Welcome to the Coding Adventure, where students thrive through development
Hey there, fellow code enthusiasts! \ud83d\ude80 Ready to embark on a journey of building something truly amazing with Java Full Stack Projects? Whether you\u2019re a seasoned developer or just dipping your toes into the coding world, get ready for an exciting adventure! \n\n \n\"Ever dreamt of crea
1 views • 2 slides
Mern Stack Training Institute in - Hyderabad
Visualpath is one of the best MERN Stack Training Course in - Hyderabad institutes in Hyderabad. We are providing Live Instructor-Led Online Classes delivered by experts from Our Industry. We will provide live project training after course completion. Enroll Now!! Contact us 91-9989971070.\nwhatsAp
1 views • 13 slides
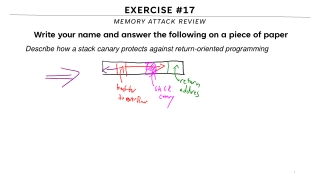
Memory Attack Review Overview
This content provides insights on memory attacks, particularly focusing on return-oriented programming and stack canary protection. It explores how stack canaries safeguard against return-oriented programming by detecting buffer overflows and preventing the alteration of return addresses. With a vis
1 views • 32 slides
MERN Stack Online Training - Courses - MERN STACK Training - Ameerpet
Visualpath offers the Best MERN STACK Training - Ameerpet by real-time experts for hands-on learning. Our MERN Stack Online Training - Courses is available in Hyderabad and is provided to individuals globally in the USA, UK, Canada, Dubai, and Australia. Contact us at 91-9989971070.\nJoin us on wha
3 views • 13 slides
Principles for ESS Time Schedule & VDER Usecase.
Exploring the principles and key components of the VDER program, including ESS time scheduling and value stack compensation. The VDER components such as E-value, LSRV, DRV, Energy Value, and ICAP are discussed alongside the MCOS studies that assess marginal system cost reductions due to distributed
1 views • 8 slides
MERN Stack Training in Hyderabad - MERN Stack Training Course in Hyderabad
\nVisualpath offers the Best MERN Stack Training in Hyderabad by real-time experts for hands-on learning. Our MERN Stack Training Course in Hyderabad is available in Hyderabad and is provided to individuals globally in the USA, UK, Canada, Dubai, and Australia. Contact us at 91-9989971070.\nJoin us
1 views • 13 slides
Stack Based Attacks in Linux (an intro)
Explore the world of stack-based attacks in Linux through an introductory session presented by Bryce L. Meyer at the Saint Louis Linux Users Group. Covering topics from weaknesses to exploits, shellcode, and mitigations like stack canaries and address space randomization, this overview delves into c
7 views • 60 slides
Unlock Your Coding Superpowers with Mastering in Full Stack Web Development in Java
Full stack web development is a process of developing web applications which includes front-end and back-end. Encompasses data, business layers, and presentation ones to provide a smooth user experience.
10 views • 3 slides
Unlock Your Coding Superpowers with Mastering in Full Stack Web Development in Java
Full stack web development is a process of developing web applications which includes front-end and back-end. Encompasses data, business layers, and presentation ones to provide a smooth user experience. Java is a highly popular object-oriented language that is chosen by various businesses because o
10 views • 3 slides
A Safety Expert’s Guide: How to Stack Pallets Safely
In the bustling world of warehouses, logistics, and manufacturing, the proper stacking of pallets is a critical aspect of maintaining a safe and organized workspace. As a safety expert, I\u2019ve seen firsthand the importance of implementing best practices to ensure the secure stacking of pallets. I
14 views • 2 slides
full stack React developers company
Binary Informatics is one of the global leaders in full-stack development with React, having an unmatched experience when it comes to the development of strong and easily scalable applications. Binary Informatics is recognized for its team of experienced developers, proficient in both front- and bac
0 views • 7 slides
Design Your Journey Enroll in the Best Full Stack Java Developer Course in Pune
Java is an extremely adaptable and robust programming language in the wide technology area. Ambitious developers can benefit greatly from having this ability due to its versatility and broad use across other disciplines. Pune has various options to launch your career if you're hoping to enter the fi
0 views • 3 slides
Design Your Journey Enroll in the Best Full Stack Java Developer Course in Pune
Java is an extremely adaptable and robust programming language in the wide technology area. Ambitious developers can benefit greatly from having this ability due to its versatility and broad use across other disciplines. Pune has various options to launch your career if you're hoping to enter the fi
1 views • 3 slides
full stack React development services
They can handle server-side logic, databases, and the integration of APIs with the power of React to bring responsive and interactive user interfaces. At Binary Informatics, we focus on modern development practices and agile methodologies to create scalable, maintainable, and efficient applications
0 views • 7 slides
Piezoelectric Stack Actuator Market Analysis, Size, Share, Growth, Trends Foreca
The Global Piezoelectric Stack Actuator market stands at the forefront of technological driving advancements in various industries through its dynamic applications. These actuator systems harness the unique properties of piezoelectric materials, providing precision and versatility in a range of mech
0 views • 8 slides
Efficient Stack Emission Monitoring Procedure for Air Quality Control
Stack emission monitoring is crucial for industries to assess and reduce pollutants in exhaust air. This procedure involves tasks like measurement, testing, and analysis of flue gases. Sampling sites are selected strategically for accurate readings, and molecular weight and gas velocity are determin
1 views • 11 slides
Stack Organization in Computer Systems
A stack is an ordered linear list where insertions and deletions occur at one end, known as the top. It follows the Last In First Out (LIFO) access method and is commonly used in CPUs. Key operations include Push (inserting) and Pop (deleting) items from the stack. Applications include evaluating ma
0 views • 5 slides
Understanding The Stack in Embedded Systems Design
The stack plays a crucial role in embedded systems design by providing a last-in, first-out storage structure for dynamic memory allocation. In this chapter, Dr. Brock J. Lameres explores the concept of the stack, its physical implementation in microcontrollers like the MSP430FR2355, and the operati
2 views • 27 slides
Understanding Activation Records and Stack in Assembly Programming
Explore the key concepts of activation records and the stack in assembly programming, including their roles in function calls, memory management, and variable storage. Gain insights into the low-level layout of variables, call conventions in MIPS and x86, and practical examples illustrating stack op
2 views • 66 slides
Optimizing User-Space Network Services with F-Stack and FreeBSD TCP/IP Stack
F-Stack, a user-space network service using DPDK and FreeBSD TCP/IP stack, addresses challenges in handling service traffic like CDN and live streaming. By leveraging 25GbE, 40GbE, and 100GbE NICs, coupled with multi-core CPUs and kernel bypass techniques, F-Stack overcomes bottlenecks between user
1 views • 17 slides
Genetic Manipulation in Environmental Biotechnology
Genetic manipulation strategies in environmental biotechnology involve techniques like gene splicing and molecular cloning to modify genes directly. These methods have various applications such as isolating genes, producing specific molecules, improving biochemical production, creating organisms wit
0 views • 20 slides
Understanding Buffer Overflow Attacks at Carnegie Mellon
Learn about the Carnegie Mellon 15-213 Recitation Attack Lab, where you can hijack programs using buffer overflow attacks. Gain insights into stack discipline, stack frames, and defeating secure programs through return-oriented programming. Dive into topics like stack smashing attacks, buffer overfl
8 views • 24 slides
Understanding Ethical Considerations in Manipulated Photography for Media
Ethical control in photojournalism involves capturing non-fiction events without manipulation, but some control over the image is acceptable within ethical bounds. However, moving into manipulated images for non-news events requires a different approach, involving subject and scene manipulation for
0 views • 28 slides
How Advanced Algorithms Are Reshaping Data Manipulation
Explore the transformative impact of advanced algorithms on data manipulation in our latest feature. This insightful exploration delves into the sophisticated technologies revolutionizing business analytics and understanding what is data manipulation
0 views • 7 slides
Basin Manipulation Simulation Analysis Tool Overview
Basin Manipulation Simulation Analysis Tool provides a comprehensive solution for managing and analyzing basin data, including tasks like basin manipulation, simulation analysis, case management, and defining simulation time steps. The tool allows for easy data entry, visualization of simulation res
2 views • 17 slides
Protective Measures Against Stack Overflows
Host-based defenses such as Canaries, DEP, ASLR, and CFI play a crucial role in safeguarding systems against malicious attacks. Canaries act as early warning systems, alerting to stack overflows by monitoring changes in sensitive data. By implementing stack canaries, developers can prevent buffer ov
0 views • 51 slides
Understanding x86-64 Procedures and Data Structures
This content provides insights into x86-64 programming, covering topics such as procedures, integer registers, stack frames, locals in the red zone, interesting features of stack frames, arrays, multi-dimensional structures, and more. It dives into the usage conventions of integer registers, the all
0 views • 44 slides
Analysis of Lady Macbeth's Manipulation in Shakespeare's Macbeth
In a pivotal moment in Macbeth, Lady Macbeth's manipulation of her husband is showcased when she calls upon supernatural forces to overcome his kindness and convince him to kill Duncan. This extract is crucial in introducing Lady Macbeth's character and power dynamics within the play, particularly h
0 views • 49 slides
Understanding Memory Stack and Variable Scope in Computer Architecture
This content delves into the scope of variables, the stack in memory architecture, automatic and global variables, and the concept of constant types. It explains the functioning of the stack, how function calls are managed, and the allocation of variables within stack frames. The relationship betwee
0 views • 18 slides
Understanding x86-64 Stack and Register Usage at Carnegie Mellon
Explore the concepts of stack management, function invocation, and register usage in x86-64 architecture as taught in Carnegie Mellon's 15-213 recitation on Attack Lab. Learn about stack operations, caller vs. callee functions, and the conventions for using registers effectively. Gain insights into
0 views • 26 slides
Storage and Manipulation of Liquefied Gases with Dewars and Cryostats
Storage and manipulation of liquefied gases involve using specialized equipment like Dewars and Cryostats to minimize heat transfer and maintain low temperatures. Dewars, invented by James Dewar, are double-walled vacuum vessels designed to store liquefied gases with minimal losses. The use of vacuu
0 views • 11 slides
Understanding Stack Protection and Exploitation Techniques
Delve into the world of stack protection and exploitation, covering topics like exploiting arbitrary write, issues with stack canaries, and shadow stack usage. Explore defense mechanisms like Stack Cookie and learn about the power of exploiting vulnerabilities to write arbitrary memory. Discover met
0 views • 23 slides
Understanding Direct Manipulation in HCI
In this lecture, learn about the concept of direct manipulation in Human-Computer Interaction (HCI), including its benefits, drawbacks, and related terms such as engagement, distance, semantic, and articulatory distances. Explore the evolution of GUIs and interaction styles, and compare edge maps an
0 views • 24 slides
Understanding Stack Buffer Overflow Vulnerabilities
Stack buffer overflow is a critical security issue caused by writing more data to a buffer than allocated, leading to bugs, crashes, and potential attacks. This vulnerability, exemplified by the Twilight Hack, allows executing arbitrary code. Learn about its causes, implications, and mitigation stra
0 views • 7 slides
Understanding Buffer Overflow in Stack: SEED Workshop Lab
This content provides a comprehensive overview of buffer overflow in stack focusing on SEED Workshop Lab scenarios. It covers principles, practice, high-level pictures, program memory layout, function stack layout, function call chains, vulnerable program examples, and more. Through detailed images
0 views • 34 slides
Understanding Stack Overflow Vulnerabilities and Exploitation Techniques
Explore the history of stack overflow vulnerabilities, learn how to control a PC using stack overflow, place shellcode in memory, calculate shellcode addresses, and execute shellcode. Understand different types of overflows including stack overflow, heap overflow, and integer overflow. Delve into th
0 views • 33 slides
Understanding Pushdown Automata (PDA) in Computer Science
Pushdown Automata (PDA) are essential in theoretical computer science, serving as an extension of non-deterministic finite automata (NFA). PDAs incorporate a stack, enabling them to recognize non-regular languages. They are described by transitions involving input symbols, state changes, and stack m
0 views • 46 slides
Understanding Narcissistic Abuse: The Insidious Manipulation of Victims
Narcissistic abuse is a form of severe psychological and emotional manipulation that targets a victim's spirit and identity. The abuser employs tactics such as lying, manipulation, denial of reality, and control. This abuse is often invisible and devastating, characterized by a lack of empathy and a
0 views • 15 slides
Ethical Analysis of Manipulation in Organ Allocation System
This resource tackles the issue of manipulation in organ transplant waitlist priority through unnecessary medical interventions. It highlights the ethical concerns, potential harms, and ways to mitigate this manipulation, urging adherence to systemic safeguards and ethical clinical practice.
0 views • 9 slides
Innovative Multicellular Computing Circuits for Genetic Manipulation
Cells are utilized as computational devices in a innovative approach for genetic manipulation. Various logic gates and promoters are combined to achieve complex circuit behavior without the need for genetic manipulation. Advantages include a wide dynamic range and low variability, but with the drawb
0 views • 10 slides