Protecting Accounts & Devices: Stay Secure Online
Secure accounts & devices, manage breaches, prevent attacks, recover lost data. What to do in case of security breach and steps to safeguard personal information and devices.
1 views • 18 slides
Security Breach: Detecting and Exploiting SQL Injection in Contact Groups
Suspect a potential SQL injection in the macros used in Contact groups? Learn how to identify and exploit it through blind SQL injection techniques. Follow step-by-step instructions to execute a payload that alters user data and gain unauthorized access. Stay vigilant and proactively safeguard your
3 views • 27 slides
Privacy Breach Management Guide by Health PEI
Understanding, Preventing, and Managing Privacy Breaches in Healthcare: Learn about what constitutes a privacy breach, how to prevent breaches, steps to determine and manage breaches effectively, including containment, investigation, and notification processes.
0 views • 10 slides
Ask On Data for Efficient Data Wrangling in Data Engineering
In today's data-driven world, organizations rely on robust data engineering pipelines to collect, process, and analyze vast amounts of data efficiently. At the heart of these pipelines lies data wrangling, a critical process that involves cleaning, transforming, and preparing raw data for analysis.
2 views • 2 slides
Cyber Data Breach Review_ A Comprehensive Insight with LDM Global in the USA
In today's digital landscape, cyber data breaches pose significant threats to organizations of all sizes. A cyber data breach can result in severe financial losses, reputational damage, and legal ramifications. To navigate these challenges effectively, companies turn to expert services like those pr
1 views • 13 slides
Data Wrangling like Ask On Data Provides Accurate and Reliable Business Intelligence
In current data world, businesses thrive on their ability to harness and interpret vast amounts of data. This data, however, often comes in raw, unstructured forms, riddled with inconsistencies and errors. To transform this chaotic data into meaningful insights, organizations need robust data wrangl
0 views • 2 slides
Data Breach Exercise: Responding to a School District Breach
This tabletop exercise simulates a data breach within a school district, putting participants in critical decision-making roles to react and respond effectively. Recommendations include anticipating roles needed, preparing for the unexpected, and considering communication strategies. The background
1 views • 31 slides
Postsecondary Data Breach Exercise: Prepare for the Unexpected!
This tabletop exercise simulates a data breach scenario within a complex organization, engaging participants to make critical decisions and respond effectively. Teams will work together to uncover the extent of the breach and devise a response plan. Consider various roles needed in your organization
0 views • 31 slides
Overcoming-Retail-Compliance-and-Security-Challenges-with-Right-GRC-tools
ver felt like your retail business is a house of cards, ready to collapse with one data breach, budget cut, or compliance failure? It\u2019s a scary thought, and one that keeps many retailers up at night. Consider the March 2024 incident with Giant T
6 views • 4 slides
Understanding the Domino's Data Breach Incident and Its Implications
The recent data breach at Domino's India has raised concerns over consumer data protection. With personal information of millions compromised, the need for a uniform Data Protection Law is emphasized. Users are advised to take precautions, while the accountability of companies under existing regulat
0 views • 9 slides
Understanding the General Data Protection Regulation (GDPR) and Data Protection Bill
The General Data Protection Regulation (GDPR) is a set of rules aimed at safeguarding individuals' personal data and privacy rights, with key changes from the previous Data Protection Act 1998. The GDPR introduces transparency, consent requirements, enhanced individual rights, breach notifications,
3 views • 40 slides
Understanding CBAM: Perspectives on the Controversial Carbon Pricing Policy
The article delves into the contentious trade tool CBAM, focusing on its impact from various perspectives such as the EU, driver of CBAM, exporting countries, and challenges related to data sharing. It discusses how CBAM aims to balance carbon pricing norms for imported goods, the phasing out of fre
0 views • 11 slides
Contempt in the Family Jurisdiction with Respect to Breach of Orders
The concept of contempt in the family jurisdiction regarding the breach of court orders other than those for financial relief is crucial for upholding the due administration of justice. Courts have the authority to punish for contempt to safeguard their processes and ensure compliance with their ord
0 views • 17 slides
Understanding Data Governance and Data Analytics in Information Management
Data Governance and Data Analytics play crucial roles in transforming data into knowledge and insights for generating positive impacts on various operational systems. They help bring together disparate datasets to glean valuable insights and wisdom to drive informed decision-making. Managing data ma
0 views • 8 slides
Preparing for EU General Data Protection Regulation with Revd. Mark James
In this comprehensive presentation by Revd. Mark James, learn about the EU General Data Protection Regulation (GDPR) including its background, timeframe, key differences from the EU Data Protection Directive, scope, definitions, and objectives. Understand the enhanced documentation, privacy notices,
1 views • 64 slides
Essential Steps for Personal Data Breach Management
Detect, identify, and respond effectively to personal data breaches by containing the breach, assessing risks, notifying relevant authorities and affected individuals, and implementing measures to prevent future occurrences. Debunk common myths surrounding breach reporting and focus on mitigating ne
0 views • 5 slides
Understanding Breach of Confidence and Privacy Rights in English Law
English law does not provide a specific right to privacy, but breach of confidence laws offer protection against unauthorized disclosure of private information. While there is no overarching invasion of privacy tort, legal controls exist to balance freedom of expression with respect for individual p
0 views • 18 slides
Understanding Professional Duties in Accountancy
This informative content discusses various aspects of professional duties in accountancy, such as negligence, breach of duty of care, causation, asset valuation, and ethics. It covers topics like duty of care, foreseeability test, breach of duty standards, causation principles, and the accountants'
1 views • 10 slides
Understanding Data Privacy in Emerging Technologies
Explore the importance of data privacy in emerging technologies through insights on security threats, breach examples, costs and liabilities, traditional solutions, and legal aspects. Learn about internal and external threats, liability costs, and safeguarding measures to ensure privacy and security
0 views • 13 slides
Can You Afford a Data Breach? Understanding the Risks and Consequences
Explore the potential dangers and implications of a data breach through insightful presentations and visuals by Laura Middleton and James Hayward. Learn about the value of personal data, human errors, and organizational measures to mitigate risks. Stay informed and subscribe to the e-newsletter for
0 views • 10 slides
Effective Method to Protect Web Servers Against Breach Attacks
Abdusamatov Somon presents an effective method called HTB to protect web servers against breach attacks, focusing on secure computation and mitigation. The research addresses side-channel attacks based on compression and the CRIME BREACH issue, providing insights into implementing the breach attack
1 views • 13 slides
Understanding Data Collection and Analysis for Businesses
Explore the impact and role of data utilization in organizations through the investigation of data collection methods, data quality, decision-making processes, reliability of collection methods, factors affecting data quality, and privacy considerations. Two scenarios are presented: data collection
1 views • 24 slides
Privacy Breach Response and Reporting under the Health Information Act
Understanding privacy breaches under the Health Information Act (HIA) is crucial for organizations dealing with health data. This document outlines what constitutes a breach, mandatory notification requirements, factors to consider in determining risk of harm, and potential offences and penalties fo
0 views • 21 slides
Understanding Alabama Data Breach Notification Act for County Governments
Alabama's Data Breach Notification Act requires all county governments and related entities to comply with specific security measures to protect sensitive information of residents. The law mandates prompt investigation and notification in case of a breach, defining what constitutes a breach and sens
1 views • 36 slides
Legal Case Study: Compensation for Breach of Promise
In this legal case study, we examine different scenarios involving breach of promise and the resulting compensation. The study covers promises kept, losses caused by breaches, and the corresponding awards for individuals involved. Various situations are analyzed, from promises kept without mitigatio
0 views • 6 slides
NHS Sussex Conflicts of Interest Breach Register Summary May 2024
NHS Sussex manages conflicts of interest breaches by recording and publishing them on their website. Breaches are documented with details of the nature of the breach and actions taken. In May 2024, no breaches were reported. Previous months had breaches due to late declarations of interest. Staff we
0 views • 5 slides
Cyber Security and Data Privacy Recommendations in Autonomous Vehicles
The recommendations provided by the Subcommittee on Cyber Security and Data Privacy Advisory Council address key considerations such as definitions, data classification, security protocols, public-private partnerships, regulatory frameworks, and data collection, storage, and distribution in the cont
0 views • 26 slides
Data Breach Occurrence at Illinois Department of Transportation
A data breach at the Illinois Department of Transportation exposed social security numbers and employee identification numbers of all current and former employees. The breach was discovered on April 14, 2022, after being visible from April 6, 2022. The breached file was located on an internal IDOT w
0 views • 11 slides
Understanding the European Union General Data Protection Regulation (GDPR)
The European Union General Data Protection Regulation (GDPR) is a comprehensive data protection law that aims to safeguard personal data and privacy within the EU. It replaced the Data Protection Directive and has notable requirements such as notice/consent, data subject rights, data retention, secu
0 views • 5 slides
Evolution of Data Storage and Processing Technologies
Moore's Law, illustrated through examples in processor capacity and travel efficiency, showcases the rapid advancements in technology. From expensive and limited storage options to cheap and abundant data storage, the journey has been transformative. Additionally, data security laws and breach notif
0 views • 21 slides
Legal Dispute Between Walker & Co. and Harrison: Contract Breach Analysis
In the legal dispute between Walker & Co. and Harrison regarding a breached contract over a billboard, Harrison claimed that Walker failed to maintain the sign, justifying contract termination. However, Walker's actions to remedy the breach and the criteria for material breach were evaluated by the
0 views • 9 slides
Understanding Breach of Confidence and Privacy Rights in Legal Context
The legal landscape regarding breach of confidence and privacy rights, especially in the context of English law and the European Convention on Human Rights, is complex and ever-evolving. While English law traditionally does not recognize a right to privacy, recent developments and landmark cases hav
0 views • 18 slides
Cyber Data Breach Review_ Safeguarding Firms in the Digital Age
This blog explores the critical role of Cyber Data Breach Review in protecting legal firms from digital threats. It highlights how LDM Global's approach, grounded in their core values\u2014Team, Results, Accountability, and Quality\u2014helps firms n
1 views • 10 slides
State of Idaho Data Breach & Credit Monitoring Services Overview
This document outlines the State of Idaho's Division of Purchasing's procurement of data breach and credit monitoring services through NASPO ValuePoint. The purpose, scope of services, sourcing team details, evaluation criteria, and RFP process are detailed, emphasizing the benefits of having pre-es
0 views • 33 slides
Healthcare Security Posture at Centura Health in Southern California
Centura Health in Southern California has a robust healthcare security posture overseen by Scott Raymond, encompassing five hospitals, 350 employed physicians, 400 specialists, and various affiliated centers. The approach covers best practices, breach prevention, threats, NIST, HIPAA compliance, and
0 views • 18 slides
Understanding Spectre and Meltdown Security Flaws
Recent security vulnerabilities named Spectre and Meltdown have surfaced in the realm of computer architecture and hardware implementation. These flaws allow attackers to access sensitive data through covert channels utilizing speculative execution mechanisms. The vulnerabilities exploit the perform
0 views • 12 slides
Interactive Data Sharing Exercise by US Department of Education
This interactive exercise conducted by the United States Department of Education's Privacy Technical Assistance Center involves a tabletop simulation of a data breach scenario among organizations sharing student data. Participants take on decision-making roles to respond to evolving challenges and u
0 views • 37 slides
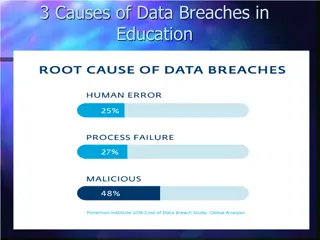
Understanding Data Breach Causes in Education
Data breaches in education are often caused by human errors, process failures, and malicious breaches. Human errors include leaving computers unlocked, sharing passwords, and carelessly discarding sensitive information. Process failures involve not keeping software up-to-date, lack of security polic
0 views • 15 slides
Legal Issues in Data Breaches and Confidentiality Violations
The content covers various scenarios related to breach of confidence, liability of businesses in safeguarding data, and legal causes of action in case of data breaches. It discusses real-life analogies and legal principles concerning the mishandling of confidential information, including a case stud
1 views • 23 slides
Comprehensive Integrated Security Solution Overview by Microsoft
Ponemon Institute's Cost of Data Breach Study reveals the significant financial impacts of data breaches. Microsoft offers an intelligent, unified enterprise defense solution through Microsoft Threat Protection, Azure Security Center, and Azure Sentinel. This comprehensive array of integrated securi
0 views • 6 slides