Budget Execution Challenges in Somalia's Social Sectors
Addressing malnutrition in Somalia is hindered by low budget execution rates in the health and education sectors. Only a small portion of Official Development Assistance (ODA) is channeled through government systems, impacting service delivery and development financing. Donor-supported budgets for h
0 views • 32 slides
PUMM: Preventing Use-After-Free Using Execution Unit Partitioning
Memory-unsafe languages like C and C++ are prone to Use-After-Free (UAF) vulnerabilities. PUMM introduces execution unit partitioning to efficiently tackle this issue. By segregating and managing execution units, PUMM aims to prevent UAF exploits and enhance software security.
0 views • 31 slides
Optimizing Minimum Order Quantity Strategies for Supply Chain Success
Welcome to our presentation on \"Minimum Order Quantity (MOQ): Optimizing Supply Chain Efficiency.\" In today's dynamic business environment, managing inventory effectively is crucial for businesses to minimize costs and maximize profitability. One key aspect of inventory management is determining t
7 views • 7 slides
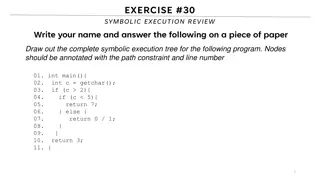
Symbolic Execution Tree for a Program
Generate the complete symbolic execution tree for a given program by annotating nodes with path constraints and line numbers, aiding in understanding program execution flow.
0 views • 26 slides
Order food online jensen beach
Do you fancy genuine\u00ad Italian food in Jensen Beach? Nonna's Italian Eate\u00adry is best order food online jensen beach. This gem, located in the\u00ad picturesque cente\u00adr of town, offers a menu filled with Italian classics\u2014from tasty, rich pastas and pe\u00adrfect pizzas to crisp sal
1 views • 6 slides
Understanding Memory Ordering in Programming
Memory ordering in programming is crucial for developers to understand, as it dictates the sequence of memory operations at different levels - source code, program order, and execution order. Compiler optimizations and reordering of memory accesses can impact how code is executed by the processor, e
1 views • 30 slides
Understanding the Neglected Provisions of Order XXI CPC, 1908
Explore the overlooked aspects of Order XXI CPC, 1908, focusing on the definitions, types of decrees, modes of execution, procedures for executing decrees, reasons for neglect, impact, recommendations, and conclusion. Learn about neglected provisions like summary execution, execution against legal r
0 views • 14 slides
Understanding Software Testing: Test Cases, Selection, and Execution
Software testing plays a crucial role in identifying and resolving issues within software products. Test cases, selection, and execution are fundamental aspects of the testing process. Test cases define conditions for testing software functionality, with a focus on repeatability and data specificity
2 views • 36 slides
Understanding Properties of Database Transactions
Database transactions play a crucial role in ensuring data integrity and consistency within a database system. This content explores the fundamental properties of transactions, such as atomicity, durability, consistency, and isolation. It delves into the requirements and implications of each propert
2 views • 44 slides
Understanding Spiritual Assistance in the Secular Franciscan Order
The nature of spiritual assistance in the Secular Franciscan Order, as outlined by Michael J. Higgins, TOR, and Benedetto Lino, OFS, delves into the core elements of providing spiritual and pastoral guidance to members. It highlights the duties, structure, and supervision within the Order, emphasizi
0 views • 30 slides
Optimization Methods: Understanding Gradient Descent and Second Order Techniques
This content delves into the concepts of gradient descent and second-order methods in optimization. Gradient descent is a first-order method utilizing the first-order Taylor expansion, while second-order methods consider the first three terms of the multivariate Taylor series. Second-order methods l
0 views • 44 slides
FERC Order 844 Compliance: Uplift Cost Allocation and Transparency
FERC Order 844, issued in April 2018, mandates reporting on uplift payments and unit commitments, along with revising tariff language for compliance. ISO-NE is proposing new reports and tariff revisions to adhere to the Order, enhancing transparency in operational practices. The Order aims to improv
1 views • 30 slides
Ensuring Security in Persistent Key-Value Stores using Shielded Execution
This content discusses the challenges and solutions for securing LSM-based Key-Value stores in untrusted computing environments using Shielded Execution. It addresses the need for confidentiality, integrity, and freshness of data in persistent storage systems. The research explores Trusted Execution
0 views • 32 slides
Modes of Execution of Decree in Civil Law
The lecture discusses the various modes of execution of decree in civil law, such as execution against a person through arrest and detention, and execution against property. It explains the procedures involved in arrest and detention, including the conditions for release, restrictions on arrest, and
0 views • 9 slides
Understanding Java Memory Management
Explore how memory is managed in Java programs, including memory allocation for code, objects, and execution stack. Learn about memory areas like the execution stack and heap, and understand the concept of activation records in method execution.
0 views • 27 slides
Efficient Construction Practices for Successful Project Execution
Efficiently managing critical stages of construction, from site identification to masonry works, is crucial for project success. Key steps include site acquisition, material procurement, setting out structures, concrete work, and masonry works. Each stage requires careful planning, adherence to spec
0 views • 10 slides
Exploring Instruction Level Parallel Architectures in Embedded Computer Architecture
Delve into the intricacies of Instruction Level Parallel Architectures, including topics such as Out-Of-Order execution, Hardware speculation, Branch prediction, and more. Understand the concept of Speculation in Hardware-based execution and the role of Reorder Buffer in managing instruction results
0 views • 51 slides
Understanding Computer Architecture: Superscalar Pipelines
Explore the concept of Superscalar Pipelines in computer architecture, featuring in-order execution, instruction-level parallelism, hardware issues, and more. Discover the limitations of scalar pipelines and the potential for parallel execution. Delve into the required checking for executing multipl
1 views • 23 slides
Evolution of Execution Methods in Modern Society
Explore the historical and modern methods of execution, from hanging to lethal injection, and the transition towards more civilized approaches. Learn about the contributions of prominent figures like Elbridge Gerry in advocating for humane execution methods. Delve into the commercial rivalry between
0 views • 13 slides
Secure and Efficient Multi-Variant Execution in Distributed Settings
This paper discusses dMVX, a system for secure multi-variant execution in distributed settings to mitigate memory errors and protect against attacks. Using leader and follower variants, diversified program variants run in lockstep to ensure security. The system monitors and replicates I/O results, e
0 views • 35 slides
Demand Planning and Order Management: Enhancing Efficiency
Explore the intricate relationship between demand planning and order management, crucial for optimizing customer order fulfillment cycles. Learn key principles, tools, and techniques to enhance communication and manage demand effectively, along with contemporary approaches and e-commerce fulfillment
1 views • 28 slides
Embedded Computer Architecture - Instruction Level Parallel Architectures Overview
This material provides an in-depth look into Instruction Level Parallel (ILP) architectures, covering topics such as hazards, out-of-order execution, branch prediction, and multiple issue architectures. It compares Single-Issue RISC with Superscalar and VLIW architectures, discussing their differenc
0 views • 49 slides
Hardware-Assisted Task Scheduler for OS Intensive Applications
A hardware-assisted task scheduler called SchedTask is proposed to address the issue of instruction cache pollution in OS intensive applications. By utilizing SuperFunction characterization and a specialized scheduler, the system aims to optimize task execution on different cores for improved perfor
0 views • 28 slides
Engineering-To-Order Product/System Configuration Strategies
Strategies for dealing with engineering-to-order product/system configuration including assemble-to-order, make-to-order, configure-to-order, and engineer-to-order approaches. Highlights different levels of diversity, challenges, and solutions in personalized system configurations.
0 views • 10 slides
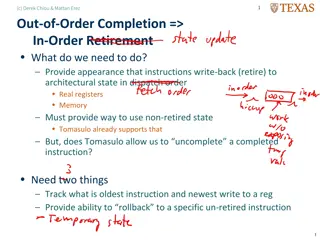
Enhancing Out-of-Order Completion with In-Order Retirement
To improve performance, instructions are retired in dispatch order rather than completion order. Introduce appearance changes in architectural state, track oldest and newest instructions, and allow rollback to un-retired instructions. Implement reorder buffers, separate rename registers, and utilize
0 views • 5 slides
Understanding Code Execution Graphs and Superblocks in Software Analysis
Explore the concepts of Static Execution Graphs, Dynamic Execution Graphs, Superblocks, hot-path detection, and memory arithmetic in software analysis. Learn about the grouping of blocks, violation tracking, control dependencies, and code behaviors across time through these graphical representations
0 views • 9 slides
Impact of Supporting Out-of-order Communication on In-order Performance
This study delves into the impact of out-of-order communication on in-order performance in high-end computing systems, specifically investigating the potential solutions, challenges, and network handling strategies associated with this issue. The research focuses on the implications of supporting ou
0 views • 29 slides
Understanding Processes in Operating Systems - ECE344 Lecture 3 Summary
This lecture delves into the essential concepts of processes, threads, and synchronization in operating systems. Key topics covered include units of execution, representation of units of execution in the OS, process execution states, and state transitions. Users, programs, and the role of processes
0 views • 45 slides
InvisiSpec: Making Speculative Execution Invisible
InvisiSpec presents a novel defense mechanism to address speculative execution attacks in the cache hierarchy. By making speculative execution invisible to potential attackers, this holistic approach aims to mitigate the risks associated with exploiting side effects on incorrect paths, such as Spect
0 views • 18 slides
Multicycle Datapath and Execution Steps Overview
This content provides a detailed explanation of a multicycle datapath and the execution steps involved in processing instructions. It covers key elements such as instruction fetching, decoding, memory referencing, ALU operations, branch and jump instructions, as well as memory access for read and wr
0 views • 11 slides
Understanding Symbolic Execution and Directed Automated Random Testing
Symbolic Execution is a method used for analyzing programs to determine inputs causing each part to execute, vital in program testing. However, limitations arise in cases without code availability, hindering definitive path conditions. Directed Automated Random Testing (DART) overcomes this through
0 views • 20 slides
Secure Cloud Applications with Intel SGX - OSDI 2014 Presentation Summary
This presentation discusses the challenges of trusting cloud environments and proposes solutions utilizing Intel SGX technology. It explores the need for secure execution of applications on untrusted cloud platforms, presents existing solutions, and introduces the concept of Haven for private execut
0 views • 33 slides
Rethinking Processes with Threads in Operating Systems
Processes in operating systems traditionally include various resources and execution states, leading to inefficiencies in communication and parallel program execution. By separating the concept of a process from its execution state, modern OSes like Mac, Windows, and Unix introduce threads as lightw
0 views • 29 slides
Python Programming Essentials: Basics, Operators, Expressions, and Control Flow
This segment delves into the fundamentals of Python programming with a focus on essential concepts such as comments, numbers, strings, variables, arithmetic operators, logical operators, order of execution, expressions, and control flow statements like conditional execution and looping. Learn about
0 views • 12 slides
Understanding Computer Architecture Concepts in CSE502
Exploring advanced topics in computer architecture like out-of-order execution, dynamic scheduling, memory disambiguation, load/store queues, and more. Delve into the intricacies of executing memory instructions, handling memory disambiguation problems, and optimizing performance through techniques
0 views • 23 slides
Understanding Operating System Concepts: Multiprogramming, Multiprocessing, Multitasking, and Multithreading
In the realm of operating systems, terms like multiprogramming, multiprocessing, multitasking, and multithreading can often be confusing due to their similar appearance but distinct meanings. These concepts play a crucial role in efficiently managing resources in a computing system, particularly in
0 views • 6 slides
Vortex Transport by Uniform Flow - High-Order CFD Workshop Summary
Vortex transport by uniform flow case study presented at the First International High-Order CFD Workshop in 2012. It focuses on assessing the efficiency of high-order methods for LES/DES of turbulent flows and comparing them with state-of-the-art 2nd order FV algorithms. The case involves a very low
0 views • 11 slides
Memory Allocation and Program Execution Overview
Understanding memory allocation is crucial for efficient program execution. This content delves into the importance of memory allocation, considerations for storing data during program execution, and the requirements for allocating memory efficiently. It also explores solutions for managing memory s
0 views • 35 slides
Understanding Kinetics in Chemical Reactions
Kinetics is the study of reaction rates and factors affecting them. Reaction rate is the speed at which a reaction occurs, influenced by factors like concentration, temperature, pH, light, catalysts, and solvents. Reactant concentration determines reaction order, which categorizes reactions as zero-
0 views • 18 slides
Understanding CPU Virtualization and Execution Control in Operating Systems
Explore the concepts of CPU virtualization, direct execution, and control mechanisms in operating systems illustrated through a series of descriptive images. Learn about efficient CPU virtualization techniques, managing restricted operations, system calls, and a limited direct execution protocol for
0 views • 18 slides