BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Explore Diverse Courses and Study Modes for Your Future Education
Discover a range of courses at different SCQF levels, from Childcare to Cyber Security, offered by the school. Explore study modes like online, face-to-face at UHI Perth, or blended options. Consider factors like travel time, university entry requirements, and speaking with guidance teachers for gui
0 views • 20 slides
Understanding Transport Operations: Modes, Categories, and Efficiency
Explore typical transport operations across various modes, including land, water, and air transportation. Learn about the advantages and disadvantages of different modes, such as road, railway, and air transport. Delve into scheduling long-distance trips and the impact of guidelines on transport eff
1 views • 9 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Understanding Addressing Modes in Computer System Architecture
Addressing modes determine how the operand in an instruction is specified, impacting the interpretation and execution. Implied, stack, immediate, direct, indirect, register direct, register indirect, relative, indexed, base register, auto-increment, and auto-decrement are various addressing modes ex
0 views • 4 slides
Understanding Transmission Modes in Computer Networks
Transmission modes in computer networks can be divided into serial and parallel modes. Parallel transmission allows multiple bits to be sent simultaneously over separate media, while serial transmission sends one bit at a time. The choice between serial and parallel transmission depends on factors s
0 views • 13 slides
Addressing Modes and Formats in Instruction Sets
This material discusses addressing modes and formats in instruction sets, covering types of addressing modes, design trade-offs, and the distinction between machine language and assembly language. It explores the need for various addressing techniques to reference locations in memory and presents co
1 views • 58 slides
Understanding Digital Payments: Process and Security
Digital payments revolutionize the way transactions are conducted by enabling cashless transfers between payers and payees through various modes like banking cards, mobile wallets, and internet banking. This article delves into the concept of digital payments, different modes available, the pros and
0 views • 19 slides
Understanding Addressing Modes in Assembly Language
This content delves into the intricacies of addressing modes in assembly language, covering topics such as one-dimensional arrays, the DUP operator for defining arrays, and various modes like register, immediate, direct, and register-indirect modes. It explains how operands are specified in differen
2 views • 24 slides
Understanding Waveguides in Electromagnetic Theory
The concept of waveguides in electromagnetic theory involves the transmission of electromagnetic waves through hollow metallic tubes, such as rectangular and circular waveguides made from materials like copper and aluminum. These waveguides support different modes of propagation, including TE, TM, a
5 views • 15 slides
Understanding Addressing Modes in 8051 Microcontroller
Addressing modes in the 8051 microcontroller play a crucial role in specifying how data is accessed and operated by instructions. They include register addressing, direct addressing, register indirect addressing, immediate addressing, and indexed addressing modes. Each mode offers unique ways to han
2 views • 20 slides
Understanding Addressing Modes in 8086
Delve into the world of addressing modes in the 8086 processor to comprehend how different types of operands are accessed and utilized during instruction execution. Explore immediate, direct, register, register-indirect, and other addressing modes with detailed examples.
1 views • 17 slides
Coupling and Mutual Transformation of Acoustic and Gravitational Modes in Kinematically Complex Flows
This study explores the coupling and mutual transformation of acoustic and gravitational modes in kinematically complex flows. The research delves into phenomena such as stratified fluid, internal gravity waves, and formalism related to background flow and compressible cases. The presentation plan c
0 views • 20 slides
Managing Higher-order Modes in Normal Conducting RF Technology
The excitation of higher-order transverse modes due to misalignments between the beam and RF structures can lead to beam instability in linear colliders. This instability can be mitigated by selectively damping the transverse modes and/or detuning the dipole mode frequencies. Understanding the diffe
0 views • 34 slides
Understanding Transit Modes: A Comparative Analysis by Watkins, LaMondia, and Brakewood
This study delves into defining transit modes, exploring different families of transit modes, and comparing mode selection in the US. The materials developed by K. Watkins, J. LaMondia, and C. Brakewood provide insights into transit mode characteristics like right-of-way systems, technology types, a
0 views • 43 slides
Understanding Rectangular Waveguides and Cutoff Frequency
Investigate waveguides supporting non-TEM modes like TE and TM, where cutoff frequency is crucial. Rectangular waveguides with TE and TM modes are explored, detailing mode orders and field configurations. The cutoff frequency formula and standard waveguide designations are also discussed, along with
0 views • 7 slides
Understanding Modes in Data Analysis
Explore the concept of modes in data analysis through examples like ice-cream sales and mathematical connections to fashion. Learn about unimodal, bimodal, and multimodal datasets and how to identify modes effectively. Discover the significance of modes in making decisions and solving real-world pro
0 views • 9 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
0 views • 12 slides
Understanding User Mode, Kernel Mode, Interrupts, and System Calls in Computer Architecture
In modern computers following Von Newman Architecture, programs and data are stored in RAM. The CPU, RAM, ROM, and devices communicate via address and data buses. The system operates in both kernel and user modes, where kernel mode allows full system control, while user mode restricts access for sec
0 views • 29 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Understanding Failure Modes and Effects Analysis (FMEA) Training
Failure Modes and Effects Analysis (FMEA) is a methodology that helps in process improvement by identifying and eliminating concerns early in the development of a process or design. It aims to improve customer satisfaction, manage risks, and prevent defects. Training objectives include understanding
0 views • 25 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Locally-Unique Address Assignment Protocols in IEEE 802 Networks
This content discusses the Local MAC Address Protocol for locally-unique assignment of 48-bit and 64-bit addresses in IEEE 802 networks. It specifies protocols, procedures, and management objects for address assignment in a structured manner. The document also covers peer-to-peer claiming, server mo
0 views • 11 slides
Understanding ESD Force, Noise, and Range in Various Modes
This content discusses ESD force, noise, and range in different modes of operation, presenting assumptions, possible operation modes, and details on maximum range mode and noise characteristics. It explores concepts like control voltage offset, force noise calculations, and practical applications fo
0 views • 9 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
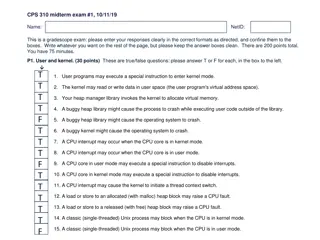
Understanding User and Kernel Modes in Operating Systems
The content provided discusses various aspects of user and kernel modes in operating systems through a set of true/false questions related to user programs, CPU interrupts, heap management, and process behavior in different modes. It touches on the role of the kernel in managing virtual memory, hand
0 views • 10 slides
The Time Cost Distance Model
The Time Cost Distance Model in Transit Corridors aims to illustrate the cost and time aspects of door-to-door movement along available routes and modes within a transit transport corridor while highlighting delays at borders or inspection points. The model proposes a methodology based on cost and t
0 views • 14 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Semiotics and Multimodality in Communication
Exploring the realm of semiotics and multimodality, this study delves into the use of multiple semiotic modes in communication. It discusses the significance of combining different modes like verbal, visual, and aural symbols to convey messages effectively. The concept of multimodal texts and their
0 views • 19 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides