Cyber Crime Police Station Hyderabad City
Learn about various types of cyber crimes including online debit/credit card and bank frauds, UPI money scams, social media offenses, hacking incidents, job/visa frauds, and loan/insurance/lottery scams. Stay informed and protect yourself online.
1 views • 12 slides
How to Protect Your On-Demand App from Cyberattacks and Data Breaches
On-demand app development solutions provide convenient services but also carry cybersecurity risks like hacking, malware, and data breaches. This comprehensive guide explores best practices to secure on-demand apps and protect sensitive user data. Learn how encryption, multifactor authentication, ac
0 views • 4 slides
Dismissive Reviews, Citation Cartels, and the Replication Crisis
The study delves into the replication crisis in research, citing factors influencing research credibility such as sample size, effect size, and financial interests. It highlights issues like gaming the system, P-hacking, and data sharing reluctance. The growth of Metascience as a response to these c
0 views • 45 slides
Growth Strategies for Business Success
Explore various growth and survival strategies for businesses, including vertical and horizontal growth, overcoming scarcity of funds, factors affecting organizational growth, and advantages and limitations of business expansion. Learn about different growth strategies such as intensive growth, dive
2 views • 35 slides
Practice Areas - Aegle Marmelos Law Firm in Chennai & Madurai
Practice Areas - Aegle Marmelos Law Firm in Chennai & Madurai\n\n\u2022\tCriminal:\nViolent crimes (murder, assault)\n\u2022\tSexual offenses (rape, harassment)\n\u2022\tProperty crimes (theft, burglary)\n\u2022\tFinancial crimes (fraud, embezzlement)\n\u2022\tCybercrimes (hacking, online fraud)\n\u
0 views • 4 slides
Penetration Testing and Incident Response Technologies Overview
Explore the world of penetration testing, incident response technologies, and ethical hacking in the context of CIS 6395 course at UCF. Learn about tools like Metasploitable 2 VM for vulnerability testing and techniques such as Ping Sweep and Ping. Discover essential concepts for testing and securin
0 views • 32 slides
Understanding Man-in-the-Middle Attacks and Network Security Threats
Explore the risks associated with Man-in-the-Middle attacks including password sniffing and cracking. Learn about ethical hacking, ARP poisoning techniques, encryption methods, and the importance of information security. Discover the legality of hacking under certain conditions and gain insights int
0 views • 13 slides
Understanding the Essence of Data Science
Data science is a dynamic field blending hacking and statistics to derive insights from vast amounts of data. It involves converting various aspects of life into data, creating new forms of value. The demand for data scientists is surging due to the data explosion and technological advancements. A d
0 views • 11 slides
Understanding Cyber Crimes: History, Categories, and Types
Delve into the world of cyber crimes through an exploration of its history, categories, and types. Discover the evolution of cyber crimes from the first recorded incident in 1820 to modern-day threats like hacking, child pornography, denial of service attacks, and more. Uncover the motives behind th
3 views • 15 slides
Understanding Cyber Crime: Risks and Prevention Measures
Cyber crime, including hacking, phishing, and pharming, poses a significant threat in today's digital world. Learn about the types of hackers and how to tackle phishing and pharming attacks effectively. By following security measures such as avoiding sharing sensitive information and updating anti-p
4 views • 18 slides
Understanding Non-Standard Errors in Research Methods
Research teams conducting experiments using the same data show large variations in results, termed as non-standard errors (NSE). Peer feedback helps reduce NSE, but factors like vague hypotheses and test statistic definitions can lead to result discrepancies. Addressing issues like multiple hypothes
0 views • 12 slides
Analysis of Indian Economic Growth: Perspectives and Turnaround
Dr. Shailesh Kumar, Assistant Professor at Bharati College, University of Delhi, delves into the Indian growth experience from two perspectives - aggregate growth over time and variations across states. The turnaround in growth measures post-1980, including GDP per capita and productivity, has been
1 views • 12 slides
Comprehensive Guide to Hacking Techniques & Intrusion Detection
This guide by Ali Al-Shemery provides insights into reconnaissance, intelligence gathering, target selection, and open-source intelligence for successful attacks. It covers the importance of OSINT, rules of engagement, and different forms of information gathering in the realm of cybersecurity.
2 views • 46 slides
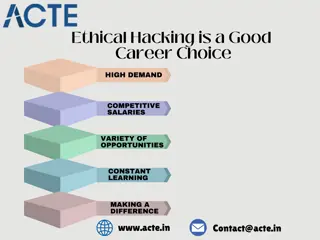
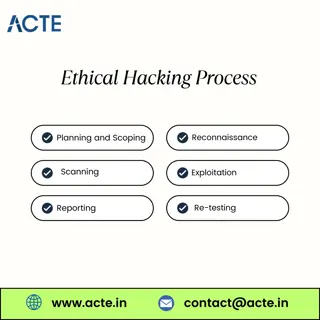
Fundamentals of Ethical Hacking
Ethical hackers are often called \u201cwhite hats\u201d in contrast to \u201cblack hats,\u201d who are the malicious hackers. White hats use their skills to improve security and protect information, while black hats exploit vulnerabilities for illega
0 views • 1 slides
Ethical Hacking Essential Knowledge
Ethical hackers use the same tools and techniques as cybercriminals but with permission and for good reasons.\n\nThink of it as a friendly security check-up. Just like you might get a health check-up to catch any issues early, ethical hacking helps o
0 views • 2 slides
Strategic Management in Tourism: Current Trends and Future Perspectives
This content delves into the strategic management aspects of tourism, focusing on projected growth, determinants of tourism growth, challenges in lesser developed countries, and policies for destination competitiveness. It discusses the projected increase in international tourist arrivals, drivers o
0 views • 9 slides
Understanding Exponential Growth Functions Based on Gordon's Book
This presentation delves into exponential growth functions using real-world examples such as the population growth of Niger. It covers topics such as algebra with exponents, finding formulas for growth models, terminology, and graphing population growth over time. The content explores how exponentia
1 views • 21 slides
Understanding Chronic Cough: Case Study and Assessment
30-year-old L.B., a secretary, presents with a dry, hacking cough and shortness of breath post-bronchitis recovery. History of asthma in family raises concerns. Intake nurse must acquire vital signs, medical history, symptoms, and potential triggers to determine the underlying cause of the chronic c
0 views • 13 slides
Protecting Your Work Environment from Hacking Threats
Safeguarding your work environment from hacking is crucial to prevent potential losses. Addressing human errors, hacker infiltration, targeted phishing, and extortion are key steps to enhance security. Implementing measures like device security, two-factor authentication, firewall protection, and em
0 views • 8 slides
Unveiling Google Hacking Techniques
Explore the art of Google hacking, a method of utilizing advanced search operators and logic operators to uncover sensitive information online. From understanding Google hacking to diving into advanced search strategies and leveraging the Google Hacking Database (GHDB), discover how to enhance your
0 views • 14 slides
Strategies for Growth Hacking in Child Welfare Tech Entrepreneurship
Implementing growth hacking tactics, such as social media engagement, webinars, and event participation, to elevate the visibility of a women-led tech company improving child welfare through software solutions. Focus on leveraging female tech entrepreneurship, engaging social worker communities, and
0 views • 6 slides
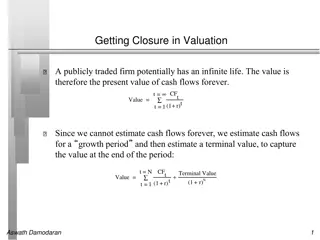
Understanding Terminal Value in Valuation
Valuation of publicly traded firms with potentially infinite lives involves estimating cash flows for a growth period and a terminal value to capture value at the end. The stable growth rate, which cannot exceed the economy's growth rate, plays a crucial role in determining the present value of futu
0 views • 8 slides
Ethical Hacking_ Principles, Practices, and Significance
Ethical hacking involves authorized attempts to gain unauthorized access to a system, application, or data. Also known as penetration testing or white-hat hacking, ethical hacking uses the same methods as malicious hackers to find security weaknesses
0 views • 8 slides
Understanding Oregon's Growth Model for Education Accountability
Oregon's Growth Model for education accountability uses a system that compares student growth to academic peers in the state. School growth ratings are determined based on levels of growth in reading and math, with a focus on tracking student progress over time. By comparing growth percentiles and s
0 views • 25 slides
Implementation of WHO Growth Charts for Infants and Children
Growth charts are essential for assessing children's growth, with WHO setting international standards since 2006. The discussion includes interpreting growth charts, the history of growth references, and the difference between reference and standard growth. It compares CDC's U.S. growth reference to
0 views • 30 slides
Understanding Unix/Linux Hacking Techniques
Explore Unix/Linux hacking techniques including footprinting, scanning, enumeration, vulnerability mapping, remote access, data-driven attacks, buffer overflow, input validation, and countermeasures. Discover methods to gain root access, exploit vulnerabilities, perform brute force attacks, and secu
0 views • 6 slides
Understanding Logistic Growth in Population Dynamics
Explore the logistic growth equation and its applications in modeling population dynamics. Dive into the concept of sigmoidal growth curves and the logistic model, which reflects population growth with limits. Learn how to calculate population change using the logistic growth equation and understand
0 views • 26 slides
Health Care Cost Trends in Oregon: 2013-2019 Report Insights
The report delves into the cost growth trends in health care in Oregon from 2013 to 2019, highlighting the establishment of the Sustainable Health Care Cost Growth Target Program by the state legislature. It monitors and reports on factors driving health care cost increases, with a focus on per-pers
0 views • 35 slides
Exploring Ethical Hacking: Understanding the Different Types of Hackers
Ethical hacking, presented by Mr. Bhushan S. Kulkarni, involves identifying and exploiting vulnerabilities in computer systems for security improvement. This article delves into the definition of hacking, the roles of hackers (Black Hat, White Hat, Grey Hat), and their distinct characteristics and m
0 views • 7 slides
Comprehensive Guide to Hacking Techniques & Intrusion Detection
Dive into the world of hacking techniques, intrusion detection, and network protocols with expert Ali Al-Shemery. Learn about host discovery, port scanning, packet crafting, and more using tools like Nmap. Explore the importance of network protocols like TCP, UDP, ICMP, and ARP. Discover the art of
0 views • 50 slides
Inside the Mind of Hackers: Behavior, Motivation, and Notable Cases
Explore the intriguing world of hackers, delving into their behavior, motivations, and infamous cases such as Kevin Mitnick's social engineering hacks and Adrian Lamo's unique approach to vulnerability disclosures. Discover how figures like Stephen Wozniak and Loyd Blankenship transitioned from hack
0 views • 59 slides
Understanding Hacking: Types, Hackers, and Ethics
Hacking is a complex area covering various topics and activities, originating from MIT in 1960. It involves finding vulnerabilities in computer systems and networks for unauthorized access, potentially harming systems or stealing information. Ethical hacking serves the purpose of identifying and fix
0 views • 11 slides
Understanding BCG Matrix: Market Growth and Relative Market Share
BCG Matrix, developed by Bruce Henderson of the Boston Consulting Group, categorizes business units into Question Marks, Stars, Cash Cows, and Dogs based on market growth and relative market share. Market share and market growth are crucial factors in determining a company's position in the market.
0 views • 31 slides
Comprehensive Guide to Hacking Techniques and Intrusion Detection
This guide by Ali Al-Shemery provides insights into hacking techniques, intrusion detection, fingerprinting, external and internal footprinting, passive reconnaissance, WHOIS lookups, and various online tools for intelligence gathering during penetration tests. It covers identifying customer externa
0 views • 29 slides
Understanding Bacterial Growth and Nutritional Requirements
Bacterial growth involves processes like binary fission, exponential phase, and stationary phase. Factors influencing growth include nutrient availability, oxygen levels, and toxic waste accumulation. Lag phase precedes exponential growth, where cells prepare for division. Stationary phase occurs wh
0 views • 11 slides
Neonatal Nutrition: Growth, Nutritional Support, and Management Phases
Neonatal nutrition, specifically focusing on growth faltering and early nutritional support, is crucial for the well-being of premature infants. Understanding growth rates and providing appropriate nutrients are key goals. Target growth rates and reference growth curves are important considerations.
0 views • 28 slides
Standardizing Fetal Growth Assessment for Improved Patient Care
The SOON Consensus Working Group focuses on conducting large-scale research, quality improvement, and standardizing care in fetal growth assessment. With a mission to address the wide variation among centers, the group aims to enhance patient care by standardizing the measurement and interpretation
0 views • 10 slides
Innovative Security Solutions: Gaetano Perrone Tutor Simon Pietro Romano
Gaetano Perrone, a PhD holder in Information Technology, is the co-founder of SecSI and has a background in Computer Science Engineering. He has worked on projects like AI platforms for ethical hacking and security automation. His contributions include software development of a collaborative ethical
0 views • 10 slides
Understanding Cross-Site Scripting (XSS) Attacks and Prevention Measures
Cross-Site Scripting (XSS) is a prevalent security vulnerability in web applications that allows attackers to inject malicious scripts, potentially leading to unauthorized data access or manipulation. The content covers types of XSS attacks, finding vulnerable websites, testing exploits, and legal i
0 views • 10 slides