Circle of Security-Parenting: Enhancing Attachment for Child Development
The Circle of Security-Parenting program, an attachment-based intervention that supports children's mental health. Discover the benefits of secure attachment and understand the different types of insecure attachment. Find out how the program helps caregivers meet their child's attachment needs and r
31 views • 12 slides
Understanding Secure Act 2.0 Key Provisions
In a detailed report by Dee Spivey and Angie Zouhar, key provisions of SECURE Act 2.0 are outlined, including changes in retirement plans like RMD age increase, employee certification of hardship withdrawals, and more. Secure 1.0 and Secure 2.0 differences, effective dates, and necessary actions for
5 views • 12 slides
Modern Perspectives on Attachment Theory: Bridging Research and Practice
Delve into the contemporary developments in attachment theory within social work and education. Explore how practitioners and researchers are navigating outdated notions and embracing newer insights to enhance their understanding and application of attachment concepts.
1 views • 16 slides
Understanding Autism Spectrum Disorder and Attachment: Insights from the Coventry Grid
Exploring the commonalities, desired outcomes, concerns leading to assessment, and the Coventry Grid regarding autism spectrum disorder and attachment. The Coventry Grid highlights the lack of flexibility of thought and behavior in individuals with ASD, emphasizing the importance of predictability,
0 views • 50 slides
Introduction to SFTP & PGP Encryption for Secure Data Transfer
Discover how to ensure reliable data transfer, make informed decisions, and gain a strategic advantage through the use of Secure File Transfer Protocol (SFTP) and Pretty Good Privacy (PGP) encryption. The session includes demonstrations on PGP encryption and SFTP access, along with insights on setti
1 views • 22 slides
Ensuring Secure Testing Environments in Oregon Education System
Oregon's Statewide Assessment System (OSAS) emphasizes the critical need for secure testing environments to maintain the validity and accuracy of assessment data. This includes handling secure printed test materials, identifying and preventing improprieties, and reporting any irregularities. From ma
2 views • 20 slides
Understanding Love Styles in Relationships Based on Attachment Theory
Early life experiences play a crucial role in shaping how we love in relationships. Milan and Kay Yerkovich have developed tools rooted in attachment theory to help individuals understand and improve their love styles. People tend to fall into five categories of Love Styles, such as the Avoider, who
1 views • 22 slides
Secure Computation Techniques in RAM Models with Efficient Automation
Explore the automation of efficient RAM-model secure computation techniques, including examples such as secure binary search. Discover how traditional solutions using circuit abstractions can be improved for sub-linear time computation through methods like Oblivious RAM. Learn about techniques such
0 views • 37 slides
Understanding Adenoviruses: Structure, Replication, and Epidemiology
Adenoviruses, known for causing respiratory infections, have at least 41 serotypes categorized into 6 subgenera. Their structure includes 252 capsomeres, 240 hexons, and specific proteins for attachment. The replication involves virus attachment, penetration, uncoating, and transportation of viral D
0 views • 22 slides
Understanding Sternberg's Triangular Theory of Love and Attachment Styles
Sternberg's Triangular Theory of Love defines the key dimensions of a healthy romantic relationship as intimacy, passion, and commitment. These components play vital roles in shaping relationships and can be influenced by attachment styles developed in infancy. Secure attachment leads to greater rel
1 views • 19 slides
Understanding Attachment, Trauma, and Life Stories in EMDR Therapy
Explore the impact of attachment-related trauma on adult attachment classifications, the significance of life stories in shaping our present, and how EMDR therapy helps individuals make sense of challenging childhood experiences to create a coherent narrative for healing and growth.
0 views • 66 slides
Tamper-Evident Pairing (TEP) Protocol for Secure Wireless Pairing Without Passwords
This article discusses the challenges of traditional secure wireless pairing methods that rely on password validation and proposes the Tamper-Evident Pairing (TEP) protocol as a secure in-band solution to protect against Man-in-the-Middle (MITM) attacks. TEP eliminates the need for out-of-band chann
1 views • 40 slides
Understanding Infant Attachment Through the Strange Situation Experiment
The Strange Situation experiment conducted by Mary Ainsworth et al. in 1978 aimed to describe and evaluate the attachment relationship between caregivers and infants. The study involved observing caregiver-infant interactions through separations and reunions to classify attachment types such as secu
1 views • 6 slides
Actively Secure Arithmetic Computation and VOLE Study
Exploring actively secure arithmetic computation and VOLE with constant computational overhead at Tel Aviv University. Understanding how functions are represented in secure computation using arithmetic circuits over boolean circuits. Efficiently evaluating arithmetic circuits over large finite field
0 views • 36 slides
Understanding ARC: Attachment, Regulation, and Competency in Trauma Care
Explore the world of ARC (Attachment, Regulation, and Competency) in trauma care, a framework designed for working with children and teens affected by trauma. Learn about the core principles of ARC, its focus on strengthening relationships, enhancing self-regulation, and building resilience. Discove
0 views • 20 slides
Insights into Attachment Theory and Clinical Implications
Explore the clinical implications of attachment theory, as discussed by Miriam Steele and Bowlby, highlighting how early attachment patterns persist into adulthood and influence relationships. Learn about the Strange Situation test, Adult Attachment Interview, and intergenerational patterns of attac
0 views • 34 slides
Accessing and Utilizing CPCSSN Secure Research Environment (SRE)
Learn how to access the CPCSSN Secure Research Environment (SRE) for secure data analysis. Follow steps such as setting up VPN, accessing SQL databases, and establishing ODBC connections for statistical analysis using tools like SAS, R, SPSS, or Stata. Enhance your research capabilities within a sec
0 views • 12 slides
Understanding Attachment Theory in Developmental Psychology
Attachment theory in developmental psychology, pioneered by Bowlby and Ainsworth, examines the emotional bonds between infants and caregivers. It delves into phases of attachment development, key components, and evaluation methods such as the Strange Situation Procedure. The theory emphasizes the si
0 views • 13 slides
Rochester Public Utilities Presentation on True-up of Attachment O Transmission Revenue Requirements
Rochester Public Utilities (RPU) holds annual meetings to discuss and provide information on the calculation of the True-up of RPU's 2016 Annual Transmission Revenue Requirements. The presentation also covers the True-up Adjustment applied to the 2018 Forward-Looking Rate. RPU uses a FERC-approved F
0 views • 14 slides
Enhancing Animal Telemetry Data Systems for Secure Collaboration
Wide spectrum of animal telemetry data collection protocols and platforms require enhanced data stewardship options for secure sharing before public release. The need for a more granular understanding of available data and structured systems integration is crucial. Initial workflow involves providin
0 views • 4 slides
Looking for a Drill Saw Attachment? How Can It Transform Your Drill into a Power
If you're seeking versatility and efficiency in your toolkit, a drill saw attachment might be the perfect solution. This innovative accessory transforms your standard drill into a powerful cutting tool, allowing you to handle a range of tasks with ea
0 views • 4 slides
Looking for a Drill Saw Attachment? How Can It Transform Your Drill into a Power
If you're seeking versatility and efficiency in your toolkit, a drill saw attachment might be the perfect solution. This innovative accessory transforms your standard drill into a powerful cutting tool, allowing you to handle a range of tasks with ea
6 views • 4 slides
Attachment Wizard and File Management: A Comprehensive Guide for Efficient Workflows
Empower yourself with the knowledge and tools presented in this guide to effectively manage files, streamline attachments, and optimize your workflow. Discover best practices, learn about file naming conventions, explore different attachment methods, and enhance your productivity through expert tips
0 views • 12 slides
Understanding Canine Attachment and Cross-Species Relationships
Dogs exhibit strong social attachment to humans, forming enduring bonds that serve as a secure base. This attachment benefits both organisms, providing resources for survival and establishing social structures. Imprinting studies suggest that animals, like humans, develop proximity-seeking behaviors
0 views • 29 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
0 views • 12 slides
Understanding Secure Electronic Transactions (SET)
Secure Electronic Transactions (SET) is an encryption and security specification designed to protect credit card transactions on the Internet. SET provides a secure way to utilize existing credit card payment infrastructure on open networks, such as the Internet, involving participants like clients,
1 views • 6 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Exploring Secure Care Services in Scotland
Delve into the world of secure care services in Scotland, focusing on achievements, challenges, and opportunities in providing youth justice. Learn about trends in secure care, reduction in costs, reasons for referrals, and evidence-based programs like DBT in Glasgow. Gain insights from industry lea
0 views • 77 slides
Understanding Secure PRFs and PRPs in Cryptography
Dive into the world of secure Pseudo-Random Functions (PRFs) and Pseudo-Random Permutations (PRPs) in cryptography. Learn about the definitions, security criteria, and examples of secure PRFs and PRPs such as 3DES and AES. Explore the concepts of secure block ciphers and key principles behind these
0 views • 54 slides
Understanding Wire Ropes for Flexible Load Handling Attachment
Wire ropes offer advantages over chains for flexible load handling attachment, such as lighter weight, less damage susceptibility from jerks, silent operation, and greater reliability. They consist of multiple wires or strands wound about an axis, with independent components interacting during servi
0 views • 17 slides
The Power of Social Connection: Understanding Human Nature
This collection of content emphasizes the importance of social connection in human society, exploring why people are social animals and the benefits of being social. It delves into dimensions of our ultra-social behavior, early life experiences, attachment styles like secure attachment, and the impa
0 views • 30 slides
Impact of Sexually Coercive Attitudes on Adolescent Relationships
Research explores the development of sexually coercive attitudes in adolescence and their effects on romantic relationship functioning. The KLIFF study, a 20-year longitudinal investigation, tracks 184 individuals from age 13, examining attachment with parents, peers, and partners. Secure, anxious,
0 views • 16 slides
Understanding Attachment, Addiction, and Defense Mechanisms in Family Therapy
Exploring the intricate relationship between attachment experiences, addiction patterns, and defense mechanisms in family therapy. Recognizing the impact of family history, stressors, and psychological responses on secure attachments, optimal brain functioning, and successful treatment outcomes.
0 views • 30 slides
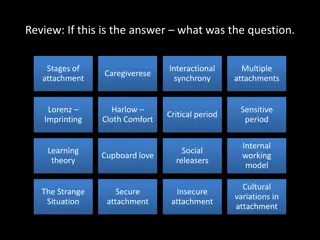
Understanding Bowlby's Attachment Theory: A Comprehensive Overview
This content provides an in-depth exploration of Bowlby's Attachment Theory, covering key concepts such as stages of attachment, interactional synchrony, multiple attachments, imprinting, secure and insecure attachment styles, and the impact of maternal deprivation. It also delves into short-term an
0 views • 22 slides
Understanding the Significance of Attachment in Supporting Vulnerable Children
Attachment plays a crucial role in the well-being of children, especially those in care. It influences their emotional and behavioral responses, impacting their overall development. This content emphasizes the importance of providing proper support and attachment relationships for children facing ad
0 views • 24 slides
Exploring the Nurture Group Approach and Attachment Theory
Delve into the Nurture Group Approach and Attachment Theory, examining the key ideas and theorists involved. Secure attachment and its evolutionary significance in fostering healthy relationships are highlighted. The importance of warm, continuous caregiver relationships in child development is emph
0 views • 29 slides
Understanding Attachment in Young Children and Caregivers
Attachment plays a crucial role in the development of young children, shaping their sense of security and emotional well-being. Secure relationships help children manage emotions and foster healthy identities, while insecure attachments may lead to behaviors like inhibition of exploration and diffic
0 views • 12 slides
Foundations of Cryptography: Secure Multiparty Computation
Explore the foundations of cryptography with insights into secure multiparty computation, including the Secure 2PC from OT Theorem and the Two-Party Impossibility Theorem. Delve into the impossibility of 2-Party Secure MPC, claims, and exercises on extending to statistical security. Learn about redu
0 views • 39 slides
Understanding Attachment Trauma and Healing Process
Attachment trauma involves disruptions in forming bonds, leading to complex trauma that affects neurological development. Therapy aims to create compassionate healing opportunities for individuals struggling with attachment-based trauma, addressing both big and little "t" traumas to increase emotion
0 views • 37 slides
Understanding Secure Messaging and Encryption Techniques
Explore the possibilities of sending secure messages through encryption without the need for advanced degrees in Computer Science or Math. Learn about symmetric and asymmetric key encryption methods, the use of PGP for secure messaging, and the concept of shared-key encryption. Discover the intricac
0 views • 16 slides