Navigating Financial Aid Verification for 2024-25
Learn about the current practices and upcoming changes in financial aid verification for the 2024-25 academic year at the SCASFAA Annual Conference. Discover the key tracking groups, standard requirements, and considerations for students and parents regarding household size and support. Get insights
0 views • 29 slides
Electors Verification Program and Special Summary Revision Activities
The Electors Verification Program (EVP) aims to encourage citizens to authenticate their electoral details through various methods like mobile apps, portals, and Common Service Centers. The program includes verifying existing entries, collecting family information, enrolling unenrolled citizens, and
0 views • 31 slides
Importance of Timely Verification in Care After Death
Understanding the verification process and importance of timely verification in care after death is crucial for improving the experience of death and dying for families. This session covers the definitions, process, and care after death, emphasizing the significance of timely verification in end-of-
1 views • 15 slides
Electors Verification Programme Overview
The Electors Verification Programme (EVP) is a campaign initiative encouraging citizens to verify and authenticate electoral details, including family members. Various methods such as NVSP, Mobile App, and 1950 helpline are utilized for verification. Citizens can also submit details through BLOs to
1 views • 25 slides
Understanding Triangle Inequalities and Angle-Side Relationships
Explore the Vocabulary of Exterior Angle Inequality Theorem, Angle-Side Relationship Theorems 5.9 and 5.10. Understand how to order triangel angle measures and side lengths from smallest to largest through examples. Discover the principles governing triangles in terms of angles and side lengths.
0 views • 12 slides
Criticisms and Defenses of Verification and Falsification Principles
Explore the criticisms and defenses of the Verification and Falsification Principles in religious language. Understand how believers defend the use of religious language and analyze challenges posed to the Verification Principle by notable thinkers like Swinburne, Hare, and Mitchell. Delve into resp
2 views • 15 slides
GLP.BBBEE.(PTY).LTD - Your Trusted BEE Verification Agency
GLP.BBBEE.(PTY).LTD is a level 3 SANAS accredited BEE verification agency with 9 years of experience specializing in complex ownership structures. They offer professional BEE verification services with a team of technical signatories ensuring fair ratings for clients across various sectors. Their ef
0 views • 7 slides
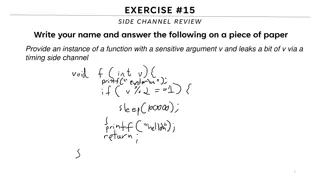
Understanding Side Channels in Software Security
This content delves into the topic of side channels in software security, focusing on the leakage of sensitive information through timing side channels. It discusses the concept of covert channels, reference monitors, limitations of analysis, and prevention strategies to mitigate the risks associate
0 views • 25 slides
Integrated Verification and Repair in Control Plane
Modern networks face challenges from incorrect configurations affecting millions of users. This presentation discusses the integration of verification and repair processes into the control plane, aiming for consistent and policy-compliant network operations. It explores the complexities of network c
0 views • 16 slides
Formal Verification and Automata Abstraction in Esterel
This content delves into the applications of formal verification and automata abstraction in Esterel, focusing on techniques such as verification by abstraction of automata, boolean verification using BDDs, bounded model checking in SAT/SMT, and more. The work of Gérard Berry at the Collège de Fra
0 views • 38 slides
Program Verification via an Intermediate Verification Language
Dive into the world of program verification through an intermediate verification language with a focus on static program verification, reasoning about programs, and separation of concerns. Explore tools like Dafny and verification architectures like Boogie and Why3, along with key concepts including
0 views • 36 slides
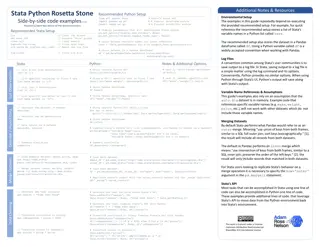
Stata-Python Rosetta Stone: Side-by-side Code Examples v1.0
A comprehensive guide providing side-by-side code examples in Stata, Python, and R, facilitating easy translation between the languages. It covers setting up Python for Stata, handling dataframes, storing datasets, working with log files, merging datasets, describing and summarizing data, and more.
1 views • 21 slides
Quality Assurance for CCE Tests at Multiple International Sites
This document outlines the quality assurance procedures for CCE tests conducted on behalf of groups from Birmingham, Ljubljana, Tsukuba, Toronto, and Valencia during the ITK week in February 2020. It covers site verifications, irradiation and test sites, testing procedures, fluence measurements, and
0 views • 11 slides
Importance of Side and Site Verification in Medical Procedures
Ensuring proper side and site verification in non-operative areas is crucial to guarantee patient safety during medical procedures. NYSSIPP standards outline the necessary protocols for correct patient identification, procedure execution, and site marking. Consent verification, pre-procedural checks
0 views • 27 slides
Software Bugs and Formal Verification in Critical Systems
Software bugs have caused catastrophic events like radiation overdoses and rocket explosions, emphasizing the importance of formal verification in ensuring software correctness. Formal verification uses mathematical models to prove software correctness, offering higher assurance, especially in safet
1 views • 26 slides
Automated and Modular Refinement Reasoning for Concurrent Programs
This research explores automated modular refinement reasoning for concurrent programs, focusing on safety and correctness in operating systems and applications. Projects like Verve and Ironclad aim to achieve end-to-end security through formal verification tools and small trusted computing bases. Th
1 views • 12 slides
Next-Generation Logic for Program Verification Challenges
Explore the innovative work by Gennaro Parlato and collaborators on a new logic for reasoning with programs that manipulate heap and data using deductive verification and SMT solvers. This research delves into the complexities of unbounded structures and data, addressing challenges in classical theo
0 views • 31 slides
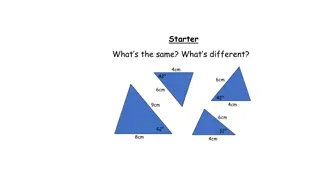
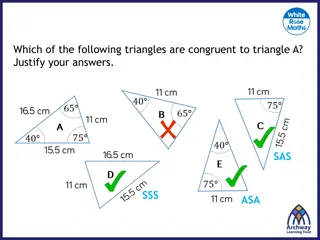
Understanding Triangle Congruence Properties
Delve into the principles of congruent triangles by exploring the properties of side-side-side (SSS), side-angle-side (SAS), angle-side-angle (ASA), and right-angle-hypotenuse-side (RHS) congruence. Visual explanations help clarify how these properties determine if triangles are congruent.
0 views • 18 slides
Constructing SSS Triangles: A Geometric Exercise
Explore the construction of Side-Side-Side (SSS) triangles step-by-step, using compass and straightedge techniques to draw triangles given specific side lengths. Understand the process of constructing triangles without angle information and enhance your geometric skills with practical examples.
0 views • 13 slides
Formal Verification of Cyberphysical Systems and Future Certification Methods
Explore the formal verification techniques and tools used in cyberphysical systems, including KeYMaera verification tool, applications in distributed car control and adaptive cruise control, and the formal verification of ACC algorithms. The future work section highlights considerations for sensor d
0 views • 17 slides
Comprehensive Solution for EU Digital COVID Certificate Verification
This solution offers face recognition, temperature monitoring, and verification of EU Digital COVID Certificates for personnel. It includes products like DHI-ASI7213X-V1-T1 and ASF172X-T1, with various unlocking modes and support for certificate verification. The system allows for accurate and fast
0 views • 7 slides
Automated Static Verification of Higher-order Functional Programs
Explore the automated static verification of higher-order functional programs, focusing on Haskell code. Learn about denotational semantics, program assertions, and tools like GHC for verification. Discover the emphasis on simplicity and structural properties for easy proofs. Consider utilizing exis
0 views • 22 slides
On-Site Burial for Carcass Disposal: Methods and Environmental Impacts
Explore the process of carcass disposal through on-site burial, covering topics such as trench burial, site selection, construction and design considerations, environmental impacts, and a comparison with other disposal methods. Learn about key factors influencing on-site burial, including soil prope
0 views • 13 slides
Gradual Program Verification and its Techniques
Gradual Program Verification introduces a method where static verification is combined with dynamic verification to ensure program correctness gradually. This approach allows for partial specifications and runtime checks to be gradually applied, reducing the risk of errors and overhead in software d
0 views • 18 slides
Enhancing Security for XMSS and SPHINCS+ Using Machine-Checked Methods
Advanced cryptographic techniques such as XMSS and SPHINCS+ are critical for ensuring secure digital signatures in a post-quantum world. This project focuses on improving the security and verification processes of XMSS and SPHINCS+ using machine-checked methods, aiming to enhance trust in these cruc
1 views • 17 slides
Warning Verification and Scoring Guidelines in Weather Forecasting Workshop
Learn about the verification of warnings, classical contingency scoring, false alarm ratio, hits, false alarms, missed alarms balance, threshold-based warning verification, and impact-based warning verification discussed in the IMS Warning workshop at KNMI Block III. Understand the importance of mai
0 views • 13 slides
Verification Modulo Versions: Towards Usable Verification
Explore the challenges and solutions in compile-time verification with CodeContracts in Visual Studio. Delve into addressing warnings, improving analysis precision, and managing syntactic baselines for a more reliable verification process.
0 views • 33 slides
Machine Learning and Artificial Neural Networks for Face Verification: Overview and Applications
In the realm of computer vision, the integration of machine learning and artificial neural networks has enabled significant advancements in face verification tasks. Leveraging the brain's inherent pattern recognition capabilities, AI systems can analyze vast amounts of data to enhance face detection
0 views • 13 slides
SKA1 Low Assembly Integration & Verification Plan
The SKA1 Low Assembly, Integration, and Verification (AIV) Plan outlines the responsibilities of the AIV Consortium, consortium partners, and the roll-out plan for the SKA1 Low telescope. The plan encompasses user requirements validation, system verification, operational concepts, and more. It detai
0 views • 12 slides
Overview of Web Libraries, Tools, and Frameworks for Building Web Apps
Explore various client-side and server-side web libraries, tools, and frameworks such as Angular, Ember, Rails, Express, jQuery, d3, and more. Learn about the importance of web app frameworks, the challenges they solve, and considerations for choosing between server-side and client-side implementati
0 views • 57 slides
Object-Oriented Software: Specification and Verification
This resource delves into theory, techniques, and architectures for verifying object-oriented software, focusing on a basic program verifier for dynamically allocated objects. It covers specification styles, verification conditions, modeling execution traces, states, and commands in a variety of lan
0 views • 11 slides
ICAO Strategic Objective: Economic Development of Air Transport Verification and Validation Overview
This content provides an in-depth analysis of the ICAO Strategic Objective focusing on the economic development of air transport through verification and validation processes for air carriers. It includes details on forms verification, economic analysis, and policy considerations discussed at the IC
0 views • 22 slides
Overview of Program Verification Tools and Techniques
Explore the pillars of program verification, early mechanical verification systems, software quality assurance, and a spectrum of verification tools used for ensuring functional correctness, safety-critical systems, and more. Discover the role of proof assistants and automatic decision procedures in
0 views • 21 slides
Understanding Triangle Congruence by SSS and SAS Postulates
Explore the Side-Side-Side (SSS) and Side-Angle-Side (SAS) postulates to prove triangle congruence. Learn how to use corresponding sides and included angles to establish congruence between triangles. Practice identifying congruent triangles and whether to use SSS or SAS for proof.
0 views • 11 slides
Exploring Triangle Similarity and Congruence
This content delves into understanding triangle congruence and similarity through various scenarios and visual representations. It discusses how to determine congruence using side-side-side, side-angle-side, and angle-side-angle criteria, and explores the concept of similarity in triangles based on
0 views • 21 slides
Introduction to UVM: Verification Methodologies Overview
Explore the Universal Verification Methodology (UVM) for writing modular, scalable, and reusable testbenches. Learn about UVM's key technical highlights, its support for migration towards Coverage Driven Verification (CDV), and the advantages of Constrained Random Verification (CRV) in functional ha
0 views • 20 slides
Comprehensive Overview of Fault Modeling and Fault Simulation in VLSI
Explore the intricacies of fault modeling and fault simulation in VLSI design, covering topics such as testing philosophy, role of testing in VLSI, technology trends affecting testing, fault types, fault equivalence, dominance, collapsing, and simulation methods. Understand the importance of testing
0 views • 59 slides
Side Channel Monitoring in Additive Manufacturing for Cybersecurity and Quality Assurance
Side channel monitoring is crucial in the field of additive manufacturing to bridge cybersecurity and quality assurance. This process involves detecting physical domain data leakage through various side channels like acoustics, thermal, laser, vibration, electric current, optical, and pressure. By m
0 views • 10 slides
DeepFace: Advancements in Face Verification Technology
DeepFace by Yaniv Taigman, Ming Yang, Marc Aurelio Ranzato, and Lior Wolf from Facebook AI Group and Tel Aviv University presents a breakthrough in face verification technology. The system achieves human-level performance by utilizing deep neural networks for face recognition, detection, alignment,
0 views • 12 slides
Side by Side Refrigerator in Pakistan: Best Picks for Spacious and Stylish Kitch
A Side by Side Refrigerator can be an exciting addition to modern kitchens that combine design space, efficiency, and space all in one piece. \/\/kinkedpress.com\/side-by-side-refrigerator-in-pakistan-best-picks-for-spacious-and-stylish-kitchens\/
1 views • 1 slides