Modern Threat Modeling & Cloud Systems in OWASP Sacramento
Explore modern threat modeling techniques for cloud systems at OWASP Sacramento's June 2023 event. Agenda includes community topics and more. Membership at Granite City offers workspace perks and access to exclusive events. Learn about threat modeling history and methodologies like STRIDE and PASTA.
1 views • 14 slides
Overview of Army Modeling and Simulation Office
The U.S. Army Modeling and Simulation Office (AMSO) serves as the lead activity in developing strategy and policy for the Army Modeling and Simulation Enterprise. It focuses on effective governance, resource management, coordination across various community areas, and training the Army Analysis, Mod
1 views • 8 slides
Capacity Zone Modeling for Forward Capacity Auction 17 Results
This presentation unveils the Capacity Zone modeling calculations for Forward Capacity Auction 17 associated with the 2026-2027 Capacity Commitment Period by ISO-NE PUBLIC. It delves into boundary definitions, import-constrained zone modeling, and market rules guiding the assessments and modeling pr
0 views • 16 slides
Distribution Feeder Modeling and Analysis Overview
This document delves into the modeling, optimization, and simulation of power distribution systems, specifically focusing on Distribution Feeder Modeling and Analysis. It covers the components of a typical distribution feeder, series components, Wye-Connected Voltage Regulator modeling, and equation
0 views • 14 slides
Comprehensive Guide to Penetration Testing Execution Standard (PTES)
Penetration Testing Execution Standard (PTES) is a crucial methodology to simulate attackers' methods for compromising security controls and gaining access to systems. The PTES process involves phases such as Pre-Engagement, Intelligence Gathering, Threat Modeling, Vulnerability Analysis, Exploitati
3 views • 14 slides
Understanding Data Modeling vs Object Modeling
Data modeling involves exploring data-oriented structures, identifying entity types, and assigning attributes similar to class modeling in object-oriented development. Object models should not be solely based on existing data schemas due to impedance mismatches between object and relational paradigm
0 views • 17 slides
Cyber Threat Detection and Network Security Strategies
Threat detection is crucial in analyzing security ecosystems to identify and neutralize malicious activities. Methods like leveraging threat intelligence, behavior analytics, setting intruder traps, and conducting threat hunts are essential for proactive security. Implementing security through obscu
1 views • 51 slides
Evolution of Modeling Methodologies in Telecommunication Standards
Workshop on joint efforts between IEEE 802 and ITU-T Study Group 15 focused on information modeling, data modeling, and system control in the realm of transport systems and equipment. The mandate covers technology architecture, function management, and modeling methodologies like UML to YANG generat
1 views • 16 slides
Understanding Geometric Modeling in CAD
Geometric modeling in computer-aided design (CAD) is crucially done in three key ways: wireframe modeling, surface modeling, and solid modeling. Wireframe modeling represents objects by their edges, whereas surface modeling uses surfaces, vertices, and edges to construct components like a box. Each
1 views • 37 slides
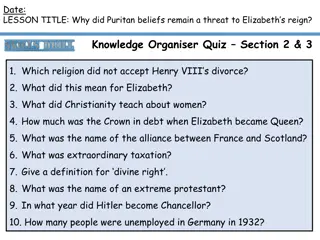
The Persistent Threat of Puritan Beliefs to Elizabeth's Reign
The Puritan belief system posed a significant threat to Queen Elizabeth I's reign, challenging the religious settlement she had put in place. Puritans disagreed with key aspects of the Church of England, such as the use of crucifixes and clergy vestments, leading to conflicts and resistance. Elizabe
0 views • 10 slides
Mathematical Modeling and Error Analysis in Engineering
Mathematical modeling plays a crucial role in solving engineering problems efficiently. Numerical methods are powerful tools essential for problem-solving and learning. This chapter explores the importance of studying numerical methods, the concept of mathematical modeling, and the evaluation proces
0 views • 10 slides
Understanding Stereotype Threat and Teacher Response in Education
Stereotype Threat Theory explores the fear of confirming negative stereotypes and its impact on academic performance. Reduction of this threat can lead to improved learning outcomes. Teacher response plays a crucial role in shaping student writing, with various studies highlighting the importance of
0 views • 9 slides
Introduction to Dynamic Structural Equation Modeling for Intensive Longitudinal Data
Dynamic Structural Equation Modeling (DSEM) is a powerful analytical tool used to analyze intensive longitudinal data, combining multilevel modeling, time series modeling, structural equation modeling, and time-varying effects modeling. By modeling correlations and changes over time at both individu
0 views • 22 slides
System Modeling and Simulation Overview
This content provides insights into CPSC 531: System Modeling and Simulation course, covering topics such as performance evaluation, simulation modeling, and terminology in system modeling. It emphasizes the importance of developing simulation programs, advantages of simulation, and key concepts lik
0 views • 28 slides
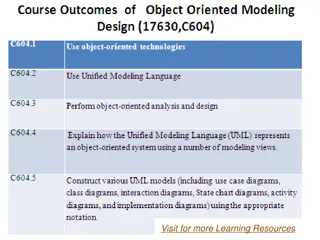
Understanding Object Modeling in Software Development
Object modeling is a crucial concept in software development, capturing the static structure of a system by depicting objects, their relationships, attributes, and operations. This modeling method aids in demonstrating systems to stakeholders and promotes a deeper understanding of real-world entitie
1 views • 65 slides
Behavioral Threat Assessment Tabletop Exercise - College First Year Analysis
Explore a comprehensive behavioral threat assessment tabletop exercise focused on analyzing a college first-year scenario. The exercise includes roles and responsibilities for players, facilitators, evaluators, and observers, guiding participants through phases to familiarize themselves with a stude
0 views • 19 slides
Coupled Ocean-Atmosphere Modeling on Icosahedral Grids
Coupled ocean-atmosphere modeling on horizontally icosahedral and vertically hybrid-isentropic/isopycnic grids is a cutting-edge approach to modeling climate variability. The design goals aim to achieve a global domain with no grid mismatch at the ocean-atmosphere interface, with key indicators such
1 views • 21 slides
Understanding Cyber Threat Assessment and DBT Methodologies
Comprehensive information on methodologies and approaches useful for cyber threat assessment and Cyber DBT alongside classical DBT methodology as outlined in the NSS-10 document by S.K. Parulkar. The content discusses the importance of threat assessment, differences between physical and cyber threat
4 views • 17 slides
Challenges in Computer Systems Security
Understanding security in computer systems involves achieving goals in the presence of adversaries. However, this task is challenging due to the need to guarantee policies in the face of realistic and open-ended threat models. Issues can arise from problems with policy formulation, assumptions in th
0 views • 16 slides
Enhancing Incident Response Through Threat Intelligence
Explore the importance of threat intelligence in incident response, covering aspects such as understanding adversaries, assessing risks, evaluating threats, and leveraging strategic intelligence. Learn how organizations can benefit from a proactive approach to cybersecurity by utilizing threat intel
1 views • 18 slides
Fire and Smoke Modeling Evaluation Effort (FASMEE) Overview
FASMEE is a collaborative project aimed at assessing and advancing fire and smoke modeling systems through critical measurement techniques and observational data. Led by key technical leads, FASMEE focuses on diverse modeling areas such as fire growth, effects, coupled fire-atmosphere behavior, smok
5 views • 30 slides
Subarea and Highway Corridor Studies: Travel Demand Modeling and Refinements
In this lesson, we delve into subarea and corridor studies focusing on travel demand model refinements, highway network coding, corridor congestion relief, and trip assignment theory. Subarea modeling plays a crucial role in forecasting travel within smaller regions with detailed traffic patterns, t
1 views • 45 slides
Essential Steps for Setting up a Modeling Study
Ensure clarity on modeling goals and uncertainties. Select sample areas strategically based on interest and available data. Determine appropriate resolution for modeling. Define variables to model and validate the model effectively. Assess sample data adequacy and predictor variables availability. E
0 views • 9 slides
Water Storage Tanks Hydraulic Modeling and Water Quality Considerations
This presentation by Justine Carroll, P.E., Project Manager, focuses on the hydraulic modeling and water quality considerations related to water storage tanks. It covers topics such as water age evaluation, steady state modeling, extended period simulations, pump controls, demand patterns, EPS verif
0 views • 34 slides
Advancing Computational Modeling for National Security and Climate Missions
Irina Tezaur leads the Quantitative Modeling & Analysis Department, focusing on computational modeling and simulation of complex multi-scale, multi-physics problems. Her work benefits DOE nuclear weapons, national security, and climate missions. By employing innovative techniques like model order re
0 views • 6 slides
Comprehensive Training on Campus Threat Assessment Teams
Explore the advanced training curriculum developed by experts Marisa Randazzo, Ph.D., and Gene Deisinger, Ph.D., for Virginia Campus Threat Assessment Teams. The training covers areas like threat assessment processes, case management, legal updates, and challenges in team implementation. Participant
0 views • 92 slides
Mobile App Security Threat Modeling and Mitigation
Explore mobile app security threats, learn how to conduct threat modeling exercises, and implement mitigation strategies. Discover built-in security features, threat modeling technologies, and common threats like malware and code injection. Enhance your understanding of app security constraints and
0 views • 63 slides
Pennsylvania School Threat Assessment: Keeping Schools Safe
Pennsylvania schools have implemented a Threat Assessment Team to ensure the safety and security of students, staff, and community members. The team follows specific guidelines and procedures to assess and address threats, involving key stakeholders and promoting collaboration among multidisciplinar
0 views • 37 slides
Understanding Stereotype Threat in Education
Stereotype threat is a phenomenon where individuals from marginalized groups experience anxiety due to negative stereotypes about their abilities. This can impact their performance and self-perception. Various groups, such as African-Americans, Latinos, females in STEM, elderly individuals, Roma, an
0 views • 42 slides
Threat Assessment Tabletop Exercise Overview
Conducting a tabletop exercise focused on threat assessment in a school setting. The exercise agenda includes welcome, introductions, exercise goals, objectives, participants' roles, exercise structure, and rules. The goals are to test preparedness for potential threats, coordinate plans effectively
0 views • 33 slides
Understanding Threat Modeling and Offensive Security
Threat modeling in offensive security involves determining potential threat scenarios that could compromise a system, understanding the system from an attacker's perspective, and devising defensive strategies. It helps confirm security implementations, identify gaps, monitor shortcomings, vulnerabil
0 views • 31 slides
Understanding Threat Assessment in Conservation: Direct, Stress, and Indirect Threats
Within threat assessment for conservation, different types of threats are identified and categorized, including direct threats which are human-induced actions directly affecting conservation targets, stressors which result from biophysical impacts of actions on targets, and indirect threats contribu
0 views • 24 slides
Pennsylvania School Threat Assessment Procedures and Guidance
Ongoing concerns about school safety led to legislation in 2019, requiring schools in Pennsylvania to establish threat assessment teams. This presentation provides an overview of the statute, threat levels, team responsibilities, procedures, and resources for school staff, parents, and guardians to
0 views • 25 slides
Conducting Threat Assessments Through the Atrocity Prevention Lens
This module from the GLOBAL CENTRE FOR THE RESPONSIBILITY TO PROTECT focuses on conducting threat assessments through an atrocity prevention lens. It covers risk identification, situational awareness in field settings, information collection methods, addressing vulnerabilities of women and children,
0 views • 20 slides
Bomb Threat Preparedness Guidelines for Shifa International Hospital
The Shifa International Hospital emphasizes the importance of maintaining a secure environment for employees, patients, and visitors in the event of a bomb threat. This presentation covers the types of bomb threats, steps to follow in case of a bomb threat, and provides guidance on handling telephon
0 views • 14 slides
High School Students Behavioral Threat Assessment Tabletop Exercise Analysis
Conduct a tabletop exercise analyzing the behavioral threat assessment of two high school students. Explore roles and responsibilities, exercise itinerary, goal, and purpose to enhance threat assessment team preparedness and response. Utilize simulated scenarios to simulate real-world events for opt
0 views • 23 slides
Examining Stereotype Threat in Engineering Education
Exploring the experiences of female engineering students facing stereotype threat, this critical theoretical framework study sheds light on the challenges that impact their academic journey. Through narrative inquiry methodology, the research focuses on white female students to understand how stereo
0 views • 37 slides
NetLogo - Programmable Modeling Environment for Simulating Natural and Social Phenomena
NetLogo is a powerful and versatile programmable modeling environment created by Uri Wilensky in 1999. It allows users to simulate natural and social phenomena by giving instructions to multiple agents operating independently, making it ideal for modeling complex systems evolving over time. NetLogo
0 views • 7 slides
School Safety and Threat Assessment Program Overview
Fact-based Threat Assessment for Safe and Supportive School Programs involves identifying, inquiring, assessing, and managing potentially dangerous situations. It aims to distinguish between those making threats and those posing real risks, without profiling or labeling individuals. Understanding th
0 views • 20 slides
Impact of Stereotypes on Perceived Facial Threat in Women Offenders
Facial expressions play a significant role in understanding emotions, but stereotypes can influence how people perceive facial affect. This study examines how reading tabloid articles about crimes committed by dark and light-skinned women offenders affects the perceived facial threat. Using a 2x2 fa
0 views • 9 slides