Budget Execution Challenges in Somalia's Social Sectors
Addressing malnutrition in Somalia is hindered by low budget execution rates in the health and education sectors. Only a small portion of Official Development Assistance (ODA) is channeled through government systems, impacting service delivery and development financing. Donor-supported budgets for h
0 views • 32 slides
PUMM: Preventing Use-After-Free Using Execution Unit Partitioning
Memory-unsafe languages like C and C++ are prone to Use-After-Free (UAF) vulnerabilities. PUMM introduces execution unit partitioning to efficiently tackle this issue. By segregating and managing execution units, PUMM aims to prevent UAF exploits and enhance software security.
0 views • 31 slides
Comparison Between Static and Dynamic Program Instrumentation
The difference between static and dynamic program instrumentation lies in when the analysis or measurement probes are inserted into a program. Static instrumentation occurs before the program is run and is more closely associated with proactive software evaluation. Dynamic instrumentation, on the ot
4 views • 14 slides
Programming in C
Control statements play a crucial role in C programming by allowing the control flow to change during program execution. They enable decision-making and transfer control from one part of the program to another. Additionally, loops help in executing a set of statements repeatedly until a specified co
1 views • 35 slides
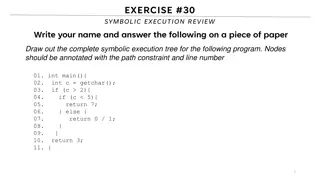
Symbolic Execution Tree for a Program
Generate the complete symbolic execution tree for a given program by annotating nodes with path constraints and line numbers, aiding in understanding program execution flow.
0 views • 26 slides
Amity School of Engineering & Technology - Java Program Compilation and Execution
Explore the steps for compiling and running a Java program at Amity School of Engineering & Technology. Learn about the compilation and execution process, converting source code into byte code, creating directories, renaming files, and launching command prompts. Dive into the world of Java programmi
1 views • 19 slides
Understanding the Neglected Provisions of Order XXI CPC, 1908
Explore the overlooked aspects of Order XXI CPC, 1908, focusing on the definitions, types of decrees, modes of execution, procedures for executing decrees, reasons for neglect, impact, recommendations, and conclusion. Learn about neglected provisions like summary execution, execution against legal r
0 views • 14 slides
Understanding Addressing Modes in Computer System Architecture
Addressing modes determine how the operand in an instruction is specified, impacting the interpretation and execution. Implied, stack, immediate, direct, indirect, register direct, register indirect, relative, indexed, base register, auto-increment, and auto-decrement are various addressing modes ex
0 views • 4 slides
Understanding Software Testing: Test Cases, Selection, and Execution
Software testing plays a crucial role in identifying and resolving issues within software products. Test cases, selection, and execution are fundamental aspects of the testing process. Test cases define conditions for testing software functionality, with a focus on repeatability and data specificity
2 views • 36 slides
Understanding Exceptions in Computer Science
Errors in programming, such as syntax, semantic, runtime, and logical errors, can disrupt the execution of a program. Syntax errors relate to grammatical violations, semantic errors occur when statements lack meaning, and runtime errors happen during program execution due to illegal operations. By i
1 views • 35 slides
Semi-Annual Financial Report S2 - 2022 Summary
This report provides key financial data for the second half of 2022, including budgetary execution, fund quotas compliance, member states' balances due, liquidity risk assessment, and more. It outlines the overall program budget execution, quota compliance of member states, and fund liquidity status
0 views • 14 slides
Understanding the Dynamics of Program and Contract Management Team
The Program Management Contract Management Team, led by Joe Hidalgo, explores the synergy and conflicts between Program Managers and Contract Managers. Highlighting the importance of harmonizing business and program management skills for successful program execution in R&D environments, the content
1 views • 35 slides
Understanding C++ Variable Scope and Lifetime
The program behavior in C++ can be affected by variable scope and lifetime. This includes global variables accessible throughout the program's execution, local variables limited to function execution, variables declared within blocks, and pointers managing memory allocation. Issues such as memory pr
0 views • 5 slides
Ensuring Security in Persistent Key-Value Stores using Shielded Execution
This content discusses the challenges and solutions for securing LSM-based Key-Value stores in untrusted computing environments using Shielded Execution. It addresses the need for confidentiality, integrity, and freshness of data in persistent storage systems. The research explores Trusted Execution
0 views • 32 slides
Modes of Execution of Decree in Civil Law
The lecture discusses the various modes of execution of decree in civil law, such as execution against a person through arrest and detention, and execution against property. It explains the procedures involved in arrest and detention, including the conditions for release, restrictions on arrest, and
0 views • 9 slides
Understanding Program Execution in Linux
Explore the process of program execution in Linux, including details on the ELF executable file format, creating executable files, static vs. dynamic linking, and the impact of linking on executable sizes. Learn about compilation, linking, and the differences between static and dynamic linking in th
2 views • 17 slides
Understanding Java Memory Management
Explore how memory is managed in Java programs, including memory allocation for code, objects, and execution stack. Learn about memory areas like the execution stack and heap, and understand the concept of activation records in method execution.
0 views • 27 slides
Exploring Instruction Level Parallel Architectures in Embedded Computer Architecture
Delve into the intricacies of Instruction Level Parallel Architectures, including topics such as Out-Of-Order execution, Hardware speculation, Branch prediction, and more. Understand the concept of Speculation in Hardware-based execution and the role of Reorder Buffer in managing instruction results
0 views • 51 slides
Evolution of Execution Methods in Modern Society
Explore the historical and modern methods of execution, from hanging to lethal injection, and the transition towards more civilized approaches. Learn about the contributions of prominent figures like Elbridge Gerry in advocating for humane execution methods. Delve into the commercial rivalry between
0 views • 13 slides
Secure and Efficient Multi-Variant Execution in Distributed Settings
This paper discusses dMVX, a system for secure multi-variant execution in distributed settings to mitigate memory errors and protect against attacks. Using leader and follower variants, diversified program variants run in lockstep to ensure security. The system monitors and replicates I/O results, e
0 views • 35 slides
Challenges of Unbounded Program Analysis
Verifying unbounded programs poses challenges due to the undecidability of certain computational resources like memory usage, execution time, and data structures. The presence of infinite execution paths, unbounded loops, recursion, and dynamic memory allocation makes it difficult to determine progr
0 views • 32 slides
Hardware-Assisted Task Scheduler for OS Intensive Applications
A hardware-assisted task scheduler called SchedTask is proposed to address the issue of instruction cache pollution in OS intensive applications. By utilizing SuperFunction characterization and a specialized scheduler, the system aims to optimize task execution on different cores for improved perfor
0 views • 28 slides
Understanding MIPS Instruction Sets and Binary Execution
This lecture covers the mapping of MIPS instructions to binary for execution, the use of pseudo-instructions to improve code readability, and the handling of large constants. It discusses levels of representation and interpretation, the concept of stored-program computers, addressing in memory, bina
0 views • 50 slides
Introduction to Programming Recap and Memory in IDLE
Explore the world of programming through a recap session covering essential topics like variable scope, recursive functions, and the difference between return and print statements. Dive into the details of function execution and memory management in IDLE, learning how parameters are passed and store
0 views • 31 slides
Understanding Code Execution Graphs and Superblocks in Software Analysis
Explore the concepts of Static Execution Graphs, Dynamic Execution Graphs, Superblocks, hot-path detection, and memory arithmetic in software analysis. Learn about the grouping of blocks, violation tracking, control dependencies, and code behaviors across time through these graphical representations
0 views • 9 slides
Understanding Programs, Processes, and Threads in Computer Systems
In this comprehensive guide, we delve into the fundamental concepts of programs, processes, and threads in computer systems. Exploring topics such as dynamic code execution, program formats, and the execution of .exe files, we uncover the intricate workings of how software is executed and managed by
0 views • 110 slides
Understanding Processes in Operating Systems - ECE344 Lecture 3 Summary
This lecture delves into the essential concepts of processes, threads, and synchronization in operating systems. Key topics covered include units of execution, representation of units of execution in the OS, process execution states, and state transitions. Users, programs, and the role of processes
0 views • 45 slides
InvisiSpec: Making Speculative Execution Invisible
InvisiSpec presents a novel defense mechanism to address speculative execution attacks in the cache hierarchy. By making speculative execution invisible to potential attackers, this holistic approach aims to mitigate the risks associated with exploiting side effects on incorrect paths, such as Spect
0 views • 18 slides
Multicycle Datapath and Execution Steps Overview
This content provides a detailed explanation of a multicycle datapath and the execution steps involved in processing instructions. It covers key elements such as instruction fetching, decoding, memory referencing, ALU operations, branch and jump instructions, as well as memory access for read and wr
0 views • 11 slides
Understanding Symbolic Execution and Directed Automated Random Testing
Symbolic Execution is a method used for analyzing programs to determine inputs causing each part to execute, vital in program testing. However, limitations arise in cases without code availability, hindering definitive path conditions. Directed Automated Random Testing (DART) overcomes this through
0 views • 20 slides
Understanding a.mini.TRACS Program Execution
Explore the program execution of a.mini.TRACS through step-by-step analysis, including variable values and output at each stage. Witness how the program progresses and learn the sequence of statements executed. Follow the journey of the counter variable and discover what is printed at each iteration
0 views • 16 slides
Western Resource Adequacy Program Overview
Western Resource Adequacy Program (WRAP) is a vital initiative in the Western Power Pool, providing valuable grid integration and coordination services to its customer-members across the entire Western Interconnection. As the Program Administrator, Western Power Pool undertakes all necessary actions
0 views • 11 slides
Secure Cloud Applications with Intel SGX - OSDI 2014 Presentation Summary
This presentation discusses the challenges of trusting cloud environments and proposes solutions utilizing Intel SGX technology. It explores the need for secure execution of applications on untrusted cloud platforms, presents existing solutions, and introduces the concept of Haven for private execut
0 views • 33 slides
Rethinking Processes with Threads in Operating Systems
Processes in operating systems traditionally include various resources and execution states, leading to inefficiencies in communication and parallel program execution. By separating the concept of a process from its execution state, modern OSes like Mac, Windows, and Unix introduce threads as lightw
0 views • 29 slides
Python Programming Essentials: Basics, Operators, Expressions, and Control Flow
This segment delves into the fundamentals of Python programming with a focus on essential concepts such as comments, numbers, strings, variables, arithmetic operators, logical operators, order of execution, expressions, and control flow statements like conditional execution and looping. Learn about
0 views • 12 slides
N-Variant Execution for Improved Security Measures
N-Variant Execution (NVX) is a technique used to enhance security measures by running diversified program variants in parallel and comparing their outputs for transparency. NVX systems can protect against attacks relying on knowledge of virtual address spaces but have limitations against attacks bas
0 views • 48 slides
Understanding Operating System Concepts: Multiprogramming, Multiprocessing, Multitasking, and Multithreading
In the realm of operating systems, terms like multiprogramming, multiprocessing, multitasking, and multithreading can often be confusing due to their similar appearance but distinct meanings. These concepts play a crucial role in efficiently managing resources in a computing system, particularly in
0 views • 6 slides
VIBRANCE: Securing Java Applications with Advanced Techniques
VIBRANCE project aims to eliminate vulnerabilities in Java applications by analyzing bytecode and implementing nuanced confinement and diversification strategies. By addressing common security pitfalls such as SQL injection, command execution, and loop manipulation, VIBRANCE enhances application sec
0 views • 28 slides
Memory Allocation and Program Execution Overview
Understanding memory allocation is crucial for efficient program execution. This content delves into the importance of memory allocation, considerations for storing data during program execution, and the requirements for allocating memory efficiently. It also explores solutions for managing memory s
0 views • 35 slides
Understanding CPU Virtualization and Execution Control in Operating Systems
Explore the concepts of CPU virtualization, direct execution, and control mechanisms in operating systems illustrated through a series of descriptive images. Learn about efficient CPU virtualization techniques, managing restricted operations, system calls, and a limited direct execution protocol for
0 views • 18 slides