INTEGRITY: A FACTOR FOR EQUALITY THROUGH INCLUSIVE POLICIES
In a global context of growing income inequality, the importance of integrity in fostering equality through inclusive policies is emphasized. The OECD works with Mexico to address issues of inequality, corruption, and declining trust in government, highlighting the need for integrity and competence
0 views • 17 slides
Protection Analysis using the PAF
In this session, participants will learn how to utilize the Protection Analysis Framework (PAF) and its tools to conduct effective protection analysis. The session covers an overview of PAF, understanding its pillars, and analyzing data to comprehend essential protection concepts. Key points include
5 views • 48 slides
Ensuring Integrity in the Voluntary Carbon Market for a Just Transition
The voluntary carbon market plays a crucial role in achieving a just transition to 1.5°C, emphasizing high integrity standards. The ICVCM has set Core Carbon Principles to uphold quality standards for carbon credits, ensuring market integrity and participant eligibility. Key components include asse
1 views • 18 slides
The Digital Personal Data Protection Act 2023
The Digital Personal Data Protection Act of 2023 aims to regulate the processing of digital personal data while balancing individuals' right to data protection and lawful data processing. It covers various aspects such as obligations of data fiduciaries, rights of data principals, and the establishm
3 views • 28 slides
Research Integrity 2.0 Australian Version: A Comprehensive Training Programme
Introducing the Research Integrity programme tailored for the Australian research community, focusing on principles, practices, and responsibilities outlined in the Australian Code for the Responsible Conduct of Research (2018). This interactive courseware aims to enhance integrity, boost confidence
5 views • 16 slides
Governance and Managerial Leadership of Formal Social Protection in Africa: Insights from Cameroon's National Social Insurance Fund (CNPS)
This presentation delves into the governance and managerial leadership of formal social protection in Africa, focusing on Cameroon's CNPS system. It discusses the institutional evolution of social protection, the challenges faced by bureaucratic and political stakeholders, and the roles of various s
0 views • 8 slides
Top Malware Protection Services in Dallas - Keep Your Business Safe
If you are searching for the best Malware Protection in Dallas, then you are in the right place. For all your Cyber Security needs look no further than Black Swan Cyber Security. As cyber threats continue to evolve, it is important to prevent the introduction of malicious code that can compromise th
2 views • 3 slides
Understanding the Role of Florida Department of Environmental Protection
The Florida Department of Environmental Protection (DEP) is dedicated to managing and safeguarding the state's air, water, and land resources. With a vision to be a global leader in environmental protection and a mission to enforce environmental laws and preserve natural resources, DEP focuses on ed
4 views • 20 slides
Eye Protection Training for Workplace Safety
Understand the importance of proper eye protection at work, including identifying at-risk job functions, selecting the right PPE, and knowing responsibilities for employees and employers. Training covers when PPE is necessary, how to use, maintain, and dispose of it properly, and the need for retrai
2 views • 28 slides
Understanding Cryptographic Data Integrity Algorithms
Cryptographic data integrity algorithms ensure data integrity, verifying data received matches what was sent by authorized entities. Cryptographic hash functions play a crucial role in ensuring data integrity through hash values. Applications include message authentication, digital signatures, and v
3 views • 41 slides
Understanding Academic Integrity at the University of Manitoba
Explore the essential aspects of academic integrity, including its definition, importance for students, types of dishonesty, and expectations in a class setting. Discover why students should care about academic integrity, the various types of academic misconduct such as plagiarism and cheating, and
0 views • 28 slides
Understanding Integrity at Ok Tedi: Values and Practices
Ok Tedi's commitment to integrity is reflected in their values and operational practices. The organization emphasizes honesty, good moral principles, and accountability in all aspects of their work. Integrity is demonstrated through speaking the truth, maintaining safety, accurate reporting, and tre
0 views • 6 slides
Understanding Integrity Constraints in Relational Database Systems
Integrity constraints play a crucial role in maintaining the accuracy and integrity of data in a database. They include domain constraints, entity integrity, and referential integrity, each serving a specific purpose to ensure data consistency and reliability. Domain constraints ensure values in a c
1 views • 12 slides
Understanding the General Data Protection Regulation (GDPR) and Data Protection Bill
The General Data Protection Regulation (GDPR) is a set of rules aimed at safeguarding individuals' personal data and privacy rights, with key changes from the previous Data Protection Act 1998. The GDPR introduces transparency, consent requirements, enhanced individual rights, breach notifications,
3 views • 40 slides
Exploring Public Integrity and Ethics in Civil Service
This module on public integrity and ethics delves into key instruments for strengthening ethical practices in public organizations, challenges faced, analyzing codes of ethics, and managing integrity risks. The agenda includes activities like structured ethical reflection, understanding public value
1 views • 13 slides
Understanding Integrity: A Biblical Perspective
Explore the concept of integrity through the lens of biblical teachings, focusing on examples from the story of Solomon and David. Discover the meaning of integrity in Hebrew and how it relates to being complete, whole, and consistent in actions and words. Learn about subconscious ways integrity can
0 views • 17 slides
The Significance of Integrity and Honesty in Personal Skills
Understanding the meaning of integrity and how it relates to honesty is crucial for individuals to live ethically. This article delves into the importance of honesty and integrity, evaluating one's own level of honesty, and practical scenarios showcasing integrity in action.
0 views • 16 slides
Groundskeeping Safety and Personal Protective Equipment Training
This presentation covers essential information on groundskeeping safety and the proper use of personal protective equipment (PPE). Topics include head protection, eye/face protection, hearing protection, respiratory protection, hand protection, body protection, foot protection, as well as guidance o
0 views • 35 slides
Rethinking Conditionalities in Social Protection Programs
The images and descriptions provided delve into the concept of conditionalities within social protection programs, highlighting how they can mask poor service quality, create opportunities for coercion, and strip away the protection and safety nets meant to support individuals. The narrative advocat
0 views • 8 slides
Veeam Software: Risk Mitigation and Protection Overview
Veeam Software offers solutions for risk mitigation and data protection, helping businesses save time, reduce costs, and meet their goals. With a focus on virtualization, storage, and cloud technologies, Veeam addresses challenges in data protection, backup integrity, and recovery speed. Through enc
0 views • 10 slides
Academic Integrity Policy at UIS - Guidelines and Procedures
The Academic Integrity Council at UIS ensures fair operation of hearing panels, reviews the policy implementation, and educates the community. It aims to protect the integrity of the academic environment and helps students develop integrity. Enforcement and effectiveness rely on faculty and departme
0 views • 14 slides
The Importance of Social Protection and the African Union in Africa
Social protection is recognized as a fundamental human right, and efforts within the African Union have been made to promote social protection programs to combat poverty in Africa. The growth of social protection initiatives since the Ouagadougou declaration of 2004 has led to increased awareness an
0 views • 12 slides
Academic Integrity Board Game Overview
Academic Integrity Board Game offers a fun and educational approach to understanding academic integrity. The game revolves around values like honesty, trust, fairness, respect, responsibility, and courage, as defined by the International Center for Academic Integrity. Players set up the board, place
0 views • 4 slides
Importance of Fall Protection Systems in Workplace Safety
Fall protection systems play a crucial role in preventing injuries and fatalities caused by falls at the workplace. Understanding the anatomy of a fall, statistics on fall-related incidents, and the various philosophies of fall protection can help companies plan and implement effective fall protecti
0 views • 50 slides
Enhancing Data Integrity Protection in Cloud Storage Using Regenerating Codes
This paper explores the importance of data integrity protection in cloud storage and presents a solution using regenerating codes to detect corrupted data chunks, provide fault tolerance, and enable efficient recovery. It compares regenerating codes with Reed-Solomon codes and discusses their implic
0 views • 36 slides
Understanding Durability and Integrity in Data Storage Systems
Durability and integrity are crucial aspects of data storage systems. Durability ensures data survives faults like crashes and power loss, while integrity ensures data correctness in the face of faults. Disk data is durable due to surviving power loss, and has integrity through explicit and complex
0 views • 24 slides
Exploring the Concept of Integrity through Art and Quotes
Delve into the multifaceted theme of integrity through thought-provoking quotes, artistic interpretations, and personal reflections. Witness how individuals from diverse backgrounds define and exemplify integrity in their own lives. Join the journey to understand the significance of integrity and it
0 views • 8 slides
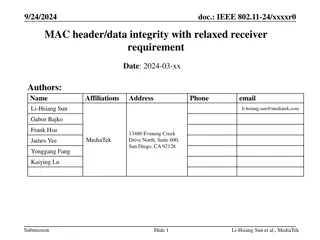
Enhancing Data Integrity in IEEE 802.11 Networks
This document discusses proposals for improving data integrity in IEEE 802.11 networks, specifically focusing on header protection for individually addressed data and management frames. It explores the challenges and alternatives related to verifying Message Integrity Check (MIC) before sending ackn
0 views • 20 slides
Safety and Integrity Enhancements for Gas Transmission Pipelines
The PHMSA Mega Rule (RIN 2) brings significant improvements to the safety and integrity of gas transmission pipelines through repair criteria, integrity management enhancements, cathodic protection, management of change requirements, and more. Key provisions include definitions, inspection protocols
0 views • 15 slides
Supervisor's Role in Guiding Students in Citizen Science and Business Projects
This module focuses on the critical role supervisors play in guiding students engaged in citizen science and business projects. It covers topics such as ethical challenges, academic integrity, and educational materials to support students and supervisors in their collaboration. The training plan inc
0 views • 6 slides
I/O-Efficient Protection Against Silent Data Corruptions in RAID Arrays
This paper discusses the risks of silent data corruptions in RAID arrays, which are challenging to detect and can lead to serious consequences. It presents the concept of integrity protection to enhance RAID systems' ability to detect and recover from such corruptions efficiently. The paper investig
0 views • 26 slides
Improving Consumer Protection in Ghana: Insights from the Sixth Annual African Dialogue Consumer Protection Conference
The Sixth Annual African Dialogue Consumer Protection Conference held in Lilongwe, Malawi in September 2014 shed light on the challenges faced by Ghana's consumer protection policies. Irene Aborchie-Nyahe, a legal consultant, highlighted the gaps in Ghana's legislative framework, lack of effective i
0 views • 14 slides
Proactive Network Protection Through DNS Security Insights
Exploring proactive network protection methods using DNS, security challenges, botnet threats, firewall management, malware controls, and DNS-based malware control. Discussions on DNS security vulnerabilities, DNSSEC, threat intelligence, machine learning, and best practices like RPZ for DNS protect
0 views • 29 slides
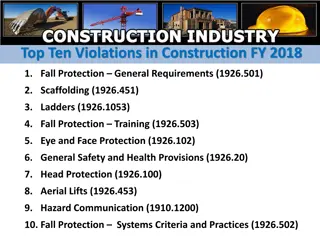
Top Ten Construction Violations FY 2018 Overview
The top ten violations in construction for fiscal year 2018 are related to fall protection, scaffolding, ladders, safety training, eye and face protection, general safety provisions, head protection, aerial lifts, hazard communication, and fall protection systems criteria and practices. The violatio
0 views • 11 slides
Understanding Carnegie Mellon's Protection and Security Concepts
Carnegie Mellon University emphasizes the importance of protection and security in operating systems. Protection involves preventing unauthorized access by users, while security focuses on external threats and authenticating system users. The goals of protection include preventing access violations
0 views • 37 slides
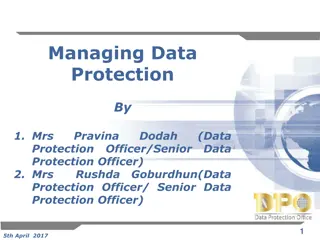
Understanding Data Protection Regulations and Definitions
Learn about the roles of Data Protection Officers (DPOs), the Data Protection Act (DPA) of 2004, key elements of the act, definitions of personal data, examples of personal data categories, and sensitive personal data classifications. Explore how the DPO enforces privacy rights and safeguards person
0 views • 33 slides
Implementing HIPPS for High Integrity Pressure Protection System
Implementing High Integrity Pressure Protection System (HIPPS) is crucial for maintaining the safety and integrity of high-pressure pipelines. HIPPS helps prevent explosions by controlling pressure levels in the pipeline, especially when abnormal conditions occur. By using advanced technology and sa
0 views • 31 slides
Medicaid Integrity Institute 2012 Training Conference Overview
The Medicaid Integrity Institute (MII) provides training and technical assistance to state Medicaid program integrity employees at no cost. The institute, established in 2007 by CMS and the US Dept. of Justice, aims to enhance national program integrity standards. Located at the National Advocacy Ce
0 views • 8 slides
Workshop on Data Protection: Mauritius Police Force Presentation
The workshop on data protection by Mrs. D. Madhub, Data Protection Commissioner, held on May 15, 2019, focused on the Data Protection Act, the Data Protection Office, definitions, functions, powers, and obligations related to data protection, covering areas such as processing of personal data and ri
0 views • 46 slides
Practice Test for Developing Integrity in 4th Grade
This practice test by Renee Cook from Brownsburg, IN, focuses on developing integrity in 4th-grade students. The test includes scenarios where students have to choose the best action reflecting integrity. The test is designed like a dartboard, aiming to find the "bull's-eye" answer that aligns most
0 views • 18 slides