Privacy Breach Management Guide by Health PEI
Understanding, Preventing, and Managing Privacy Breaches in Healthcare: Learn about what constitutes a privacy breach, how to prevent breaches, steps to determine and manage breaches effectively, including containment, investigation, and notification processes.
0 views • 10 slides
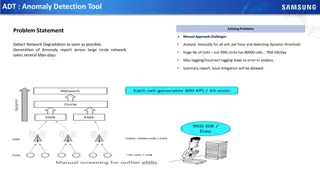
Automated Anomaly Detection Tool for Network Performance Optimization
Anomaly Detection Tool (ADT) aims to automate the detection of network degradation in a mobile communications network, reducing the time and effort required significantly. By utilizing statistical and machine learning models, ADT can generate anomaly reports efficiently across a large circle network
8 views • 7 slides
Drone Detection Using mmWave Radar for Effective Surveillance
Utilizing mmWave radar technology for drone detection offers solutions to concerns such as surveillance, drug smuggling, hostile intent, and invasion of privacy. The compact and cost-effective mmWave radar systems enable efficient detection and classification of drones, including those with minimal
0 views • 8 slides
Cyber Data Breach Review_ A Comprehensive Insight with LDM Global in the USA
In today's digital landscape, cyber data breaches pose significant threats to organizations of all sizes. A cyber data breach can result in severe financial losses, reputational damage, and legal ramifications. To navigate these challenges effectively, companies turn to expert services like those pr
1 views • 13 slides
Data Breach Exercise: Responding to a School District Breach
This tabletop exercise simulates a data breach within a school district, putting participants in critical decision-making roles to react and respond effectively. Recommendations include anticipating roles needed, preparing for the unexpected, and considering communication strategies. The background
1 views • 31 slides
Postsecondary Data Breach Exercise: Prepare for the Unexpected!
This tabletop exercise simulates a data breach scenario within a complex organization, engaging participants to make critical decisions and respond effectively. Teams will work together to uncover the extent of the breach and devise a response plan. Consider various roles needed in your organization
0 views • 31 slides
Machine Learning Techniques for Intrusion Detection Systems
An Intrusion Detection System (IDS) is crucial for defending computer systems against attacks, with machine learning playing a key role in anomaly and misuse detection approaches. The 1998/1999 DARPA Intrusion Set and Anomaly Detection Systems are explored, alongside popular machine learning classif
0 views • 36 slides
Understanding the Domino's Data Breach Incident and Its Implications
The recent data breach at Domino's India has raised concerns over consumer data protection. With personal information of millions compromised, the need for a uniform Data Protection Law is emphasized. Users are advised to take precautions, while the accountability of companies under existing regulat
0 views • 9 slides
NC22Plex STR Detection Kit: Advanced 5-Color Fluorescence Detection System
Explore the cutting-edge NC22Plex STR Detection Kit from Jiangsu Superbio Biomedical, offering a 5-color fluorescence detection system suitable for multiple applications. Enhance your research capabilities with this innovative product designed for precision and efficiency.
0 views • 20 slides
Contempt in the Family Jurisdiction with Respect to Breach of Orders
The concept of contempt in the family jurisdiction regarding the breach of court orders other than those for financial relief is crucial for upholding the due administration of justice. Courts have the authority to punish for contempt to safeguard their processes and ensure compliance with their ord
0 views • 17 slides
Automated Melanoma Detection Using Convolutional Neural Network
Melanoma, a type of skin cancer, can be life-threatening if not diagnosed early. This study presented at the IEEE EMBC conference focuses on using a convolutional neural network for automated detection of melanoma lesions in clinical images. The importance of early detection is highlighted, as exper
0 views • 34 slides
Essential Steps for Personal Data Breach Management
Detect, identify, and respond effectively to personal data breaches by containing the breach, assessing risks, notifying relevant authorities and affected individuals, and implementing measures to prevent future occurrences. Debunk common myths surrounding breach reporting and focus on mitigating ne
0 views • 5 slides
Colorimetric Detection of Hydrogen Peroxide Using Magnetic Rod-Based Metal-Organic Framework Composites
Nanomaterials, particularly magnetic rod-based metal-organic frameworks composites, are gaining attention for their exceptional properties and various applications in different fields. This study by Benjamin Edem Meteku focuses on using these composites for colorimetric detection of hydrogen peroxid
0 views • 16 slides
Understanding Breach of Confidence and Privacy Rights in English Law
English law does not provide a specific right to privacy, but breach of confidence laws offer protection against unauthorized disclosure of private information. While there is no overarching invasion of privacy tort, legal controls exist to balance freedom of expression with respect for individual p
0 views • 18 slides
Understanding Professional Duties in Accountancy
This informative content discusses various aspects of professional duties in accountancy, such as negligence, breach of duty of care, causation, asset valuation, and ethics. It covers topics like duty of care, foreseeability test, breach of duty standards, causation principles, and the accountants'
1 views • 10 slides
Can You Afford a Data Breach? Understanding the Risks and Consequences
Explore the potential dangers and implications of a data breach through insightful presentations and visuals by Laura Middleton and James Hayward. Learn about the value of personal data, human errors, and organizational measures to mitigate risks. Stay informed and subscribe to the e-newsletter for
0 views • 10 slides
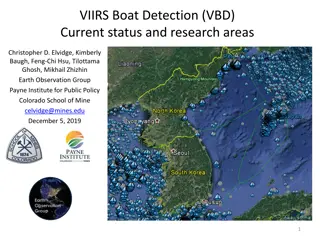
VIIRS Boat Detection (VBD) Research Overview
The Visible Infrared Imaging Radiometer Suite (VIIRS) program, a joint effort between NASA and NOAA, focuses on weather prediction and boat detection using low light imaging data collected at night. The VIIRS system provides global coverage with sensitive instruments and efficient data flow processe
1 views • 13 slides
Effective Method to Protect Web Servers Against Breach Attacks
Abdusamatov Somon presents an effective method called HTB to protect web servers against breach attacks, focusing on secure computation and mitigation. The research addresses side-channel attacks based on compression and the CRIME BREACH issue, providing insights into implementing the breach attack
1 views • 13 slides
Real-Time Cough and Sneeze Detection Project Overview
This project focuses on real-time cough and sneeze detection for assessing disease likelihood and individual well-being. Deep learning, particularly CNN and CRNN models, is utilized for efficient detection and classification. The team conducted a literature survey on keyword spotting techniques and
1 views • 15 slides
Stop Hidden Water Damage: Your Ultimate Guide to Leak Detection in San Diego
Learn how San Diego leak detection services can help protect your home from water damage. Discover the signs of leaks, advanced detection technologies, and tips to prevent costly repairs. Stay ahead with proactive slab leak detection and expert solut
0 views • 6 slides
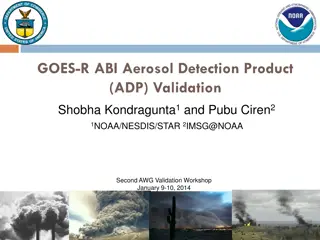
GOES-R ABI Aerosol Detection Product Validation Summary
The GOES-R ABI Aerosol Detection Product (ADP) Validation was conducted by Shobha Kondragunta and Pubu Ciren at the NOAA/NESDIS/STAR workshop in January 2014. The validation process involved testing and validating the ADP product using proxy data at various resolutions for detecting smoke, dust, and
1 views • 21 slides
Real-Time Cough and Sneeze Detection Using Deep Learning Models
Detection of coughs and sneezes plays a crucial role in assessing an individual's health condition. This project by Group 71 focuses on real-time detection using deep learning techniques to analyze audio data from various datasets. The use of deep learning models like CNN and CRNN showcases improved
0 views • 15 slides
Development of Satellite Passive Microwave Snowfall Detection Algorithm
This study focuses on the development of a satellite passive microwave snowfall detection algorithm, highlighting the challenges in accurately determining snowfall using satellite instruments. The algorithm uses data from AMSU/MHS, ATMS, and SSMIS sensors to generate snowfall rate estimates, overcom
0 views • 20 slides
Privacy Breach Response and Reporting under the Health Information Act
Understanding privacy breaches under the Health Information Act (HIA) is crucial for organizations dealing with health data. This document outlines what constitutes a breach, mandatory notification requirements, factors to consider in determining risk of harm, and potential offences and penalties fo
0 views • 21 slides
Data Error Detection Techniques Overview
Two-dimensional parity and Cyclic Redundancy Check (CRC) are data error detection methods used to ensure data integrity during transmission. Two-dimensional parity involves organizing bits in a table to calculate parity bits for data units and columns, while CRC appends a string of zeros to the data
0 views • 20 slides
Understanding Alabama Data Breach Notification Act for County Governments
Alabama's Data Breach Notification Act requires all county governments and related entities to comply with specific security measures to protect sensitive information of residents. The law mandates prompt investigation and notification in case of a breach, defining what constitutes a breach and sens
1 views • 36 slides
Legal Case Study: Compensation for Breach of Promise
In this legal case study, we examine different scenarios involving breach of promise and the resulting compensation. The study covers promises kept, losses caused by breaches, and the corresponding awards for individuals involved. Various situations are analyzed, from promises kept without mitigatio
0 views • 6 slides
NHS Sussex Conflicts of Interest Breach Register Summary May 2024
NHS Sussex manages conflicts of interest breaches by recording and publishing them on their website. Breaches are documented with details of the nature of the breach and actions taken. In May 2024, no breaches were reported. Previous months had breaches due to late declarations of interest. Staff we
0 views • 5 slides
Overview of GRANDproto Project Workshop on Autonomous Radio Detection
GRANDproto project workshop held in May 2017 focused on improving autonomous radio detection efficiency for the detection of extensive air showers (EAS). Issues such as detector stability and background rates were discussed, with the goal of establishing radio detection as a reliable method for EAS
1 views • 14 slides
Timely Leak Detection San Diego | Professional Leak Detection Services
Protect your home with expert leak detection services in San Diego. Avoid costly water damage and health risks with timely detection of hidden leaks. Schedule today!\n\nKnow more: \/\/ \/san-diego-slab-leak-detection\/
0 views • 7 slides
How Professional Leak Detection Can Save Your San Diego Home | Leak Detection Sa
Protect your home from costly damage with professional leak detection in San Diego. Learn about expert services like slab leak detection, non-invasive testing, and more. Save money and prevent water damage with top San Diego leak detection services.\
0 views • 8 slides
EPA Compliance Basics: Tank Leak Detection and Monitoring Methods
Learn about EPA requirements for tank leak detection, release detection methods, and compliance methods for monitoring tank systems. Understand the importance of implementing effective leak detection systems to prevent contamination and comply with federal regulations, including Automatic Tank Gaugi
0 views • 18 slides
Data Breach Occurrence at Illinois Department of Transportation
A data breach at the Illinois Department of Transportation exposed social security numbers and employee identification numbers of all current and former employees. The breach was discovered on April 14, 2022, after being visible from April 6, 2022. The breached file was located on an internal IDOT w
0 views • 11 slides
Understanding Intrusion Detection Systems (IDS) and Snort in Network Security
Intrusion Detection Systems (IDS) play a crucial role in network security by analyzing traffic patterns and detecting anomalous behavior to send alerts. This summary covers the basics of IDS, differences between IDS and IPS, types of IDS (host-based and network-based), and the capabilities of Snort,
0 views • 34 slides
Understanding Anomaly Detection in Data Mining
Anomaly detection is a crucial aspect of data mining, involving the identification of data points significantly different from the rest. This process is essential in various fields, as anomalies can indicate important insights or errors in the data. The content covers the characteristics of anomaly
0 views • 50 slides
Legal Dispute Between Walker & Co. and Harrison: Contract Breach Analysis
In the legal dispute between Walker & Co. and Harrison regarding a breached contract over a billboard, Harrison claimed that Walker failed to maintain the sign, justifying contract termination. However, Walker's actions to remedy the breach and the criteria for material breach were evaluated by the
0 views • 9 slides
Understanding Breach of Confidence and Privacy Rights in Legal Context
The legal landscape regarding breach of confidence and privacy rights, especially in the context of English law and the European Convention on Human Rights, is complex and ever-evolving. While English law traditionally does not recognize a right to privacy, recent developments and landmark cases hav
0 views • 18 slides
Cyber Data Breach Review_ Safeguarding Firms in the Digital Age
This blog explores the critical role of Cyber Data Breach Review in protecting legal firms from digital threats. It highlights how LDM Global's approach, grounded in their core values\u2014Team, Results, Accountability, and Quality\u2014helps firms n
1 views • 10 slides
State of Idaho Data Breach & Credit Monitoring Services Overview
This document outlines the State of Idaho's Division of Purchasing's procurement of data breach and credit monitoring services through NASPO ValuePoint. The purpose, scope of services, sourcing team details, evaluation criteria, and RFP process are detailed, emphasizing the benefits of having pre-es
0 views • 33 slides
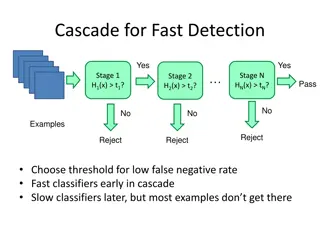
Object Detection Techniques Overview
Object detection techniques employ cascades, Haar-like features, integral images, feature selection with Adaboost, and statistical modeling for efficient and accurate detection. The Viola-Jones algorithm, Dalal-Triggs method, deformable models, and deep learning approaches are prominent in this fiel
0 views • 21 slides