Corporate Unconscionability
The concept of corporate unconscionability, including the exploitation of individuals in a special disadvantage. It explores the requirement of knowledge in cases of exploitation, such as actual knowledge, wilful blindness, recklessness, constructive knowledge, and constructive notice.
0 views • 18 slides
Preventing Sexual Exploitation and Abuse in the Workplace
This content highlights the importance of preventing sexual exploitation and abuse within organizations. It covers definitions of sexual exploitation and abuse, core principles, and measures to raise awareness and protect individuals. The focus is on promoting a safe and respectful work environment
0 views • 25 slides
Understanding Exploitation Strategy Meetings and MARVE for Children at Risk of Contextual Harm
To address concerns of extra familial harm affecting children and young people, this session delves into exploitation strategy meetings and MARVE intervention. Learn about making effective referrals, identifying risks, and when to convene strategy meetings to safeguard vulnerable individuals from ha
1 views • 25 slides
Understanding and Preventing Exploitation - Wolverhampton Safeguarding Together
Explore the sensitive topic of exploitation, focusing on the intricacies of coercion, manipulation, and deception, particularly among children and young people. Learn to identify signs of exploitation, including criminal activities, sexual coercion, and modern slavery. Enhance awareness to provide s
0 views • 24 slides
Comprehensive Training on Protection from Sexual Exploitation and Abuse
This training program covers the history, key concepts, zero tolerance principles, roles and responsibilities, risk factors, consequences, community-based complaints mechanisms, human resources, protection of whistleblowers, and mandatory reporting related to protection from sexual exploitation and
1 views • 38 slides
Cash Frontliners: GBV Risk Mitigation & PSEA Induction
Responsibilities of cash frontliners in mitigating Gender-Based Violence (GBV) risks and protecting against Sexual Exploitation, Abuse, and Harassment (PSEA). Emphasizing the importance of treating beneficiaries with respect, ensuring zero tolerance for any form of exploitation, and implementing fee
0 views • 6 slides
Comprehensive Guide to Penetration Testing Execution Standard (PTES)
Penetration Testing Execution Standard (PTES) is a crucial methodology to simulate attackers' methods for compromising security controls and gaining access to systems. The PTES process involves phases such as Pre-Engagement, Intelligence Gathering, Threat Modeling, Vulnerability Analysis, Exploitati
3 views • 14 slides
Implementation of Updated Form 87A for Exploitation Referrals
This briefing note discusses the implementation of an updated Form 87A to address concerns related to domestic abuse, child sexual and criminal exploitation, FGM, and referrals for child and adolescent exploitation issues. The rationale behind the update, consultation process with key partners, and
0 views • 8 slides
Maximizing Project Impact through Communication, Dissemination & Exploitation
Effective communication, dissemination, and exploitation play a crucial role in Horizon projects, including Horizon Europe, to enhance research visibility, attract support, and open up new opportunities. Understanding the contractual obligations, pathway to impact, and central definitions in this co
0 views • 15 slides
Preventing Sexual Exploitation and Abuse in Humanitarian Work
Sexual exploitation and abuse (SEA) in humanitarian settings involves acts of gross misconduct by workers, including abuse of power for sexual purposes and engaging in sexual activities with minors. Six core principles guide the prevention of SEA, emphasizing the prohibition of sexual relationships
0 views • 10 slides
Enhancing Human Resources for Preventing Sexual Exploitation and Abuse in Humanitarian Responses
This training module focuses on developing policies and measures to promote staff awareness and accountability in preventing sexual exploitation and abuse (PSEA) within humanitarian organizations. The sessions cover strategies for raising staff awareness, integrating PSEA responsibilities into job d
0 views • 22 slides
Understanding Sexual Harassment and Exploitation in Project Implementation
This comprehensive guide covers sexual harassment and exploitation issues within project implementation, including definitions, responsibilities, legal frameworks, and case studies. It emphasizes the importance of reporting and preventing such misconduct to uphold a safe work environment. The conten
0 views • 28 slides
Understanding PSEA: Prevention and Response to Sexual Exploitation and Abuse in Humanitarian Settings
Sexual exploitation and abuse in humanitarian settings pose serious threats to vulnerable populations, directly contradicting humanitarian principles. The establishment of initiatives like the Iraq PSEA Network aims to prevent and respond to such misconduct through awareness-raising, capacity buildi
0 views • 14 slides
Protection from Sexual Exploitation and Abuse (PSEA) in COVID-19 Response
Amid the COVID-19 crisis, the risks of Sexual Exploitation and Abuse (SEA) are heightened, impacting vulnerable populations. It is crucial for humanitarian actors to uphold existing PSEA commitments and systems. SEA violates fundamental human rights, undermines trust, and has severe consequences for
0 views • 18 slides
Addressing Sexual Harassment and Exploitation in Humanitarian Work
Discussing a case study where a female teacher, Haleema, faces sexual advances from a male staff member, Ahmad, in a humanitarian project in Balochistan. Exploring the definitions of sexual harassment and exploitation, analyzing the power dynamics between the individuals involved, and considering th
0 views • 35 slides
Horizon Results Booster - Maximizing Impact for Research & Innovation Projects
The Horizon Results Booster, a service offered by the European Commission, aims to boost the impact of Research & Innovation projects by helping beneficiaries better disseminate and valorize their results, increase exploitation potential, improve access to the market, and implement effective dissemi
0 views • 4 slides
Novelties of Horizon Europe on Dissemination & Exploitation (D&E)
Horizon Europe emphasizes the dissemination and exploitation of project results to enhance impact. Lessons learned from H2020 highlight challenges such as lack of skills and awareness. Horizon Europe addresses these issues through improved guidance, redesigned proposal forms, and increased training
0 views • 17 slides
Toolkit for Identifying Vulnerable Children and Youth at Risk of Exploitation
This toolkit provides resources to support practitioners in identifying children and young people who may be vulnerable to exploitation. It includes a glossary of terms related to exploitation, information on Prevent concerns, safety and support plans, and ways to deliver anti-abuse curriculum. The
0 views • 32 slides
LBHF Gangs, Violence, and Exploitation Unit (GVEU) Overview
LBHF's Gangs, Violence, and Exploitation Unit (GVEU) focuses on keeping residents safe by preventing children and young people from being victimized by organized crime. The council collaborates with the Metropolitan Police to address gang-related issues and provide support to vulnerable individuals
1 views • 9 slides
Part One: Screening Tool Practitioner Toolkit for Child Exploitation Vulnerability
This toolkit provides practitioners with a screening template to identify children and young people vulnerable to exploitation. It covers indicators, checklists, and guidance for addressing immediate needs. The content defines child exploitation, outlines vulnerable groups, emphasizes professional j
0 views • 27 slides
Understanding Child Sexual Exploitation
Child sexual exploitation involves grooming and controlling a child for sexual purposes, with activities categorized into street grooming and online grooming. Street grooming includes befriending the child, gaining their trust, offering substances or gifts, and engaging in sexual acts in exchange fo
4 views • 12 slides
Understanding Child Sexual Exploitation (CSE) in School Communities
Child Sexual Exploitation (CSE) is a form of child sexual abuse involving coercion, manipulation, or deceit for sexual activity. Vulnerable groups include children with disabilities, care leavers, those experiencing bullying, and more. Offenders employ grooming tactics to prepare victims and maintai
0 views • 13 slides
Understanding Complex Safeguarding in Child Protection
Complex Safeguarding involves addressing criminal activities linked to vulnerable children and exploitation. The Child Sexual Exploitation Team focuses on building relationships with youth to reduce risks. The team, comprising various professionals, handles cases related to child sexual exploitation
0 views • 16 slides
Violence Prevention and Trafficking of Indigenous Women, Girls, and 2SLGBTQQIA+ People
This content discusses key terms related to violence prevention and trafficking of Indigenous women, girls, and 2SLGBTQQIA+ people, including assimilation, colonialism, discrimination, grooming, human trafficking, imperialism, intergenerational trauma, patriarchy, racism, settler colonialism, sexual
0 views • 33 slides
Maximizing Project Results: Key Strategies for Effective Exploitation
Discover how to enhance project outcomes through strategic exploitation with the Horizon Results Booster Service. Dive into the Key Exploitable Result (KER) methodology, seminar details, and the crucial approach to optimizing project exploitation activities. Gain insights on maximizing resources, en
0 views • 15 slides
Exploring Issue-Based Marketing and Alliances to Address Violence and Exploitation: A Journey of Transformation
This proposal outlines a strategic shift towards issue-based marketing and alliances to combat violence and exploitation, particularly against children. The document details sessions, updates, and meetings discussing the transition from a product-oriented organization to one focused on causes. Key t
0 views • 8 slides
The History of Racial Discrimination in Queensland: A Documentation of Systematic Injustices
The historical documentation illuminates the systematic racial discrimination in Queensland, spanning early occupation to the implementation of oppressive laws and control mechanisms. From kidnapping indigenous women and children for servitude to enforced employment practices and financial exploitat
2 views • 9 slides
Lessons Learned from Norwich Multi-Agency Child Exploitation Team
The Norwich Multi-Agency Child Exploitation Team pilot project aimed to address exploitation of children in Norfolk through a contextual safeguarding approach. By reframing the criminal justice response, the team focused on supporting exploited children as victims rather than perpetrators. The team
1 views • 10 slides
Labor Super-Exploitation and Value Transfer in Global Economy
Original research explores how labor super-exploitation and transformation drive international value transfer in the capitalist system. The study bridges orthodox Marxist and Ricardian perspectives, offering new insights into unequal exchange and imperialism.
1 views • 21 slides
SMOS Pilot Mission Exploitation Platform (Pi-MEP) Overview
The presentation highlights the tools and capabilities of the SMOS Pilot-Mission Exploitation Platform (Pi-MEP) for providing instantaneous answers to data-related questions, showcasing three ICT infrastructures, and outlining FELYX/NAIAD, Datavore, Datalaps, Merginator, Syntool, and Jupyter noteboo
0 views • 21 slides
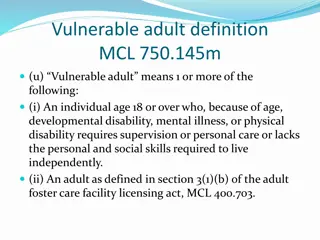
Risks of Financial Exploitation Faced by Vulnerable Adults
Vulnerable adults, including those with disabilities or cognitive impairments, are at risk of financial exploitation through scams like IRS fraud, family emergency scams, and healthcare insurance fraud. Elder financial abuse is on the rise, with billions of dollars lost annually. Recognizing these s
0 views • 32 slides
Zero Tolerance for Sexual Exploitation and Abuse by UN Personnel
Presentation and discussion of the film "To Serve with Pride: Zero Tolerance for Sexual Exploitation and Abuse by UN and related personnel." The session objectives include raising awareness, explaining the principles of the Secretary-General's Bulletin, defining sexual exploitation and abuse, and hi
0 views • 13 slides
Understanding Stack Protection and Exploitation Techniques
Delve into the world of stack protection and exploitation, covering topics like exploiting arbitrary write, issues with stack canaries, and shadow stack usage. Explore defense mechanisms like Stack Cookie and learn about the power of exploiting vulnerabilities to write arbitrary memory. Discover met
0 views • 23 slides
Understanding Stack Overflow Vulnerabilities and Exploitation Techniques
Explore the history of stack overflow vulnerabilities, learn how to control a PC using stack overflow, place shellcode in memory, calculate shellcode addresses, and execute shellcode. Understand different types of overflows including stack overflow, heap overflow, and integer overflow. Delve into th
0 views • 33 slides
Understanding Gang Culture and Criminal Exploitation - Session Insights
This session delves into the complexities of gang culture, criminal exploitation, vulnerability, and violence. Attendees will learn about identifying susceptibility to exploitation, recognizing early warning signs in child protection work, and implementing effective responses to criminal exploitatio
0 views • 42 slides
Protecting Children from Sexual Online Exploitation: Understanding the Threat
Child sexual exploitation is a form of abuse where offenders exploit their power over children, both in person and online. This abuse can take various forms such as cyber molestation, grooming, sextortion, and sexting. It is crucial to educate children, parents, and caregivers about the risks and si
0 views • 13 slides
Understanding Heap Exploitation Techniques in CSE 545 Fall 2020
This collection of images covers various heap exploitation techniques discussed in CSE 545 Fall 2020, such as fastbin use-after-free vulnerabilities, tcache poisoning, double-free exploits, metadata manipulation, and more. The images depict scenarios involving tcache, fast bins, unsorted bins, and f
0 views • 72 slides
Financial Exploitation of Older Americans: Legal and Policy Solutions
Explore the legal and policy solutions for addressing financial exploitation of older Americans, including definitions, incidences, regulatory approaches, risk factors, statistics, and consumer financial market trends. Discover the nuances of elder financial abuse, the distinctions between pure and
0 views • 24 slides
Supporting Families Against Child Exploitation: The CACE Journey
Empowering parents and caregivers through education, support groups, and mentorship to combat child exploitation. The Collaboration Against Child Exploitation (CACE) offers informative sessions, ongoing support, and valuable feedback from parents with lived experiences. Through collaboration and pro
0 views • 12 slides
Preventing Sexual Exploitation and Abuse in Humanitarian Settings
Understanding Sexual Exploitation and Abuse (SEA) is crucial in humanitarian work. SEA includes acts like sexual exploitation and abuse, and it is strictly prohibited. This training focuses on the history, core principles, and application of SEA within humanitarian organizations to protect beneficia
0 views • 20 slides