Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding Leverage and Operating Leverage in Financial Management
Leverage in financial management refers to using assets or funds with fixed costs to analyze the impact of debt and equity mix on shareholder returns and risk. Operating leverage focuses on leveraging fixed operating costs to amplify profit changes with sales variations, measured by the degree of op
2 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Operating Systems
An operating system is a crucial program that manages all other programs on a computer. It handles tasks like input recognition, file management, and device control. There are different types of operating systems such as single-user, single-task systems, multi-user, multi-task systems, real-time ope
6 views • 11 slides
Understanding File System Interface in Operating Systems
The file system interface is a crucial aspect of any operating system, providing users with a method for storage and access to data and programs. It comprises files for data storage and a directory structure for organizing and managing files within the system. File attributes like name, identifier,
0 views • 8 slides
SDS/DYW Annual Operating Plan and Target Operating Model Guidance - March 2024
This guidance outlines the development of an Annual Operating Plan and Target Operating Model (TOM) to enhance collaboration and improve outcomes for young people. It emphasizes aligning planning activities, co-designing learner experiences, and maximizing collective resources through strategic part
1 views • 9 slides
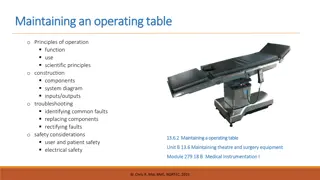
Maintaining an Operating Table: Principles and Functions
An operating table system comprises three components - the table column, table top, and transporter, each available in different versions for various surgical disciplines. Stationary tables are anchored to the floor, offering flexibility to adapt to patient needs. Mobile tables provide maneuverabili
0 views • 12 slides
Understanding Operating Costing in Service Industries
Operating costing is a method utilized by service-oriented businesses to ascertain the costs of providing services. Industries such as transportation services, welfare services, utility suppliers, and municipal services find operating costing beneficial. The method involves classifying costs into th
0 views • 6 slides
Understanding Operating Systems: Basics and Types
An operating system is essential software that manages a computer's hardware and software, allowing users to interact with the computer. Learn about the functions of an operating system, its importance, types available such as Microsoft Windows and macOS, and how they impact different devices. Disco
1 views • 11 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
NASA Platform Layer Updates for the CAELUM (7.0) Release
The National Aeronautics and Space Administration (NASA) discusses platform layer updates for the CAELUM (7.0) release of the Core Flight System in the 2021 Flight Software Workshop. The platform layer consists of the Operating System Abstraction Layer (OSAL) and Platform Support Package (PSP), whic
1 views • 20 slides
Understanding Operating Systems: Introduction and Functions
An operating system plays a crucial role in managing computer hardware and facilitating user-computer interactions. It serves as an intermediary between users and hardware components, ensuring efficient resource allocation and control. The operating system coordinates the use of hardware resources b
5 views • 16 slides
Fundamentals of Operating Systems Explained
Explore the core concepts of operating systems, including kernel-userspace interactions, system calls, context switching, and virtual memory management. Delve into x86 assembly for system calls, hardware interrupts, and the flow of control during system call invocations. Gain insights into key compo
7 views • 19 slides
Understanding Operating Systems: Functions and Evolution
Operating systems are essential software that enable computers to function effectively by managing hardware resources and facilitating communication between applications and hardware. This article covers the basics of operating systems, their structure, evolution, functions, and types. It also explo
2 views • 23 slides
Overview of Social Security and Health Care System in Turkey
The social security system in Turkey comprises three main organizations: Social Insurance Institution (SGK/SSK), Social Security Institution for the Self-employed (Bag-Kur/SISE), and Pension Fund for Civil Servants (Emekli Sandigi). Hospitals in Turkey are dispersed among various social security and
7 views • 42 slides
Understanding Operating System Concepts: Lecture Overview and Services
Exploring the lecture content on operating system concepts, structures, services, system calls, and file manipulation. Delve into the importance of operating system services, error detection, program execution, I/O operations, protection, security, and resource allocation in operating systems. Learn
4 views • 26 slides
Understanding Operating System Services and Functions
An operating system provides services for both users and programs, including user interfaces, program execution, I/O operations, file-system manipulation, communication between processes, error detection, resource allocation, accounting, and protection/security measures. These functions ensure effic
5 views • 15 slides
Understanding Computer Software and Operating Systems
Computer software, comprising system software and application software, plays a crucial role in managing computer resources and facilitating user instructions. System software consists of control programs, support programs, and development programs, while application software assists in specific tas
1 views • 26 slides
Introduction to Operating Systems and Processes
In this informative content, we delve into the fundamental concepts of operating systems (OS) and processes. Operating systems are essential software that manage a computer's resources for users and applications. We explore the core functionalities of an OS, such as resource allocation, isolation, c
0 views • 41 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
MST Operating and Capital Budget FY 2025 Summary
The MST Operating and Capital Budget for FY 2025 focuses on maximizing revenues, increasing bus advertising rates, promoting transit services, seeking grants for capital projects, and maintaining stable staffing levels. The budget priorities also include operating a Better Bus Network at Board-adopt
0 views • 10 slides
Understanding UNIX Operating System
UNIX is a versatile operating system that enables multi-user access, multitasking, and portability across various computing environments. It serves as the foundation for many modern operating systems and has influenced concepts incorporated in Microsoft Windows and DOS. The UNIX system comprises dis
0 views • 51 slides
Understanding Operating System Interrupts and System Calls
Explore the fundamentals of operating system interrupts and system calls in COMP.530. Learn about synchronous and asynchronous interrupts, control flow handling, and the hardware tools available for irregular control flow. Delve into the key building blocks of operating systems such as context switc
0 views • 30 slides
Understanding Computer Systems and Operating System Architectures
An exploration of computer systems and operating system architectures, covering topics such as CPU modes, monolithic and layered architectures, microkernel architecture, Linux and Windows kernel architectures, as well as devices and their terminology. The content delves into the roles, structures, a
0 views • 57 slides
Introduction to Linux: Course Overview and Objectives
This introduction to Linux course provides a comprehensive overview of operating systems, including the history, variations, user interface, and essential commands. The course is designed with lectures, labs, and exercises to help participants gain a better understanding of Linux and its practical a
0 views • 77 slides
Understanding Embedded Operating System Security
Embedded operating systems are designed for special purposes with limited resources and small sizes, found in various devices like ATMs, smartphones, cars, and more. Common operating systems include VxWorks, Windows, QNX, and SCADA, with different applications and requirements. Windows CE stands out
0 views • 21 slides
Understanding Operating Systems: An Introduction and Overview
An operating system is a crucial program that manages computer hardware and serves as an intermediary between users and hardware. This chapter explores the role of operating systems in a computer system, covering components like hardware, application programs, and users. It delves into how operating
0 views • 16 slides
Understanding Carnegie Mellon's Protection and Security Concepts
Carnegie Mellon University emphasizes the importance of protection and security in operating systems. Protection involves preventing unauthorized access by users, while security focuses on external threats and authenticating system users. The goals of protection include preventing access violations
0 views • 37 slides
Introduction to Processes and Operating Systems in Embedded Systems
Processes and operating systems play a crucial role in building complex applications on microprocessors, offering flexibility to meet timing requirements. The operating system (OS) manages processes by providing mechanisms for switching execution between them. Real-Time Operating Systems (RTOS) are
0 views • 65 slides
Insights from Public Police Executives on Private Security Services
This survey conducted by the FSU Policing, Security Technology and Private Security Research & Policy Institute gathered opinions from 68 public police executives on private security services. The executives shared anticipation of future expansions, factors influencing growth, types of private secur
0 views • 9 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Best Practices for Password Security and User Authentication
Password security is crucial for protecting sensitive information. Passwords should not be shared and should be changed regularly to prevent unauthorized access. Implementing strong passwords, two-factor authentication, and biometric security measures can greatly enhance security. Additionally, main
0 views • 16 slides
Understanding Operating Systems: Principles and Practice in CSE Curriculum
Dive into the world of operating systems through the lens of "Operating Systems: Principles and Practice" by Tom Anderson. Discover how this course fits in the UW CSE curriculum, covering systems programming, operating system interfaces, and distributed systems. Explore the project work on building
0 views • 21 slides
An Overview of Network Operating Systems and Multitasking
This informative content discusses the services of network operating systems, multitasking concepts, essential components, client and server software elements, and network services. It explains the two forms of multitasking - preemptive and nonpreemptive - and their functions within operating system
0 views • 48 slides
Overview of Network Operating Systems and Their Features
Network operating systems are essential software that manage computer resources and provide services for programs. This lecture covers the types of computers in a network, features of operating systems such as process and memory management, disk and file systems, and networking capabilities. Underst
0 views • 27 slides