Child Protection in Nutrition CVA
Mainstreaming child protection within humanitarian responses is crucial in addressing risks of exploitation, abuse, and violence during crises like in Myanmar. By integrating protection concepts into various sectors and programs, actors can better ensure the safety, dignity, and empowerment of vulne
0 views • 27 slides
A Primer on Planetary Protection for Thermal Engineers
Delve into the realm of planetary protection with this comprehensive primer tailored for thermal engineers by Betsy Pugel, PhD. Explore the intersection of thermal and planetary protection, flight project practicalities, and the crucial components of forward and backward contamination. Gain insights
1 views • 48 slides
Protection Analysis using the PAF
In this session, participants will learn how to utilize the Protection Analysis Framework (PAF) and its tools to conduct effective protection analysis. The session covers an overview of PAF, understanding its pillars, and analyzing data to comprehend essential protection concepts. Key points include
5 views • 48 slides
Understanding Computer Organization and Architecture
A computer system is a programmable digital electronics device that processes data as per program instructions to provide meaningful output. It comprises hardware and software components, with hardware being the physical parts and software essential for driving the hardware. Computer organization fo
14 views • 71 slides
The Digital Personal Data Protection Act 2023
The Digital Personal Data Protection Act of 2023 aims to regulate the processing of digital personal data while balancing individuals' right to data protection and lawful data processing. It covers various aspects such as obligations of data fiduciaries, rights of data principals, and the establishm
3 views • 28 slides
Addressing Gender-Based Violence in Windhoek, Namibia: Enhancing Protection Order Enforcement
Exploring the challenges and shortcomings in enforcing protection orders related to gender-based violence in Windhoek, Khomas Region, Namibia. The team members from various health and public service sectors collaborate to tackle issues like complicated application procedures, delays in serving prote
4 views • 12 slides
Governance and Managerial Leadership of Formal Social Protection in Africa: Insights from Cameroon's National Social Insurance Fund (CNPS)
This presentation delves into the governance and managerial leadership of formal social protection in Africa, focusing on Cameroon's CNPS system. It discusses the institutional evolution of social protection, the challenges faced by bureaucratic and political stakeholders, and the roles of various s
0 views • 8 slides
Understanding Humanitarian Protection and Addressing Needs in Conflict Situations
Explore the concept of protection in conflict situations, identify risks faced by individuals, and learn ways to address protection needs through examples and case studies. Understand the intertwining of protection and health interventions in humanitarian work.
0 views • 9 slides
Overview of Computer Hardware Components and Software Functions
Computer hardware components such as monitor, CPU, mouse, and projector are essential physical parts of a computer system, while software includes intangible programs like operating systems and utility software. Hardware components perform tasks like displaying data, processing information, and prin
8 views • 9 slides
Ultimate Guide to Paint Protection Film - Keep Your Car Looking New
Investing in Paint Protection Film is a smart decision for any car owner who values their vehicle's appearance and wants to extend its lifespan. With its numerous benefits, from scratch resistance to UV protection, PPF offers unparalleled protection
0 views • 3 slides
Securing BIOS: Flash Protection Mechanisms and Best Practices
Explore advanced x86 BIOS security mechanisms like Global Flash Protection, Global BIOS Write Protection, and SMM-derived Write Protection to prevent unauthorized writing to the BIOS. Discover how BIOS vendors can enhance security configurations to thwart attackers effectively.
2 views • 38 slides
Progress Report on Equitable Occupant Protection Working Group
The Informal Working Group on Equitable Occupant Protection (IWG EqOP) has made significant strides in enhancing the safety and protection of a diverse population, focusing on passenger car occupants. The IWG's workplan includes tasks related to regulatory changes, addressing diversity issues, and a
0 views • 12 slides
Eye Protection Training for Workplace Safety
Understand the importance of proper eye protection at work, including identifying at-risk job functions, selecting the right PPE, and knowing responsibilities for employees and employers. Training covers when PPE is necessary, how to use, maintain, and dispose of it properly, and the need for retrai
2 views • 28 slides
Tailoring Innovative Protection Response in Times of Covid-19
Tailoring an innovative and pragmatic response to a multi-faceted protection crisis amidst Covid-19 can be achieved through a comprehensive approach that addresses key issues, operational challenges, field operations and capacity, funding asks, advocacy messages, and incorporating the Protection Clu
2 views • 7 slides
Understanding Computer Architecture and Organization
Computer architecture and organization are fundamental aspects of computing systems. Computer architecture focuses on the functional design and implementation of various computer parts, while computer organization deals with how operational attributes come together to realize the architectural speci
3 views • 40 slides
Tribal Workforce Protection and Sovereignty-based Legislation
Tribal workforce protection and sovereignty-based legislation play a crucial role in safeguarding diverse workforces from discrimination, harassment, and disparate treatment. This legislation, enacted by Tribal Governments, aims to ensure equal rights and opportunities for individuals regardless of
1 views • 22 slides
Understanding Computer System and Organization
Computer Organization involves the logical structure of a computer, defining the interconnections of components for optimal performance. Computers process data through an Input-Process-Output cycle, with input, processing, and output units working together. The characteristics of a computer include
1 views • 20 slides
Computer Science Department Information and Courses Offered
The Computer Science Department provides information on courses offered for GCSE or BTEC qualifications, specifically focusing on the AQA GCSE in Computer Science. The course equips students with valuable thinking and programming skills essential in the modern workplace, covering key concepts and pr
3 views • 7 slides
Anatomy of a Computer System: Hardware Components and Functions
A typical computer system consists of hardware and software working together to perform various computational tasks. The hardware components include the central processing unit (CPU), input/output devices, storage units, and the motherboard. The CPU acts as the main brain of the computer, performing
6 views • 6 slides
Understanding Computer Processing Systems
Computer processing systems consist of various components such as the control unit, ALU, input unit, CPU, output unit, memory, and more. Input devices feed raw data to the computer, while output devices provide processed information. The CPU plays a crucial role in executing instructions and data pr
0 views • 13 slides
Understanding the General Data Protection Regulation (GDPR) and Data Protection Bill
The General Data Protection Regulation (GDPR) is a set of rules aimed at safeguarding individuals' personal data and privacy rights, with key changes from the previous Data Protection Act 1998. The GDPR introduces transparency, consent requirements, enhanced individual rights, breach notifications,
3 views • 40 slides
Civil Society Training on Public Finance Management for Social Protection
Public Finance Management involves mobilizing revenue, allocating funds, and undertaking public spending efficiently and transparently to achieve satisfactory social outcomes. Civil society and trade union advocates play a crucial role in integrating social protection into the PFM process to realize
0 views • 52 slides
Understanding Social Protection and Disability Inclusion
Social protection encompasses various programs such as social security, social assistance, and welfare to ensure individuals have access to healthcare and income security. Disability-inclusive social protection addresses risks and vulnerabilities faced by Persons with Disabilities (PWDs), including
0 views • 24 slides
**Exploring Inquiry-Based Learning in Computer Science Education**
Inquiry-based learning (IBL) in computer science classrooms focuses on fostering communication, collaboration, decision-making, and problem-solving skills among students. The approach involves students constructing knowledge through independent, active activities based on real-world experiences. How
0 views • 18 slides
Evolution of Algorithms and Computer Science Through History
The history of algorithms and algorithmic thinking dates back to ancient times, with the development of general-purpose computational machines by Charles Babbage in the 19th century marking a significant advancement. The term "computer science" emerged in 1959, encompassing theoretical computer scie
1 views • 39 slides
Groundskeeping Safety and Personal Protective Equipment Training
This presentation covers essential information on groundskeeping safety and the proper use of personal protective equipment (PPE). Topics include head protection, eye/face protection, hearing protection, respiratory protection, hand protection, body protection, foot protection, as well as guidance o
0 views • 35 slides
Rethinking Conditionalities in Social Protection Programs
The images and descriptions provided delve into the concept of conditionalities within social protection programs, highlighting how they can mask poor service quality, create opportunities for coercion, and strip away the protection and safety nets meant to support individuals. The narrative advocat
0 views • 8 slides
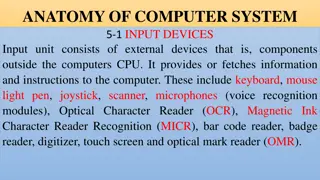
Overview of Computer Input and Output Devices
Input devices of a computer system consist of external components like keyboard, mouse, light pen, joystick, scanner, microphone, and more, that provide information and instructions to the computer. On the other hand, output devices transfer information from the computer's CPU to the user through de
0 views • 11 slides
Understanding Computer Graphics: An Overview
Computer graphics involves creating images and animations using a computer through hardware and software systems. It has evolved significantly over the years, with advancements in generating various types of computer graphics. Learn about the basics of computer graphics, including digital image repr
0 views • 15 slides
Understanding Computer Crimes and Prevention Strategies
Computer crimes involve illegal acts utilizing computer systems, leading to various consequences. This lecture covers the types of computer system attacks, motives behind computer crimes, costs, prevention strategies, and reflection on the discussed topics. It emphasizes the increasing scope of comp
1 views • 20 slides
The Importance of Social Protection and the African Union in Africa
Social protection is recognized as a fundamental human right, and efforts within the African Union have been made to promote social protection programs to combat poverty in Africa. The growth of social protection initiatives since the Ouagadougou declaration of 2004 has led to increased awareness an
0 views • 12 slides
Importance of Fall Protection Systems in Workplace Safety
Fall protection systems play a crucial role in preventing injuries and fatalities caused by falls at the workplace. Understanding the anatomy of a fall, statistics on fall-related incidents, and the various philosophies of fall protection can help companies plan and implement effective fall protecti
0 views • 50 slides
Improving Consumer Protection in Ghana: Insights from the Sixth Annual African Dialogue Consumer Protection Conference
The Sixth Annual African Dialogue Consumer Protection Conference held in Lilongwe, Malawi in September 2014 shed light on the challenges faced by Ghana's consumer protection policies. Irene Aborchie-Nyahe, a legal consultant, highlighted the gaps in Ghana's legislative framework, lack of effective i
0 views • 14 slides
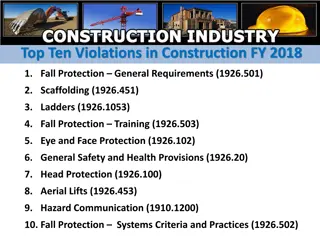
Top Ten Construction Violations FY 2018 Overview
The top ten violations in construction for fiscal year 2018 are related to fall protection, scaffolding, ladders, safety training, eye and face protection, general safety provisions, head protection, aerial lifts, hazard communication, and fall protection systems criteria and practices. The violatio
0 views • 11 slides
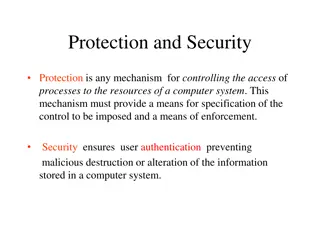
Understanding Computer System Protection and Security
Mechanisms like protection and security ensure controlled access to a computer system's resources and prevent malicious activities. Protection involves defining access control levels through models, policies, and mechanisms. Security focuses on user authentication to safeguard stored information. Di
0 views • 25 slides
Understanding Carnegie Mellon's Protection and Security Concepts
Carnegie Mellon University emphasizes the importance of protection and security in operating systems. Protection involves preventing unauthorized access by users, while security focuses on external threats and authenticating system users. The goals of protection include preventing access violations
0 views • 37 slides
Overview of Computer Science at Al Mustaqbal University College of Dentistry
Al Mustaqbal University College of Dentistry offers courses in computer science, covering topics like data reception, processing, storage, and output. The curriculum includes the study of computers as electronic devices, data and information, computer features, operating systems like Windows, and ta
0 views • 10 slides
Understanding Data Protection Regulations and Definitions
Learn about the roles of Data Protection Officers (DPOs), the Data Protection Act (DPA) of 2004, key elements of the act, definitions of personal data, examples of personal data categories, and sensitive personal data classifications. Explore how the DPO enforces privacy rights and safeguards person
0 views • 33 slides
Understanding the Essence of Computer Science and Computational Thinking
Delve into the fundamentals of Computer Science and Computational Thinking through chapters discussing the nature of science, predictions in physics, and the distinction between Computer Science and Computer Information Systems. Explore the relationships between Math, Physics, and Computer Science i
0 views • 29 slides
Workshop on Data Protection: Mauritius Police Force Presentation
The workshop on data protection by Mrs. D. Madhub, Data Protection Commissioner, held on May 15, 2019, focused on the Data Protection Act, the Data Protection Office, definitions, functions, powers, and obligations related to data protection, covering areas such as processing of personal data and ri
0 views • 46 slides