evolution of Light Theory: From Wave Theory to Quantum Theory
At the turn of the century, the discovery of the photoelectric effect challenged the wave theory of light, leading to the development of the quantum theory by Max Planck and Albert Einstein. This new theory introduced the concept of discrete energy units known as quanta, bridging the gap between wav
1 views • 62 slides
Understanding Actor Analysis in British Parliamentary Debates
This detailed analysis explores the concept of Actor Analysis in British Parliamentary debates, covering aspects such as preparation, in-round analysis, and weighing actor impacts. It emphasizes the importance of considering various factors including socio-economic status, minority groups, and histo
0 views • 10 slides
Dp-branes, NS5-branes, U-duality, and M-Theory Overview
Overview of Dp-branes, NS5-branes, and U-duality derived from nonabelian (2,0) theory with Lie 3-algebra. Introduction to M-theory, including M2-branes and M5-branes in the strong coupling limit. Discussion on BLG theory, Lorentzian Lie 3-algebra, and the ABJM theory for M2-branes.
1 views • 32 slides
Reactor: A Case for Predictable, Virtualized Actor Database Systems
Exploring the integration of actor programming models in modern relational databases to achieve high performance. The focus is on addressing challenges related to stored procedures, data partitioning, modularity, isolation, software engineering, and performance. The talk outlines motivation, the rel
0 views • 41 slides
Multi-Actor Approach for Sustainable Chemical Use in Agriculture
The project focuses on engaging various actors in the sustainable use of chemicals in agriculture to address the hot-spots of chemical exceedance in European groundwater. Through a multi-actor partnership and action labs, the initiative aims to implement effective management practices and mitigation
0 views • 16 slides
Transportation Network Modeling and Analysis with C.Coupled SE Platform
This content outlines the features and functionalities of the C.Coupled SE Platform (CSET Platform) developed by the Connetics Transportation Group. It covers aspects such as interface design, inputs merging, purposes, platform development using Cube, TAZs merging, and network attributes. The platfo
0 views • 11 slides
Understanding Time-Independent Perturbation Theory in Quantum Mechanics
Perturbation theory is a powerful tool in solving complex physical and mathematical problems approximately by adjusting solutions from a related problem with known solutions. This theory allows for more accurate approximate solutions by treating the difference as a small perturbation. An example inv
0 views • 19 slides
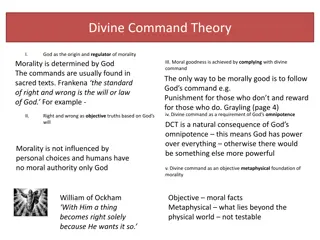
Ethical Theories: Divine Command vs. Virtue Theory Explained
Divine Command Theory asserts that morality is derived from God's commands, contrasting with Virtue Theory which focuses on developing moral virtues to achieve human flourishing and excellence. Divine Command Theory relies on religious texts, while Virtue Theory emphasizes the cultivation of virtues
0 views • 24 slides
Understanding Fermi Liquid Theory in Interacting Fermion Systems
Fermi liquid theory, also known as Landau-Fermi liquid theory, is a theoretical model that describes the normal state of metals at low temperatures. Introduced by Landau and further developed by Abrikosov and Khalatnikov, this theory explains the similarities and differences between interacting ferm
0 views • 23 slides
A Deep Dive into the Pony Programming Language's Concurrency Model
The Pony programming language is designed for high-performance concurrent programming, boasting speed, ease of learning and use, data race prevention, and atomicity. It outperforms heavily optimized MPI versions in benchmarks related to random memory updates and actor creation. With an API adopted f
0 views • 33 slides
Meridian: An SDN Platform for Cloud Network Services
Meridian is an SDN platform developed by Mohammad Banikazemi, David Olshefski, Anees Shaikh, John Tracey, and GuohuiWang at IBM T. J. Watson Research Center. The platform focuses on providing cloud network services efficiently. It encompasses an architecture that enables faster and more convenient n
0 views • 21 slides
Computational Learning Theory: An Overview
Computational Learning Theory explores inductive learning algorithms that generate hypotheses from training sets, emphasizing the uncertainty of generalization. The theory introduces probabilities to measure correctness and certainty, addressing challenges in learning hidden concepts. Through exampl
0 views • 43 slides
The Fascinating Life of Frank Sinatra: Singer, Actor, and Car Enthusiast
Frank Sinatra, the iconic American singer and actor, began his music career as a teenager and captured hearts with timeless classics like "Fly Me to the Moon." Apart from his musical talents, Sinatra also had a passion for cars, owning a luxurious 1967 Lamborghini Miura. Sadly, the world lost this l
0 views • 5 slides
Automata Theory and Theory of Computation Overview
This course overview covers concepts in automata theory and theory of computation, including formal language classes, grammars, recognizers, theorems in automata theory, decidability, and intractability of computational problems. The Chomsky hierarchy, interplay between computing components, modern-
0 views • 42 slides
Theories of Interest in Microeconomics II
Explore various theories of interest in economics, including the Classical Theory, Liquidity Preference Theory by Keynes, Productivity Theory, Abstinence Theory, Time-Preference Theory, Fisher's Time Preference Theory, and the Loanable Fund Theory. These theories offer different perspectives on the
0 views • 6 slides
Exploring the Evolution of Atomic Theory
Delve into the historical journey of atomic theory starting from Democritus and Aristotle's views to modern advancements proving some aspects of Dalton's theory incorrect. Learn about key laws and theories such as the Particle Theory of Matter, Dalton's Atomic Theory, and JJ Thomson's discoveries, s
0 views • 30 slides
Actor-Based Services: Geo-Distribution Challenges and Solutions
Explore the complexities of geo-distributing actor-based services, handling multiple users, devices, data centers, and concurrent code execution. Delve into client app architecture, challenges of correctness under failures, and the quest for the right abstractions in composed services. Discover stra
0 views • 54 slides
Understanding Network Analysis: Whole Networks vs. Ego Networks
Explore the differences between Whole Networks and Ego Networks in social network analysis. Whole Networks provide comprehensive information about all nodes and links, enabling the computation of network-level statistics. On the other hand, Ego Networks focus on a sample of nodes, limiting the abili
0 views • 31 slides
Decentring Collective Action in Internet Activism: A Study on Collective Agency in China
This study explores the concept of collective agency in internet activism within the context of social movements in China. It discusses the role of ICT in virtual collective action, the structural preconditions for collective action, and the shift towards a more decentralized approach to collective
1 views • 16 slides
Network Function Virtualization (NFV) Overview
Network Function Virtualization (NFV) focuses on virtualizing network functions to improve efficiency and reduce costs in network infrastructure. The lecture discusses key readings, devices that compose a network, specialization of devices, benefits of one-device-does-anything approach, and the goal
0 views • 21 slides
Enhancing Network Stability with Network Monitoring Systems
Network monitoring is crucial for efficient management and proactive issue detection in a network environment. Factors influencing an effective network system include choosing the best OEM, SLA agreements, and selecting a reliable System Integrator. Reactive monitoring can lead to financial losses a
0 views • 12 slides
Jihadi Governance by Lake Chad: Research on ISWAP's Governing Techniques
Research by Alessio Iocchi explores ISWAP's development of governing techniques in Lake Chad, emphasizing the interaction with civilian populations. The study draws on actor-network theory and the dialectic of trans-local entanglement, revealing ISWAP's adaptation to the geographical and human conte
0 views • 11 slides
Macromechanical Analysis of Lamina and Tsai-Hill Failure Theory Overview
The Tsai-Hill failure theory is based on the strengths of a unidirectional lamina, incorporating longitudinal and transverse tensile and compressive strengths, as well as in-plane shear strength. This theory, derived from the distortion energy theory, provides criteria for determining lamina failure
0 views • 15 slides
Understanding Network Breaches: Methods and Mitigation
Discover how networks are breached through phishing, exposed services, and publicly available exploits as explained by a security consultant. Learn about phishing techniques, externally exposed services vulnerabilities, and common exploits used to gain unauthorized access. Explore ways to mitigate t
0 views • 22 slides
Traffic Routing and Game Theory in Network Design
Explore the intersection of traffic routing and game theory in network design scenarios. Delve into concepts like Atomic Congestion Games, Potential Function, Price of Anarchy and Stability, Nash Equilibrium, Braess's Paradox, and the pursuit of Pure Strategy Nash Equilibriums in traffic routing gam
0 views • 16 slides
Accelerating Systemic Change Network Inaugural Workshop Summary
The Accelerating Systemic Change Network held its inaugural workshop at Howard Hughes Medical Institute in July 2016 to address the lack of coordination in improving higher education. With a vision to become a professional hub for change researchers in STEM education, the network aims to enhance ind
0 views • 5 slides
University Network Section Overview July 2015 - March 2016
The presentation covers the network team structure, team members, objectives, goals, report outline, network statistics, accomplishments, and future plans of the university network section from July 2015 to March 2016. It highlights efforts to provide stable internet and intranet services, restructu
0 views • 16 slides