Modern Threat Modeling & Cloud Systems in OWASP Sacramento
Explore modern threat modeling techniques for cloud systems at OWASP Sacramento's June 2023 event. Agenda includes community topics and more. Membership at Granite City offers workspace perks and access to exclusive events. Learn about threat modeling history and methodologies like STRIDE and PASTA.
1 views • 14 slides
DESE End-of-Course Assessments Spring 2024 Overview
DESE's End-of-Course Assessments for Spring 2024 include assessments in subjects like Algebra, Biology, English, and Government, with optional assessments in other subjects. The transition to DRC and the Insight platform will require coordination between District Test Coordinators and High School st
1 views • 30 slides
Comprehensive Review on Medical Separations and Direct Threat Assessments for Health Staff
This resource provides an extensive overview of medical separations and direct threat assessments relevant to Job Corps health and wellness staff and subcontractors. It covers topics such as the process of medical separations, reinstatement rights, disability accommodation, and when medical separati
1 views • 60 slides
Faculty Instructions: Accessing, Viewing & Scoring Student Assessments in VIA/SLL - George Mason University Summer 2023
George Mason University's College of Education and Human Development (CEHD) utilizes the online assessment platform VIA/SLL by Watermark for collecting course-based assessment data. This guide outlines the process for faculty members to access, view, and score student assessments within VIA/SLL. It
6 views • 32 slides
MONEYVAL,the next six months.The view from the Isle of Man Experience from assessments.
Detailed insights on upcoming MONEYVAL assessments, experiences from the Isle of Man, timelines for 2023-2024, and advice for preparing for assessments. The content covers events, timelines, nationwide strategies, risk assessments, and publications related to money laundering and terrorist financing
1 views • 16 slides
Florida Statewide Assessments Training for Test Administrators Spring/Summer 2024
Training materials for test administrators participating in the Spring/Summer 2024 Florida Statewide Assessments covering various exams such as B.E.S.T., Writing, Science FSA, FAST Retakes, End-of-Course Assessments, and the Florida Civic Literacy Exam for grades 3-10. The materials are based on the
5 views • 76 slides
Cyber Threat Detection and Network Security Strategies
Threat detection is crucial in analyzing security ecosystems to identify and neutralize malicious activities. Methods like leveraging threat intelligence, behavior analytics, setting intruder traps, and conducting threat hunts are essential for proactive security. Implementing security through obscu
0 views • 51 slides
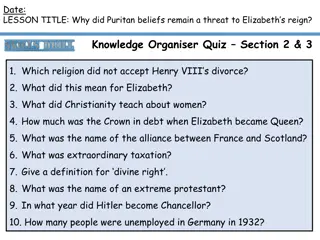
The Persistent Threat of Puritan Beliefs to Elizabeth's Reign
The Puritan belief system posed a significant threat to Queen Elizabeth I's reign, challenging the religious settlement she had put in place. Puritans disagreed with key aspects of the Church of England, such as the use of crucifixes and clergy vestments, leading to conflicts and resistance. Elizabe
0 views • 10 slides
Understanding Personality Assessments in Interviews
Personality assessments in interviews are valuable tools for evaluating a candidate's characteristics, abilities, and aspirations. Various types of assessments, such as structured and unstructured interviews, personality inventories like the Minnesota Multiphasic Personality Inventory, the Big Five
0 views • 28 slides
Understanding Stereotype Threat and Teacher Response in Education
Stereotype Threat Theory explores the fear of confirming negative stereotypes and its impact on academic performance. Reduction of this threat can lead to improved learning outcomes. Teacher response plays a crucial role in shaping student writing, with various studies highlighting the importance of
0 views • 9 slides
Risk Management Strategies in Organizational Security
Exploring risk management in organizational security, this study guide delves into resiliency, automation strategies, policies, and procedures to reduce risk. It covers threat assessments, computing risk assessments, qualitative vs. quantitative risk measurements, and actions based on risk assessmen
1 views • 19 slides
Understanding the In-Combination Effect Test and De Minimis Effects in Environmental Assessments
This content discusses the complexities of the in-combination effect test and de minimis effects in environmental impact assessments. It covers when the in-combination effect assessment is needed, the legislation surrounding such assessments, and the concept of no appreciable effect as a threshold f
0 views • 21 slides
Understanding AML Risk Assessments and Due Diligence Regulations
Anti-money laundering (AML) risk assessments and due diligence regulations are crucial for preventing money laundering and terrorist financing. This content discusses the importance of risk assessments, client due diligence, and regulatory compliance in the AML landscape. It emphasizes the need for
0 views • 13 slides
Maximizing Student Growth Through Common Formative Assessments
Key concepts around common formative assessments (CFAs) are highlighted in this presentation, emphasizing the importance of shared understanding, aligning assessments with standards, and supporting student growth. The content delves into the purpose and benefits of CFAs, outlining criteria for effec
0 views • 13 slides
Behavioral Threat Assessment Tabletop Exercise - College First Year Analysis
Explore a comprehensive behavioral threat assessment tabletop exercise focused on analyzing a college first-year scenario. The exercise includes roles and responsibilities for players, facilitators, evaluators, and observers, guiding participants through phases to familiarize themselves with a stude
0 views • 19 slides
Severe Malaria Rapid Assessments: Knowledge, Attitudes, and Practices
This presentation discusses severe malaria rapid assessments conducted by Development Data in Uganda and Zambia. The assessments aimed to improve severe malaria case management at community and lower health facility levels. Key findings include knowledge levels among health workers, transitioning kn
0 views • 20 slides
Understanding Cyber Threat Assessment and DBT Methodologies
Comprehensive information on methodologies and approaches useful for cyber threat assessment and Cyber DBT alongside classical DBT methodology as outlined in the NSS-10 document by S.K. Parulkar. The content discusses the importance of threat assessment, differences between physical and cyber threat
4 views • 17 slides
Challenges in Computer Systems Security
Understanding security in computer systems involves achieving goals in the presence of adversaries. However, this task is challenging due to the need to guarantee policies in the face of realistic and open-ended threat models. Issues can arise from problems with policy formulation, assumptions in th
0 views • 16 slides
Enhancing Incident Response Through Threat Intelligence
Explore the importance of threat intelligence in incident response, covering aspects such as understanding adversaries, assessing risks, evaluating threats, and leveraging strategic intelligence. Learn how organizations can benefit from a proactive approach to cybersecurity by utilizing threat intel
1 views • 18 slides
Utah State Board of Education Testing Ethics Policy Presentation
This presentation by the Utah State Board of Education outlines the organization of the Standard Test Administration and Testing Ethics Policy. It covers the purpose of testing, assessments, mandated assessments, state assessments, federal assessments, and required district assessments. The focus is
0 views • 26 slides
Developing the Prehab Pathway for Lung Cancer Patients by Dr. Louise Brown
Dr. Louise Brown from North Manchester General Hospital leads the development of a prehab pathway for lung cancer patients in the NE sector. The project aims to enhance patient outcomes through pre-surgical preparation, addressing challenges such as frailty, deprivation, and lack of access to assess
0 views • 14 slides
Understanding the 2015 Smarter Balanced Interim Assessments
This informational piece delves into the details of the 2015 Smarter Balanced Interim Assessments, which are part of the broader assessment system designed to aid teaching and student learning. The assessments are optional yet highly recommended, offering valuable insights to teachers for monitoring
0 views • 50 slides
Comprehensive Training on Campus Threat Assessment Teams
Explore the advanced training curriculum developed by experts Marisa Randazzo, Ph.D., and Gene Deisinger, Ph.D., for Virginia Campus Threat Assessment Teams. The training covers areas like threat assessment processes, case management, legal updates, and challenges in team implementation. Participant
0 views • 92 slides
Effective Design of Learning Outcomes and Assessments
This session covers writing measurable learning outcomes, designing assessments aligning with outcomes, creating assessments for specific outcomes, analyzing assessments to determine intended learning outcomes, and the importance of clarifying expectations for students and instructors through learni
0 views • 16 slides
Mobile App Security Threat Modeling and Mitigation
Explore mobile app security threats, learn how to conduct threat modeling exercises, and implement mitigation strategies. Discover built-in security features, threat modeling technologies, and common threats like malware and code injection. Enhance your understanding of app security constraints and
0 views • 63 slides
Pennsylvania School Threat Assessment: Keeping Schools Safe
Pennsylvania schools have implemented a Threat Assessment Team to ensure the safety and security of students, staff, and community members. The team follows specific guidelines and procedures to assess and address threats, involving key stakeholders and promoting collaboration among multidisciplinar
0 views • 37 slides
Academic Assessments and Proficiency Overview at Hamilton County Elementary School
This overview provides insights into academic assessments and proficiency levels at Hamilton County Elementary School. It includes data on i-Ready Reading and Math, STAR assessments for Early Literacy, Reading, and Math across different grade levels, as well as Kindergarten and 1st-3rd Grade assessm
0 views • 37 slides
Understanding Stereotype Threat in Education
Stereotype threat is a phenomenon where individuals from marginalized groups experience anxiety due to negative stereotypes about their abilities. This can impact their performance and self-perception. Various groups, such as African-Americans, Latinos, females in STEM, elderly individuals, Roma, an
0 views • 42 slides
Ensuring Health and Safety in Club and Society Activities
Club and society activities require completing annual risk assessments to ensure the safety of members and guests. Different activities may need additional assessments. Submission deadlines and contact information are provided for coordinating assessments. Societies must submit a Health & Safety For
0 views • 20 slides
Threat Assessment Tabletop Exercise Overview
Conducting a tabletop exercise focused on threat assessment in a school setting. The exercise agenda includes welcome, introductions, exercise goals, objectives, participants' roles, exercise structure, and rules. The goals are to test preparedness for potential threats, coordinate plans effectively
0 views • 33 slides
Understanding Threat Modeling and Offensive Security
Threat modeling in offensive security involves determining potential threat scenarios that could compromise a system, understanding the system from an attacker's perspective, and devising defensive strategies. It helps confirm security implementations, identify gaps, monitor shortcomings, vulnerabil
0 views • 31 slides
Understanding Threat Assessment in Conservation: Direct, Stress, and Indirect Threats
Within threat assessment for conservation, different types of threats are identified and categorized, including direct threats which are human-induced actions directly affecting conservation targets, stressors which result from biophysical impacts of actions on targets, and indirect threats contribu
0 views • 24 slides
Pennsylvania School Threat Assessment Procedures and Guidance
Ongoing concerns about school safety led to legislation in 2019, requiring schools in Pennsylvania to establish threat assessment teams. This presentation provides an overview of the statute, threat levels, team responsibilities, procedures, and resources for school staff, parents, and guardians to
0 views • 25 slides
Conducting Threat Assessments Through the Atrocity Prevention Lens
This module from the GLOBAL CENTRE FOR THE RESPONSIBILITY TO PROTECT focuses on conducting threat assessments through an atrocity prevention lens. It covers risk identification, situational awareness in field settings, information collection methods, addressing vulnerabilities of women and children,
0 views • 20 slides
Bomb Threat Preparedness Guidelines for Shifa International Hospital
The Shifa International Hospital emphasizes the importance of maintaining a secure environment for employees, patients, and visitors in the event of a bomb threat. This presentation covers the types of bomb threats, steps to follow in case of a bomb threat, and provides guidance on handling telephon
0 views • 14 slides
High School Students Behavioral Threat Assessment Tabletop Exercise Analysis
Conduct a tabletop exercise analyzing the behavioral threat assessment of two high school students. Explore roles and responsibilities, exercise itinerary, goal, and purpose to enhance threat assessment team preparedness and response. Utilize simulated scenarios to simulate real-world events for opt
0 views • 23 slides
Examining Stereotype Threat in Engineering Education
Exploring the experiences of female engineering students facing stereotype threat, this critical theoretical framework study sheds light on the challenges that impact their academic journey. Through narrative inquiry methodology, the research focuses on white female students to understand how stereo
0 views • 37 slides
Fall/Winter 2023 Florida Statewide Assessments Training Materials Overview
Training materials based on the Fall/Winter 2023 Test Administration Manual for Florida Statewide Assessments, including End-of-Course assessments, Florida Civic Literacy Exam, and FSA/FAST retakes. Emphasizes test administration policies and procedures, not a replacement for reading the manual. Inf
0 views • 88 slides
Utah State Board of Education Testing Ethics Policy Presentation
The presentation outlines Utah's Standard Test Administration and Testing Ethics Policy for educators, emphasizing the importance of ethical testing practices and fair assessment of students. It covers the organization of the policy, purpose of testing, statewide assessments, mandated assessments, s
0 views • 30 slides
OASIS-C Quiz: Test Your Knowledge of OASIS-C Assessments
Test your understanding of OASIS-C assessments with this quiz covering different scenarios and requirements such as reporting data, comprehensive assessments, recertification, and types of assessments. Find out more about OASIS-C guidelines and practices through this interactive quiz.
0 views • 21 slides