BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
National Food Processing Policy and Its Importance
National Food Processing Policy aims to address the significant wastage in food production through value addition and efficient processing. The policy highlights the reasons for food processing, including reducing losses in the supply chain and enhancing quality. It emphasizes creating an enabling e
1 views • 19 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
8 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
10 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Enhancing Security Definitions for Functional Encryption
This study delves into the realm of functional encryption (FE) against probabilistic queries, highlighting the necessity for improved security definitions to address existing limitations such as counter-intuitive examples and impossibility results. The exploration leads to proposing a new security n
4 views • 20 slides
Shielding Your Organization: Chief Security Officer Recruitment Insights
\"Shielding Your Organization: Chief Security Officer Recruitment Insights\" offers invaluable guidance for businesses seeking to fortify their security posture by recruiting the right Chief Security Officer (CSO). This comprehensive resource delves into the intricacies of chief security officer rec
1 views • 7 slides
Introduction to Spark Streaming for Large-Scale Stream Processing
Spark Streaming, developed at UC Berkeley, extends the capabilities of Apache Spark for large-scale, near-real-time stream processing. With the ability to scale to hundreds of nodes and achieve low latencies, Spark Streaming offers efficient and fault-tolerant stateful stream processing through a si
0 views • 30 slides
Real-Time Data Insights with Azure Databricks
Processing high-volume data in real-time can be achieved efficiently using Azure Databricks, a powerful Apache Spark-based analytics platform integrated with Microsoft Azure. By transitioning from batch processing to structured streaming, you can gain valuable real-time insights from your data, enab
0 views • 23 slides
Opportunities in Ethiopia's Agro-Processing Industry
Ethiopia stands out as a leader in raw material production for agro-processing industries, offering opportunities in dairy, juice processing, edible oil processing, poultry, beef production, and tomato processing. With abundant resources, suitable climate conditions, and a growing domestic market, E
2 views • 8 slides
Significance of Raw Materials in Food Processing
Effective selection of raw materials is crucial for ensuring the quality of processed food products. The quality of raw materials directly impacts the final products, making it important to procure materials that align closely with processing requirements. Quality evaluation, including microbiologic
2 views • 30 slides
Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
2 views • 17 slides
Unlocking Opportunities in Food and Agro-Processing in Nigeria
Explore the potential for food and agro-processing in Nigeria to generate income, enhance food security, and boost the economy. Learn about the objectives, strategies, and reasons behind agro-processing activities, as well as the growing demand for convenience and processed foods in the country. Dis
2 views • 46 slides
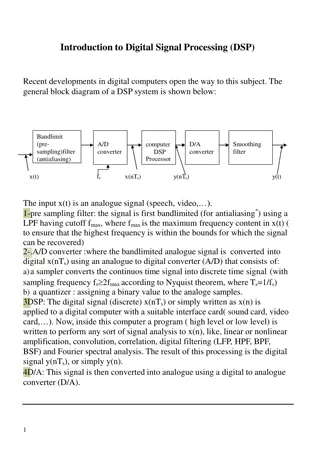
Overview of Digital Signal Processing (DSP) Systems and Implementations
Recent advancements in digital computers have paved the way for Digital Signal Processing (DSP). The DSP system involves bandlimiting, A/D conversion, DSP processing, D/A conversion, and smoothing filtering. This system enables the conversion of analog signals to digital, processing using digital co
1 views • 24 slides
Advancements in Signal Processing for ProtoDUNE Experiment
The team, including Xin Qian, Chao Zhang, and Brett Viren from BNL, leverages past experience in MicroBooNE to outline a comprehensive work plan for signal processing in ProtoDUNE. Their focus includes managing excess noise, addressing non-functional channels, and evolving signal processing techniqu
1 views • 23 slides
Sampling and Signal Processing Fundamentals
Sampling plays a crucial role in converting continuous-time signals into discrete-time signals for processing. This lecture covers periodic sampling, ideal sampling, Fourier transforms, Nyquist-Shannon sampling, and the processing of band-limited signals. It delves into the relationship between peri
1 views • 60 slides
Enhancing Near-Data Processing with Active Routing
Explore the implementation and benefits of Active-Routing for efficient data processing in memory networks. Motivated by the increasing demands for memory in graph processing and deep learning, this approach aims to reduce data movement, energy consumption, and costs associated with processing large
0 views • 46 slides
Real-Time Data-Driven Network Security Workshop by Joe St. Sauver
Explore the insightful workshop on batch versus flow processing in network security conducted by Joe St. Sauver from Farsight Security, Inc. The workshop delves into the dynamics of near-real-time security data analysis and its importance in today's cyber landscape. Joe's unique presentation style a
0 views • 84 slides
Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Overview of RNMRTK Software for NMR Data Processing
Rowland NMR Toolkit (RNMRTK) is a comprehensive software platform primarily used for NMR data processing tasks such as running MaxEnt, apodization, DFT processing, linear prediction, and more. It offers a robust set of tools for various processing needs and supports efficient parallel processing. RN
0 views • 17 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
1 views • 41 slides
Transaction Processing Systems (TPS)
Transaction Processing Systems (TPS) are vital components in capturing, storing, and processing data generated from various business transactions. They ensure efficient handling of high volumes of data while maintaining accuracy, security, and privacy. TPS operate through automated data entry, batch
0 views • 24 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Centre of Excellence in Signal Processing Activities and Progress Report
Broad areas of signal processing activities at the Centre of Excellence in Signal Processing include audio, speech, language, medical image processing, computer vision, wireless communications, and machine learning. The center focuses on addressing various challenges in audio/speech recognition, emo
0 views • 17 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Edge Computing for Optimizing Internet Devices
Edge computing brings computing closer to the data source, minimizing communication distances between client and server for reduced latency and bandwidth usage. Distributed in device nodes, edge computing optimizes processing in smart devices instead of centralized cloud environments, enhancing data
0 views • 32 slides
Multi-Processing in Computer Architecture
Beginning in the mid-2000s, a shift towards multi-processing emerged due to limitations in uniprocessor performance gains. This led to the development of multiprocessors like multicore systems, enabling enhanced performance through parallel processing. The taxonomy of Flynn categories, including SIS
0 views • 46 slides
Insight into PEPS Data Processing Architecture by Erwann Poupard
Erwann Poupard, a Software Ground System Engineer at CNES, Toulouse, France, plays a crucial role in the PEPS data processing architecture. The outline covers PEPS HPSS data storage statistics, current data processing trends, and future plans including PEPS V2 development. Explore PEPS processing ch
0 views • 8 slides
HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
1 views • 68 slides
Data Processing and Preprocessing Summary
In this document, Aymeric Sauvageon from CEA/DRF/Irfu/DAp presents a detailed overview of the preprocessing steps involved in data processing from L0 to L1. It covers the definition of L0/L1 and coding, utilization of the database for processing, input file specifications from China, packet content
0 views • 11 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
1 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
1 views • 5 slides
Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
Orleans Streaming Orleans Streaming
In this content, Orleans Streaming and real-life scenarios are discussed, highlighting the flexibility of stream processing logic, support for dynamic topologies, and fine-grained stream granularity. The content explores scenarios such as actor calls, IoT device event processing, chat room events, a
0 views • 17 slides
Automatic Security Testing for Linux Enhancement
In this paper, methods and technologies for automating security testing of Linux-based systems are discussed. The focus is on enhancing security through the implementation of least privilege mechanisms in the Linux environment. Various security modules and testing frameworks are explored to achieve
0 views • 16 slides
Introduction to Processing - The Basics
Processing, initiated by Ben Fry and Casey Reas at MIT Media Lab in 2001, is a Java-based platform designed for visual artists. It simplifies complex Java syntax for creating art. Processing incorporates numerous libraries for various purposes such as computer vision, data visualization, music compo
0 views • 32 slides