Algorithm Analysis
Algorithm analysis involves evaluating the efficiency of algorithms through measures such as time and memory complexity. This analysis helps in comparing different algorithms, understanding how time scales with input size, and predicting performance as input size approaches infinity. Scaling analysi
1 views • 30 slides
OCTIVUS Randomized Clinical Trial: OCT-Guided vs IVUS-Guided PCI
The OCTIVUS Randomized Clinical Trial compared the clinical efficacy and safety of Optical Coherence Tomography (OCT)-guided and Intravascular Ultrasound (IVUS)-guided strategies in patients undergoing PCI for significant CAD. The study aimed to determine if OCT-guided PCI is noninferior to IVUS-gui
8 views • 27 slides
Understanding Booth's Algorithm for Binary Integer Division
Learn about Booth's Algorithm and how it facilitates binary integer division. Discover key points to remember when using the algorithm, steps to initiate the process, and a detailed example to illustrate the multiplication of two operands using Booth's Algorithm.
1 views • 42 slides
Discussion of Randomized Experiments and Experimental Design Challenges
Randomized experiments face statistical power challenges due to rare outcomes and high variance. Stratifying randomization can help control for correlated residual variance based on baseline values of outcomes. Implications for applied economists include addressing attrition and treatment effect het
0 views • 6 slides
Understanding Stable Matchings and the Gale-Shapley Algorithm
The concept of stable matchings is explored, along with the Gale-Shapley algorithm for finding them efficiently. Key ideas and steps of the algorithm are explained, supported by visuals. The process, examples, and observations related to the algorithm's effectiveness are discussed, highlighting the
1 views • 29 slides
Ricart and Agrawala's Algorithm for Mutual Exclusion
The Ricart-Agrawala Algorithm is a distributed system algorithm for achieving mutual exclusion without the need for release messages, developed by Glenn Ricart and Ashok Agrawala. The algorithm involves processes sending timestamped requests to enter a critical section, with careful handling of repl
1 views • 16 slides
Understanding Algorithm Efficiency Analysis
In this chapter, Dr. Maram Bani Younes delves into the analysis of algorithm efficiency, focusing on aspects such as order of growth, best case scenarios, and empirical analysis of time efficiency. The dimensions of generality, simplicity, time efficiency, and space efficiency are explored, with a d
1 views • 28 slides
Biometrical Techniques in Animal Breeding: Analysis of Variance in Completely Randomized Design
Biometrical techniques in animal breeding involve the use of analysis of variance (ANOVA) to partition total variance into different components attributable to various factors. In completely randomized designs, experimental units are randomly assigned to treatments, ensuring homogeneity. The total n
0 views • 34 slides
Understanding Lamport Algorithm for Mutual Exclusion
Lamport Algorithm, presented by Prafulla Santosh Patil, is a permission-based algorithm utilizing timestamps to order critical section requests and resolve conflicts. It employs three types of messages: REQUEST, REPLY, and RELEASE, where each site manages a queue to store requests. By ensuring commu
0 views • 15 slides
Analysis of Variance in Completely Randomized Design
This content covers the analysis of variance in a completely randomized design, focusing on comparing more than two groups with numeric responses. It explains the statistical methods used to compare groups in controlled experiments and observational studies. The content includes information on 1-way
0 views • 48 slides
Digital Differential Analyzer (DDA) Algorithm in Computer Graphics
In computer graphics, the Digital Differential Analyzer (DDA) Algorithm is utilized as the basic line drawing algorithm. This method involves interpolation of variables between two endpoints to rasterize lines, triangles, and polygons efficiently. The algorithm requires inputting coordinates of two
0 views • 9 slides
Understanding Randomized Hill Climbing Algorithm for Challenging Problem Solving
Randomized Hill Climbing is a versatile approach to solving complex problems by sampling points in the neighborhood of the current best solution. This method is easy to apply, resource-efficient, and usually fast. However, defining the neighborhood and choosing appropriate parameters can pose challe
4 views • 14 slides
ACST-2 Trial: Stenting vs. Surgery for Carotid Artery Stenosis
ACST-2 is a randomized trial comparing carotid artery stenting (CAS) versus carotid artery surgery (CEA) in asymptomatic patients with severe carotid stenosis. The trial, published in The Lancet in August 2021, involved 3625 patients. While surgery has been shown to reduce stroke rates, modern medic
0 views • 19 slides
Understanding Randomized Algorithms: Types and Examples
Explore the world of randomized algorithms through types like Las Vegas and Monte Carlo, with a focus on classic examples such as Quick Sort. Learn how randomness plays a crucial role in computation and discover the principles behind these algorithms. Dive into the applications of randomized algorit
0 views • 22 slides
Understanding Randomized Algorithms: A Deep Dive into Las Vegas and Monte Carlo Algorithms
Randomized algorithms incorporate randomness into computations, with Las Vegas algorithms always providing the correct answer but varying in time, while Monte Carlo algorithms occasionally give wrong answers. Quick Sort is a classic Las Vegas algorithm that involves pivoting elements for sorting. Ch
4 views • 21 slides
Overview of Mutual Exclusion and Memory Models in Distributed Systems
Discussion on fast, randomized mutual exclusion techniques by George Giakkoupis and Philipp Woelfel. Exploring asynchronous shared memory systems with atomic operations. Understanding mutual exclusion principles as outlined by Dijkstra in 1965 and measuring time efficiency in critical sections. Delv
2 views • 23 slides
Enhancing Privacy with Randomized MAC Addresses in 802.11 Networks
This presentation discusses the use of randomized MAC addresses as a privacy-enhancing measure in 802.11 networks. Passive observation of MAC addresses poses privacy risks, and the proposal suggests assigning random MAC addresses to portable devices to mitigate tracking risks. By periodically changi
0 views • 10 slides
Electronic Case Report Form (eCRF) for Randomized Trial of Enteral Glutamine to Minimize Thermal Injury
Development of case report form worksheets for data collection in a randomized trial focusing on enteral glutamine use to minimize thermal injury. The document provides detailed instructions for research coordinators on data recording from medical charts to be entered into the electronic data captur
1 views • 61 slides
Grey Wolf Optimizer: A Nature-Inspired Optimization Algorithm
The Grey Wolf Optimizer algorithm is based on the social hierarchy of grey wolves in the wild. Inspired by the pack behavior of grey wolves, this algorithm utilizes alpha, beta, and delta solutions to guide the optimization process. The hunting phases of tracking, pursuing, and attacking prey mimic
3 views • 16 slides
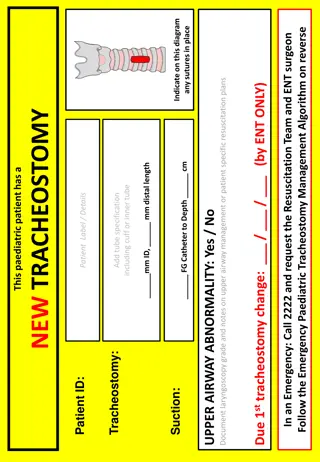
Emergency Paediatric Tracheostomy Management Algorithm
Emergency Paediatric Tracheostomy Management Algorithm provides a structured approach for managing pediatric patients requiring tracheostomy in emergency situations. The algorithm outlines steps for assessing airway patency, performing suction, and changing the tracheostomy tube if necessary. It emp
0 views • 4 slides
Development of Satellite Passive Microwave Snowfall Detection Algorithm
This study focuses on the development of a satellite passive microwave snowfall detection algorithm, highlighting the challenges in accurately determining snowfall using satellite instruments. The algorithm uses data from AMSU/MHS, ATMS, and SSMIS sensors to generate snowfall rate estimates, overcom
0 views • 20 slides
Expected Duration of a Randomized Experiment: Coupon Collector Problem Analysis
Explore the fascinating Coupon Collector Problem, where distinct coupons are randomly selected from a bag until each has appeared at least once. Dive into the analysis of the expected number of iterations required for all coupons to be collected, shedding light on the gradual transition through disc
0 views • 33 slides
Understanding Euclid's Algorithm: An Ancient Approach to Finding Greatest Common Divisors
Euclid's Algorithm, dating back 2500 years, offers a simpler method to find the greatest common divisor (gcd) of two non-negative integers compared to traditional factorization. By iteratively applying a rule based on the gcd of remainders, it efficiently computes gcd values. The basis of the algori
0 views • 15 slides
GPU Accelerated Algorithm for 3D Delaunay Triangulation
Thanh-Tung Cao, Todd Mingcen Gao, Tiow-Seng Tan, and Ashwin Nanjappa from the National University of Singapore's Bioinformatics Institute present a GPU-accelerated algorithm for 3D Delaunay triangulation. Their work explores the background, related works, algorithm implementation, and results of thi
0 views • 24 slides
Cuckoo Search: A Nature-Inspired Optimization Algorithm
Cuckoo Search (CS) algorithm, developed in 2009, mimics the brood parasitism of cuckoo species and utilizes Lévy flights for efficient optimization. This algorithm has shown promise in outperforming other traditional methods like PSO and genetic algorithms. The behavior of cuckoos in laying eggs an
0 views • 25 slides
BiGraph: Bipartite-Oriented Distributed Graph Partitioning for Big Learning
BiGraph is a distributed graph partitioning algorithm designed for bipartite graphs, offering a scalable solution for big data processing in Machine Learning and Data Mining applications. The algorithm addresses the limitations of existing partitioning methods by efficiently distributing and managin
0 views • 45 slides
Ford-Fulkerson Algorithm for Maximum Flow in Networks
The Ford-Fulkerson algorithm is used to find the maximum flow in a network by iteratively pushing flow along paths and updating residual capacities until no more augmenting paths are found. This algorithm is crucial for solving flow network problems, such as finding min-cuts and max-flow. By modelin
0 views • 26 slides
Advanced Encoding Techniques in Randomized Algorithms
Explore innovative approaches in randomized algorithms through techniques such as perfect memory, efficient card guessing strategies, and polynomial encoding methods over finite fields. Learn how to optimize memory usage and enhance predictive capabilities in algorithmic processes.
0 views • 41 slides
3GPP Voting Rights Algorithm: Contiguous-3 Solution Evaluation
This evaluation delves into the advantages and disadvantages of the 3 Contiguous-3 solution within the 3GPP voting rights algorithm. It explores scenarios to test the algorithm's effectiveness in granting and revoking voting rights based on meeting attendance types. The evaluation includes diverse h
0 views • 10 slides
Introduction to Algorithm Analysis and Complexity in Computer Science
Algorithm analysis is crucial in determining the efficiency of programs by analyzing resource usage such as time and space. This involves comparing programs, understanding data structures, and evaluating algorithm performance. Efficiency is key as program execution time depends on various factors be
0 views • 66 slides
Understanding Probabilistic Concurrency Testing for Bug Detection
Explore the concept of probabilistic concurrency testing and how randomized scheduling algorithms can help detect bugs efficiently. Learn about bug depth, randomized algorithms, and the development of PCT to improve the effectiveness of stress testing tools like Cuzz.
0 views • 23 slides
Challenges and Solutions in Concurrency Testing with Randomized Algorithms
Concurrency testing in complex cloud services presents challenges such as bugs, performance problems, and data loss. Randomized algorithms, like Probabilistic Concurrency Testing (PCT), offer effective bug-finding solutions. PCT provides probabilistic guarantees and scalable bug detection for distri
0 views • 37 slides
Bresenham Line Drawing Algorithm Explained with Examples
Bresenham Line Drawing Algorithm is a method used to generate points between starting and ending coordinates to draw lines efficiently. This algorithm involves calculating parameters, decision parameters, and iteratively finding points along the line. Two example problems are provided with step-by-s
0 views • 8 slides
Algorithm Strategies: Greedy Algorithms and the Coin-changing Problem
This topic delves into general algorithm strategies, focusing on the concept of greedy algorithms where locally optimal choices are made with the hope of finding a globally optimal solution. The discussion includes the nature of greedy algorithms, examples such as Dijkstra's algorithm and Prim's alg
0 views • 91 slides
Stable Matching Problem and Gale-Shapley Algorithm Overview
The content provides information on the stable matching problem and the Gale-Shapley algorithm. It covers the definition of stable matching, the workings of the Gale-Shapley algorithm, tips for algorithm implementation, and common questions related to the topic. The content also includes a summary o
0 views • 16 slides
Understanding Deutsch's Algorithm in Quantum Computing
Deutsch's Algorithm is a fundamental quantum algorithm designed to solve the problem of determining if a given function is constant or balanced. This algorithm leverages quantum principles such as superposition and entanglement to provide a more efficient solution compared to classical methods. By e
0 views • 17 slides
Algorithm for Determining Endpoints in Speech Recognition
This article discusses an algorithm proposed by L.R. Rabiner and M.R. Sambur in 1975 for determining endpoints in isolated utterances. The algorithm focuses on detecting word boundaries in speech through the recognition of silence, which can lead to reduced processing load and increased convenience,
0 views • 22 slides
Randomized Algorithms for Approximate Median with Elementary Probability
This content covers a lecture on a randomized algorithm for finding an approximate median element using elementary probability theory. It discusses the importance of insight and basic probability in designing and analyzing such algorithms. The lecture presents a simple probability exercise involving
0 views • 25 slides
Time-space Tradeoffs and Optimizations in BKW Algorithm
Time-space tradeoffs and optimizations play a crucial role in the BKW algorithm, particularly in scenarios like learning parity with noise (LPN) and BKW algorithm iterations. The non-heuristic approach in addressing these tradeoffs is discussed in relation to the hardness of the LPN problem and the
0 views • 14 slides
Forty-eight-Week Outcomes of a Site-Randomized Trial for Depression Among Youth with HIV
This study explores the outcomes of a site-randomized trial utilizing a combined cognitive behavioral therapy and medication management algorithm for treating depression among youth with HIV in the U.S. The team involved includes medical officers, data managers, statisticians, clinical trial special
0 views • 22 slides