Protecting Your Rights Across Borders_ Expert Legal Assistance for Cross-Border Injuries in Canada(20_03_2024)
Protecting Your Rights Across Borders: Expert Legal Assistance for Cross-Border Injuries in Canada\n\nIn today's interconnected world, accidents don't always adhere to national borders. Whether you're a resident or a visitor, being injured in Canada can present unique legal challenges, especially wh
0 views • 2 slides
Border Management Authority (BMA) FY2025 Budget Presentation: Securing Borders for Development
Presenting the Border Management Authority's (BMA) vision, mission, and value proposition for FY2025 budget allocation, focusing on secure borders for development. The establishment of BMA as a Section 3A public entity is outlined, along with the purpose of ensuring legitimate movement of goods and
3 views • 12 slides
Parsimoni – the European IoT/Edge OS. Secure, efficient, flexible.
Revolutionizing IoT/Edge computing with secure, efficient, and flexible technology, Parsimoni aims to set new standards in the industry. Led by CEO Miklos Tomka, the company leverages European open-source technology to create a secure-by-design OS for IoT/Edge applications. Seeking partners for cons
1 views • 5 slides
Crossing Borders, Finding Opportunities: Overseas Employment Agencies Explained
\"Crossing Borders, Finding Opportunities: Overseas Employment Agencies Explained\" delves into the pivotal role of agencies in connecting job seekers with global opportunities, navigating visas, and facilitating cultural integration for successful international careers.\n\n\/\/ \/overseas-recruitme
3 views • 4 slides
Talent Without Borders: The Evolution of Global Recruitment Strategies
\"Talent Without Borders: The Evolution of Global Recruitment Strategies\" explores how organizations leverage diverse talent pools worldwide, embracing technology, data, and cultural competence to drive success in today's globalized landscape. From remote work to legal challenges, discover the tran
15 views • 4 slides
Borders Climate Action Network Overview
Borders Climate Action Network aims to achieve a net-zero and climate-resilient Scottish Borders through a self-organising, inclusive network supporting communities. The network provides capacity building, gap identification, and interconnections to foster community actions. The approach focuses on
0 views • 8 slides
Understanding Secure Act 2.0 Key Provisions
In a detailed report by Dee Spivey and Angie Zouhar, key provisions of SECURE Act 2.0 are outlined, including changes in retirement plans like RMD age increase, employee certification of hardship withdrawals, and more. Secure 1.0 and Secure 2.0 differences, effective dates, and necessary actions for
5 views • 12 slides
Beyond Borders: Empowering Businesses with Overseas Manpower Consultancy Service
\"Beyond Borders: Empowering Businesses with Overseas Manpower Consultancy Services in Delhi\" explores how Delhi-based consultancy firms connect local businesses with global talent. By leveraging their expertise, these consultancies facilitate seamless international hiring, drive business growth, a
0 views • 6 slides
Beyond Borders: Choosing the Best Recruitment Agency in Kenya for Global Talent
The global pool geography is continuously evolving, and businesses are decreasingly looking beyond their borders to find the stylish gift. Whether it\u2019s for niche places that bear technical chops or to diversify the pool with transnational perspe
0 views • 9 slides
Analysis of "Borders" by Thomas King
In "Borders" by Thomas King, the story revolves around Laetitia, her mother, and their interaction with border guards. The characters exhibit different traits, with Laetitia displaying courage and curiosity, while the border guards represent discrimination. The conflict arises from the unfair treatm
0 views • 15 slides
Introduction to SFTP & PGP Encryption for Secure Data Transfer
Discover how to ensure reliable data transfer, make informed decisions, and gain a strategic advantage through the use of Secure File Transfer Protocol (SFTP) and Pretty Good Privacy (PGP) encryption. The session includes demonstrations on PGP encryption and SFTP access, along with insights on setti
1 views • 22 slides
Ensuring Secure Testing Environments in Oregon Education System
Oregon's Statewide Assessment System (OSAS) emphasizes the critical need for secure testing environments to maintain the validity and accuracy of assessment data. This includes handling secure printed test materials, identifying and preventing improprieties, and reporting any irregularities. From ma
2 views • 20 slides
Understanding Vulnerable Situations of Migrants at International Borders
This training course focuses on migrants in vulnerable situations at international borders, discussing why special consideration is needed for their human rights protection. It covers the concept of vulnerable situations, reasons for focusing on such migrants, and the specific protection they requir
0 views • 15 slides
Training Course on Human Rights at International Borders
This training course focuses on human rights at international borders, emphasizing the importance of a human rights-based approach to border security and management. Participants will learn about key concepts, rights of migrants, due process, gender-responsive approaches, and more. Through reflectiv
1 views • 16 slides
Safe & Secure Gaming Platform Is Online Cricket ID In India
The most secure and safe gaming platform in India is Online Cricket ID. Faster withdrawals within 5 minutes with your online cricket ID. Secure and trusted online cricket and casino ID provider with 24x7 customer support.\nVisit for more information:
1 views • 3 slides
Enhancing Privacy in Crowdsourced Spectrum Allocation
This research focuses on protecting privacy in crowdsourced spectrum allocation, addressing the security challenges faced due to the presence of multiple entities and the sensitive information collected. By proposing potential ideas like Fully Homomorphic Encryption (FHE) and Secure Multi-Party Comp
0 views • 26 slides
Secure Computation Techniques in RAM Models with Efficient Automation
Explore the automation of efficient RAM-model secure computation techniques, including examples such as secure binary search. Discover how traditional solutions using circuit abstractions can be improved for sub-linear time computation through methods like Oblivious RAM. Learn about techniques such
0 views • 37 slides
Advancements in Active Secure Multiparty Computation (MPC)
Delve into the realm of secure multiparty computation under 1-bit leakage, exploring the intersection of DP algorithms, MPC, and the utilization of leakage for enhanced performance. Discover the overhead implications of achieving active security, as well as the evolution of secure computation protoc
0 views • 43 slides
Secure Access to OAuth-Based Services in HTCondor Jobs
Enhance the security of HTCondor job submissions by leveraging OAuth tokens for secure access to file storage services. Learn how the Credd and Credmon architecture facilitates the management and secure transfer of credentials, ensuring sensitive data remains protected during job execution.
0 views • 23 slides
Understanding the Extraterritorial Reach of US Law
The extraterritorial reach of US law extends beyond its borders, impacting both US citizens and non-citizens. Within the US, individuals have constitutional protections, while outside the US, the reach of these protections varies based on the individual's relationship with the US. The application of
0 views • 22 slides
Enhancing Cybersecurity in University Research: Insights from SouthEast SECURE Program
The SouthEast SECURE program at universities like Clemson and University of Alabama focuses on improving cybersecurity for NSF-funded research projects. It provides metrics, communication facilitation, and practical assistance to enhance data security. The program aims to support researchers in util
0 views • 22 slides
Tamper-Evident Pairing (TEP) Protocol for Secure Wireless Pairing Without Passwords
This article discusses the challenges of traditional secure wireless pairing methods that rely on password validation and proposes the Tamper-Evident Pairing (TEP) protocol as a secure in-band solution to protect against Man-in-the-Middle (MITM) attacks. TEP eliminates the need for out-of-band chann
1 views • 40 slides
Evolution of Proofs in Cryptography
Cryptography has evolved from classical proofs to interactive and probabilistically checkable proofs, enabling the development of applications like Non-Malleable and Chosen-Ciphertext Secure Encryption Schemes. Non-Malleability protects against active attacks like malleability and chosen-ciphertext
0 views • 29 slides
Secure Multiparty Computation: Enhancing Privacy in Data Sharing
Secure multiparty computation (SMC) enables parties with private inputs to compute joint functions without revealing individual data, ensuring privacy and correctness. This involves computations on encrypted data using techniques like homomorphic encryption for scenarios like e-voting. SMC serves as
2 views • 27 slides
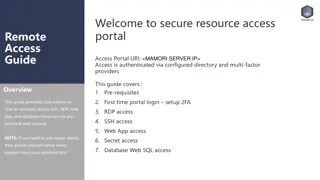
Comprehensive Remote Access Guide for Secure Resource Access Portal
This detailed guide provides step-by-step instructions for setting up remote access to SSH, RDP, web applications, and databases via secure authentication processes. It covers prerequisites, initial login setup with 2FA, and connecting to various resources securely. Follow the guide to ensure a smoo
0 views • 12 slides
Actively Secure Arithmetic Computation and VOLE Study
Exploring actively secure arithmetic computation and VOLE with constant computational overhead at Tel Aviv University. Understanding how functions are represented in secure computation using arithmetic circuits over boolean circuits. Efficiently evaluating arithmetic circuits over large finite field
0 views • 36 slides
Accessing and Utilizing CPCSSN Secure Research Environment (SRE)
Learn how to access the CPCSSN Secure Research Environment (SRE) for secure data analysis. Follow steps such as setting up VPN, accessing SQL databases, and establishing ODBC connections for statistical analysis using tools like SAS, R, SPSS, or Stata. Enhance your research capabilities within a sec
0 views • 12 slides
Enhancing Animal Telemetry Data Systems for Secure Collaboration
Wide spectrum of animal telemetry data collection protocols and platforms require enhanced data stewardship options for secure sharing before public release. The need for a more granular understanding of available data and structured systems integration is crucial. Initial workflow involves providin
0 views • 4 slides
Perceptions of Borders Among Young Mobile Europeans in Europe
This research delves into the perceptions of borders by young mobile Europeans within Europe, exploring how these constructs impact their daily lives. The study investigates the concept of a borderless Europe facilitated by the EU's free movement of persons policy, shedding light on differences and
0 views • 18 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
0 views • 12 slides
Understanding Secure Electronic Transactions (SET)
Secure Electronic Transactions (SET) is an encryption and security specification designed to protect credit card transactions on the Internet. SET provides a secure way to utilize existing credit card payment infrastructure on open networks, such as the Internet, involving participants like clients,
1 views • 6 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Exploring Secure Care Services in Scotland
Delve into the world of secure care services in Scotland, focusing on achievements, challenges, and opportunities in providing youth justice. Learn about trends in secure care, reduction in costs, reasons for referrals, and evidence-based programs like DBT in Glasgow. Gain insights from industry lea
0 views • 77 slides
Understanding Secure PRFs and PRPs in Cryptography
Dive into the world of secure Pseudo-Random Functions (PRFs) and Pseudo-Random Permutations (PRPs) in cryptography. Learn about the definitions, security criteria, and examples of secure PRFs and PRPs such as 3DES and AES. Explore the concepts of secure block ciphers and key principles behind these
0 views • 54 slides
Understanding the Externalisation of European Borders: A Case Study on Turkey
The externalisation of European borders involves pushing activities to subcontractors in return for payment, including returning irregular migrants and blocking migrants in third countries. The process consists of three steps, with key geopolitical events shaping policies and treaties. The case stud
0 views • 16 slides
Proposals for Prioritizing Bids and Managing Collateral Requirements in Auctions
Market Participants face significant collateral requirements in auctions due to multiple bidding zone borders. Proposal to assign priority to bids for credit limit reasons aims to address randomness in bid rejection. Bid XSD is extended to include priority as a component, enhancing bid management ef
0 views • 6 slides
Foundations of Cryptography: Secure Multiparty Computation
Explore the foundations of cryptography with insights into secure multiparty computation, including the Secure 2PC from OT Theorem and the Two-Party Impossibility Theorem. Delve into the impossibility of 2-Party Secure MPC, claims, and exercises on extending to statistical security. Learn about redu
0 views • 39 slides
Euroscepticism in Border Regions: A Deep Dive into Cross-Border Practices and Perceptions
Explore the phenomenon of Euroscepticism in border regions, delving into cross-border practices and perceptions at the EU's internal borders. This study sheds light on how border regions emerge both functionally and institutionally, emphasizing the importance of understanding Euroscepticism in these
0 views • 16 slides
Understanding Secure Messaging and Encryption Techniques
Explore the possibilities of sending secure messages through encryption without the need for advanced degrees in Computer Science or Math. Learn about symmetric and asymmetric key encryption methods, the use of PGP for secure messaging, and the concept of shared-key encryption. Discover the intricac
0 views • 16 slides
Challenges and Solutions for the European Union's Borders
The European Union faces issues with its borders, specifically regarding migration and the reintroduction of internal borders. The Schengen Area plays a crucial role in facilitating movement between member states. EU regulations allow temporary border checks in certain circumstances. The arrival of
0 views • 27 slides