MONITORING OF TREASURY OPERATIONS
The state financial control system in Uzbekistan is governed by the Budget Code and involves various bodies such as the Accounts Chamber, Ministry of Economy and Finance, and Treasury Service Committee. It includes methods like full control and selective control, types such as preliminary and ongoin
5 views • 10 slides
Budget Execution Challenges in Somalia's Social Sectors
Addressing malnutrition in Somalia is hindered by low budget execution rates in the health and education sectors. Only a small portion of Official Development Assistance (ODA) is channeled through government systems, impacting service delivery and development financing. Donor-supported budgets for h
0 views • 32 slides
PUMM: Preventing Use-After-Free Using Execution Unit Partitioning
Memory-unsafe languages like C and C++ are prone to Use-After-Free (UAF) vulnerabilities. PUMM introduces execution unit partitioning to efficiently tackle this issue. By segregating and managing execution units, PUMM aims to prevent UAF exploits and enhance software security.
0 views • 31 slides
Comprehensive Marketing Process Implementation Plan Presentation
This comprehensive marketing process implementation plan template is designed to guide project teams through the phases of project execution. It includes detailed tasks, timelines, milestones, and phases to ensure successful implementation. The plan covers key aspects from initial project setup to f
5 views • 7 slides
Compliance with Article 66 of the Public Sector Budget Law for Fiscal Year 2023
The document discusses the fulfillment of Article 66 of the Public Sector Budget Law for the fiscal year 2023, detailing approved budget modifications, budget execution progress, and interventions to address and prevent the El Niño phenomenon. It highlights budget reallocations, execution achieveme
2 views • 23 slides
Manufacturing Execution Systems (MES) Market Worth $17.83 Billion by 2030
The global manufacturing execution systems market is projected to reach $ 17.83 billion by 2030, at a CAGR of 7.7% from 2023 to 2030. The growth of this market is attributed to the growing complexity of manufacturing operations, the rising adoption of industrial automation in process and discrete in
2 views • 4 slides
Crash Course in Supercomputing: Understanding Parallelism and MPI Concepts
Delve into the world of supercomputing with a crash course covering parallelism, MPI, OpenMP, and hybrid programming. Learn about dividing tasks for efficient execution, exploring parallelization strategies, and the benefits of working smarter, not harder. Discover how everyday activities, such as p
0 views • 157 slides
Programming in C
Control statements play a crucial role in C programming by allowing the control flow to change during program execution. They enable decision-making and transfer control from one part of the program to another. Additionally, loops help in executing a set of statements repeatedly until a specified co
1 views • 35 slides
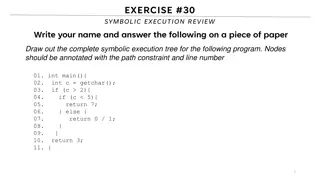
Symbolic Execution Tree for a Program
Generate the complete symbolic execution tree for a given program by annotating nodes with path constraints and line numbers, aiding in understanding program execution flow.
0 views • 26 slides
Integrity in Attestation and Isolation by Luca Wilke
Explore the significance of integrity in the context of attestation and isolation in cloud computing and trusted execution environments. The research delves into the role of Trusted Execution Environments (TEE), commercial TEEs like ARM Trustzone, Intel SGX, and AMD SEV, potential attacks on SEV's a
4 views • 37 slides
Amity School of Engineering & Technology - Java Program Compilation and Execution
Explore the steps for compiling and running a Java program at Amity School of Engineering & Technology. Learn about the compilation and execution process, converting source code into byte code, creating directories, renaming files, and launching command prompts. Dive into the world of Java programmi
1 views • 19 slides
Understanding Advertising Campaign Planning and Execution
Dive into the world of advertising campaigns through insightful information on creative briefs, elements, DAGMAR approach, and budget factors. Learn about the critical role of the creative brief in guiding the message execution process, the objectives and steps of DAGMAR for setting advertising goal
0 views • 23 slides
Modernizing Public Financial Management Systems for Enhanced Efficiency
This content discusses the implementation of an Integrated Financial Management Information System (IFMIS) to improve revenue mobilization, budget execution, and government financial transparency. It covers the objectives of the new IFMIS, including fiscal discipline, improved budget planning, and e
2 views • 14 slides
Enhanced Workshop Planning and Execution Guidelines
Elevate your workshop planning and execution with this comprehensive template designed to streamline the process and ensure a successful outcome. Utilize the Slide Master feature for universal changes, insert your organization's logo, and follow the step-by-step instructions for a professional and e
0 views • 23 slides
Comprehensive Guide to Penetration Testing Execution Standard (PTES)
Penetration Testing Execution Standard (PTES) is a crucial methodology to simulate attackers' methods for compromising security controls and gaining access to systems. The PTES process involves phases such as Pre-Engagement, Intelligence Gathering, Threat Modeling, Vulnerability Analysis, Exploitati
3 views • 14 slides
Understanding the Neglected Provisions of Order XXI CPC, 1908
Explore the overlooked aspects of Order XXI CPC, 1908, focusing on the definitions, types of decrees, modes of execution, procedures for executing decrees, reasons for neglect, impact, recommendations, and conclusion. Learn about neglected provisions like summary execution, execution against legal r
0 views • 14 slides
Virtual Event Management: Strategies and Implementation
Event management involves planning, organizing, and executing various types of events such as corporate, personal, virtual, or hybrid. It encompasses diverse aspects like event structure, marketing, and coordination, crucial for successful event execution. The roles within event management, from coo
1 views • 13 slides
Understanding Addressing Modes in Computer System Architecture
Addressing modes determine how the operand in an instruction is specified, impacting the interpretation and execution. Implied, stack, immediate, direct, indirect, register direct, register indirect, relative, indexed, base register, auto-increment, and auto-decrement are various addressing modes ex
0 views • 4 slides
Understanding Software Testing: Test Cases, Selection, and Execution
Software testing plays a crucial role in identifying and resolving issues within software products. Test cases, selection, and execution are fundamental aspects of the testing process. Test cases define conditions for testing software functionality, with a focus on repeatability and data specificity
2 views • 36 slides
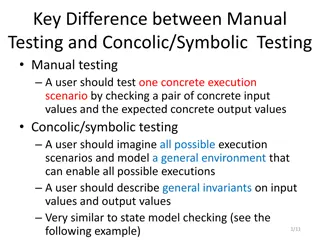
Difference Between Manual Testing and Concolic/Symbolic Testing in Software Development
Manual testing involves checking concrete input and output values for specific execution scenarios, while concolic/symbolic testing requires imagining all possible scenarios and modeling a general environment. General invariants on input and output values are described, similar to state model checki
0 views • 4 slides
Ensuring Security in Persistent Key-Value Stores using Shielded Execution
This content discusses the challenges and solutions for securing LSM-based Key-Value stores in untrusted computing environments using Shielded Execution. It addresses the need for confidentiality, integrity, and freshness of data in persistent storage systems. The research explores Trusted Execution
0 views • 32 slides
Modes of Execution of Decree in Civil Law
The lecture discusses the various modes of execution of decree in civil law, such as execution against a person through arrest and detention, and execution against property. It explains the procedures involved in arrest and detention, including the conditions for release, restrictions on arrest, and
0 views • 9 slides
Understanding Java Memory Management
Explore how memory is managed in Java programs, including memory allocation for code, objects, and execution stack. Learn about memory areas like the execution stack and heap, and understand the concept of activation records in method execution.
0 views • 27 slides
Exploring Instruction Level Parallel Architectures in Embedded Computer Architecture
Delve into the intricacies of Instruction Level Parallel Architectures, including topics such as Out-Of-Order execution, Hardware speculation, Branch prediction, and more. Understand the concept of Speculation in Hardware-based execution and the role of Reorder Buffer in managing instruction results
0 views • 51 slides
Evolution of Execution Methods in Modern Society
Explore the historical and modern methods of execution, from hanging to lethal injection, and the transition towards more civilized approaches. Learn about the contributions of prominent figures like Elbridge Gerry in advocating for humane execution methods. Delve into the commercial rivalry between
0 views • 13 slides
Secure and Efficient Multi-Variant Execution in Distributed Settings
This paper discusses dMVX, a system for secure multi-variant execution in distributed settings to mitigate memory errors and protect against attacks. Using leader and follower variants, diversified program variants run in lockstep to ensure security. The system monitors and replicates I/O results, e
0 views • 35 slides
Hardware-Assisted Task Scheduler for OS Intensive Applications
A hardware-assisted task scheduler called SchedTask is proposed to address the issue of instruction cache pollution in OS intensive applications. By utilizing SuperFunction characterization and a specialized scheduler, the system aims to optimize task execution on different cores for improved perfor
0 views • 28 slides
Automated Concolic Testing of Smartphone Apps
This research focuses on automated concolic testing of smartphone apps, addressing problems and solutions related to generating test inputs for exhaustive testing. It explores the challenges of generating individual events and sequences of events in smartphone applications, aiming to enhance testing
0 views • 47 slides
Understanding Code Execution Graphs and Superblocks in Software Analysis
Explore the concepts of Static Execution Graphs, Dynamic Execution Graphs, Superblocks, hot-path detection, and memory arithmetic in software analysis. Learn about the grouping of blocks, violation tracking, control dependencies, and code behaviors across time through these graphical representations
0 views • 9 slides
Understanding Processes in Operating Systems - ECE344 Lecture 3 Summary
This lecture delves into the essential concepts of processes, threads, and synchronization in operating systems. Key topics covered include units of execution, representation of units of execution in the OS, process execution states, and state transitions. Users, programs, and the role of processes
0 views • 45 slides
InvisiSpec: Making Speculative Execution Invisible
InvisiSpec presents a novel defense mechanism to address speculative execution attacks in the cache hierarchy. By making speculative execution invisible to potential attackers, this holistic approach aims to mitigate the risks associated with exploiting side effects on incorrect paths, such as Spect
0 views • 18 slides
Multicycle Datapath and Execution Steps Overview
This content provides a detailed explanation of a multicycle datapath and the execution steps involved in processing instructions. It covers key elements such as instruction fetching, decoding, memory referencing, ALU operations, branch and jump instructions, as well as memory access for read and wr
0 views • 11 slides
Understanding Symbolic Execution and Directed Automated Random Testing
Symbolic Execution is a method used for analyzing programs to determine inputs causing each part to execute, vital in program testing. However, limitations arise in cases without code availability, hindering definitive path conditions. Directed Automated Random Testing (DART) overcomes this through
0 views • 20 slides
Secure Cloud Applications with Intel SGX - OSDI 2014 Presentation Summary
This presentation discusses the challenges of trusting cloud environments and proposes solutions utilizing Intel SGX technology. It explores the need for secure execution of applications on untrusted cloud platforms, presents existing solutions, and introduces the concept of Haven for private execut
0 views • 33 slides
Rethinking Processes with Threads in Operating Systems
Processes in operating systems traditionally include various resources and execution states, leading to inefficiencies in communication and parallel program execution. By separating the concept of a process from its execution state, modern OSes like Mac, Windows, and Unix introduce threads as lightw
0 views • 29 slides
Python Programming Essentials: Basics, Operators, Expressions, and Control Flow
This segment delves into the fundamentals of Python programming with a focus on essential concepts such as comments, numbers, strings, variables, arithmetic operators, logical operators, order of execution, expressions, and control flow statements like conditional execution and looping. Learn about
0 views • 12 slides
Understanding Operating System Concepts: Multiprogramming, Multiprocessing, Multitasking, and Multithreading
In the realm of operating systems, terms like multiprogramming, multiprocessing, multitasking, and multithreading can often be confusing due to their similar appearance but distinct meanings. These concepts play a crucial role in efficiently managing resources in a computing system, particularly in
0 views • 6 slides
Memory Allocation and Program Execution Overview
Understanding memory allocation is crucial for efficient program execution. This content delves into the importance of memory allocation, considerations for storing data during program execution, and the requirements for allocating memory efficiently. It also explores solutions for managing memory s
0 views • 35 slides
Automated Unit Testing of Large Industrial Embedded Software using Concolic Testing
Embedded software is growing in size and complexity, especially in industries like smartphone development. Manual testing is often ineffective and inefficient due to corner case bugs and test case generation challenges. To address these issues, automated unit testing utilizing Concolic Testing, a co
0 views • 33 slides
Understanding CPU Virtualization and Execution Control in Operating Systems
Explore the concepts of CPU virtualization, direct execution, and control mechanisms in operating systems illustrated through a series of descriptive images. Learn about efficient CPU virtualization techniques, managing restricted operations, system calls, and a limited direct execution protocol for
0 views • 18 slides