The Secure Path_ Implementing Digital Product Keys for Online Businesses (1)
In today's digital landscape, where online businesses reign supreme, safeguarding products and services against piracy and unauthorized access is paramount. Enter the era of digital product keys \u2013 a secure path towards ensuring the integrity of online transactions and protecting intellectual pr
1 views • 3 slides
Coverage Semantics for Dependent Pattern Matching
Delve into the world of dependent pattern matching with a focus on coverage semantics. Dive deep into the concepts of denotational semantics, topologies, and coverages. Explore the interplay between patterns, values, and types in a novel way, shedding light on the essence of pattern matching.
4 views • 26 slides
windows 10 pro OEM kEYS
Windows 10 Pro OEM keys are digital licenses that activate Windows 10 Pro on a device. They're sold at lower prices than retail keys, often to system builders. These keys tie to the original hardware and offer full OS functionality, updates, and support. They're cost-effective for PC builders and in
3 views • 2 slides
Cracking the Code Understanding Windows 10 Pro OEM Keys
Understanding Windows 10 Pro OEM keys is crucial for activating licenses efficiently. OEM keys are linked to specific hardware, like pre-built systems, ensuring affordability but limited to that hardware. They're not transferable between devices. Retail keys, on the other hand, offer flexibility but
1 views • 8 slides
WindowKeys Unlocking the Power of Windows with Genuine License Keys
Windows with Genuine License Keys provide a secure and reliable operating system experience. These keys ensure that your version of Windows is legitimate and allows you to access all features and updates. With a genuine license key, you can activate your copy of Windows, receive support from Microso
4 views • 3 slides
Best Automotive Locksmith In Los Angeles
Need a skilled automotive locksmith in Los Angeles. A skilled locksmith with the ability to create car keys and fix ignition issues is known as an automotive locksmith. This locksmith can also fix your automobile's lock mechanisms and unlock your car. Car locksmith are capable of cutting car keys. W
10 views • 7 slides
Understanding VSAM Logical Record Access Methods
VSAM utilizes three primary methods to find logical records - Relative Byte Address, Relative Record Number, and Key field. Relative Byte Address assigns a unique address to each record based on sequential ordering. Relative Record Number is used in RRDS datasets to access records by a numbered sequ
3 views • 35 slides
Key Management and Distribution Techniques in Cryptography
In the realm of cryptography, effective key management and distribution are crucial for secure data exchange. This involves methods such as symmetric key distribution using symmetric or asymmetric encryption, as well as the distribution of public keys. The process typically includes establishing uni
1 views • 27 slides
Understanding Keys in Relational Databases
Keys play a crucial role in relational databases by uniquely identifying records and establishing relationships between tables. Primary keys are essential for data integrity, ensuring each entity is identified uniquely. Learn about primary keys, types of keys, and examples of creating tables with pr
0 views • 57 slides
Introduction to Public Key Cryptography
Public key cryptography, exemplified by algorithms like Diffie-Hellman and RSA, revolutionizes secure communication by allowing users to encrypt messages with public keys known to all and decrypt them with private keys known only to the intended recipient. This advanced encryption method ensures sec
1 views • 44 slides
Colorado Alliance of Research Libraries: MARC Record Matching System Overview
Designed and hosted by the Colorado Alliance of Research Libraries, the Gold Rush Analytics Technical Overview showcases a cost-effective system utilizing open-source software with tailored solutions. The Matching MARC section details the methodology for matching records, emphasizing the pre-built m
1 views • 10 slides
English Class Practice for SSC Examinees: Sentence Matching Activities
Engage in sentence matching activities to enhance your English skills for the SSC exams. Practice writing complete sentences by matching different parts from columns A, B, and C. Improve your language proficiency and prepare effectively for the English paper with this educational resource.
0 views • 21 slides
English Class Practice for SSC Examinee - Column Matching
Engage in column matching exercises to enhance your English skills. Develop the ability to construct complete sentences by matching sentence parts in an educational setting. Practice with different topics and improve sentence formation skills effectively.
6 views • 21 slides
Understanding the Key Concepts of Relational Databases
Introduction to the fundamental concepts of relational databases including the relational model proposed by Edgar F. Codd, relation schemes, relation instances, keys for a relation, and more. Discover the significance of keys, candidate keys, superkeys, and primary keys in database design.
0 views • 27 slides
Understanding Database Management Systems and Keys in SQL
This content discusses the importance of organizing data into multiple tables within a database management system, the concept of keys and foreign keys, and the potential issues of data redundancy. It also covers examples of structured data related to products, orders, and manufacturers.
0 views • 55 slides
English Class Practice with Column Matching for SSC Examinees
Join our English class for practice exercises on column matching, aimed at helping SSC examinees improve their sentence construction skills. Learn how to match parts of sentences and create complete sentences effectively. Our senior teacher, Manik Chandra Majumder, is dedicated to helping you succee
0 views • 21 slides
Exploring Dichotomous Keys in Biology
Delve into the world of dichotomous keys with lessons on their types and practical application. Learn how to use these keys to identify various organisms and classify them based on specific characteristics. From distinguishing between different cat species to identifying aquatic organisms, this expl
0 views • 17 slides
Exploring Computer Keyboards And Typewriters
Dive into the world of computer keyboards and typewriters to understand their similarities and differences. Learn about the layout of alphabetic keys like QWERTY, utilizing the shift key for capitalization and special characters, the function of the enter key, differences between computer keyboards
0 views • 18 slides
Entity Resolution Problem in Customer Data Matching
The challenge of entity resolution, especially in the context of matching customer data between companies, is addressed in this content. The scenario involves accurately identifying which records correspond to the same individuals despite potential variations or errors in the data. Strategies such a
1 views • 56 slides
Engaging English Lesson for Second Graders - Alphabet Learning and Word Matching
Engage young learners in an interactive English lesson focusing on alphabet recognition and word-object matching. The Head Teacher leads students at Jagotpur Government Primary School through fun activities like singing the alphabet song, identifying objects by initial sounds, and matching words wit
0 views • 16 slides
Enhancing Long-Term Fostering Matching Process for Social Care Teams
This presentation outlines the long-term fostering matching process in March 2023 by South Gloucestershire Council. It emphasizes the importance of understanding and following the process for Service Managers, Team Managers, and new starters in Social Care. The responsibilities of staff in ensuring
3 views • 19 slides
Classroom Connectivity Initiative in Texas: E-rate and State Matching Fund Process
The Classroom Connectivity Initiative in Texas outlines how E-rate and State Matching funds work to make telecommunications and information services more affordable for schools and libraries. With federal E-rate discounts ranging from 20% to 90%, and state matching funds providing dollar-for-dollar
0 views • 9 slides
Understanding Matching Theory in Two-Sided Markets
Matching theory explores the dynamics of two-sided markets where participants on both sides seek suitable matches without using money. Examples include marriage markets, medical residencies, school choice programs, and more. We delve into the marriage model, stable matching criteria, and the deferre
0 views • 28 slides
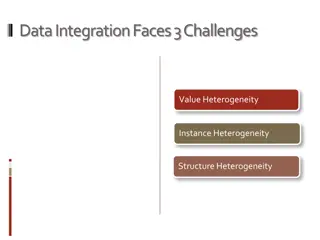
Challenges in Data Integration: Heterogeneity and Solutions
Data integration faces challenges such as value heterogeneity, instance heterogeneity, and structure heterogeneity. Existing solutions assume independence of data sources and utilize methods like data fusion, truth discovery, string matching, object matching, schema matching, and model management. T
0 views • 5 slides
Matching Gift Roadmap: Boost Your Nonprofit's Fundraising Efforts
Elevate your nonprofit's fundraising potential with the Matching Gift Roadmap provided by Double the Donation. This presentation guides organizations on identifying key leaders, assessing current revenue, optimizing donor information, exploring marketing opportunities, and setting timelines for succ
0 views • 10 slides
Enhancing Matching Gift Strategies for Nonprofits
Explore a comprehensive roadmap for maximizing matching gift opportunities provided by Double the Donation. This presentation covers important steps such as determining donor information, evaluating revenue, and setting timelines for success. Learn how to identify responsible departments and individ
0 views • 10 slides
Tuning and Matching of 1 and 2 Loops Antenna
The aim of the project is to match the impedance of the circuit to 50 ohms at the resonance frequency of 14.8 MHz. The process involves calculating the impedance, working at low frequencies to determine key parameters, calculating capacitors, determining Q, and finally calculating tuning and matchin
0 views • 25 slides
Gender Wage Gap Among Those Born in 1958: A Matching Estimator Approach
Examining the gender wage gap among individuals born in 1958 using a matching estimator approach reveals significant patterns over the life course. The study explores drawbacks in parametric estimation, the impact of conditioning on various variables, and contrasts with existing literature findings,
0 views • 18 slides
SPC Algorithm: Shift-based Pattern Matching for Compressed Web Traffic
Victor Zigdon presents the SPC Algorithm, a simpler and more efficient approach to pattern matching in compressed web traffic. By applying an accelerating idea on pattern matching algorithms, the SPC Algorithm skips bytes and achieves throughput improvements. The background includes information on G
0 views • 21 slides
Graph Pattern Matching Challenges and Solutions
Graph pattern matching in social networks presents challenges such as costly queries, excessive results, and query focus issues. The complexity of top-k and diversified pattern matching problems requires heuristic algorithms for efficient solutions. Finding best candidates for project roles involves
0 views • 19 slides
Understanding Matching Keys in Database Systems
Matching keys play a crucial role in identifying the same real-world entities in database systems. They specify which attributes to compare and how to compare them, helping minimize redundancy and improve data accuracy. This summary discusses relative candidate keys, minimal matching keys, and relia
0 views • 13 slides
Key and Splines Design at Minia University
Key and splines design play a crucial role in connecting mechanical elements like shafts and hubs to transmit power efficiently. This article covers the types of keys, principles of work, and various classifications of keys such as sunk keys, saddle keys, tangent keys, round keys, and splines. It de
0 views • 20 slides
Stable Matching Problem and Gale-Shapley Algorithm Overview
The content provides information on the stable matching problem and the Gale-Shapley algorithm. It covers the definition of stable matching, the workings of the Gale-Shapley algorithm, tips for algorithm implementation, and common questions related to the topic. The content also includes a summary o
0 views • 16 slides
Understanding Cryptography and Symmetric Keys in Digital Communication
Cryptography, a vital part of digital communication, involves safeguarding messages from adversaries like eavesdroppers and impostors. Initially reliant on symmetric keys for encryption and decryption, the need to securely share keys posed a challenge. Technologies like DES and AES have advanced cry
0 views • 55 slides
The Case of the Missing Keys
In this amusing tale, Kylee Goodwin narrates the comical ordeal of her mum losing her keys yet again. The family embarks on a frantic search through various rooms, only for the keys to be found hanging safely on their hook by Dad in the end. A lighthearted story of everyday mishaps and the relief of
0 views • 13 slides
Advanced SQL Concepts and Queries Overview
Today's lecture highlights advanced SQL topics such as multi-table queries, set operators, joins, primary keys, foreign keys, and more. The session covers practical activities and fundamental concepts in database management. Explore the nuances of SQL semantics and understand the importance of keys
0 views • 55 slides
Understanding Stable Matching and Orderly Markets in Various Allocation Systems
Exploring the concept of stable matching and orderly markets in different allocation systems such as medical residencies, law clerk placements, and college admissions. From theory to practice, the history of the National Residency Matching Program (NRMP) to centralized clearinghouses, the importance
0 views • 36 slides
Understanding Database Constraints, Keys, and Triggers
Explore the concepts of constraints, foreign keys, local and global constraints, and triggers in the context of database management systems. Delve into topics such as types of constraints, keys, and expressing foreign keys with examples. Enhance your understanding of database integrity and data rela
0 views • 40 slides
Weak Keys Detection in Network Devices
TLS and SSH rely on RSA and DSA for security, but weaknesses in random number generation can lead to widespread weak keys among hosts on the Internet. This paper uncovers the prevalence of repeated keys and easily inferred private keys, emphasizing the importance of entropy pools in key generation.
0 views • 28 slides
Understanding Computer Input Devices and Keystrokes
The system box of a computer contains essential components like the CPU, motherboard, and memory chips. Character keys, action keys, and application-dependent keys on a keyboard serve different functions, from typing letters to performing actions. Key combinations and shortcuts provide efficient way
0 views • 10 slides