CMS IT Governance Process: Intro to the Target Lifecycle
The target lifecycle governance process, including an overview of the TLC phases, the TLC framework, IT planning governance, team responsibilities, and audit requirements.
7 views • 32 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Building a Script: Steps and Best Practices for Implementation
Explore the process of moving from an idea to implementing a script, including outlining best practices, considering factors before starting, and understanding the script lifecycle with a focus on design, writing, testing, and maintenance. Discover the importance of writing code for automation, cons
2 views • 14 slides
Understanding Data Lifecycle and Mining for Business Intelligence
Explore the data life cycle, data mining, and knowledge discovery in business intelligence to transform data into valuable information for profitable business actions. Learn about data life cycle stages, data mining process, and data lifecycle management framework. Discover how data mining allows bu
2 views • 20 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Understanding Product Life Cycle Costing: A Comprehensive Analysis
Lifecycle costing involves tracking cost records of assets throughout their entire lives, optimizing asset usage at minimal cost. Product lifecycle costing accumulates a product's costs from inception to disposal, with stages like Introduction, Growth, Maturity, and Decline. It helps assess profitab
4 views • 19 slides
API Lifecycle Patterns and Practices
This document explores the significance of MuleSoft APIs in streamlining the API lifecycle process, providing insights into best practices, standards, and comparisons with other APIs. Topics include the transition from individual developer APIs to MuleSoft's comprehensive platform, clean API connect
3 views • 19 slides
Workplace Adjustments and Employee Lifecycle Overview
This content discusses the key stages in the employee lifecycle where workplace adjustments may be necessary to support employees effectively. It emphasizes the importance of providing reasonable adjustments as required under the Equality Act 2010, especially during recruitment, induction, performan
3 views • 4 slides
Understanding the Product Life Cycle: Stages and Examples
The product life cycle (PLC) concept is essential for marketers to navigate through the stages of a product's market presence - from introduction to decline. Studying PLC with reference to demand-technology dynamics provides insights into competitive strategies. The main stages are research & develo
0 views • 31 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Network Slicing Joint Proposal and Management Functions Overview
Explore the joint proposal for ONAP network slicing in Frankfurt, detailing the involvement of prominent industry players and the scoping of use cases for NSI lifecycle view. The document outlines the key tasks of 3GPP slice management functions and the network slice lifecycle specific to Frankfurt,
0 views • 27 slides
Enhancing Customer Experience in ezFedGrants Recipient Portal
Offering a comprehensive solution for grants and agreements management, ezFedGrants allows agencies and recipients to efficiently manage awards throughout the agreement lifecycle. With features tailored for both agency and recipient portals, the system streamlines processes from pre-award to closeou
0 views • 13 slides
Enhanced Award Lifecycle Management Overview
Explore the comprehensive overview of the Award Lifecycle Management process, encompassing pre-award and post-award phases. From discovering opportunities to managing awards efficiently, this guide covers essential steps such as proposal development, award setup, budget management, compliance adhere
0 views • 6 slides
BI Trends Are Enhancing Product Lifecycle Management, and It’s About Smarter Decisions
Explore how cutting-edge Business Intelligence trends are revolutionizing Product Lifecycle Management (PLM), enabling more informed and strategic decision-making. This blog delves into the transformative integration of BI into PLM processes, highlig
0 views • 9 slides
Understanding OSGi Framework for Modular Java Applications
OSGi, a dynamic module system for Java, enables loading, unloading, and upgrading modules on a running system. It provides a service-oriented, component-based environment for developers, standardized software lifecycle management, and supports various application design patterns. Apache Karaf aligns
0 views • 24 slides
Lifecycle History Report for Document State Changes
This lifecycle history report example details the time taken from document creation to entering each state, focusing on documents currently in a Released state. The report allows user input of non-sensitive document names with wildcards, listing document details, state, duration, and entry date. Use
0 views • 5 slides
Understanding Marketing Mix and Product Lifecycle in Business
Explore the concepts of marketing mix, product lifecycle, and extension strategies in business. Learn about the differences between products of small and large companies, analyze examples of products through their lifecycle stages, and discover extension strategies used by companies like iPhone, Cad
0 views • 15 slides
Management of Paddy Stemborer: Economic Importance and Lifecycle Analysis
Paddy stemborer, also known as the yellow stem borer, is a significant pest affecting paddy crops in various regions of India. This pest exhibits a lifecycle involving egg laying, larval stages inside the plant stem, pupation, and emergence as adult moths. The economic impact of paddy stemborer infe
0 views • 20 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Lifecycle and Treatment of Dicrocoelium Dendriticum - A Lancet Fluke
Plagiorchiformes is an order with diverse adult species, notably Dicrocoelium dendriticum causing Dicrocolidiasis. Its complex lifecycle involves snails, ants, and multiple hosts. The parasite can infect various animals and rarely humans. The treatment options for controlling D. dendriticum infestat
0 views • 13 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
Strategic Approach to Responsible Research Development
Strategic approach to research development covers the entire research lifecycle from identifying funding opportunities to managing awards. It discusses institutional research resources, grant lifecycle, funding sources, common funding mechanisms, and pathways to sponsored research, providing insight
0 views • 27 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Effective Change Management in the ET Project
Managing changes in the ET Project involves navigating the R&D phase, establishing a baseline design, and preparing for a lifecycle supported by proper documentation. This presentation outlines the key concepts, processes, and steps for effective change management to ensure quality and traceability
0 views • 9 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
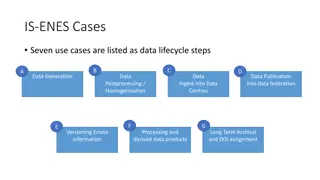
Challenges in Developing a Coherent Provenance Architecture
In the IS-ENES Cases, challenges arise in establishing a formal model for provenance architecture across various data lifecycle steps. The need for a coherent approach is emphasized to manage provenance information artifacts effectively. These challenges demand the creation of a structured framework
0 views • 11 slides
Analysis of Resource Reallocation Across Generations
The presentation discusses how various institutions like the state, market, and household reallocate resources across generations to finance the lifecycle deficit. It highlights public spending patterns, net public transfers, and the inadequacy of public transfers in covering the lifecycle deficit.
0 views • 11 slides
Development Lifecycle Overview - Roles, Systems, and Revisions
Explore the comprehensive development lifecycle encompassing acceptance mode, test mode, live mode, and maintenance. Dive into roles and organization structures, application versions, project resources, connectors, and system configurations. Witness the evolution of live and acceptance versions, alo
0 views • 4 slides
Understanding the Pork Tapeworm, Taenia solium: Appearance, Lifecycle, and Reproduction
The pork tapeworm, Taenia solium, is a potentially dangerous flatworm to humans, with a white ribbon-like body that can grow up to 9 meters in length. This parasite has distinct body parts including the scolex, neck, and strobilia. Humans can get infected by ingesting larvae in measly pork, leading
0 views • 18 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Secure IoT Application Lifecycle Overview
This presentation by Angelo Brancato delves into IoT security, focusing on malware threats in June 2016. It discusses HPE's Secure IoT Application Lifecycle, including security intelligence, data visualization, application security, and more. The presentation emphasizes the need for secure connectiv
0 views • 19 slides
Wyoming Government Savings and Efficiency Project Status Update
The Wyoming Government Savings and Efficiency Project aims to assist the Governor in implementing cost-saving initiatives authorized by Senate Enrolled Act 70 and supported by the Wyoming Spending and Government Efficiency Commission. The project's financial status, workstream budget details, planne
0 views • 18 slides
Overview of Data Analytics Lifecycle and Key Stakeholders in Projects
Understanding the Data Analytics Lifecycle is crucial for data science projects, which are exploratory in nature and involve phases like discovery, data preparation, model planning, execution, results communication, and operationalization. The lifecycle is designed for Big Data challenges with itera
0 views • 23 slides
Overview of MEF Modeling Activities in LSO and Network Evolution
This content outlines MEF's modeling activities in the context of Lifecycle Service Orchestration (LSO) and the evolving landscape of network services. It covers challenges, the vision for agile networks, lifecycle service orchestration capabilities, and the methodology for engineering LSO capabilit
0 views • 17 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Enhancing Wind Blade Reliability: Strategies for Improved Lifecycle Performance
Reliability plays a crucial role throughout the lifecycle of wind turbine blades. This workshop presentation by Gary Kanaby delves into the various stages from design to decommissioning, emphasizing the importance of proper maintenance and involvement of owner/operators. It provides insights on pree
0 views • 15 slides