Modern Threat Modeling & Cloud Systems in OWASP Sacramento
Explore modern threat modeling techniques for cloud systems at OWASP Sacramento's June 2023 event. Agenda includes community topics and more. Membership at Granite City offers workspace perks and access to exclusive events. Learn about threat modeling history and methodologies like STRIDE and PASTA.
1 views • 14 slides
Understanding Vector Operations in Linear Algebra
Explore the world of vector operations in linear algebra through this detailed presentation. Learn about vector addition, scalar multiplication, field operations, and more. Gain insights into the notation of Fn and the significance of scalar multiplication and vector addition in linear algebra. Whet
8 views • 9 slides
Understanding Normed Vector Spaces for Nanotechnology Engineering
Introduction to normed vector spaces, focusing on defining norms for vectors in finite-dimensional spaces, exploring different ways to measure vector length, and understanding the concept of unit vectors and norm properties. This topic equips readers with the ability to calculate vector norms, norma
0 views • 9 slides
Vector Multiplication
Learn about vector multiplication, unit vectors, magnitude calculations, scalar dot products, cross products, and angle determinations between vectors. Explore video explanations and visual representations for a comprehensive understanding of vector mathematics concepts.
0 views • 11 slides
Cyber Threat Detection and Network Security Strategies
Threat detection is crucial in analyzing security ecosystems to identify and neutralize malicious activities. Methods like leveraging threat intelligence, behavior analytics, setting intruder traps, and conducting threat hunts are essential for proactive security. Implementing security through obscu
1 views • 51 slides
Understanding Vector Algebra and Its Applications
Explore the fundamentals of vector algebra, including position vectors, direction cosines, direction ratios, vector addition, scalar product, vector product, and more. Learn about the dot product, cross product, and the angle between two vectors. Visual aids and examples help clarify key concepts in
0 views • 18 slides
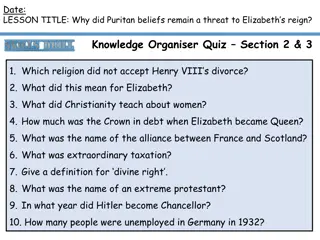
The Persistent Threat of Puritan Beliefs to Elizabeth's Reign
The Puritan belief system posed a significant threat to Queen Elizabeth I's reign, challenging the religious settlement she had put in place. Puritans disagreed with key aspects of the Church of England, such as the use of crucifixes and clergy vestments, leading to conflicts and resistance. Elizabe
0 views • 10 slides
Understanding Stereotype Threat and Teacher Response in Education
Stereotype Threat Theory explores the fear of confirming negative stereotypes and its impact on academic performance. Reduction of this threat can lead to improved learning outcomes. Teacher response plays a crucial role in shaping student writing, with various studies highlighting the importance of
0 views • 9 slides
Overview of Vector Calculus for ECE 3317 Course
This overview provides a brief explanation of vector calculus concepts essential for the ECE 3317 course on Applied Electromagnetic Waves. It covers del operator, gradient, divergence, curl, vector Laplacian, vector identities, and their applications in electromagnetic field theory.
0 views • 24 slides
Understanding Basis and Dimension in Linear Algebra
Basis and dimension are fundamental concepts in linear algebra. A basis is a set of vectors in a vector space that allows us to represent any vector by multiplying and adding the basis vectors. The dimension of a vector space is the number of elements in its basis. Linear independence, spanning sets
0 views • 13 slides
Behavioral Threat Assessment Tabletop Exercise - College First Year Analysis
Explore a comprehensive behavioral threat assessment tabletop exercise focused on analyzing a college first-year scenario. The exercise includes roles and responsibilities for players, facilitators, evaluators, and observers, guiding participants through phases to familiarize themselves with a stude
0 views • 19 slides
Understanding Parallelism and Vector Instructions in CMPT 295
Delve into the world of parallelism and vector instructions in CMPT 295 as you explore fixed-length vector intrinsics, RISC-V concepts, computer programming fundamentals, processor execution processes, scalar and vector loops, and more. Discover the intricacies of memory, data arrays, structs, integ
1 views • 45 slides
Understanding Subspaces and Span of Vector Sets
Subspaces are vector sets that satisfy specific properties like containing the zero vector, being closed under vector addition, and scalar multiplication. Examples illustrate these properties and concepts such as the zero subspace and column space. The relationship between column space, row space, a
1 views • 11 slides
Understanding Word Meaning through Vector Space Models
Explore how Vector-Space (Distributional) Lexical Semantics represent word meanings as points in a high-dimensional space. Learn about Semantic similarity, creating sample lexical vector spaces, and using word vectors to measure semantic relatedness. Discover how other contextual features and featur
0 views • 33 slides
Understanding Cyber Threat Assessment and DBT Methodologies
Comprehensive information on methodologies and approaches useful for cyber threat assessment and Cyber DBT alongside classical DBT methodology as outlined in the NSS-10 document by S.K. Parulkar. The content discusses the importance of threat assessment, differences between physical and cyber threat
4 views • 17 slides
Challenges in Computer Systems Security
Understanding security in computer systems involves achieving goals in the presence of adversaries. However, this task is challenging due to the need to guarantee policies in the face of realistic and open-ended threat models. Issues can arise from problems with policy formulation, assumptions in th
0 views • 16 slides
Enhancing Incident Response Through Threat Intelligence
Explore the importance of threat intelligence in incident response, covering aspects such as understanding adversaries, assessing risks, evaluating threats, and leveraging strategic intelligence. Learn how organizations can benefit from a proactive approach to cybersecurity by utilizing threat intel
1 views • 18 slides
Linear Algebra and Vector Calculus Course Details
This course covers topics in linear algebra and vector calculus, including systems of linear equations, matrices, determinants, vector operations, functions of several variables, differentiation, and optimization. Textbooks by H. Anton and Swokowski are recommended, along with additional lecture not
0 views • 13 slides
Understanding SIMD for High-Performance Software Development
SIMD (Single Instruction Multiple Data) hardware support utilizes vector registers for high-performance computing. Vector instructions operate on multiple data elements simultaneously, offering scalability and efficient processing strategies. The use of wide vector registers enhances arithmetic oper
0 views • 41 slides
Comprehensive Training on Campus Threat Assessment Teams
Explore the advanced training curriculum developed by experts Marisa Randazzo, Ph.D., and Gene Deisinger, Ph.D., for Virginia Campus Threat Assessment Teams. The training covers areas like threat assessment processes, case management, legal updates, and challenges in team implementation. Participant
0 views • 92 slides
Fundamental Concepts in Vector Spaces and Inner Product Spaces
A vector space over a field F is characterized by operations such as addition and scalar multiplication. Subspaces, direct sums, linear combinations, linear spans, dimensions, and dual spaces are fundamental concepts in vector spaces. Moving into inner product spaces, the concept of inner products,
0 views • 13 slides
National Vector Borne Disease Control Program Overview
The National Vector Borne Disease Control Program (NVBDCP) focuses on preventing and controlling diseases such as Malaria, Dengue, Chikungunya, Filariasis, Japanese Encephalitis, and Kala-azar. Implemented at state level, NVBDCP aims to eliminate these diseases through strategic planning, policy mak
0 views • 9 slides
Mobile App Security Threat Modeling and Mitigation
Explore mobile app security threats, learn how to conduct threat modeling exercises, and implement mitigation strategies. Discover built-in security features, threat modeling technologies, and common threats like malware and code injection. Enhance your understanding of app security constraints and
0 views • 63 slides
Pennsylvania School Threat Assessment: Keeping Schools Safe
Pennsylvania schools have implemented a Threat Assessment Team to ensure the safety and security of students, staff, and community members. The team follows specific guidelines and procedures to assess and address threats, involving key stakeholders and promoting collaboration among multidisciplinar
0 views • 37 slides
Language Operations for Quantum Computers: Implementing Vector-Based Approaches
Exploration of language operations suited for quantum computing, focusing on vector-based techniques for NLP tasks such as text search, factorization, classification, and logic operations. Topics include analogy, composition, inference, and the significance of negation in semantic vector operations.
0 views • 23 slides
Understanding Stereotype Threat in Education
Stereotype threat is a phenomenon where individuals from marginalized groups experience anxiety due to negative stereotypes about their abilities. This can impact their performance and self-perception. Various groups, such as African-Americans, Latinos, females in STEM, elderly individuals, Roma, an
0 views • 42 slides
Threat Assessment Tabletop Exercise Overview
Conducting a tabletop exercise focused on threat assessment in a school setting. The exercise agenda includes welcome, introductions, exercise goals, objectives, participants' roles, exercise structure, and rules. The goals are to test preparedness for potential threats, coordinate plans effectively
0 views • 33 slides
Understanding Vectors in AP Physics C: Mechanics
Explore the fundamental concepts of vectors in AP Physics C: Mechanics, including scalar vs. vector quantities, vector operations, and vector multiplication. Discover the significance of vectors in explaining and predicting physical phenomena through graphical methods and mathematical equations. Div
0 views • 28 slides
Understanding Word Vector Models for Natural Language Processing
Word vector models play a crucial role in representing words as vectors in NLP tasks. Subrata Chattopadhyay's Word Vector Model introduces concepts like word representation, one-hot encoding, limitations, and Word2Vec models. It explains the shift from one-hot encoding to distributed representations
0 views • 25 slides
Understanding Gradient, Divergence, and Curl of a Vector with Dr. S. Akilandeswari
Explore the concepts of gradient, divergence, and curl of a vector explained by Dr. S. Akilandeswari through a series of informative images. Delve into the intricacies of vector analysis with clarity and depth.
0 views • 13 slides
Understanding Vector Calculus II Concepts with Examples by Prof. Somesh Kr. Malhotra
Explore advanced topics in vector calculus including gradient, divergence, curl, and theorems like the Divergence Theorem and Stokes' Theorem. Follow along with examples presented in Cartesian, spherical, and cylindrical coordinates to deepen your understanding of vector calculus concepts.
0 views • 29 slides
Understanding Vector Graphics in Computer Graphics
Vector graphics in computer graphics are defined by 2D points connected by lines and curves to form shapes. Commonly found in SVG, EPS, PDF, or AI formats, they differ from raster graphics like JPEG or PNG. The W3C standard for vector graphics is SVG, allowing scalable and resolution-independent ima
0 views • 4 slides
Understanding Vector Programming and Machines
Vector programming involves efficient processing of data through SIMD models, parallel computing, and vector extensions in architectures like SSE and AVX. Programming vector machines in C requires addressing challenges with automatic vectorization related to pointers and data layouts.
0 views • 58 slides
Advances in Online Learning with Vector Costs and Bandits with Knapsacks
Explore cutting-edge research on online learning algorithms dealing with vector costs and bandits, including applications in load balancing and bandits with knapsacks. The studies cover topics such as regret minimization, minimizing vector costs, and maximizing rewards while maximizing budget constr
0 views • 17 slides
Understanding Vector-Valued Functions and Motion in Space
Explore the concept of vector-valued functions and motion in space, including curves, tangents, position vectors, scalar functions, derivatives, and differentiation rules. Learn how to represent curves in vector form and understand the smoothness of a curve based on its derivatives. Gain insights in
0 views • 28 slides
Vector Art Services
At ArtWorkLady, we specialize in providing high-quality Vector Art Services to businesses worldwide. Whether you need raster to vector conversion, logo vectorization, or product illustrations, our experienced team delivers precise and scalable vect
2 views • 5 slides
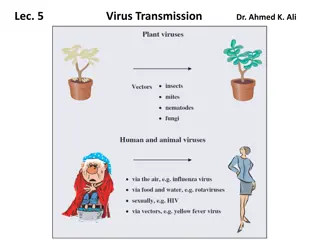
Understanding Virus Transmission via Vectors in Hosts
Viruses must be propagated and transmitted to new hosts for survival. They can be spread via vectors like arthropods, which acquire and transmit viruses during feeding. This transmission can occur quickly through the vector's mouthparts or more slowly via circulation in the vector's body. Plant viru
0 views • 14 slides
Understanding Divergence and the Divergence Theorem in Vector Fields
This content discusses the concept of divergence and the divergence theorem in vector fields through detailed examples and explanations. It covers topics such as finding divA in different coordinate systems, calculating charge density in regions based on given vector fields, and applying the diverge
0 views • 8 slides
Understanding Transformer Vector Groups in Transformer Systems
Transformer vector groups play a crucial role in determining the phase relationships between high and low voltage sides in transformer windings. Proper understanding of vector groups is essential for parallel connection of transformers to prevent phase differences and potential short circuits. The a
0 views • 36 slides
Impact of Stereotypes on Perceived Facial Threat in Women Offenders
Facial expressions play a significant role in understanding emotions, but stereotypes can influence how people perceive facial affect. This study examines how reading tabloid articles about crimes committed by dark and light-skinned women offenders affects the perceived facial threat. Using a 2x2 fa
0 views • 9 slides