Engaging Students' Voices in Curriculum Making
Understanding the importance of student views in the curriculum-making process and the need for an authentic experience to empower student voice. The Independent Investigation explores findings from student surveys and A-level specification preferences. Delve into how investigations were organized a
1 views • 22 slides
Software Requirement Analysis and Documentation Process
The requirement analysis and specification process involves gathering information from customers, identifying the problem, solutions, data requirements, complexities, and potential interfaces. Key components of a Software Requirements Specification (SRS) document include functional requirements, non
0 views • 23 slides
Design Methodology for IoT Platforms: Functional View Specification
Functional view specification in IoT platform design methodology involves defining functional groups for devices, communication, services, management, security, and applications. Each group serves specific purposes such as device monitoring, communication protocols, service provision, system managem
1 views • 12 slides
Approaching Exam Questions in A Level English Literature: AQA Specification Overview
Explore how to approach exam questions in A Level English Literature following the AQA specification, focusing on question types such as Aspects of Tragedy and Social and Political Protest Writing. The guidance includes insights on interpreting Shakespeare extracts, understanding tragic trajectory,
0 views • 28 slides
Understanding Memory Management in Computer Systems
Explore Carnegie Mellon University's concepts on heap management and memory allocation strategies as detailed in "Computer Systems: A Programmer's Perspective." Dive into topics such as extending the heap, free blocks, and common problems with throughput and memory utilization.
0 views • 21 slides
Importance of Job Description and Job Specification in Job Analysis
Job description and job specification are essential components of job analysis, providing crucial data for HR managers to understand job requirements and find the right candidate. While not legal requirements, they play a vital role in recruiting, selecting, and placing employees effectively. Job de
0 views • 6 slides
Understanding Specification and Quantity Survey in Construction Projects
Specification in construction projects is a detailed written description of materials, workmanship, and instructions for executing tasks. Specifications complement drawings and serve as contract documents, guiding contractors on materials, methods, standards, and project requirements.
0 views • 31 slides
IoT Platforms Design Methodology for Efficient System Development
Designing IoT systems can be complex due to the interactions between various components like devices, network resources, web services, analytics, applications, and servers. This article presents a generic design methodology for IoT systems that is independent of specific products or services, leadin
2 views • 8 slides
Eduqas GCSE Geography Specification Overview
Welcome to the online meeting of the Eduqas regional team! This session provides information on the GCSE Geography Specification, including changes for 2021. The ethos of the qualification emphasizes developing learners' geographer thinking skills. The course is divided into three components coverin
0 views • 33 slides
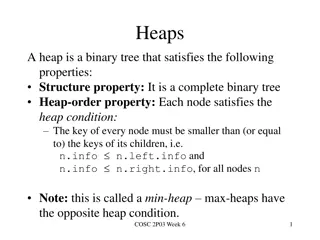
Understanding Heaps in Binary Trees
Heaps are binary trees that adhere to specific properties, such as being complete and satisfying the heap-order property. This involves nodes having keys smaller than or equal to their children. Key operations like removeMin and insert can be performed on heaps efficiently. Array implementations all
0 views • 10 slides
IoT Platforms Design Methodology by Dr. Snehlata Barde - Overview
Designing IoT systems can be complex, but with a generic methodology like the one proposed by Dr. Snehlata Barde, designing, testing, and maintaining IoT systems becomes more efficient. The methodology focuses on purpose, requirements, process specification, domain model specification, information m
0 views • 9 slides
Runtime Checking of Expressive Heap Assertions
Motivated by the unreliability of large software systems due to concurrency bugs and limitations of static analysis, the goal is to enable runtime analysis of deep semantic properties with low overhead. This involves checking expressive heap assertions at runtime with minimal impact on performance,
0 views • 15 slides
2013 C&MS Traffic and Roadway Specification Updates Overview
Detailed overview of key specification updates in 2013 for traffic, roadway, guardrail, fence, maintaining traffic, and concrete barriers. Includes changes in materials, methods of measurement, and new items like fenceline seeding and mulching. Contractor requirements and measurement specifics are h
0 views • 29 slides
Data Structures and Heaps in Computer Science - Lecture 10 Overview
Explore the concept of heaps and heapsort in data structures, focusing on the binary heap data structure as an array object that resembles a nearly complete binary tree. Learn about binary tree representations, heap properties, and vertex assignments in a linear array to enhance search efficiency. U
1 views • 33 slides
Soft Heap and Soft Sequence Heaps: Properties and Applications
Explore the properties and applications of Soft Heap and Soft Sequence Heaps, discussing how corruption handling and selection functions are optimized in these data structures. The concept of car-pooling and the simplification of heap operations are highlighted, along with references to relevant res
1 views • 10 slides
Overview of Soft Sequence Heaps in Algorithms
Soft sequence heaps are a specialized data structure designed to handle corruptions in heap operations efficiently. This technology, introduced at Aarhus University, simplifies heap manipulation, particularly in car-pooling and other applications, with a focus on minimizing corruptions during extrac
0 views • 10 slides
Understanding Heap Sort in Data Structures
Heap Sort, a sorting algorithm based on the concept of a heap data structure, is explained in detail. The properties of a heap, its implementation using a complete binary tree, and its application in priority queues are discussed. The process of building a heap, inserting elements, and sorting them
0 views • 7 slides
Understanding Heap Overflows: An Introduction to Exploit Development
Learn about heap overflows in exploit development, including heap structure, memory maps, exploiting vulnerabilities, and controlling writes in the heap. Understand the difference between stack and heap, viewing heap in gdb, targeted exploit techniques, and the challenges of controlling EIP in the h
0 views • 17 slides
Understanding Priority Queues and Heap Data Structures
Priority queues play a key role in computer science algorithms by managing data based on priority levels. The use of heap data structures enhances the efficiency of priority queue operations. This tutorial covers the basics of priority queues, their applications, different implementations such as li
0 views • 30 slides
Abstract Domains for Lists and Heap Structures: A Comprehensive Overview
Explore the concepts of quantified data automata on skinny trees, automatic shapes in static analysis, universally quantified properties on lists, heap configurations with skinny trees, and the extension of quantified data automata over lists. Dive into the abstract domain of automata to capture inf
1 views • 20 slides
Heapsort and Heaps: A Generic Algorithm for Sorting
This content discusses the concept of heapsort and heaps in the context of sorting algorithms. It covers a generic algorithm for sorting a sequence of numbers in non-decreasing order, detailing different implementations and time requirements for inserting and removing elements from a set. A clever c
0 views • 50 slides
Understanding Heap Data Structure Implementation
Explore the implementation of a heap data structure through a complete binary tree concept, array representation, adding elements, removing elements, and avoiding swaps. Learn the steps involved in adding, removing, and organizing elements within a heap for efficient data storage and retrieval.
0 views • 17 slides
Understanding Heap Sort and Binary Search Tree Concepts
Learn about Heap Sort for sorting elements in ascending or descending order, Priority Queue as a data structure supporting key operations, Binary Trees with recursive definitions, and exercises involving priority queue operations. Explore the concepts through visual aids and examples provided in the
0 views • 18 slides
Understanding Heap Overflow Attacks
A heap is a collection of variable-size memory chunks managed by the program. Heap overflow attacks occur when malicious actors corrupt heap memory, potentially allowing them to overwrite data and execute arbitrary code. This poses a significant security risk. The process involves manipulating heap
2 views • 19 slides
Implementing Heaps: Node Operations and Runtime Analysis
Understanding the implementation of heaps involves knowing various node operations like finding the minimum node, last node, next open space, children, and parent. The runtime analysis of heap operations such as peekMin, removeMin, and insert are crucial for optimizing performance. This recap covers
0 views • 9 slides
Understanding Priority Queues and Heaps in CSE 373 Lecture
Today's lecture in CSE 373 covers the Priority Queue Abstract Data Type (ADT), the properties of heaps, and their implementations. Key topics include the completeness property of heaps, different priority queue implementations such as the binary search tree for faster insert and find operations, and
0 views • 21 slides
A Comparative Analysis of Heap Specification Approaches
This presentation discusses various approaches to heap specification, including ownership systems, dynamic frames, permissions, and capabilities. It explores challenges related to invariants and frames, showcasing examples from RockBand and Object state specifications. The discussion covers tools li
0 views • 11 slides
Understanding Memory Management Tradeoffs in Web Browsers
Explore the tradeoffs between memory usage, CPU cost, and performance in web browsers. Learn about setting heap limits, Pareto optimality, and compositional heap limit rules to optimize memory usage efficiently.
1 views • 18 slides
Binary Trees and Heap Implementation in Java
Explore the concepts of binary trees, heap implementation, and traversal techniques in Java through engaging peer instruction materials by Cynthia Lee. Learn about heap uniqueness, in-place heapsort, and generic binary trees. Test your knowledge with reading quizzes and analyze heap outcomes based o
0 views • 27 slides
Overview of SB 850 Homeless Emergency Aid Program (HEAP)
SB 850 establishes the Homeless Emergency Aid Program (HEAP) to provide flexible block grant funds to address immediate homelessness challenges in California. The program moves the Homeless Coordinating and Financing Council (HCFC) to the BCSH Agency and designates the BCSH Secretary as the HCFC Cha
0 views • 33 slides
Dynamic Memory Management Overview
Understanding dynamic memory management is crucial in programming to efficiently allocate and deallocate memory during runtime. The memory is divided into the stack and the heap, each serving specific purposes in storing local and dynamic data. Dynamic memory allocators organize the heap for efficie
0 views • 31 slides
Understanding Memory Management in C Programming
The discussion covers various aspects of memory management in C programming, including common memory problems and examples. It delves into memory regions, stack and heap management, and static data. The examples illustrate concepts like static storage, heap allocation, and common pitfalls to avoid.
0 views • 24 slides
Comprehensive Overview of AI Technical Test Specification
This presentation provides a detailed look at the AI technical test specification authored by Auss Abbood from the Robert Koch Institute in Berlin. It covers best practices in AI testing, essential tests for assessment platforms, testing principles, test levels, test types, and more. The deliverable
0 views • 15 slides
CSE 545 Heap Challenges Overview
In CSE 545, students can expect a series of challenges related to heap exploitation techniques. The assignments involve releasing new challenges with specific deadlines and combining the points earned from previous challenges. The grading system is structured to allocate percentages to each assignme
0 views • 32 slides
Specification Techniques for Verifying Object-Oriented Software
This research discusses specification techniques for verifying object-oriented software, emphasizing the importance of building and maintaining correct programs. It delves into the Verified Software Initiative's vision for reliable computer programs and introduces Spec# programming system, demo, and
0 views • 24 slides
Understanding CPU and RAM Relationship in Memory Segments
A program's address space consists of four segments - code, static data, stack, and heap. Each segment plays a crucial role in memory allocation and management. The OS and C++ runtime handle the allocation and deallocation of memory in the heap segment. Garbage collectors in certain languages aid in
0 views • 22 slides
Understanding Heap Exploitation Techniques in CSE 545 Fall 2020
This collection of images covers various heap exploitation techniques discussed in CSE 545 Fall 2020, such as fastbin use-after-free vulnerabilities, tcache poisoning, double-free exploits, metadata manipulation, and more. The images depict scenarios involving tcache, fast bins, unsorted bins, and f
0 views • 72 slides
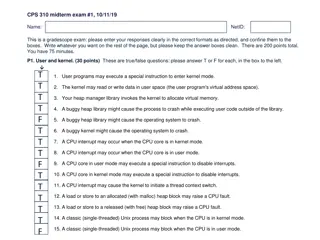
Understanding User and Kernel Modes in Operating Systems
The content provided discusses various aspects of user and kernel modes in operating systems through a set of true/false questions related to user programs, CPU interrupts, heap management, and process behavior in different modes. It touches on the role of the kernel in managing virtual memory, hand
0 views • 10 slides
IoT Platform Design Methodology and Specifications
This content elaborates on the IoT platform design methodology, including purpose and requirement specifications, process specification, domain model specification, and information model specification. It also covers IoT level specifications, functional view specification, operational view specifica
0 views • 10 slides
Mail Specification and Processing Changes Effective September 2024
This document outlines changes in the processing of out-of-specification mail, starting from September 2nd, 2024. Mail pieces that do not meet specified requirements will undergo manual sortation or less efficient processing, potentially incurring additional charges. Reasons for introducing these ch
0 views • 16 slides