Automated Mobile App QoE Diagnosis with Cross-layer Analysis
This work presents the QoE Doctor, a solution for accurate and repeatable QoE measurements and analysis in mobile apps. By introducing UI automation, it enables the replay of user behavior to measure UI layer QoE metrics without modifying app source code. The QoE Doctor also supports multi-layer dia
3 views • 28 slides
Update on SWAG Protocols and New NICE TA Progress Report
Kate Gregory leads the SWAG Protocols update for March 2024, with advancements in new protocols and NICE TA updates. A comparison of activities from Oct 2023 to Mar 2024 shows progress in issuing, reviewing, and drafting protocols. The latest NICE TA additions include treatments for advanced cancers
5 views • 13 slides
Layer 2 Token Marketing Services
Layer-2 token marketing promotes tokens built on scalable layer-2 solutions, highlighting benefits like faster transactions and lower fees. Get connected with our experts today and launch a lucrative \ntoken platform.
0 views • 3 slides
Understanding Ozone Depletion: Causes and Impact
The ozone layer, found in the stratosphere at 15 to 40 km altitude, plays a crucial role in absorbing harmful ultraviolet radiation. However, due to the use of Chlorofluorocarbons (CFCs), the ozone layer has been depleted, leading to the formation of the ozone hole. This depletion is caused by chemi
0 views • 27 slides
Understanding Consistency Protocols in Distributed Systems
Today's lecture covers consistency protocols in distributed systems, focusing on primary-based protocols and replicated-write protocols. These protocols play a crucial role in ensuring consistency across multiple replicas. One example discussed is the Remote-Write Protocol, which enforces strict con
0 views • 35 slides
NASA Platform Layer Updates for the CAELUM (7.0) Release
The National Aeronautics and Space Administration (NASA) discusses platform layer updates for the CAELUM (7.0) release of the Core Flight System in the 2021 Flight Software Workshop. The platform layer consists of the Operating System Abstraction Layer (OSAL) and Platform Support Package (PSP), whic
1 views • 20 slides
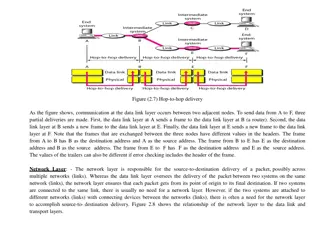
Understanding Communication Layers in Computer Networks
Communication in computer networks is facilitated through different layers such as the data link, network, and transport layers. Each layer has specific responsibilities in ensuring data delivery from one point to another. The data link layer handles communication between adjacent nodes, the network
3 views • 7 slides
Understanding Mobile Computing and TCP/IP Protocol Suite
Mobile computing is crucial for continuous internet connectivity regardless of physical location. The TCP/IP protocol suite, consisting of Transmission Control Protocol (TCP) and Internet Protocol (IP), forms the backbone of internet infrastructure. IP addressing and mobility challenges are addresse
1 views • 51 slides
Network Slicing with OAI 5G CN Workshop Overview
Overview of Network Slicing with OAI 5G CN workshop focusing on the crucial role of network slicing in realizing the service-oriented 5G vision. This workshop covers topics like multiple logical networks creation on shared infrastructure, different types of network slices, preparation and instantiat
1 views • 6 slides
Understanding OSI Reference Model Layers
The OSI (Open Systems Interconnection) model consists of 7 layers, each with specific functions in network communication. From the Application layer handling user services to the Physical layer dealing with data transmission, learn about the responsibilities and interactions of these layers in netwo
0 views • 26 slides
Understanding Computer Communication Networks at Anjuman College
This course focuses on computer communication networks at Anjuman College of Engineering and Technology in Tirupati, covering topics such as basic concepts, network layers, IP addressing, hardware aspects, LAN standards, security, and administration. Students will learn about theoretical and practic
0 views • 72 slides
Understanding the OSI Model and Layered Tasks in Networking
The content highlights the OSI model and layered tasks in networking, explaining the functions of each layer in the OSI model such as Physical Layer, Data Link Layer, Network Layer, Transport Layer, Session Layer, Presentation Layer, and Application Layer. It also discusses the interaction between l
1 views • 41 slides
Understanding Reliable Transport and User Datagram Protocol in Computer Networking
This content covers the concepts of reliable transport in computer networking, including the reliable transport layer protocols like TCP, UDP, and the basics of Domain Name Service (DNS). It explains the layers of the Internet, the functions of each layer, and the differences between TCP and UDP pro
0 views • 28 slides
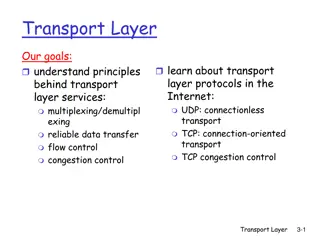
Understanding Internet Transport Layer Services and Protocols
In the realm of networking, exploring the principles of transport layer services is crucial. This involves concepts like multiplexing/demultiplexing, reliable data transfer, flow control, and congestion control, which are facilitated by protocols such as UDP and TCP. The transport layer acts as a br
0 views • 56 slides
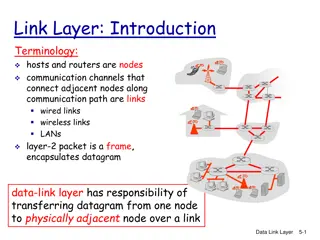
Understanding Data Link Layer in Computer Networking
The Data Link Layer (DLL) is the second layer of the OSI model, responsible for error detection and correction, framing, addressing, synchronization, flow control, and multi-access protocols. It deals with logical link control and media access control, addressing destination hardware, avoiding data
0 views • 49 slides
Fundamentals of Data Link Layer and Ethernet in Computer Networks
Delve into the essential concepts of the Data Link Layer and Ethernet in computer networking, covering services like framing, error detection, correction, reliable delivery, and more. Explore how frames transfer data between nodes, the importance of link protocols, and the role of MAC protocols in l
0 views • 46 slides
Comprehensive Overview of Computer Networks and Protocols for GCSE Level
Explore the diverse aspects of computer networks and protocols through in-depth discussions on LAN, WAN, client-server relationships, hardware requirements, network topologies, protocols like TCP/IP and HTTP, and the significance of network layers. Understand the roles, benefits, and risks associate
0 views • 23 slides
Meridian: An SDN Platform for Cloud Network Services
Meridian is an SDN platform developed by Mohammad Banikazemi, David Olshefski, Anees Shaikh, John Tracey, and GuohuiWang at IBM T. J. Watson Research Center. The platform focuses on providing cloud network services efficiently. It encompasses an architecture that enables faster and more convenient n
0 views • 21 slides
Understanding ZFS: Structure and Operations
Explore the comprehensive structure and operations of ZFS, covering aspects like MOS layer, object-set layer, Dnode, Block Pointer, and TRIM operations. Learn about the meta-object set (MOS), dataset and snapshot layer (DSL), and storage pool allocator (SPA) modules within ZFS. Understand how ZVOLs,
0 views • 10 slides
Understanding the Planetary Boundary Layer in Atmospheric Science
The Planetary Boundary Layer (PBL) plays a crucial role in atmospheric dynamics, divided into surface, mixed, stable, and residual layers. During the day, the mixed layer experiences convective motions due to surface heating, while the stable layer dominates during the night. Understanding these lay
0 views • 18 slides
Understanding Transport Layer Security (TLS) and Secure Sockets Layer (SSL)
This content delves into the concepts of Transport Layer Security (TLS) and Secure Sockets Layer (SSL), exploring their origins, application in web security, and protocol stack integration. It covers the TLS/SSL handshake process, key derivation, data transfer mechanisms, and the significance of the
0 views • 26 slides
Understanding Routing Protocols in Network Layer
Routing protocols in the network layer dictate how data packets are routed through a network. This lecture delves into key concepts such as reachability, routing protocol components, and the workings of Distance Vector (DV) algorithms. It explains how updates propagate in networks efficiently with D
0 views • 31 slides
Understanding Modular Layer 2 in OpenStack Neutron
Modular Layer 2 (ML2) is a new core plugin in OpenStack Neutron that enables interface with various network mechanisms and types for enhanced flexibility and efficiency. It replaces deprecated plugins like Open vSwitch and Linuxbridge, offering a more modular and feature-rich approach for managing l
0 views • 31 slides
Understanding Network Layer Concepts in Router Design Lecture
This content delves into the fundamental concepts of network layer functions in router design, including data forwarding, control plane operations, and route processing. It explains the analogy of the postal system to address and locate network endpoints, and emphasizes the importance of route looku
0 views • 27 slides
Understanding Ethernet and Multiple Access Protocols in Computer Networks
Exploring the fundamentals of Ethernet and multiple access protocols in computer networks, this content discusses the two primary categories of multiple access protocols - contention access and controlled access. It delves into topics such as CSMA/CD, LANs, performance of multiple access schemes, ad
0 views • 7 slides
Understanding Application-layer Protocols in Computer Communication and Networks
Explore Chapter 2 of the course on Computer Communication and Networks, focusing on the application-layer protocols in the client-server paradigm, specific protocols like HTTP and SMTP, client-server architecture, peer-to-peer architecture, and addressing needs in the network application layer.
0 views • 60 slides
Understanding Application Layer Protocols in Communication Networks
Explore the fundamentals of application layer protocols in communication networks, including HTTP, DNS, FTP, and email. Learn about the client-server model, peer-to-peer communication, and the basic workings of TCP sockets. Discover the importance of message syntax, semantics, and processing rules i
0 views • 51 slides
Understanding Transport Layer Services and Challenges
The transport layer provides essential services for reliable communication between end-hosts, including error detection, recovery, and timing preservation. Different transport service models, connection paradigms, and challenges like packet delay, reordering, and loss are discussed in comparison to
0 views • 22 slides
Enhancing Bitcoin Network Through Trust Extraction and Blockchain Scalability
Explore methods to extract trust from the blockchain and enhance scalability through Layer 1 and Layer 2 changes, including parameters adjustment, consensus algorithm modifications, sharding, payment networks, and side chains. Learn about payment channels, Bitcoin throughput, and strategies to incre
0 views • 23 slides
Understanding ARP, ICMP, and DHCP in TCP/IP Protocol Stack
ARP (Address Resolution Protocol) plays a crucial role in bridging the Layer 2/Layer 3 addressing boundary in the TCP/IP protocol stack, allowing IP to be agnostic about layer 2 addressing while still using layer 2 for packet delivery. Machines ARP for MAC addresses within their local network, where
0 views • 39 slides
Understanding the Layers of Distributed Systems
This content delves into the intricacies of distributed systems, exploring concepts such as establishing communication with applications, managing channels for actual communication, bandwidth versus latency considerations, and the functions of physical, link, and network layers. From the physical la
0 views • 27 slides
Understanding the Link Layer in Computer Communication and Networks
The link layer, an essential component in computer networks, is implemented at every host through adapters like NICs or Ethernet/802.11 cards. It handles tasks such as frame encapsulation, error checking, and flow control to ensure reliable data transmission between nodes. Link layer services includ
0 views • 64 slides
Understanding Link Layer in Computer Networking
The link layer, also known as the data link layer, plays a crucial role in transferring data between adjacent nodes over communication links. This layer is responsible for framing, access control, reliable delivery, error detection and correction, flow control, and more. It is implemented in network
0 views • 34 slides
Enhancing Network Stability with Network Monitoring Systems
Network monitoring is crucial for efficient management and proactive issue detection in a network environment. Factors influencing an effective network system include choosing the best OEM, SLA agreements, and selecting a reliable System Integrator. Reactive monitoring can lead to financial losses a
0 views • 12 slides
Understanding Network Security Part 2: Link Layer and ARP
Exploring the vulnerabilities in simple network topologies with hubs and the need for examining the link layer to prevent eavesdropping. Dive into MAC addresses, ARP (Address Resolution Protocol), and how machines translate IP addresses to physical Ethernet addresses. Learn about ARP tables, the tra
0 views • 61 slides
Understanding Network Protocols: TCP, UDP, DHCP, DNS
Explore the fundamentals of key network protocols including TCP, UDP, DHCP, and DNS. Learn about IPv4 and IPv6 addresses, IP address classes, and the roles of these protocols in the TCP/IP suite. Understand the differences between TCP and UDP in terms of connection setup and reliability. Discover th
0 views • 13 slides
Understanding the Network Layer in Computer Networking
The network layer is vital in computer networking, responsible for host-to-host delivery by carrying packets between computers. It enables internetworking, routing packets to their destinations, and ensuring unique addressing for global communication. This layer encapsulates data packets, fragments
0 views • 14 slides
Understanding Layer 3 Switches: Functionality and Configuration
Layer 3 switches combine the features of Ethernet switches and routers, allowing them to process both MAC and IP headers. By configuring VLANs, trunking, and management interfaces, these switches can handle data forwarding across different subnets efficiently. This guide explains the basic principle
0 views • 19 slides
Improved Merlin-Arthur Protocols for Fine-Grained Complexity Problems
The text discusses Merlin-Arthur proof systems and protocols for central problems in fine-grained complexity, particularly focusing on the time complexity, completeness, and soundness of these protocols. It also touches on recent interest in these protocols and presents new results in areas such as
0 views • 16 slides
Quantum Distributed Proofs for Replicated Data
This research explores Quantum Distributed Computing protocols for tasks like leader election, Byzantine agreement, and more. It introduces Quantum dMA protocols for verifying equality of replicated data on a network without shared randomness. The study discusses the need for efficient protocols wit
0 views • 28 slides