European CRM Act Proposal for Secure Supply of Critical Raw Materials
European CRM Act aims to ensure a secure and sustainable supply of critical raw materials in the EU by monitoring risks, strengthening the value chain, enhancing circularity, and diversifying imports. Strategic partnerships with key countries and developing nations are emphasized, focusing on mutual
0 views • 10 slides
Parsimoni – the European IoT/Edge OS. Secure, efficient, flexible.
Revolutionizing IoT/Edge computing with secure, efficient, and flexible technology, Parsimoni aims to set new standards in the industry. Led by CEO Miklos Tomka, the company leverages European open-source technology to create a secure-by-design OS for IoT/Edge applications. Seeking partners for cons
1 views • 5 slides
Understanding Secure Act 2.0 Key Provisions
In a detailed report by Dee Spivey and Angie Zouhar, key provisions of SECURE Act 2.0 are outlined, including changes in retirement plans like RMD age increase, employee certification of hardship withdrawals, and more. Secure 1.0 and Secure 2.0 differences, effective dates, and necessary actions for
5 views • 12 slides
Introduction to SFTP & PGP Encryption for Secure Data Transfer
Discover how to ensure reliable data transfer, make informed decisions, and gain a strategic advantage through the use of Secure File Transfer Protocol (SFTP) and Pretty Good Privacy (PGP) encryption. The session includes demonstrations on PGP encryption and SFTP access, along with insights on setti
1 views • 22 slides
Ensuring Secure Testing Environments in Oregon Education System
Oregon's Statewide Assessment System (OSAS) emphasizes the critical need for secure testing environments to maintain the validity and accuracy of assessment data. This includes handling secure printed test materials, identifying and preventing improprieties, and reporting any irregularities. From ma
2 views • 20 slides
Understanding Implications of IG Empowerment Act and Paperwork Reduction Act
The IG Empowerment Act provides beneficial provisions for Inspector Generals (IGs) such as exemptions from certain acts, including the Computer Matching Act and Paperwork Reduction Act. The Paperwork Reduction Act requires federal agencies, including IGs, to obtain OMB clearance before conducting su
1 views • 25 slides
Safe & Secure Gaming Platform Is Online Cricket ID In India
The most secure and safe gaming platform in India is Online Cricket ID. Faster withdrawals within 5 minutes with your online cricket ID. Secure and trusted online cricket and casino ID provider with 24x7 customer support.\nVisit for more information:
1 views • 3 slides
Enhancing Privacy in Crowdsourced Spectrum Allocation
This research focuses on protecting privacy in crowdsourced spectrum allocation, addressing the security challenges faced due to the presence of multiple entities and the sensitive information collected. By proposing potential ideas like Fully Homomorphic Encryption (FHE) and Secure Multi-Party Comp
0 views • 26 slides
Understanding the Hatch-Waxman Act: Promoting Affordable Generic Drugs
The Hatch-Waxman Act, also known as The Drug Price Competition and Patent Term Restoration Act, was enacted in 1984 to amend patent laws and the Federal Food, Drug, and Cosmetic Act. It aims to reduce costs associated with generic drug approval, allow early experimental use, compensate branded drug
0 views • 49 slides
Secure Computation Techniques in RAM Models with Efficient Automation
Explore the automation of efficient RAM-model secure computation techniques, including examples such as secure binary search. Discover how traditional solutions using circuit abstractions can be improved for sub-linear time computation through methods like Oblivious RAM. Learn about techniques such
0 views • 37 slides
Advancements in Active Secure Multiparty Computation (MPC)
Delve into the realm of secure multiparty computation under 1-bit leakage, exploring the intersection of DP algorithms, MPC, and the utilization of leakage for enhanced performance. Discover the overhead implications of achieving active security, as well as the evolution of secure computation protoc
0 views • 43 slides
Secure Access to OAuth-Based Services in HTCondor Jobs
Enhance the security of HTCondor job submissions by leveraging OAuth tokens for secure access to file storage services. Learn how the Credd and Credmon architecture facilitates the management and secure transfer of credentials, ensuring sensitive data remains protected during job execution.
0 views • 23 slides
Enhancing Cybersecurity in University Research: Insights from SouthEast SECURE Program
The SouthEast SECURE program at universities like Clemson and University of Alabama focuses on improving cybersecurity for NSF-funded research projects. It provides metrics, communication facilitation, and practical assistance to enhance data security. The program aims to support researchers in util
0 views • 22 slides
Tamper-Evident Pairing (TEP) Protocol for Secure Wireless Pairing Without Passwords
This article discusses the challenges of traditional secure wireless pairing methods that rely on password validation and proposes the Tamper-Evident Pairing (TEP) protocol as a secure in-band solution to protect against Man-in-the-Middle (MITM) attacks. TEP eliminates the need for out-of-band chann
1 views • 40 slides
Evolution of Proofs in Cryptography
Cryptography has evolved from classical proofs to interactive and probabilistically checkable proofs, enabling the development of applications like Non-Malleable and Chosen-Ciphertext Secure Encryption Schemes. Non-Malleability protects against active attacks like malleability and chosen-ciphertext
0 views • 29 slides
Secure Multiparty Computation: Enhancing Privacy in Data Sharing
Secure multiparty computation (SMC) enables parties with private inputs to compute joint functions without revealing individual data, ensuring privacy and correctness. This involves computations on encrypted data using techniques like homomorphic encryption for scenarios like e-voting. SMC serves as
2 views • 27 slides
Comprehensive Remote Access Guide for Secure Resource Access Portal
This detailed guide provides step-by-step instructions for setting up remote access to SSH, RDP, web applications, and databases via secure authentication processes. It covers prerequisites, initial login setup with 2FA, and connecting to various resources securely. Follow the guide to ensure a smoo
0 views • 12 slides
Actively Secure Arithmetic Computation and VOLE Study
Exploring actively secure arithmetic computation and VOLE with constant computational overhead at Tel Aviv University. Understanding how functions are represented in secure computation using arithmetic circuits over boolean circuits. Efficiently evaluating arithmetic circuits over large finite field
0 views • 36 slides
Meeting the Needs of Individuals in the Secure Estate
The Act emphasizes changing the way care and support needs are met, focusing on well-being, individual assessments, and meeting needs. It prioritizes aspects like views, wishes, participation, dignity, culture, and human rights. The Act outlines the general functions, assessment processes, advocacy,
0 views • 11 slides
Accessing and Utilizing CPCSSN Secure Research Environment (SRE)
Learn how to access the CPCSSN Secure Research Environment (SRE) for secure data analysis. Follow steps such as setting up VPN, accessing SQL databases, and establishing ODBC connections for statistical analysis using tools like SAS, R, SPSS, or Stata. Enhance your research capabilities within a sec
0 views • 12 slides
Legal Framework for Weigh-In Motion in South Africa
The legal framework in South Africa regarding weigh-in motion involves various acts and guidelines that impact the weighing of vehicles, such as the Trade Metrology Act, Legal Metrology Act, and National Road Traffic Act. The laws govern the requirements for mass measuring, equipment specifications,
0 views • 22 slides
Proposed Changes to Manitoba's Building Permitting System
Bill 38, "The Building and Electrical Permitting Improvement Act," introduces the Permit Dispute Resolution Act in Manitoba. This act allows for appeals to an adjudicator regarding building code compliance and performance standards under the Buildings Act. The adjudicator can confirm, vary, or set a
1 views • 6 slides
Advancements in Multi-Key Homomorphic Encryption Using TFHE
Revolutionary research has led to the development of Multi-Key Homomorphic Encryption (MKHE) from TFHE, enabling secure and efficient computations on encrypted data. This technology offers advantages such as dynamic operability, stronger security, and minimized interaction, making it an ideal soluti
0 views • 20 slides
Enhancing Animal Telemetry Data Systems for Secure Collaboration
Wide spectrum of animal telemetry data collection protocols and platforms require enhanced data stewardship options for secure sharing before public release. The need for a more granular understanding of available data and structured systems integration is crucial. Initial workflow involves providin
0 views • 4 slides
Understanding Secure Information Transmission in Cryptography
Explore the concepts of secure information confidentiality, integrity, and authenticity in the realm of cryptography, including digital signatures, signcryption, and the challenges faced in ensuring secure communication. Delve into the attempts to encrypt, authenticate, and solve issues like non-rep
0 views • 23 slides
Exploring Secure Computation in the Age of Information
Welcome to Secure Computation Lecture 1 by Arpita Patra. The course covers evaluation policies, projects, and references in the realm of secure computation. The content delves into the significance of information security across various sectors, emphasizing the importance of safeguarding sensitive d
0 views • 36 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
0 views • 12 slides
Understanding Secure Electronic Transactions (SET)
Secure Electronic Transactions (SET) is an encryption and security specification designed to protect credit card transactions on the Internet. SET provides a secure way to utilize existing credit card payment infrastructure on open networks, such as the Internet, involving participants like clients,
1 views • 6 slides
Understanding and Meeting Needs in the Secure Estate
This training delves into Part 11, Chapter 1 of the Act, focusing on adults in the secure estate. Participants will grasp the aims, duties, support pathway, and implications of assessing and meeting care needs. Collaboration among agencies is emphasized, along with the Act's implications. The Social
0 views • 31 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Exploring Secure Care Services in Scotland
Delve into the world of secure care services in Scotland, focusing on achievements, challenges, and opportunities in providing youth justice. Learn about trends in secure care, reduction in costs, reasons for referrals, and evidence-based programs like DBT in Glasgow. Gain insights from industry lea
0 views • 77 slides
Understanding Secure PRFs and PRPs in Cryptography
Dive into the world of secure Pseudo-Random Functions (PRFs) and Pseudo-Random Permutations (PRPs) in cryptography. Learn about the definitions, security criteria, and examples of secure PRFs and PRPs such as 3DES and AES. Explore the concepts of secure block ciphers and key principles behind these
0 views • 54 slides
Understanding the Uniform Power of Attorney Act and Hawaii Act 22
Explore the significance of the Uniform Power of Attorney Act and Hawaii Act 22 regarding Powers of Attorney, termination of agent's authority, general powers granted, and more. Learn about the legal document granting authority to act on behalf of a principal and the termination clauses that may be
0 views • 22 slides
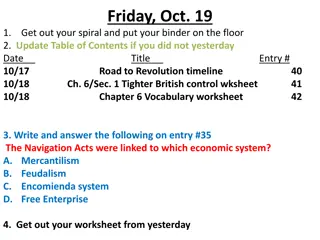
Colonial Challenges Under British Rule
In this academic material, students are instructed to update the Table of Contents and engage with resources related to tighter British control over the colonies. The tasks include exploring historical events like the Proclamation Act of 1763, Quartering Act, Sugar Act, Stamp Act, Declaratory Act, a
0 views • 18 slides
Data Act Reporting and Financial Management Overview
The Digital Accountability and Transparency Act (DATA Act) of 2014 aims to enhance transparency in federal expenditures. It directs the government to standardize and publish various financial reports and data compilations related to obligations, spending, payments, budget actions, procurement, and a
0 views • 16 slides
Foundations of Cryptography: Secure Multiparty Computation
Explore the foundations of cryptography with insights into secure multiparty computation, including the Secure 2PC from OT Theorem and the Two-Party Impossibility Theorem. Delve into the impossibility of 2-Party Secure MPC, claims, and exercises on extending to statistical security. Learn about redu
0 views • 39 slides
Campus Sexual Violence Elimination Act (SAVE) at California Lutheran University
Campus Sexual Violence Elimination Act (SAVE) was passed in March 2013 as part of the Violence Against Women Reauthorization Act, impacting institutions of higher education like California Lutheran University (CLU). The act mandates CLU to educate its community on prevention/awareness of sexual viol
0 views • 22 slides
Overview of Lease and Tenancy Laws in Great Britain
Understand the lease and tenancy laws in Great Britain, including the Landlord and Tenant Act 1954 for commercial properties and the Housing Act 1985 for secure tenancies. Learn about the operation of break clauses, security of tenure for tenants, and how landlords can end leases with security of te
0 views • 10 slides
The Civil Rights Act of 1964 and the Supreme Court
In the 1960s, Congress passed the Civil Rights Act of 1964, a pivotal legislation that prohibited discrimination in public accommodations. This act represented a significant shift in focus towards minority rights. The Supreme Court's past rulings on the Civil Rights Act of 1875 influenced Congress t
0 views • 24 slides
Understanding Secure Messaging and Encryption Techniques
Explore the possibilities of sending secure messages through encryption without the need for advanced degrees in Computer Science or Math. Learn about symmetric and asymmetric key encryption methods, the use of PGP for secure messaging, and the concept of shared-key encryption. Discover the intricac
0 views • 16 slides