High School Civil Rights Movement Escape Room
Engage high school students in an interactive escape room activity focused on key events and figures of the Civil Rights Movement. From segregation to landmark court cases and iconic protests, students will delve into the history through reading materials, questions, ciphers, and sorting tasks. This
2 views • 38 slides
Graph Machine Learning Overview: Traditional ML to Graph Neural Networks
Explore the evolution of Machine Learning in Graphs, from traditional ML tasks to advanced Graph Neural Networks (GNNs). Discover key concepts like feature engineering, tools like PyG, and types of ML tasks in graphs. Uncover insights into node-level, graph-level, and community-level predictions, an
3 views • 87 slides
Engaging Paper-Based Problem Solving for Computational Thinking Skills
Implementing paper-based problem-solving activities using puzzles, riddles, and pattern recognition can effectively introduce computational thinking without the need for complex technology or terminology. Through real-life scenarios like transporting a fox, chicken, and corn across a river or encodi
0 views • 23 slides
Introduction to RSA Cryptography and Public Key Encryption
Explore the fundamentals of RSA cryptography and public key encryption, including shift ciphers and affine ciphers. Learn how public key encryption solves the challenges of implementing secure communication on a large scale. Discover the key components of RSA, its development history, and the mathem
2 views • 37 slides
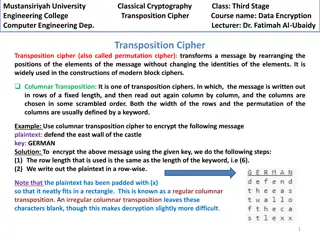
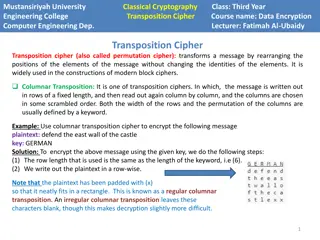
Columnar Transposition Cipher: Data Encryption Techniques at Mustansiriyah University Engineering College
Transposition ciphers, particularly the columnar transposition technique, are explored in the course "Data Encryption" at Mustansiriyah University Engineering College. The cipher involves rearranging message elements without changing their identities, making it crucial in modern block cipher designs
0 views • 4 slides
Understanding REST API Basics and Traditional Web Applications
Explore the fundamental concepts of REST API and traditional web applications, including client-server interactions, the role of HTML and HTTP, drawbacks of traditional approaches, the significance of APIs, different types of web APIs, and the principles underlying Representational State Transfer (R
3 views • 21 slides
Overview of Cryptography Techniques and Algorithms
Exploring the diverse realm of cryptography, this chapter delves into both nonmathematical and mathematical encryption methods. It covers substitution and transposition ciphers, steganography, hybrid systems, hashing, symmetric algorithms like DES and AES, as well as asymmetric algorithms utilizing
7 views • 21 slides
Chad Workshop on Integrating Traditional and Complementary Medicinal Practices
Chad held a workshop on integrating traditional and complementary medicinal practices into the health system, emphasizing the importance of traditional medicine alongside modern medical care. The presentation highlighted the country's population, reliance on traditional medicine, legal frameworks, a
0 views • 12 slides
Approaches to Study Comparative Politics: Traditional vs. Modern Perspectives
This chapter discusses the importance of approaches in the study of comparative politics, categorizing them into traditional and modern perspectives. Traditional approaches include philosophical, historical, and traditional institutional approaches, highlighting their strengths and limitations. Mode
0 views • 7 slides
Integration of Traditional and Complementary Medicine in Uganda's National Health System
Dr. Sekagya H. Yahaya discusses the integration of traditional and complementary medicine in Uganda's health system, highlighting types of TCM applications, national policies and regulations, outdated acts of parliament that can be amended, standardization of TCM education, and initiatives to train
0 views • 8 slides
Traditional Chinese Legal System: Insights and Practices
Traditional Chinese law is deeply rooted in philosophical principles, particularly Confucian doctrines. The role of law is marginalized, emphasizing harmony and amicable dispute resolution. Judges base decisions on wisdom and experience aligned with Confucian ethics. Legal advisors have low prestige
0 views • 39 slides
Traditional Medicine Integration into Gambian Health System
The Gambia's National Traditional Medicine Program aims to integrate traditional and complementary medicine practices into the health system. Established in 2001, the program faces challenges in regulating practitioners and ensuring the safety of herbal products. Despite these hurdles, it strives to
0 views • 21 slides
Transposition Cipher Techniques in Modern Block Ciphers
Transposition ciphers, specifically columnar and double columnar transpositions, are explored in the context of data encryption and computer engineering at Mustansiriyah University Engineering College. These techniques involve rearranging message elements without changing their identities, providing
0 views • 4 slides
Traditional Indigenous Seasons in the Arctic
The traditional Indigenous calendar in the Arctic is divided into five distinct seasons - Upirngassaq (Early Spring), Upirngaaq (Spring), Aujaq (Summer), Ukiassaaq (Early Fall), Ukiaq (Fall), and Ukiuq (Winter). Each season brings unique changes in sunlight, weather, ice conditions, harvest opportun
0 views • 6 slides
Understanding Block Ciphers in Cryptography
Explore the principles of block ciphers in modern cryptography, focusing on the Data Encryption Standard (DES) and its design principles. Learn about block cipher encryption, Feistel block cipher structure, n-bit block ciphers, ideal block ciphers, key length considerations, and challenges with idea
0 views • 44 slides
Understanding Symmetric Key Block Ciphers - Overview and Implementation
Delve into the world of symmetric key block ciphers through a detailed exploration of classical ciphers like substitution and transposition, modern cryptography advancements, DES encryption, Simplified DES, key scheduling, expansion functions, S-Box usage, and more. Discover the intricacies of encry
0 views • 40 slides
History and Evolution of Irish Traditional Music
Irish traditional music has a rich history dating back to the ancient times when primitive musical instruments were used for signaling and entertainment. The arrival of the Celts introduced significant instruments like the harp, shaping the musical culture of Ireland. Over the centuries, various tra
0 views • 14 slides
Understanding Encryption Techniques: From Transposition Ciphers to Rail Fence Ciphers
Explore the world of encryption techniques, diving into transposition ciphers and rail fence ciphers. Learn about encryption, decryption, plaintext, ciphertext, keys, and the art of secret writing. Discover how transposition ciphers reorder letters without changing their values and how rail fence ci
0 views • 26 slides
Czech Eating Habits and Traditional Food Overview
Explore the typical Czech meals like roasted sirloin beef with Czech dumplings, pork with dumplings and sauerkraut, soups, gingerbread, beer, and rolls. Discover the traditional Czech foods enjoyed during holidays such as Christmas cake, fish soup, Easter bread, and more. Learn about the positive an
0 views • 10 slides
Understanding Cryptography: Basics of Encryption and Padding
Cryptography is essential for secure communication between parties, ensuring confidentiality and integrity of data. This overview covers basic math concepts, block ciphers, encryption modes like ECB and CBC, and the importance of padding in securing plaintext data.
0 views • 21 slides
Understanding Traditional Skills vs. Motorized Tools in Wilderness Management
Explore the importance of traditional skills and tools versus motorized equipment in wilderness management, highlighting safety, cost, resource impacts, and training considerations. The presentation emphasizes the impact of using motorized tools, the challenges faced, and the assumptions surrounding
0 views • 25 slides
Internet Panel Surveys for Disability Data Collection
Researchers and policymakers are turning to internet panel surveys as a cost-effective and efficient method to collect data on disability and informal care prevalence. This modern approach offers advantages such as high response rates, speedy data collection, and lower costs compared to traditional
0 views • 14 slides
Overview of Modern Cryptography and Data Encryption Standard (DES)
Exploring modern cryptography including symmetric key block ciphers, public key ciphers, stream ciphers, and post-quantum ciphers. Focus on Data Encryption Standard (DES), Simplified DES, Feistel cipher, key schedule, expansion function, S-Box, DES encryption, and decryption processes.
0 views • 37 slides
ASEAN Guidelines on GMP for Traditional Medicines - Philosophy of Inspection
The ASEAN Guidelines on GMP for Traditional Medicines highlight the Philosophy of Inspection for ensuring quality and safety in traditional medicines and health supplements. The document covers legal terms, audit trail requirements, electronic signature control, and familiar auditor requirements. It
0 views • 88 slides
Understanding Public Key Cryptography in Network Security
Explore the concepts of public key cryptography, key distribution challenges, solutions to secret key schemes, and the importance of secure communication in network security. Learn about cryptology, cryptography, cryptanalysis, block ciphers, stream ciphers, and more in this informative content.
0 views • 21 slides
Traditional Music in Jordan: A Deep Dive into Jordanian Musical Heritage
Explore the rich tradition of traditional music in Jordan, ranging from popular folklore to refined artistic compositions. Learn about traditional instruments, the significance of folk music, and cultural events like the Jerash festival and the popular Arab dance, Dabke. Immerse yourself in the vibr
0 views • 7 slides
Exploring Celtic Rock Music: A Fusion of Traditional Folk and Rock Styles
Celtic Rock music is a modern genre that blends traditional folk music with rock elements. Originating in the 1970s, bands like Thin Lizzy and Runrig popularized this fusion by incorporating instruments like fiddles, bagpipes, and electric guitars. The rhythmic influences of Scottish dances and orna
0 views • 6 slides
Exploring Traditional Music in Jordan: Folk Sounds and Cultural Influences
The traditional folk music of Jordan encompasses countryside, Bedouin, and marine influences, each with unique characteristics and cultural significance. From vibrant countryside songs to the raw melodies of Bedouin music, and the limited yet distinctive marine music in Aqaba, Jordan's musical lands
0 views • 24 slides
Crack the Code: A Journey into Transposition Ciphers
Mathematicians play a crucial role in industries like telecommunications and internet companies by condensing data and ensuring error detection. Transposition ciphers, like the Scytale used by Romans, offer a challenging way to encrypt messages. Test your skills with code-breaking challenges and exp
0 views • 4 slides
African Traditional Religion and its Beliefs: An Overview
Understanding African traditional religion involves exploring the concept of the Supreme God, ancestor worship, witchcraft, magic, sorcery, and divination. This session delves into the relationship between religion, social rituals, and festivals, illustrating how it contributes to social solidarity.
0 views • 12 slides
Understanding Secure PRFs and PRPs in Cryptography
Dive into the world of secure Pseudo-Random Functions (PRFs) and Pseudo-Random Permutations (PRPs) in cryptography. Learn about the definitions, security criteria, and examples of secure PRFs and PRPs such as 3DES and AES. Explore the concepts of secure block ciphers and key principles behind these
0 views • 54 slides
Screening of Plants Used as Traditional Anticancer Remedies in Tanzania
Traditional Health Practitioners in Mkuranga and Same Districts, Tanzania, shared ethnomedical knowledge on medicinal plants used for cancer management. A total of 25 plant species were identified, with 56% showing brine shrimp toxicity. Potential anti-cancer candidates such as Ochna mossambicensis
0 views • 5 slides
Beavers Code Cracking Mystery - Detective Agency and Kidnapping Case!
In this thrilling mystery, Boo the beaver has been kidnapped, leaving behind coded messages to uncover the suspect. The Detective Agency seeks your help to crack the codes and rescue Boo. Dive into letter-number ciphers, Morse code, and a list of intriguing suspects to unravel the mystery and bring
0 views • 24 slides
Lightweight Cryptography: Key-Reduced Variants and Beyond-Birthday-Bound Security
Lightweight cryptography has emerged as a hot research topic in the past two decades, with over 60 ciphers proposed. This includes examples like PRESENT, GIFT, SIMON/SPECK, and more. Authenticated encryption through CAESAR and NIST LWC plays a vital role, with ASCON and ACORN leading the lightweight
0 views • 25 slides
The Impact of Cyber Media on Traditional Journalism
Cyber media, a merging of cybernetics and media theories, poses challenges to traditional journalism as it transitions to the online realm. With the rise of new media platforms, traditional journalists face uncertainty in adapting to the changing landscape dominated by citizen reporting and social m
0 views • 6 slides
Introduction to Cryptology in Algebra 2 Classroom
Engage students in a high school Algebra 2 class by exploring cryptology concepts such as coding, hexadecimal systems, substitution ciphers, and the Vigenere cipher. The lesson plan includes activities like solving puzzles, introducing binary systems, converting to hexadecimal, and writing messages
0 views • 16 slides
Introduction to Traditional Ciphers: Columnar Transpositions
Traditional ciphers such as Columnar Transpositions involve rearranging plaintext letters based on a fixed number of columns. This technique enhances security by incorporating a keyword for encryption and decryption. Learn about the process and examples of implementing Columnar Transpositions in thi
0 views • 8 slides
Unlock the Challenges in Cipher Cove: A STEM Adventure
Explore Cipher Cove and tackle five cryptographic challenges involving different ciphers such as Caesar Shift, Pigpen, Transposition, Substitution, and Periodic Table. Put your problem-solving skills to the test by deciphering hidden clues and codes to progress through each challenge and ultimately
0 views • 6 slides
Understanding Block Ciphers in Cryptography
Explore the world of block ciphers in cryptography through topics such as distinguishing attacks, key-recovery attacks, designing paradigms like Substitution-Permutation Networks (SPNs) and Feistel networks, concrete security considerations, confusion/diffusion principles, attack models, and more.
0 views • 27 slides
Comprehensive Overview of Encryption Techniques and Algorithms
Explore the world of encryption with insights into symmetric and public key encryption, certificate authorities, secure sockets layer, substitution ciphers, block ciphers, AES, and public key cryptography. Delve into the intricacies of encryption keys and algorithms, including the AES process, Diffi
0 views • 31 slides