Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Line Segment Intersection
Geometric intersections play a crucial role in computational geometry for tasks such as solid modeling, collision detection in robotics, and overlaying subdivisions in geographic information systems. The problem of line segment intersection involves finding all intersection points between a set of c
0 views • 17 slides
Managed Security Services Market to be Worth $75.1 Billion by 2030
\u2018Managed Security Services Market by Service Type (Managed Detection and Response, Managed Identity and Access Management), Security Type (Cloud Security, Endpoint Security), Sector (BFSI, and Healthcare), and Geography - Global Forecast to 2030.\u2019
4 views • 3 slides
Managed Security Services Market to Reach $75.1 Billion by 2030
Managed Security Services Market by Type (Managed Detection and Response, Managed Identity and Access Management), Security Type (Cloud Security, Endpoint Security), Sector (BFSI, and Healthcare), and Geography\u2014Global Forecast to 2030.\u2019\n
0 views • 6 slides
Understanding Line Sweep Algorithms in Geometry
Line sweep algorithms are a powerful tool for solving geometry problems by simulating the sweeping of a vertical line across a plane. This approach allows for efficient processing of important points and addressing various geometric challenges, such as finding the closest pair of points, determining
2 views • 10 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Understanding Performance of Transmission Lines in Electrical Engineering
The performance of a transmission line in power systems is critical for efficient operation. Factors such as voltage drop, line losses, and transmission efficiency are key considerations in design and operation. The line parameters of resistance, inductance, capacitance, and shunt conductance play c
2 views • 26 slides
Visualizing Real Numbers on a Number Line by Successive Magnification
Visualization techniques for representing real numbers on a number line through successive magnification are demonstrated step by step. The procedure involves dividing the line into equal parts and zooming in on specific ranges to accurately locate decimal values. This method helps in understanding
0 views • 12 slides
Visualizing Real Numbers on a Number Line
The procedure of representing real numbers on a number line through successive magnification is explained in detail. It involves dividing the line, marking points, and magnifying specific intervals to accurately position numbers like 5.2316. Each real number corresponds to a unique point on the numb
0 views • 12 slides
Exploring Geometry Vocabulary with Mr. Fiore & Mr. Ryan
Geometry, the study of shapes, has its roots in Ancient Mesopotamia and Ancient Egypt. Concepts such as point, line, ray, endpoint, line segment, vertex, congruent, vertical line, horizontal line, and plane are essential in understanding geometric relationships and structures. This visual guide prov
0 views • 22 slides
Understanding Line and Staff Authority in Organizational Structure
Line authority flows from top to bottom in an organization, while staff authority is provided by specialists to advise line managers. Staff members offer expert advice and support to enhance the efficiency of line officials. Different types of staff positions exist, such as personal staff, specializ
0 views • 5 slides
Understanding Least-Squares Regression Line in Statistics
The concept of the least-squares regression line is crucial in statistics for predicting values based on two-variable data. This regression line minimizes the sum of squared residuals, aiming to make predicted values as close as possible to actual values. By calculating the regression line using tec
0 views • 15 slides
Maternity Leave Guidance for Line Managers at the University
The Maternity Leave Guidance for Line Managers at the University emphasizes compassion and support for expectant mothers. It outlines essential steps for line managers before, during, and after maternity leave, including notifying HR of pregnancy, conducting risk assessments, discussing leave plans,
0 views • 8 slides
Understanding Energy Distribution System Line Models
This presentation delves into the various line models used in energy distribution systems, including exact line segment models and their derivation from Kirchhoff's voltage and current laws. The discussion covers three line segment models, the computation of phase impedance and admittance matrices,
0 views • 44 slides
Understanding Line Graphs: Year 6 Lesson Overview
This document provides an introduction to interpreting line graphs for Year 6 students. It covers key concepts, reviews essential skills, explores precise mathematical vocabulary, and includes lesson clips on right angles and perpendicular lines. The journey through the lesson involves a focus on pe
0 views • 26 slides
Managed Security Services Market: How SMEs are Adopting MSS for Enhanced Cyberse
Managed Security Services Market by Service Type (Managed Detection and Response, Managed Identity and Access Management), Security Type (Cloud Security, Endpoint Security), Sector (BFSI, and Healthcare), and Geography - Global Forecast to 2030\n
0 views • 3 slides
Efficient Line Segment Intersection Algorithm
This content discusses the Line Segment Intersection problem and presents an efficient algorithm using the line sweep technique. The algorithm utilizes ordered sets implemented as balanced search trees to efficiently determine if any two line segments intersect in the plane. By sorting endpoints and
0 views • 10 slides
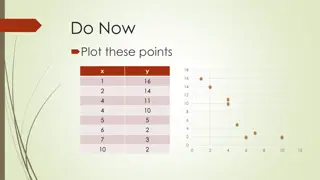
Understanding Line of Fit in Data Analysis
Line of fit is used in data analysis to model data with an approximate linear relationship. Through examples, you can learn how to find a line of fit, create scatter plots, sketch fitting lines, and estimate values based on the line of fit equation.
1 views • 13 slides
Understanding Market Research for Business Success
Market research is crucial for businesses to gather information about their target market, customer needs, competition, and market trends. Primary and secondary research methods, market share analysis, demand assessment, and calculating market size are key aspects discussed in this content. Various
1 views • 5 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Understanding Pole and Line Fishing Methods and Gear
Pole and line fishing is a traditional method involving a hooked line attached to a pole. This technique is commonly used for both sport fishing and commercial fisheries. Learn about the gear types, target species, vessel types, and auxiliary equipment used in pole and line fishing. Discover the spe
0 views • 10 slides
Talk-Line: A Helpline for Students in Grades 3-5
Talk-Line is a resource available for students in Grades 3-5 who are experiencing thoughts of self-harm, being harmed by others, or needing help. This service provides a safe space for students to talk to a trained listener for support and assistance. It is essential for students to reach out to tru
0 views • 12 slides
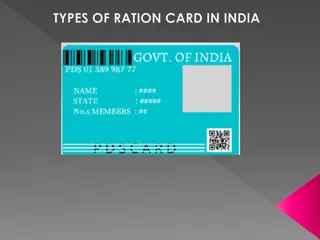
Types of Ration Cards in India and Their Benefits
In India, there are 5 types of ration cards - Priority Household (PHH), Antyodaya (AAY), APL (Above Poverty Line), BPL (Below Poverty Line), and AAY (Antyodaya). Each card serves a specific category of households, providing different amounts of food grain allocation per month. The PHH card is for el
0 views • 8 slides
THVD8000 Line Driver for AC Line PLC Bench Setup
Explore the setup of THVD8000 line driver for AC line PLC, including transmitting and receiving paths, signal flow, power distribution, and components involved. Follow the signal path from THVD8000EVM to AFE031 boostpack, transformer, HV capacitor, and UCC28880EVM. Understand the power flow from AC
0 views • 11 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
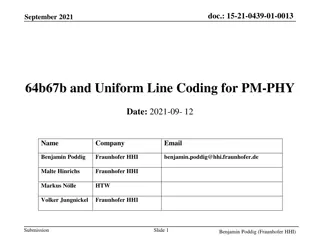
Optimizing Line Coding for PM-PHY: A Detailed Analysis
Enabling line coding and channel equalization methods for PM-PHY, the IEEE 802.15.13 standard introduces overhead while enhancing channel adaptation. This contribution proposes 64b67b and Uniform Line Coding as alternative transmission modes, aiming to reduce line coding overhead while maintaining a
0 views • 26 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Understanding BCG Matrix: Market Growth and Relative Market Share
BCG Matrix, developed by Bruce Henderson of the Boston Consulting Group, categorizes business units into Question Marks, Stars, Cash Cows, and Dogs based on market growth and relative market share. Market share and market growth are crucial factors in determining a company's position in the market.
0 views • 31 slides
Difference Between Capital Market and Money Market: A Comprehensive Overview
The capital market and money market serve different purposes in the financial world. While the capital market provides funds for long-term investments in securities like stocks and debentures, the money market deals with short-term borrowing and lending of funds. The capital market acts as a middlem
0 views • 4 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides