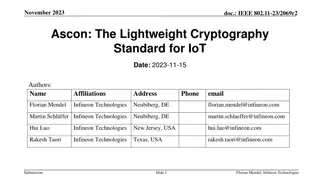
Ascon: The Lightweight Cryptography Standard for IoT
The November 2023 document IEEE 802.11-23/2069r2 discusses the importance of secure data storage and communication in IoT devices due to the increasing number of connected devices and potential security threats. It introduces Ascon as a lightweight cryptography standard selected by NIST for protecti
0 views • 26 slides
Understanding SHA-256 Algorithm and History
SHA-256 is a secure hashing algorithm that produces 256-bit hash values and is more secure than MD5, SHA-0, and SHA-1 due to fewer collisions. Created in 2001 by the NSA, it is widely used in various applications like cryptocurrency, SSL certificates, and blockchain. This summary provides insights i
0 views • 17 slides
Start Your Healthcare Career_ CNA Online Course by CNA
Open a new chapter in your life, and work towards filling a vital niche in the growing healthcare sector. You should check a course like the CNA online course provided by CNA.School if you are in need of such a class. This Course will equip you with all imaginable knowledge and practical skills that
1 views • 3 slides
Access Free CNA Classes Online and Start Your Career
Do you want to make a leap towards the healthcare industry but do not want to spend a lot of money? CNA.School provides free CNA classes online for everyone interested in learning more. These courses offer an accessible and affordable means of receiving the training and passing the tests required to
16 views • 8 slides
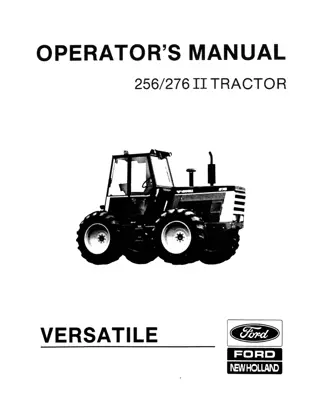
Versatile 256 276 II Tractor Operator’s Manual Instant Download (Publication No.42025620)
Please open the website below to get the complete manual\n\n\/\/
0 views • 22 slides
Versatile 256 276 Tractors Operator’s Manual Instant Download (Publication No.42025621)
Please open the website below to get the complete manual\n\n\/\/
0 views • 20 slides
Versatile 2360 Loader (Serial Number 434100 and above) for 256 276 276II and 9030 Tractors Operator’s Manual Instant Download (Publication No.43236014)
Please open the website below to get the complete manual\n\n\/\/
0 views • 11 slides
Understanding AES Encryption Algorithm and Its Implementation
Learn about the Advanced Encryption Standard (AES) algorithm - a NSA-approved NIST standard encryption method. Explore how AES works, its key rounds, SubBytes, ShiftRows, MixColumns operations, and its optimization for embedded systems and small memory devices. Discover the importance of secure cryp
0 views • 14 slides
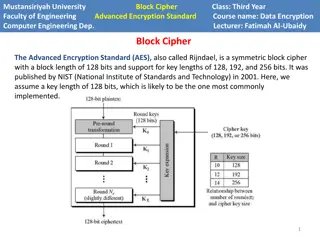
Understanding AES Encryption in Computer Engineering
Advanced Encryption Standard (AES) is a powerful symmetric block cipher used in computer engineering for data encryption. Developed by NIST, AES supports key lengths of 128, 192, and 256 bits. The algorithm operates on a state array and consists of encryption phases like initial round, main rounds,
2 views • 8 slides
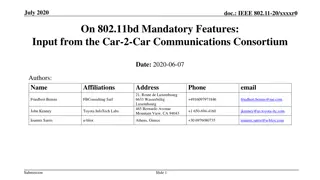
Proposal for New 802.11bd 20MHz Mode for Enhanced ITS Interoperability
The document discusses the necessity of a new 802.11bd 20MHz mode for improved interoperability within Intelligent Transportation Systems (ITS) due to limitations with current Wi-Fi channels and the scope of 256-QAM modulation. It presents proposals approved by the Car-2-Car Communications Consortiu
0 views • 8 slides
Understanding Character Sets in Computer Science
Alphanumeric characters, special symbols, and control characters play crucial roles in representing data through character sets like ASCII and Unicode in computer science. ASCII, with its 7-bit binary codes, represents 128 characters, while Extended ASCII allows for 256 characters. Unicode covers a
1 views • 12 slides
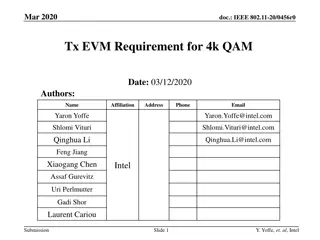
IEEE 802.11-20/0456r0: Transmission EVM Requirements for 4k QAM
The document discusses the tradeoff between error vector magnitude (EVM) and transmission power in the context of 4k QAM modulation. It explores the EVM requirements for 4k QAM and addresses issues such as channel estimation errors, modulation and coding scheme (MCS) parameters, and degradation with
0 views • 11 slides
Understanding Performance Analysis of Digital Modulation Techniques
Explore the realm of digital modulation techniques such as ASK, FSK, PSK, QPSK, QAM, and more. Learn about bandwidth efficiency, baud rates, minimum bandwidth, and how to calculate them. Discover the importance of M-ary modulation and how it impacts data transmission rates and bandwidth requirements
4 views • 18 slides
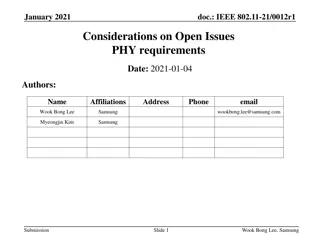
IEEE 802.11-21/0012r1 Considerations on Open Issues in PHY Requirements
In the January 2021 document IEEE 802.11-21/0012r1, discussions were held on open issues related to PHY requirements, including LO requirements for 320 MHz transmission, EVM requirements for 1024 QAM and BPSK-DCM-DUP, minimum sensitivity for 4K QAM and BPSK-DCM-DUP, and channel rejection levels. Sug
0 views • 12 slides
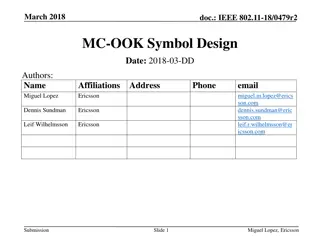
MC-OOK Symbol Design for IEEE 802.11 - March 2018
Introducing MC-OOK waveforms with low peak-to-average power ratio for IEEE 802.11, utilizing 256-QAM modulation and 4 MHz bandwidth. The design methodology involves generating time-domain waveforms, transforming to frequency domain, and proposing symbols with and without DC subcarriers. Detailed sym
0 views • 20 slides
Introduction to Quadrature Amplitude Modulation (QAM) in Digital Communication
Quadrature Amplitude Modulation (QAM) is a widely used modulation technique for transmitting data signals onto a carrier in communication systems. It offers advantages like increased efficiency by combining amplitude and phase variations, making it suitable for various radio and data delivery applic
0 views • 15 slides
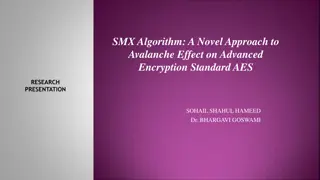
Overview of SMX Algorithm and AES Encryption Standard
The SMX Algorithm presents a fresh approach to the avalanche effect in the Advanced Encryption Standard (AES). Initially developed to overcome the limitations of the Data Encryption Standard (DES), AES boasts improved security and efficiency, supporting key lengths of 128, 192, and 256 bits. The AES
3 views • 19 slides
Powercor Industry Forum Audit Results and Trends Analysis
Audit results and trends analysis reveal that there were 256 audits completed, with 50 being re-audits. Additional resources were acquired to meet industry demand, but audit volumes in Q4 did not meet forecast. Turnaround times improved with the deployment of more auditor resources. Trends show issu
0 views • 8 slides
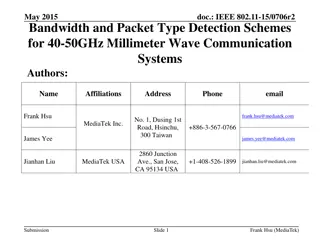
Bandwidth and Packet Type Detection Schemes for 40-50GHz Millimeter Wave Communication Systems
The document discusses bandwidth and packet type detection schemes for 40-50GHz millimeter wave communication systems in IEEE 802.11aj specifications. It proposes a preamble design for auto-detection of bandwidth and packet type to improve channel estimation and decoding efficiency. By utilizing dif
0 views • 27 slides
Highlights of ICA Journalism Studies Division Business Meeting 2014 in Seattle
Agenda highlights included discussions on upcoming elections, ways to engage members, presentation of awards, introduction of new membership categories, proposed changes to board representation, establishment of guidelines for affiliate journals, and the creation of new divisions and interest groups
0 views • 15 slides
Best Practices for Secure Password Storage - OWASP Foundation Guidelines
Learn about secure password storage techniques recommended by OWASP Foundation, including adding salt, slowing down hashing functions, using HMAC isolation, and imposing difficult verification processes on attackers. Remember to use proper encoding, avoid limiting password types or lengths unreasona
0 views • 10 slides
Understanding Interrupt Processing Sequence in X86 Processors
X86 processors have 256 software interrupts, functioning similarly to a CALL instruction. When an INT n instruction is executed, the processor follows a sequence involving pushing the flag register, clearing flags, finding the correct ISR address, and transferring CPU control. Special interrupts lik
0 views • 10 slides
Cryptographic Algorithms and Hash Collisions Overview
Explore the world of cryptographic algorithms and hash collisions. Learn about various hashing algorithms like MD5, SHA-1, SHA-256, and more. Dive into the concepts of symmetric and asymmetric key algorithms and understand the risks associated with hash collisions. Discover the implications of post-
0 views • 58 slides
Evaluation of Ed25519 Cryptography Performance in DNSSEC Validation
Edwards Curve Cryptography, specifically the Ed25519 algorithm, offers faster performance and high crypto density compared to other algorithms. This evaluation study compares key sizes, processing times, and validation support for Ed25519, ECDSA P-256, RSA-2048, and RSA-4096 in DNSSEC validation sce
0 views • 19 slides
Understanding EIGRP Network Protocol
EIGRP (Enhanced Interior Gateway Routing Protocol) is a network protocol that facilitates efficient information exchange among routers. Evolving from IGRP, EIGRP allows interoperability and can be used for IP, AppleTalk, and Novell NetWare networks. EIGRP metrics scale IGRP metrics by a factor of 25
0 views • 13 slides
IPv6 Public Policy Considerations - Addressing the Global IP Address Shortage
In light of the global shortage of IPv4 addresses, there is a pressing need for a fair policy for the allocation of remaining addresses. The rapid growth of the Internet has further increased demand for IP addresses, with IPv4 expected to run out soon. The deployment of IPv6 has become a critical is
0 views • 23 slides
Fiat Kobelco E235SR Evolution Excavator Service Repair Manual Instant Download (Print N. 604.13.256)
Please open the website below to get the complete manual\n\n\/\/
0 views • 14 slides
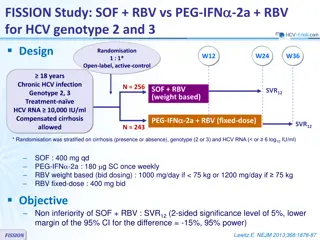
Comparison of SOF+RBV vs PEG-IFN-2a+RBV for HCV Genotype 2 and 3 Treatment
FISSION Study compared the efficacy of SOF+RBV and PEG-IFN-2a+RBV for HCV genotypes 2 and 3 in treatment-naive patients with chronic HCV infection. The study included 256 participants in the SOF+RBV group and 243 in the PEG-IFN-2a+RBV group. The primary objective was to determine the non-inferiority
0 views • 6 slides