BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Promoting Respect and Understanding: A Lesson on Avoiding Slurs and Offensive Language
This advisory lesson series focuses on building a respectful community by educating students about the harmful impact of slurs and offensive language. Through activities and discussions, students learn about the origins and offensiveness of such language, emphasizing the importance of respect and in
7 views • 21 slides
Influence of Family Values and Christian Beliefs on Perceptions of Offensive Ads
This study explores how family values and Christian beliefs influence perceptions of offensive ads, particularly those featuring controversial topics like homosexuality. Research objectives include examining differences in perceived offensiveness between Christians and non-Christians, as well as the
4 views • 19 slides
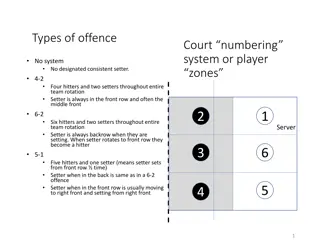
Volleyball Offensive Strategies Overview
Understanding volleyball offensive strategies such as the 4-2, 6-2, and 5-1 systems, player designations, and court numbering systems. Learn about the roles of setters, hitters, and overlap considerations for successful team rotation and gameplay. Visual representations provided for better comprehen
1 views • 6 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Understanding Offensive and Ethical Issues in Advertising
Ads can be offensive and provoke ethical concerns due to their content and presentation, leading to differing perceptions of good taste. Criticism of taste in advertising often revolves around sensitive topics like sex, violence, and brand messaging. The impact of ads can vary based on factors such
1 views • 26 slides
Understanding Wireless Security Audits and Best Practices
Explore the world of security audits with a focus on wireless networks. Learn about the types of security audits, best practices, and the steps involved. Discover the importance of systematic evaluations, identifying vulnerabilities, establishing baselines, and compliance considerations. Dive into t
0 views • 14 slides
Farmington Tiger Football Youth Offensive Formations and Concepts
In the Farmington Tiger Football youth program, coordinated offensive formations and concepts are emphasized for players in grades 3-12. The program aims to maintain consistency in offensive strategies while allowing some flexibility for coaches to incorporate age-appropriate concepts. Various forma
0 views • 54 slides
The Evolution of Dyninst in Cyber Security
The evolution of Dyninst in support of cyber security explores various aspects including different types of binary programs, security challenges, offensive and defensive strategies, adaptation techniques, better parsing methods, and the use of hybrid static and dynamic analysis. The content highligh
1 views • 19 slides
Offensive Thinking - Teaching and Practice Structure Overview
Discover the steps and strategies involved in teaching offensive thinking through structured practice sessions. Explore concepts like whole-part-whole progression, inverted pyramid coaching style, self-scout preparation, and end-zone strategies to enhance players' performance. Learn how to simplify
0 views • 19 slides
Offensive Zone Strategies for Effective Hockey Play
Learn key offensive zone habits, skills, and strategies for successful play in hockey, including techniques such as handling the puck, quick release, net-front positioning, and attacking with purpose. Discover points on creating offense, transitioning with speed, making quick decisions, and utilizin
0 views • 11 slides
Lacrosse Offensive and Defensive Strategies for Youth Playbook 2021" (70 characters)
Explore various offensive and defensive strategies in lacrosse, including crease positioning, motion plays, and offensive sets such as 2-3-1 and 2-2-2. Learn how to navigate the field effectively and make strategic plays to outmaneuver opponents in youth lacrosse. (237 characters)
0 views • 27 slides
Examining the Impact of Racially Offensive Costumes and Cultural Stereotypes on Halloween Celebrations
Controversies surrounding racially offensive Halloween costumes highlight the need for awareness and sensitivity. Costumes reflecting stereotypes, such as "Redneck" or "Geisha," can perpetuate harmful views. Initiatives like Ohio University's STARS campaign aim to educate on the implications of cost
0 views • 20 slides
Defensive Recognition and Play Scripting for Offensive Success
Explore defensive recognition strategies by analyzing defensive tendencies based on down, distance, and field zone. Learn how to create effective play scripts using offensive position recognition and Tri-O principles to achieve offensive success. Utilize the no-huddle approach, ANA system, and key c
0 views • 13 slides
Hand Gestures Around the World: What Not to Do
Communicating effectively involves more than just words - hand gestures play a significant role. However, certain gestures that may be innocuous in one culture can be highly offensive in another. For example, the OK sign in the US can insult individuals in Greece, Spain, and Brazil, the chin flick i
0 views • 14 slides
Understanding the Security Dilemma in International Relations
Uncertainty is inherent in the lives of individuals and groups, leading to the need for states to assume the worst in international relations. The security dilemma, conceptualized as a two-level strategic predicament, revolves around interpreting the intentions and capabilities of others and decidin
0 views • 12 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Understanding Cyber Conflict Fundamentals and Policy Framework
Cyber conflict involves defensive and offensive cybersecurity measures, with the need for comprehensive policy frameworks to guide the use of offensive capabilities. Governments must establish guidelines comparable to those for police officers carrying guns, covering doctrine, training, rules of eng
0 views • 79 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
3rd-4th Grade 9-Man Offensive Playbook with I-Backfield Formation Plays
Explore the offensive playbook designed for 3rd-4th grade 9-man football teams featuring various I-backfield formation plays like the 52 Dive, 152 Dive, 62 Dive, 162 Dive, 63 Dive, 163 Dive, 74 Reverse, 174 Reverse, 53 Power, 153 Power, 63 Power, and 163 Power. Each play is detailed with the positio
0 views • 47 slides
Understanding Threat Modeling and Offensive Security
Threat modeling in offensive security involves determining potential threat scenarios that could compromise a system, understanding the system from an attacker's perspective, and devising defensive strategies. It helps confirm security implementations, identify gaps, monitor shortcomings, vulnerabil
0 views • 31 slides
Expert Threat Intelligence and Incident Response Specialist
Experienced USMC Veteran with over 14 years in Information Technology/Security, specializing in Incident Response, Forensics, Threat Intelligence, and Offensive Security. Matt Nelson is a 2651 Secure Comms/Intel SysAdmin, offering a wealth of knowledge and expertise in the field.
0 views • 48 slides
Youth Football Offensive Fundamentals and Drills Overview
Explore the essential offensive skills and drills for youth football players coached by Mike Elder from Avon High School in Ohio. Learn about practice structure, position-specific skills for offensive linemen, quarterbacks, running backs, and wide receivers, along with fun and fundamental drills to
0 views • 14 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Lacrosse Offensive Playbook Strategies
Learn about various offensive plays and strategies in lacrosse, including the Open Set (Zero), 2-3-1 Sweep, and 2-3-1 Alley Dodge. Each play is designed to create scoring opportunities by maintaining spacing, utilizing player movements, and taking advantage of defensive matchups. Explore diagrams an
0 views • 16 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Leveraging Persistence for Offensive Security
Explore the tactics and techniques of persistence for offensive security, covering topics such as penetration testing, red team engagements, credential stealing, and utilizing registry keys and scheduled tasks. Discover ways to maintain access to systems through unauthorized means and understand the
0 views • 20 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
The Essentials of Offensive Security in Web Applications
Comprehensive overview of key aspects of offensive security in web applications including testing areas, OWASP guidelines, top 10 vulnerabilities, essential tools, web scoping, handling dangerous portions, understanding request types, and following a specialized methodology for exploitation. The con
0 views • 13 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
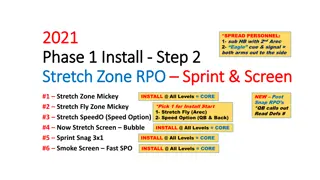
Advanced Football Offensive Plays for Effective RPO Incorporation
Explore a detailed guide on installing and executing advanced football offensive plays, focusing on concepts like Stretch Zone RPO, Pass Protection Route Concept, and Outside Zone Base RPO. Learn about key steps, signal cues, blocking strategies, post-snap reads, QB footwork, and game situations app
0 views • 13 slides