Graph Machine Learning Overview: Traditional ML to Graph Neural Networks
Explore the evolution of Machine Learning in Graphs, from traditional ML tasks to advanced Graph Neural Networks (GNNs). Discover key concepts like feature engineering, tools like PyG, and types of ML tasks in graphs. Uncover insights into node-level, graph-level, and community-level predictions, an
3 views • 87 slides
Feature-Based Agile Product Roadmap Template
Keep track of all planned product features with this comprehensive roadmap. Instantly gain insight into each feature and its duration, allowing for customization to timebox sprint periods for Agile development. Ideal for PI planning to prioritize key features effectively.
2 views • 6 slides
Modeling Scientific Software Architecture for Feature Readiness
This work discusses the importance of understanding software architecture in assessing the readiness of user-facing features in scientific software. It explores the challenges of testing complex features, presents a motivating example, and emphasizes the role of subject matter experts in validating
4 views • 20 slides
Update Summary of S-123 Data Model Revision and Major Changes
This document outlines the revisions and major changes in the S-123 Data Model, including the addition and remodeling of feature types, information types, and data models to support remote control and connectivity. It also details the removal and addition of attributes and the restructuring of compl
5 views • 23 slides
Parameter and Feature Recommendations for NBA-UWB MMS Operations
This document presents recommendations for parameter and feature sets to enhance the NBA-UWB MMS operations, focusing on lowering testing costs and enabling smoother interoperations. Key aspects covered include interference mitigation techniques, coexistence improvements, enhanced ranging capabiliti
3 views • 18 slides
Do Input Gradients Highlight Discriminative Features?
Instance-specific explanations of model predictions through input gradients are explored in this study. The key contributions include a novel evaluation framework, DiffROAR, to assess the impact of input gradient magnitudes on predictions. The study challenges Assumption (A) and delves into feature
0 views • 32 slides
What is Adjusted Service Date in QuickBooks?
What is Adjusted Service Date in QuickBooks?\nQuickBooks offers a powerful feature called the Adjusted Service Date, which reflects the actual date a service was provided. This is crucial for accurate financial reporting, better cash flow management, and maintaining strong customer relations. Unlike
0 views • 7 slides
Best service for Feature Walls in Carrigoon Beg
Derek McNamara Joinery serves the Best service for Feature Walls in Carrigoon Beg. They prides itself on delivering superior results that exceed customer expectations. They are skilled in a wide range of carpentry, such as panelling, feature walls, radiator covers, furniture design, and using only t
1 views • 6 slides
Progress Update on S-124 Development and Approval Process
The content provides a detailed agenda for a meeting in Monaco, discussing the progress and development story of S-124, including the approval of Edition 1.0.0. It covers key topics such as the Feature Catalog, Guidance Documentation, Validation, and implementing S-124/S-412 into the GMDSS. The deve
0 views • 18 slides
Exploring a Cutting-Edge Convolutional Neural Network for Speech Emotion Recognition
Human speech is a rich source of emotional indicators, making Speech Emotion Recognition (SER) vital for intelligent systems to understand emotions. SER involves extracting emotional states from speech and categorizing them. This process includes feature extraction and classification, utilizing tech
1 views • 15 slides
Git Branching Models and Workflows
Git branching models determine how code changes are managed and integrated in software development projects. This content discusses successful branching models, emphasizing the usage of master, develop, feature, release, and hotfix branches. It also explains why Git branching is different from centr
0 views • 13 slides
A Unified Approach to Interpreting Model Predictions
Unified methodology for interpreting model predictions through additive explanations and Shapley values. It discusses the relationship between Additive Explanations and LIME, introduces Shapley values, approximations, experiments, and extensions in model interpretation. The approach unifies various
1 views • 21 slides
Understanding Constructive Solid Geometry Concepts
Explore Constructive Solid Geometry (CSG) concepts including binary tree representation, Boolean operations, base feature selection in parametric modeling, and the importance of order in feature creation. Learn about CSG's role in representing solid models and its applications in the field of solid
1 views • 13 slides
Exporting STATA Results to Excel Using PutExcel Feature
Learn how to utilize the PutExcel feature in STATA to effortlessly export your results to an Excel file. With PutExcel, you can export matrices, stored results, images, estimation tables, and even add formulas for calculations. This tool streamlines the process of transferring statistical data to Ex
3 views • 32 slides
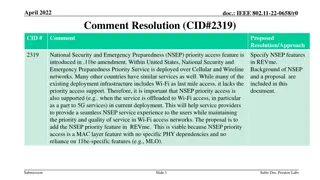
Proposal to Add National Security and Emergency Preparedness Priority Access Feature in IEEE 802.11be Amendment
The document proposes integrating the National Security and Emergency Preparedness (NSEP) priority access feature into the IEEE 802.11be standard to ensure seamless NSEP service experience, particularly in Wi-Fi networks used as last-mile access. The NSEP priority feature at the MAC layer is indepen
0 views • 12 slides
Promote Feature Adoption with Self-Service Password Reset Posters
Enhance feature adoption of self-service password reset among your employees with these ready-to-use posters. Simply customize and print them to encourage password security awareness in your workplace. Don't risk productivity downtime due to forgotten passwords – empower your team to reset their p
0 views • 13 slides
Unleashing the Power of Feature Stories in Writing
Feature stories offer a unique way to engage readers by focusing on personal elements and timeless themes compared to the timeliness of news reports. They allow for creativity, entertainment, and emotion, broadening the storytelling landscape. Understanding the distinction between news reports and f
0 views • 9 slides
Efficient Gradient Boosting with LightGBM
Gradient Boosting Decision Tree (GBDT) is a powerful machine learning algorithm known for its efficiency and accuracy. However, handling big data poses challenges due to time-consuming computations. LightGBM introduces optimizations like Gradient-based One-Side Sampling (GOSS) and Exclusive Feature
0 views • 13 slides
European Commission's Proposal for Carbon Border Adjustment Mechanism
The European Commission's proposal for a Carbon Border Adjustment Mechanism aims to address carbon leakage and reduce emissions through a comprehensive industrial policy known as the European Green Deal. The Fit For 55 Package under the EU Climate Law sets ambitious targets for emission reduction an
7 views • 8 slides
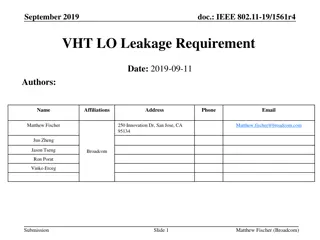
Proposed Relaxation of VHT LO Leakage Limits in IEEE 802.11-19/1561r4
VHT LO Leakage limits in the IEEE 802.11-19/1561r4 standard are deemed unrealistic under reduced TX power scenarios. This document proposes a relaxation of these limits under certain conditions, suggesting amendments for a more realistic approach to addressing LO leakage. The proposal aims to ensure
0 views • 13 slides
Understanding Feature Engineering in Machine Learning
Feature engineering involves transforming raw data into meaningful features to improve the performance of machine learning models. This process includes selecting, iterating, and improving features, converting context to input for learning algorithms, and balancing the complexity of features, concep
0 views • 28 slides
Advancements in Active Secure Multiparty Computation (MPC)
Delve into the realm of secure multiparty computation under 1-bit leakage, exploring the intersection of DP algorithms, MPC, and the utilization of leakage for enhanced performance. Discover the overhead implications of achieving active security, as well as the evolution of secure computation protoc
0 views • 43 slides
Global Relevance and Redundancy Optimization in Multi-label Feature Selection
The study focuses on optimizing multi-label feature selection by balancing global relevance and redundancy factors, aiming to enhance the efficiency and accuracy of data analysis. It delves into the challenges posed by information theoretical-based methods and offers insights on overcoming limitatio
0 views • 15 slides
Parallel Chi-square Test for Feature Selection in Categorical Data
The chi-square test is a popular method for feature selection in categorical data with classification labels. By calculating chi-square values in parallel for all features simultaneously, this approach provides a more efficient solution compared to serial computation. The process involves creating c
1 views • 4 slides
Understanding the Difference Between News and Feature Photography
Differentiating between news and feature photography involves capturing specific events for news photos and unique cultural moments or human interest stories for feature photos. News photos inform viewers with concrete information, while feature photos evoke emotions and delve into a slice of life o
0 views • 24 slides
SolidWorks Lofted Boss/Base Feature Tutorial
Learn to use the Lofted Boss/Base feature in SolidWorks to create basic or complex 3D models such as a flowerpot. Explore how to work with planes, add new planes, and sketch the contour of parts to utilize this powerful tool effectively.
0 views • 15 slides
Holland Brook School Spring Concert 2017 Featuring Strings, Chorus, and Bands
Holland Brook School is hosting its annual Spring Concert on June 8, 2017, at 7:00 PM. The concert will feature performances by the Strings, Chorus, and Bands, showcasing talented students across different grades. Directed by Mr. Jack Hasselbring, the event will include delightful musical pieces ran
1 views • 14 slides
Understanding the Importance of Feature Engineering in Data Science
Feature engineering, a manual and time-consuming process, is a crucial step in data science workflows. It involves generating and transforming features based on domain knowledge. Avoiding the pitfalls of past technologies like expert systems, feature selection plays a key role in determining which f
0 views • 25 slides
Covert Visual Search and Effective Oculomotor Range Constraints
The study delves into whether covert visual search is biologically limited by the Effective Oculomotor Range (EOMR), exploring neuropsychological evidence, eye movement studies, and participant measurements. It investigates the impact on visual search tasks, including color, orientation, and conjunc
1 views • 15 slides
Leakage-Resilient Key Exchange and Seed Extractors in Cryptography
This content discusses the concepts of leakage-resilient key exchange and seed extractors in cryptography, focusing on scenarios involving Alice, Bob, and Eve. It covers non-interactive key exchanges, passive adversaries, perfect randomness challenges, and leakage-resilient settings in symmetric-key
6 views • 35 slides
Real-time Monitoring and Detection of Android Privacy Leakage
PrivacyShield is a groundbreaking solution developed by Yan Chen's Lab at Northwestern University to address the critical issue of private data leakage from Android apps. Through extensive research and evaluations, they have identified vulnerabilities in popular anti-malware tools and uncovered alar
0 views • 19 slides
Efficient and One-Pass Leakage-Resistant Modes of Operation: Triplex Design
Triplex design, a collaborative effort by Yaobin Shen and others from UCLouvain Crypto Group, presents an efficient and leakage-resistant mode of operation. The design focuses on improving performance, enhancing protection against side-channel attacks, and implementing DPA-protected KDF/TGF for subs
0 views • 16 slides
Parallel Implementations of Chi-Square Test for Feature Selection
The chi-square test is an effective method for feature selection with categorical data and classification labels. It helps rank features based on their chi-square values or p-values, indicating importance. Parallel processing techniques, such as GPU implementation in CUDA, can significantly speed up
0 views • 4 slides
RF Leakage Investigations & Atomic Clock Signal Phase Drift Analysis
RF signals ranging from 100 kHz to 150 MHz are utilized for achieving resonance in optical cavities. DC Ground Isolation Units help decouple DC grounds and shield leakage. Spectrum analysis using RF analyzers reveals peaks possibly from neighboring balun leakages. Solutions involve increasing capaci
0 views • 14 slides
Feature Writing: A Narrative Journey Through Unique Characters and Stories
Dive into the world of feature writing, where journalistic articles take on a narrative approach to captivate readers. Explore the lives of individuals like Miley, Amy, Natasia, and Monica, each with their own compelling stories and experiences. From Harry Potter fans to Japanese tea party organizer
0 views • 51 slides
Operation and Maintenance of Multiple Effects Evaporators with TVR
Preparations required for the operation and maintenance of multiple effects evaporators include ensuring the availability of utilities like electricity, water, compressed air, and steam at the required pressure. Proper maintenance steps such as vacuum tests, checking for leakages, and conducting air
0 views • 14 slides
Fruit Image Recognition with Weka: Methods & Results
Fruit image recognition project with Weka involved testing various classification methods using deep-learning techniques for feature extraction and achieving accurate results. Methods included ZeroR, J48 decision tree, and feature manipulation to improve classification accuracy levels. Results showe
0 views • 12 slides
Privacy Challenges in Online Social Networks
Online Social Networks (OSNs) like Facebook, Twitter, and LinkedIn have gained immense popularity with millions of users worldwide. However, these platforms present significant privacy issues, from protecting user data against unwanted exposure to the leakage of sensitive information. Challenges inc
0 views • 18 slides
Revenue Leakage in Air Cargo- How RTSCorp Helps Plug the Gaps
In the competitive world of logistics, air cargo remains a vital lifeline for global trade. However, with its complexities come challenges, and one of the most pressing issues is revenue leakage. Defined as the loss of potential earnings due to ineff
0 views • 5 slides
Partial Key Exposure Attacks on BIKE, Rainbow, and NTRU
Explore the vulnerability of PQC candidates to partial key exposure attacks in schemes like BIKE, Rainbow, and NTRU. Learn about leakage resistance, modeling leakage, practical bounds, and secret key decoding methods. Dive into the erasure and error models, analyzing the security of secret keys in v
0 views • 19 slides