Automated Anomaly Detection Tool for Network Performance Optimization
Anomaly Detection Tool (ADT) aims to automate the detection of network degradation in a mobile communications network, reducing the time and effort required significantly. By utilizing statistical and machine learning models, ADT can generate anomaly reports efficiently across a large circle network
8 views • 7 slides
Drone Detection Using mmWave Radar for Effective Surveillance
Utilizing mmWave radar technology for drone detection offers solutions to concerns such as surveillance, drug smuggling, hostile intent, and invasion of privacy. The compact and cost-effective mmWave radar systems enable efficient detection and classification of drones, including those with minimal
0 views • 8 slides
Machine Learning Techniques for Intrusion Detection Systems
An Intrusion Detection System (IDS) is crucial for defending computer systems against attacks, with machine learning playing a key role in anomaly and misuse detection approaches. The 1998/1999 DARPA Intrusion Set and Anomaly Detection Systems are explored, alongside popular machine learning classif
0 views • 36 slides
NC22Plex STR Detection Kit: Advanced 5-Color Fluorescence Detection System
Explore the cutting-edge NC22Plex STR Detection Kit from Jiangsu Superbio Biomedical, offering a 5-color fluorescence detection system suitable for multiple applications. Enhance your research capabilities with this innovative product designed for precision and efficiency.
0 views • 20 slides
Automated Melanoma Detection Using Convolutional Neural Network
Melanoma, a type of skin cancer, can be life-threatening if not diagnosed early. This study presented at the IEEE EMBC conference focuses on using a convolutional neural network for automated detection of melanoma lesions in clinical images. The importance of early detection is highlighted, as exper
0 views • 34 slides
Understanding Outlier Analysis in Data Mining
Outliers are data objects that deviate significantly from normal data, providing valuable insights in various applications like fraud detection and customer segmentation. Types of outliers include global, contextual, and collective outliers, each serving distinct purposes in anomaly detection. Chall
0 views • 44 slides
Efficient Anomaly Detection for Batch Systems Using Machine Learning
Explore a lightning talk session focusing on using Collectd metrics and job data in HTCondor batch systems for anomaly detection. Challenges with raw historical data are addressed through data collection, manipulation, and application of anomaly detection techniques using ML. Various algorithms such
0 views • 14 slides
Colorimetric Detection of Hydrogen Peroxide Using Magnetic Rod-Based Metal-Organic Framework Composites
Nanomaterials, particularly magnetic rod-based metal-organic frameworks composites, are gaining attention for their exceptional properties and various applications in different fields. This study by Benjamin Edem Meteku focuses on using these composites for colorimetric detection of hydrogen peroxid
0 views • 16 slides
Semantics-Aware Intrusion Detection for Industrial Control Systems by Mer Yksel
Mer Yksel, a PhD candidate at Eindhoven University of Technology, specializes in intrusion detection and data analytics with a focus on industrial control systems. His research covers targeted attacks, threat modeling, protection of ICS networks, and innovative anomaly-based approaches for cybersecu
0 views • 31 slides
An Overview of Evading Anomaly Detection using Variance Injection Attacks on PCA
This presentation discusses evading anomaly detection through variance injection attacks on Principal Component Analysis (PCA) in the context of security. It covers the background of machine learning and PCA, related work, motivation, main ideas, evaluation, conclusion, and future work. The content
1 views • 19 slides
VIIRS Boat Detection (VBD) Research Overview
The Visible Infrared Imaging Radiometer Suite (VIIRS) program, a joint effort between NASA and NOAA, focuses on weather prediction and boat detection using low light imaging data collected at night. The VIIRS system provides global coverage with sensitive instruments and efficient data flow processe
1 views • 13 slides
Real-Time Cough and Sneeze Detection Project Overview
This project focuses on real-time cough and sneeze detection for assessing disease likelihood and individual well-being. Deep learning, particularly CNN and CRNN models, is utilized for efficient detection and classification. The team conducted a literature survey on keyword spotting techniques and
1 views • 15 slides
Stop Hidden Water Damage: Your Ultimate Guide to Leak Detection in San Diego
Learn how San Diego leak detection services can help protect your home from water damage. Discover the signs of leaks, advanced detection technologies, and tips to prevent costly repairs. Stay ahead with proactive slab leak detection and expert solut
0 views • 6 slides
Understanding Enamel Pearl Anomaly in Dentistry
Enamel Pearl is a developmental anomaly where small nodules of enamel form below the cemento enamel junction, mainly on permanent teeth. This anomaly, detected radiographically, can lead to bacterial accumulation, periodontal issues, and inflammation if left untreated. Dental hygienists play a cruci
0 views • 8 slides
Wavelet-based Scaleograms and CNN for Anomaly Detection in Nuclear Reactors
This study utilizes wavelet-based scaleograms and a convolutional neural network (CNN) for anomaly detection in nuclear reactors. By analyzing neutron flux signals from in-core and ex-core sensors, the proposed methodology aims to identify perturbations such as fuel assembly vibrations, synchronized
3 views • 11 slides
GOES-R ABI Aerosol Detection Product Validation Summary
The GOES-R ABI Aerosol Detection Product (ADP) Validation was conducted by Shobha Kondragunta and Pubu Ciren at the NOAA/NESDIS/STAR workshop in January 2014. The validation process involved testing and validating the ADP product using proxy data at various resolutions for detecting smoke, dust, and
1 views • 21 slides
Real-Time Cough and Sneeze Detection Using Deep Learning Models
Detection of coughs and sneezes plays a crucial role in assessing an individual's health condition. This project by Group 71 focuses on real-time detection using deep learning techniques to analyze audio data from various datasets. The use of deep learning models like CNN and CRNN showcases improved
0 views • 15 slides
Lessons Learned from On-Orbit Anomaly Research
The On-Orbit Anomaly Research workshop held at the NASA IV&V Facility in 2013 focused on studying post-launch anomalies and enhancing IV&V processes. The presentations highlighted common themes like Pseudo-Software Command Scripts, Software and Hardware Interface issues, Communication Protocols, and
0 views • 55 slides
On-Orbit Anomaly Research at NASA: Causes and Solutions
On-Orbit Anomaly Research (OOAR) at NASA's IV&V Facility involves studying mishaps related to space missions, identifying anomalies, and improving IV&V processes. The research delves into the causes of anomalies, such as operating system faults, and proximate causes like software deficiencies. Detai
0 views • 20 slides
Mitigating IoT-Based Cyberattacks on the Smart Grid
Exploring the challenges of cybersecurity in the Smart Grid, focusing on IoT-triggered threats and security challenges. Discusses the need for reliable information access, confidentiality, and privacy protection in the context of evolving attack vectors. Highlights related works in intrusion detecti
0 views • 25 slides
Overview of GRANDproto Project Workshop on Autonomous Radio Detection
GRANDproto project workshop held in May 2017 focused on improving autonomous radio detection efficiency for the detection of extensive air showers (EAS). Issues such as detector stability and background rates were discussed, with the goal of establishing radio detection as a reliable method for EAS
1 views • 14 slides
Timely Leak Detection San Diego | Professional Leak Detection Services
Protect your home with expert leak detection services in San Diego. Avoid costly water damage and health risks with timely detection of hidden leaks. Schedule today!\n\nKnow more: \/\/ \/san-diego-slab-leak-detection\/
0 views • 7 slides
How Professional Leak Detection Can Save Your San Diego Home | Leak Detection Sa
Protect your home from costly damage with professional leak detection in San Diego. Learn about expert services like slab leak detection, non-invasive testing, and more. Save money and prevent water damage with top San Diego leak detection services.\
0 views • 8 slides
Exploring the Potential of Big Data Analytics in Transaction Banking
Big Data Analytics (BDA) offers valuable insights in transaction banking through varied data sources and methods like Supervised, Unsupervised, and Reinforcement learning. Use cases include anomaly detection, fraud detection, default prediction, forecasting, and sentiment analysis. Discussions also
0 views • 8 slides
Understanding Intrusion Detection Systems (IDS) and Snort in Network Security
Intrusion Detection Systems (IDS) play a crucial role in network security by analyzing traffic patterns and detecting anomalous behavior to send alerts. This summary covers the basics of IDS, differences between IDS and IPS, types of IDS (host-based and network-based), and the capabilities of Snort,
0 views • 34 slides
Anomaly-Based Network Intrusion Detection in Cyber Security
An overview of the importance of network intrusion detection, its relevance to anomaly detection and data mining, the concept of anomaly-based network intrusion detection, and the economic impact of cybercrime. The content also touches on different types of computer attacks and references related to
0 views • 32 slides
Understanding Intrusion Detection and Prevention Systems
Learn about the components and implementation options of intrusion detection and prevention systems, as well as the goals and role of an IDPS in network defense. Discover the capabilities of IDPS, such as assessing network traffic, detecting unauthorized access, and responding to threats. Explore an
0 views • 57 slides
Sketch Resource Allocation for Software-defined Measurement in Network Management
Measurement plays a crucial role in network management, especially for tasks like heavy hitter detection and anomaly detection. The focus is on sketch-based measurement, using innovative techniques like Count-Min Sketch to approximate specific queries efficiently. Challenges include limited resource
0 views • 31 slides
LD-Sketch: Distributed Sketching Design for Anomaly Detection in Network Data Streams
LD-Sketch is a novel distributed sketching design for accurate and scalable anomaly detection in network data streams, addressing challenges such as tracking heavy keys in real-time across a vast key space. By combining high accuracy, speed, and low space complexity, LD-Sketch enables efficient heav
0 views • 25 slides
Data Plane Heavy Hitter Detection and Switches: A Comprehensive Overview
In this comprehensive guide, explore the concepts of heavy-hitter detection entirely in the data plane, the significance of detecting heavy hitters, emerging programmable switches, existing techniques, and constraints faced in processing heavy flows. Discover the motivation behind the Space-Saving A
0 views • 33 slides
Understanding Anomaly Detection in Data Mining
Anomaly detection is a crucial aspect of data mining, involving the identification of data points significantly different from the rest. This process is essential in various fields, as anomalies can indicate important insights or errors in the data. The content covers the characteristics of anomaly
0 views • 50 slides
Anomaly Detection in Data Mining: Understanding Outliers and Importance
Anomaly detection is crucial in data mining to identify data points significantly different from the norm. This technique helps in recognizing rare occurrences like ozone depletion anomalies. Understanding the distinction between noise and anomalies is key, as anomalies can provide valuable insights
0 views • 35 slides
Anomaly Detection Using Process Behavior Charts
Explore the philosophy behind understanding variation and key principles in anomaly detection using process behavior charts. Learn about preparing data, creating SAS charts, running tests for special causes, and executing a plan for anomaly detection and reporting processes. The material draws heavi
0 views • 41 slides
Understanding Intrusion Detection and Security Tools
Explore the world of intrusion detection, access control, and security tools through terminology, systems, classifications, and methods. Learn about intrusion detection systems (IDSs), their terminology, alert systems, classification methods like signature-based and statistical anomaly-based approac
0 views • 39 slides
Study on Ionospheric Perturbation Due to Solar and Geomagnetic Activity in Odessa Magnetic Anomaly
Research conducted in the area of the Odessa magnetic anomaly investigates ionospheric perturbations caused by solar and geomagnetic activity. The study utilizes radio astronomical and magnetometric observations from various observatories, highlighting the significance of the geomagnetic anomaly nea
0 views • 18 slides
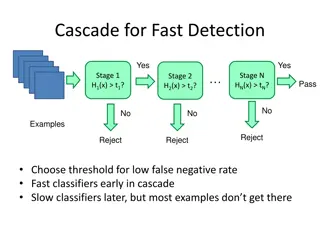
Object Detection Techniques Overview
Object detection techniques employ cascades, Haar-like features, integral images, feature selection with Adaboost, and statistical modeling for efficient and accurate detection. The Viola-Jones algorithm, Dalal-Triggs method, deformable models, and deep learning approaches are prominent in this fiel
0 views • 21 slides
Detecting Performance Anomalies in Cellular Networks via Regression Analysis
The study focuses on detecting performance anomalies in cellular networks using regression analysis. It addresses challenges such as labeling, rare anomalies, and correlated factors. The tool CellPAD is introduced for anomaly detection, supporting various prediction algorithms and offering insights
0 views • 19 slides
Solving Cosmic Gamma Background Anomaly: Ekaterina Shlepkina's Research Insights
Explore the quest to find a solution for the cosmic gamma background anomaly in cosmic rays through Ekaterina Shlepkina's research presented at the XXII International Workshop. Learn about the investigations into cosmic rays fluxes, antiparticle studies, and possible interaction types of Dark Matter
1 views • 19 slides
New Generation Network Security System Evolution and Implementation
The presentation outlines the evolution of network security systems, focusing on the transition from traditional firewalls to next-generation systems like intrusion detection systems. It highlights the limitations of current systems in detecting internal threats and the need for advanced solutions t
0 views • 9 slides
Anomaly Detection Methods for Alternative Data in CPI Statistics
Anomaly detection is crucial in ensuring the accuracy of Consumer Prices Indices (CPI). This article explores various anomaly detection methods, including distance-based, density-based, Gaussian mixture modeling, principle component analysis, and entropy-based approaches. Each method has its advanta
0 views • 24 slides