IEEE 802.11-17/1373r1 PHY Security Overview
This document outlines the security requirements for the IEEE 802.11-17/1373r1 protocol, focusing on authentication, encryption algorithms, key management, and message integrity in both associated and unassociated states. It also addresses securing against adversaries with specified response times, focusing on Type A and Type B adversaries with varying capabilities. The proposed FRD text highlights the need for secured modes to protect against different adversary types across various wireless operations.
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
You are allowed to download the files provided on this website for personal or commercial use, subject to the condition that they are used lawfully. All files are the property of their respective owners.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.
E N D
Presentation Transcript
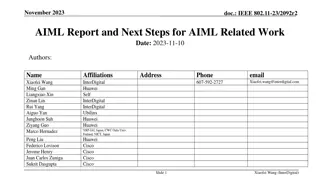
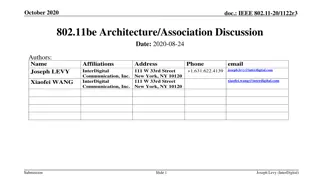
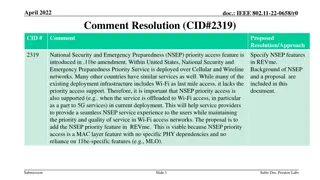
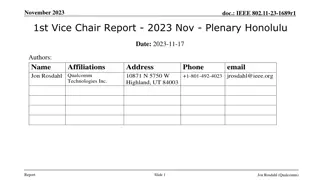
doc.: IEEE 802.11-17/1373r1 PHY Security FRD and SRD Text Date: 2017-09-06 Authors: Name SK Yong Affiliations Address Apple Inc. Phone email skyong@apple.com mingguang_xu@apple.com Mingguang Xu Apple Inc. Submission Slide 1 SK Yong and Mingguang Xu, Apple
doc.: IEEE 802.11-17/1373r1 FRD (424r6) Recap 2.1.6 Security and Privacy TGaz R35 The 11az positioning protocol shall have at least one secured mode that meets all of the following security requirements in the associated state:[Ref-11] a. Authentication - Mutual authentication of initiator and responder. b. Encryption Algorithm - The cryptographic cipher combined with various methods for encrypting the message* used in 11az-positing protocol. c. Key Management - Create, distribute and maintain the keys. d. Message Integrity - Ensures that the encrypted message* has not been tampered with. (* Message refers to frame and/or field(s) within the frame.) TGaz R36 The 11az positioning protocol shall have at least one secured mode that meets all of the following security requirements in the unassociated state:[Ref-11] a. Authentication - Mutual authentication of initiator and responder (provided there is a prior security context established). b. Encryption Algorithm - The cryptographic cipher combined with various methods for encrypting the message* used in 11az-positing protocol. c. Key Management - Create, distribute and maintain the keys. d. Message Integrity - Ensures that the encrypted message* has not been tampered with. (* Message refers to frame and/or field(s) within the frame.) Submission Slide 2 SK Yong and Mingguang Xu, Apple
doc.: IEEE 802.11-17/1373r1 FRD (424r6) Recap Cont d 2.1.6 Security and Privacy TGaz R37 The 11az protocol shall have at least one secured mode that protects against adversaries with capabilities as specified by R1 to R4 below and with the following response time.[Ref-11] a. Type A Adversary is assumed to have response time to standard-specified OTA events or scenario dependent fields of 1 msec or longer. b. Type B Adversary is assumed to have response time to known OTA events or known pre-defined fields of 1usec or longer (up to 1msec). Note: the STA capabilities is TBD (for both types of adversaries). An adversary may have at least one or more of the following capabilities and limitations: [R1] An adversary that uses commercial NIC/Sniffer; [R2] At most, the adversary may deploy/use two non-co-located Tx and Rx chains; [R3] The adversary shall be TOA and TOD capable on all received/transmitted frames; [R4] The adversary shall be able to compose and transmit any 802.11 packet or part of it. Submission Slide 3 SK Yong and Mingguang Xu, Apple
doc.: IEEE 802.11-17/1373r1 Proposed FRD Text TGaz R37: The 11az protocol shall have at least one secured mode that protects against adversaries with capabilities as specified by R1 to R4 below and with the following response time.[Ref-11] a. Type A Adversary (targeting VHT/HE/DMG/EDMG operation) is assumed to have response time to standard-specified OTA events or scenario dependent fields of 1 msec or longer. b. VHT/HE Type B Adversary is assumed to have response time to known OTA events or known pre-defined fields of 1usec or longer (up to 1msec). c. DMG/EDMG Type B Adversary is assumed to have response time to known OTA events or known pre-defined fields of 10nsec or longer (up to 1msec). Submission Slide 4 SK Yong and Mingguang Xu, Apple
doc.: IEEE 802.11-17/1373r1 SFD (0462r5) Recap 6. Security [May 2017] (1) The security setup to be negotiated in a separate optional step prior to the 802.11az protocol parameter negotiation a) Note that in lieu of security negotiation, keys derived using an out-of- band mechanism may be used to secure the exchange between the initiator and the responder [May 2017] (2) The REVmc, HEz, and VHTz FTM modes, the fields over which range measurements are performed shall be protected against a Type B adversary attack [May 2017] Submission Slide 5 SK Yong and Mingguang Xu, Apple
doc.: IEEE 802.11-17/1373r1 Proposed SFD Text (2)The REVmc, HEz and VHTz FTM modes, the fields over which range measurements are performed shall be protected against a VHT/HE Type B adversary attack (TGaz R37) (3)The DMGz and EDMGz FTM modes, the fields over which range measurements are performed shall be protected against a DMG/EDMG Type B adversary attack (TGaz R37) (4) In the PHY Security mode (VHTz, HEz, DMGz, EDMGz), the field used for channel/ToA measurement shall not include any form of repetition in time domain or structure that is predictable Submission Slide 6 SK Yong and Mingguang Xu, Apple
doc.: IEEE 802.11-17/1373r1 Straw Poll 1 Do you support to add the proposed text as shown in slide 4 to the FRD? Result: Y: 14 N: 1 A: 4 Submission Slide 7 SK Yong and Mingguang Xu, Apple
doc.: IEEE 802.11-17/1373r1 Straw Poll 2 Do you support to add the proposed text as shown in slide 6 to the SFD? Result: Y: 11 N: 1 A:7 Submission Slide 8 SK Yong and Mingguang Xu, Apple
doc.: IEEE 802.11-17/1373r1 Motion Move to incorporate text as shown in slide 4 to the FRD Result: Y: N: A: Submission Slide 9 SK Yong and Mingguang Xu, Apple
doc.: IEEE 802.11-17/1373r1 Motion Move to incorporate text as shown in slide 6 to the SFD Result: Y: N: A: Submission Slide 10 SK Yong and Mingguang Xu, Apple