Active Directory Penetration Testing, cionsystems
The partner plan of AD Guardian is used by professional services which include penetration testing to test if your AD is secure from such threats. http:\/\/tinyurl.com\/4yzps5xv
1 views • 2 slides
Active Directory Penetration Testing, cionsytems.com
The partner plan of AD Guardian is used by professional services which include penetration testing to test if your AD is secure from such threats. \/\/rb.gy\/2f1rq2
4 views • 7 slides
Active Directory Penetration Testing, cionsystems.com
The partner plan of AD Guardian is used by professional services which include penetration testing to test if your AD is secure from such threats. \/\/rb.gy\/m1wkb8
2 views • 2 slides
Understanding Social Learning Theory and the Power of Example
Social Learning Theory, introduced by Bandura, emphasizes learning through observation and modeling. It explores how individuals acquire behavioral dispositions, trial-and-error experiences, and the impact of stimuli in the environment. The theory focuses on the importance of attention, retention, a
1 views • 17 slides
Evolution of Mathematical Theories and Proof Systems
Development of mathematical theories such as model theory, proof theory, set theory, recursion theory, and computational complexity is discussed, starting from historical perspectives with Dedekind and Peano to Godel's theorems, recursion theory's golden age in the 1930s, and advancements in proof t
1 views • 29 slides
Penetration Testing and Incident Response Technologies Overview
Explore the world of penetration testing, incident response technologies, and ethical hacking in the context of CIS 6395 course at UCF. Learn about tools like Metasploitable 2 VM for vulnerability testing and techniques such as Ping Sweep and Ping. Discover essential concepts for testing and securin
0 views • 32 slides
Psychological Theories of Criminality: Understanding the Roots
Psychological theories of criminality delve into the association between intelligence, personality, learning, and criminal behavior. Major theories include Psychodynamic Theory by Freud, Behavioral Theory by Bandura, and Cognitive Theory by Kohlberg. These theories explore how unconscious mental pro
1 views • 20 slides
Comprehensive Guide to Penetration Testing Execution Standard (PTES)
Penetration Testing Execution Standard (PTES) is a crucial methodology to simulate attackers' methods for compromising security controls and gaining access to systems. The PTES process involves phases such as Pre-Engagement, Intelligence Gathering, Threat Modeling, Vulnerability Analysis, Exploitati
3 views • 14 slides
Polymeric Controlled Drug Delivery Systems
Polymeric controlled drug delivery systems play a crucial role in regulating drug release through diffusion, solvent penetration, and chemical mechanisms. These systems include diffusion-controlled, solvent-controlled, and chemically-controlled devices, each operating based on specific principles. S
0 views • 33 slides
Understanding the Theory of Firms: Neoclassical vs. Modern Approaches
The theory of firms is explored through the Neoclassical and Modern perspectives. Neoclassical theory focuses on profit maximization, while Modern theory delves into managerial, principal-agent, and transaction cost theories. The discussion covers criticisms of Neoclassical theory and the essential
1 views • 79 slides
Disaster Recovery and Incident Response Concepts
This content covers the essential concepts of disaster recovery, incident response, penetration testing, vulnerability scanning, and business continuity planning in the context of cybersecurity. It explains the goals and steps involved in penetration testing, vulnerability scanning tasks, business c
2 views • 15 slides
Theories of Causation in Psychological and Social Sciences
Overview of theories of causation categorized into psychological, social psychological, and sociological perspectives. Psychological theories focus on instinctive, biological, and psychological qualities of abusers, including Attachment Theory, Psychodynamic Theory, Social Learning Theory, and Situa
0 views • 15 slides
Insights into the Nigerian Insurance Industry: Trends and Opportunities
The Nigerian insurance industry shows promising growth potential with low penetration rates but increasing awareness and regulatory support. Despite challenges, there has been significant growth in premiums and a shift towards a more diverse professional workforce. A comparison with similar economie
0 views • 10 slides
Shopper Insight Report - Northern Ireland Region Analysis
This Shopper Insight Report covers a 52-week period from 02/05/2016 to 30/04/2017, focusing on key performance indicators like sales growth, customer penetration, and customer loyalty. Recommendations include focusing on core stores with high demand, increasing penetration and repeat rate, and utili
0 views • 23 slides
Understanding Political Theory through a Contextual Approach
Exploring G.H. Sabine's perspective on political theory through a contextual approach, emphasizing the importance of historical context and societal influences. Sabine argues that while political theory evolves with its contemporary politics, it should be analyzed within its specific time and social
0 views • 9 slides
Evolution of Light Theory: From Wave Theory to Quantum Theory
At the turn of the century, the discovery of the photoelectric effect challenged the wave theory of light, leading to the development of the quantum theory by Max Planck and Albert Einstein. This new theory introduced the concept of discrete energy units known as quanta, bridging the gap between wav
1 views • 62 slides
Understanding Social Cognitive Theory: Insights from Albert Bandura
Social Cognitive Theory, developed by Albert Bandura, emphasizes learning through observation and modeling behaviors. The theory explores how individuals acquire new behaviors, thoughts, and attitudes by observing others. Bandura's famous Bobo doll experiment showcased how children imitated aggressi
6 views • 17 slides
Theoretical Perspectives in Sociology of Education
Exploring major theoretical perspectives such as functionalism, conflict theory, and symbolic interactionism along with contemporary approaches like code theory, cultural capital, and status competition. The functionalist theory emphasizes social cohesion and maintaining social order through educati
3 views • 14 slides
Dp-branes, NS5-branes, U-duality, and M-Theory Overview
Overview of Dp-branes, NS5-branes, and U-duality derived from nonabelian (2,0) theory with Lie 3-algebra. Introduction to M-theory, including M2-branes and M5-branes in the strong coupling limit. Discussion on BLG theory, Lorentzian Lie 3-algebra, and the ABJM theory for M2-branes.
1 views • 32 slides
Understanding Penetration Testing Tactics and Techniques
In the realm of secure software engineering, penetration testing plays a crucial role in proactively identifying vulnerabilities. This involves delving deep to exploit potential weaknesses and simulate real-world attack scenarios. Skilled testers, both in-house and external, use frameworks like MITR
0 views • 16 slides
Understanding Time-Independent Perturbation Theory in Quantum Mechanics
Perturbation theory is a powerful tool in solving complex physical and mathematical problems approximately by adjusting solutions from a related problem with known solutions. This theory allows for more accurate approximate solutions by treating the difference as a small perturbation. An example inv
0 views • 19 slides
Study on EU Retail Sector: Drivers of Choice and Innovation
The study examines complaints of large retailers imposing detrimental conditions on food suppliers, affecting investment, choice, and innovation. Findings suggest that competition, economic environment, and bargaining power influence innovation, while private label penetration shows a negative corre
0 views • 8 slides
How to Boost Your Business with Effective Market Penetration
Market penetration is a strategy aimed at increasing a company\u2019s market share within existing markets. It involves selling more of the current products or services to existing customers and attracting competitors\u2019 customers.
0 views • 10 slides
Understanding Ultrasound Transducers: Applications and Functionality
Ultrasound transducers play a crucial role in medical imaging by converting electrical signals into ultrasonic energy for tissue penetration and image creation. This technology utilizes focused transducers to enhance resolution and penetration, while also managing beam intensity. The article delves
0 views • 24 slides
Understanding Affect Control Theory in Social Science: A Primer
Affect Control Theory explores how individuals maintain an orderly society through repeated actions. This primer delves into the theory's elements, the intellectual terrain of the 1960s, addressing questions on societal order, and the control principle. It also highlights the theory's scope conditio
0 views • 40 slides
Comprehensive Guide to Intelligence Gathering and Penetration Testing Stages
Understanding the importance of intelligence gathering in security and the stages of penetration testing - information gathering, scanning, exploitation, and reporting. Delve into tools like nslookup for server information and leverage Google Dorks for database vulnerabilities. Safeguard your system
0 views • 4 slides
Enhancing Insurance Penetration in Ghana Through Digital Innovation
Dr. Gideon Amenyedor explores how digital insurance can enhance insurance penetration in Ghana by leveraging technology to improve existing insurance models and create new ones. The strategic application of digital technology aims to address the low insurance penetration rate in the country by consi
0 views • 18 slides
Internet Overview in the Arab Region by ARISPA
The Arab Internet & Telecom Union (ARISPA) provides a detailed overview of internet penetration rates in the Arab region, focusing on global and regional comparisons, as well as the future IPv4 situation. Founded in 2006, ARISPA works under the Arab Economic Union Council, with 20 members representi
0 views • 17 slides
Essentials of Penetration Testing: Expectations and Performance
This presentation delves into the realm of penetration testing, outlining the basic expectations and performance aspects. It emphasizes the importance of clear planning, client-side and auditor-side negotiations, and commencing the audit process diligently. With insights into the types of audits, sc
0 views • 32 slides
Understanding Social Issues through Theory and Perspectives
Social theory is a system of interconnected ideas that organizes knowledge about the social world. It helps us analyze social problems like social pathology, disorganization, conflicts in values, and deviant behaviors. Differentiating theory, perspective, and model, it's key to note that theories pr
0 views • 37 slides
Understanding Social Neuroscience: Exploring Human Sociality and Well-Being
Social neuroscience delves into how the brain processes social interactions and their impact on human well-being. It focuses on the interconnectedness between social connections and overall life satisfaction, suggesting that humans are inherently social beings with a strong need for social belonging
2 views • 21 slides
Social Entrepreneurship and Social Inclusion in Bulgaria
The development and implementation of social entrepreneurship practices in Bulgaria aim to promote social inclusion through the development of the social economy. The focus is on combining economic results with social objectives, managed transparently with measurable, positive financial value. Vario
2 views • 12 slides
Theories of Interest in Microeconomics II
Explore various theories of interest in economics, including the Classical Theory, Liquidity Preference Theory by Keynes, Productivity Theory, Abstinence Theory, Time-Preference Theory, Fisher's Time Preference Theory, and the Loanable Fund Theory. These theories offer different perspectives on the
0 views • 6 slides
Understanding Armitage and Metasploit for Penetration Testing
Explore the capabilities of Armitage and Metasploit in penetration testing, comparing their attack styles, advantages, and limitations. Learn how Armitage simplifies the process by providing a GUI front-end for Metasploit, making it user-friendly for conducting machine-gun style attacks. Discover th
0 views • 16 slides
Social Justice as Fairness: The Theory of John Rawls
John Rawls' theory of justice focuses on addressing the inequalities in life prospects stemming from social starting positions. He argues that the basic structure of society must be the subject of justice regulation as it profoundly impacts individuals from the outset. Rawls emphasizes that social j
0 views • 10 slides
Challenges in Transitioning Austrian Energy System to High Wind Energy Penetration
The transition of Austria's energy system to embrace high wind energy penetration requires consideration of various factors such as economic incentives, costs, social norms, individual values, and beliefs. Through the TransWind project, research questions are examined, including the techno-economica
0 views • 15 slides
Exploring the Impact of Social Media on South Africa's Digital Landscape
South Africa has witnessed a significant increase in online access and social media usage, especially in light of the global pandemic. With 64% Internet penetration and 25 million social media users, the country ranks high in daily time spent on social media. This surge presents opportunities for or
0 views • 18 slides
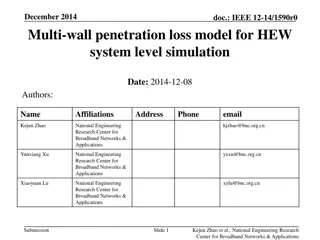
Analysis of Multi-Wall Penetration Loss Model for HEW System-Level Simulation
In December 2014, a multi-wall penetration loss model for HEW system-level simulation was proposed by Kejun Zhao, Yunxiang Xu, and Xiaoyuan Lu from the National Engineering Research Center for Broadband Networks & Applications. The model provides more accurate calculations of penetration loss in ind
0 views • 11 slides
Improving Penetration Testing Through Enhanced Input Vector Identification
Enhance your penetration testing efforts by improving information gathering and response analysis. This comprehensive guide explores various aspects of penetration testing, including information gathering, attack generation, and response analysis, offering valuable insights and strategies to bolster
0 views • 23 slides
Understanding Social Impact Theory Through Sedikides and Jackson (1990) Study
Explore Sedikides and Jackson's study on social impact theory, focusing on the variables manipulated and measured, along with their findings regarding Social Impact Number (SIN). Evaluate the study's support for the theory and its implications on factors like strength, immediacy, and number in socia
0 views • 18 slides