Buy GBP �50 Bills Online — globcoffs.com
Purchase $50 bills online For Sale from Covert Counterfeiters. Since 2002, this message has been doing the rounds. The notes are issued by either the European Central Bank or the national central banks of the Euro system.The former national currencies were quickly replaced by the euro, which then gr
3 views • 2 slides
Narration and Focalization
Unveil the intricate layers of narration and focalization in storytelling, delving into the impact of the narrator on the story's perception. From the nuances of narration in literature to the complexities of narration in audiovisual content, uncover the diverse facets that shape the fictional world
0 views • 36 slides
Understanding Attention Deficit Hyperactivity Disorder (ADHD)
ADHD is a common neurodevelopmental disorder affecting attention, activity levels, and impulse control. It manifests in different subtypes and can be spotted in children before the age of 6. Symptoms persist across contexts and should cause impairment in social, academic, or occupational areas. Gene
0 views • 39 slides
Why Starting with Cinema is Crucial for a Successful New Product Launch
Launching a new product in today's media landscape can be challenging, with fragmented audiences and intense competition for attention. Starting with cinema in your audiovisual mix can be highly effective in maximizing reach, attention, and trust for your brand. Cinema offers unparalleled levels of
2 views • 11 slides
Steganography: Hiding Secrets in Plain Sight
Steganography, the art and science of concealing secret messages in such a way that no one suspects their existence, differs from cryptography in its goal of avoiding suspicion rather than rendering the message unreadable. This method involves hiding messages within seemingly innocuous data, such as
2 views • 76 slides
Understanding Human Behavior: Foundations and Complexity
Human behavior encompasses the actions and interactions of individuals influenced by factors like genetics, culture, and situational contexts. It involves observable overt behaviors as well as hidden covert behaviors, with a dynamic interplay between individuals and their environments. Psychologists
8 views • 20 slides
Understanding Set Transformer: A Framework for Attention-Based Permutation-Invariant Neural Networks
Explore the Set Transformer framework that introduces advanced methods for handling set-input problems and achieving permutation invariance in neural networks. The framework utilizes self-attention mechanisms and pooling architectures to encode features and transform sets efficiently, offering insig
9 views • 21 slides
ANTECEDENT STRATEGIES
Learn about antecedent strategies presented by Eileen Webster, BCBA, including what antecedents are and how they can help decrease problem behaviors. Discover the importance of positive attention, predictable schedules, praising behavior, and effective pairing techniques in managing classroom behavi
1 views • 19 slides
Understanding Multi-Head Attention Layers in Transformers
Sitan Chen from Harvard presents joint work with Yuanzhi Li exploring the provable learnability of a multi-head attention layer in transformers. The talk delves into the architecture of transformers, highlighting the gap between practical success and theoretical understanding. Preliminaries, prior w
3 views • 38 slides
Unveiling the Effects of Institutionalized Racism on Indigenous Peoples
Delve into the intricate web of institutionalized racism faced by Indigenous communities, exploring key concepts like covert racism versus operant racism, decolonization, and settler benefits. Learn how historical injustices, such as the Indian Act, continue to impact Indigenous autonomy and the fig
9 views • 21 slides
Understanding Organizational Behavior and Characteristics
Organizational behavior explores how individuals behave in various contexts such as child, IPS officer, businessman, etc. An organization is a consciously coordinated unit comprising two or more individuals working towards common goals. Characteristics of an organization include deliberate creation,
2 views • 41 slides
Understanding Attention and Concentration: Key Aspects and Determinants
Attention is our ability to focus on specific stimuli while disregarding distractions. It can be categorized into focused, sustained, divided, and alternating attention. External and internal factors influence our attention levels. The nature of stimuli plays a crucial role in capturing attention ef
0 views • 19 slides
Understanding Human Behavior: Foundations and Factors
Human behavior is a multifaceted subject influenced by genetic makeup, culture, and individual values. It encompasses both overt actions and covert thoughts, a product of the individual and environmental factors. Psychologists study behavior from visible (overt) actions like playing football to inne
0 views • 20 slides
Best Wireless Alarms in Leixlip
Are you looking for the Best Wireless Alarms in Leixlip? Then contact Covert Security. They offer comprehensive residential and commercial security services nationwide. They specialize in providing bespoke intruder wireless alarms and CCTV packages t
0 views • 6 slides
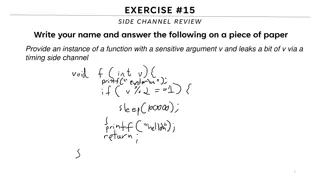
Understanding Side Channels in Software Security
This content delves into the topic of side channels in software security, focusing on the leakage of sensitive information through timing side channels. It discusses the concept of covert channels, reference monitors, limitations of analysis, and prevention strategies to mitigate the risks associate
0 views • 25 slides
Covert Actions and Their Consequences
The chapter discusses foreign covert actions, their limited statutory control, and the President's discretion in carrying them out. It delves into the Bay of Pigs incident, forms of covert actions like propaganda and paramilitary actions, unintended consequences, and the Neutrality Act of 1794. The
1 views • 31 slides
Eisenhower's Cold War Policies and Covert Operations
Eisenhower's Cold War policies focused on Massive Retaliation, Brinkmanship, and Covert Operations. He believed in investing in nuclear weapons and used threats of nuclear capabilities to deter conflicts. The CIA carried out covert operations to overthrow anti-American leaders in different countries
0 views • 10 slides
Covert Visual Search and Effective Oculomotor Range Constraints
The study delves into whether covert visual search is biologically limited by the Effective Oculomotor Range (EOMR), exploring neuropsychological evidence, eye movement studies, and participant measurements. It investigates the impact on visual search tasks, including color, orientation, and conjunc
1 views • 15 slides
Understanding Language Variation and Social Identity
Language and society are intricately connected through accent, dialect, standard English, and non-standard English. The concepts of convergence, divergence, covert prestige, and overt prestige influence how identity is formed. This text delves into regional dialects and accents, highlighting the dif
2 views • 63 slides
Covert Actions and Laws: A Historical Overview
Covert actions, unconstrained by domestic laws, have been historically carried out by various entities in different ways. This overview delves into the Intelligence Authorization Act of 1991, limitations imposed by Congress, utilization of private contractors, challenges in enforcement, and relevant
0 views • 74 slides
Understanding Malware and Computer Security
Exploring the world of malware and computer security, this content delves into different types of malware such as Trojan horses, viruses, worms, and rootkits. It discusses how malware can violate site security policies and the covert actions they can carry out without detection. Examples like the Ge
0 views • 127 slides
Comprehensive Overview of FinSpy Surveillance System
FinSpy is a powerful tool designed for Law Enforcement and Intelligence Agencies to remotely monitor computer systems. It provides access to online communication platforms, internet activities, stored data, surveillance devices, and more. The system components include FinSpy Agent with graphical use
0 views • 190 slides
Security Analysis of Networked Control Systems in Smart Vehicles
This paper explores the security challenges faced by networked control systems in smart vehicles, focusing on adaptive cruise control technology. It discusses the vulnerabilities in cyber-physical systems, such as intrusion detection systems, and highlights the potential risks posed by cyber attacks
0 views • 21 slides
Expert Guidelines on Treatment of Small Vessel Disease
Expert recommendations for the management of covert cerebral small vessel disease (ccSVD) emphasize the use of antihypertensive treatment for hypertensive patients to prevent SVD lesion progression. While there is limited evidence supporting intensive blood pressure lowering targets, systematic bloo
0 views • 14 slides
Hierarchical Attention Transfer Network for Cross-domain Sentiment Classification
A study conducted by Zheng Li, Ying Wei, Yu Zhang, and Qiang Yang from the Hong Kong University of Science and Technology on utilizing a Hierarchical Attention Transfer Network for Cross-domain Sentiment Classification. The research focuses on sentiment classification testing data of books, training
0 views • 28 slides
Psychology Review Questions on Attention and Perception
Explore ungraded review questions on topics like the Stroop effect, visual attention, eye movement tracking, feature integration theory, and more. Test your knowledge and understanding of concepts related to attention and perception in psychology. Use visual aids and prompts to demonstrate your answ
0 views • 8 slides
Evolution of Intelligence Services: Past, Present, and Future
The evolution of intelligence services from pre-digital to post-digital eras is explored, highlighting changes in data collection, analysis, and privacy implications. Legal issues, covert operations, and the impact of bulk data collection are discussed along with the challenges of analyzing vast amo
0 views • 68 slides
Understanding Spectre and Meltdown Security Vulnerabilities
Spectre and Meltdown are two critical security vulnerabilities that exploit microarchitectural features to gain unauthorized access to memory. These vulnerabilities enable attackers to read memory that should be inaccessible, targeting branch prediction and exception handling mechanisms. Side channe
0 views • 19 slides
Covert Computation: Ensuring Undetectable Engagement
Covert computation aims to conceal the fact that computation is occurring and hide engagement in certain tasks like secure computation, authenticated key exchange, and more. By making messages indistinguishable and utilizing steganographic channels, it becomes possible to keep the activities covert
0 views • 16 slides
Challenges in Content Moderation and Cognitive Performance
The content discusses the impact of global social information environment and human-centric cyber vulnerabilities on cognitive performance. It emphasizes the erosion of cognitive abilities due to biases, diminished critical thinking, and exposure to covert exploitation. The dynamics are observed in
0 views • 27 slides
Unveiling the Art of Investigative Journalism
Investigative journalism involves uncovering concealed information, whether intentionally hidden by powerful individuals or obscured amid a sea of facts. It requires utilizing a variety of sources, both public and covert. This practice distinguishes itself from conventional journalism by delving dee
0 views • 41 slides
Understanding Attention Autism: A Creative Approach for Building Communication Skills
Attention Autism is a highly engaging method for developing attention and early communication skills, beneficial for all children. It involves motivating activities, shared experiences, and clear communication. The approach consists of stages such as focusing attention, sustaining attention, shiftin
0 views • 8 slides
Understanding Political Spin and Propaganda in Media
Explore the tactics of political spin and propaganda as tools used to shape public perception and manipulate information. Learn about the techniques politicians employ to navigate media dynamics and the covert spin tactics employed in the realm of communication and journalism.
0 views • 10 slides
Fingerprinting Smart Devices Through Acoustic Components
Smartphones can be uniquely identified through their embedded acoustic components, allowing for targeted advertising and secondary authentication. This method leverages sensors like microphones to create device fingerprints. The goal is to extract these fingerprints through scenarios involving audio
0 views • 25 slides
The Economy and Ecology of Attention in the Digital Age
The text explores the concept of attention economy, emphasizing the scarcity of human attention in the information age. It delves into how attention has become a valuable commodity, driving global corporations to maximize engagement. Discussions cover distraction economics, the role of technology in
0 views • 13 slides
Understanding Spectre and Meltdown Security Flaws
Recent security vulnerabilities named Spectre and Meltdown have surfaced in the realm of computer architecture and hardware implementation. These flaws allow attackers to access sensitive data through covert channels utilizing speculative execution mechanisms. The vulnerabilities exploit the perform
0 views • 12 slides
Understanding Covert Timing Channels in Network Security
Covert timing channels are a method of leaking sensitive information across networks by violating security policies. These channels rely on conveying information through packet arrival patterns rather than the contents of the packets. Military applications, detection by USA government agencies, and
0 views • 26 slides
Russian Economic Warfare in Central and Eastern Europe: Challenges and Impacts
Russia employs overt and covert economic warfare tactics in Central and Eastern Europe, including energy blockages and media manipulation. This strategy poses challenges to democratic values and institutions. The study examines the correlation between Russia's economic footprint and democratic stand
0 views • 24 slides
Multimodal Recurrent Attention CNN for Image Aesthetic Prediction
Using a multimodal recurrent attention neural network, MRACNN, this study proposes a unified approach for image aesthetic prediction by jointly learning visual and textual features. Inspired by human attention mechanisms, the network utilizes datasets like AVA and photo.net comments to enhance multi
0 views • 14 slides
Understanding Side Channels and Information Hiding Techniques in Advanced Information Assurance
This content covers various aspects of advanced information assurance, focusing on side channels and information hiding techniques such as digital watermarking, steganography, and covert channels. It discusses the concept of side-channel attacks, types of system and network channels, fault attacks,
0 views • 24 slides